SWP2 Series Technical Data
Firmware revision: Rev.2.03.18
Thank you for your purchase of the Yamaha SWP2 series.
Please read this manual carefully, correctly installing the unit and making the proper settings before use.
Make sure to observe the warnings and cautions listed in this manual, in order to use the unit correctly and safely.

Startup guide
This explains the procedure for preparing to set up the SWP2 series unit that you purchased.
Settings for the SWP2 series can be made using the following four methods.
- Make settings via the Web GUI
- Make settings via commands using the CONSOLE port
- Make settings via commands using TELNET
- Make settings via commands using SSH
This document explains “Preparing to make settings via the Web GUI” and "Preparing to make settings via the CONSOLE port."
Preparing to make settings via the Web GUI
You’ll log into the Web GUI from Yamaha LAN Monitor, so install Yamaha LAN Monitor before you proceed.
Before you log in, connect the computer to the same network.
For details on supported web browsers, refer to the Yamaha Pro Audio website.
https://www.yamaha.com/proaudio/
- Prepare the computer and other items you’ll need when making settings.
- Obtain a category 5 Ethernet cable for connecting to this unit.
Connect this unit to the computer via a category 5 Ethernet cable.
Power-on this unit. This unit takes approximately 70 seconds to start up.
When startup is completed, the indicator of the LAN port to which the Ethernet cable is connected will light according to the communication speed and mode.Start Yamaha LAN Monitor.
Select the device for which you want to make settings, and in the “Device details” view, click the “Web GUI” button.
When access succeeds, a dialog box asking you to enter a user name and password appears.
If the user was specified in advance, enter the username and password and then click the [Login] button.
If factory default settings are configured, log in by entering “admin” as the default administrative username (and “admin” as the password).For factory default settings, a language selection screen is displayed after successfully logging in.
When prompted to change the password after using the default administrative user to log in, specify a new password.
- Subsequently, make settings as appropriate for the system in which this unit is being used.
- For details on settings via the Web GUI, refer to Help within the GUI that you accessed.
Preparing to make settings via the CONSOLE port
- Prepare the computer and other items you’ll need when making settings.
When making settings via the CONSOLE port, use an RJ-45/DB-9 console cable.
You’ll also need terminal software for controlling the serial (COM) port of the computer.
Set the communication settings of the console terminal as follows.
- Baud rate: 9600 bps
- Data: 8 bits
- Parity: none
- Stop bit: 1 bit
- Flow control: Xon/Xoff
- Use an RJ-45/DB-9 console cable to connect the computer to this unit.
- Power-on this unit. This unit takes approximately 70 seconds to start up.
Immediately after startup, the serial console screen appears as follows.
YamahaL2SW BootROM Ver.1.00 Starting ............................. SWP2 Rev.2.03.01 (Tue Mar 13 08:41:39 2018) Copyright (c) 2018 Yamaha Corporation. All Rights Reserved.
- Log in to this unit.
For factory default settings, log in by entering “admin” as the default administrative username (and “admin” as the password).
After using “admin” to log in, the password must be changed to specify a new password.Username: admin Password: admin SWP2 Rev.2.03.01 (Tue Mar 13 08:41:39 2018) Copyright (c) 2018 Yamaha Corporation. All Rights Reserved. Please change the default password for admin. New Password: ... (Enter the new password.) New Password(Confirm): ... (Enter the same password again.) Saving ... Succeeded to write configuration SWP2>
- Subsequently, make settings as appropriate for the system in which this unit is being used.
- For details on settings via the serial console, refer to Command Reference.
Firmware Updates
For stable operation, we recommend that you apply the latest firmware updates, which include new functionality and bug fixes.
Please confirm your system version before applying updates.
- Use the show environment command to check the system version.
Precautions
- Do not use this unit near another electrical product such as a television, radio, or mobile phone. Such use might cause noise in this unit or in the television or radio.
- Do not use this unit in locations of direct sunlight (such as inside a car located in the sun), in extremely hot locations such as near a stove, in extremely cold locations, nor in locations that are excessively dusty or are subject to strong vibration. Such conditions might cause this unit’s panel to deform or internal components to malfunction, or might cause unstable operation.
- If the ambient temperature in which this unit is located undergoes extreme change (such as when the unit is moved or is subject to aggressive air-conditioning or heating), and there is a danger that condensation has formed within the unit, leave the unit unpowered for several hours to ensure that condensation has disappeared before using the unit. Using the unit when condensation is present might cause malfunctions.
- Products made of vinyl, plastic, or rubber should not be placed on this unit. Such objects might cause this unit’s panel to be discolored or damaged.
- To clean this unit, use a soft dry cloth. Do not use benzene, thinner, detergent, or a chemically treated cloth, such things might cause discoloration or damage.
- Before touching this unit, discharge any static electricity from your clothing and body. Static electricity might cause malfunctions. Before you proceed, touch an unpainted metal component or the ground terminal of a grounded device.
- Do not place this unit in locations where there is a strong magnetic field. Such conditions might cause malfunctions.
- Do not connect equipment that generates noise to the same electrical power supply line as this unit. Such conditions might cause malfunctions or faulty operation.
- Do not route communication cables near power cords. High voltages might be induced, causing faulty operation.
- When using a 1000BASE-T connection, use enhanced category 5 (CAT5e) or better LAN cable.
- Optical fiber cables can suffer problems such as loss of accuracy caused by damage or abrasion to their connector, or dirty contacts, causing insufficient light reception or failure to link up. In particular, single mode fiber is more prone to suffer these effects than multi mode fiber, so it should be handled with care. Clean the contacts before making connections.
- SWP2 Series Technical Data (Basic Functions)
- Important notice
Login security
1 Function Overview
This product includes the following user account management improvements as countermeasures for ensuring cyber security.
To eliminate the risk of malicious cyber-attacks and ensure the product is used safely, be sure to read this document carefully and specify an appropriate user password before use.
For details, refer to User account management.
- Mandatory administrator registration
- At least one administrator account must be registered for this product.
Therefore, a default administrative user (username: admin and password: admin) has been specified for logging in to the product the first time.
- When first logging in, specify admin for both the username and password.
- After logging in using the default administrative user account, the user is prompted to change the password setting.
- At least one administrator account must be registered for this product.
- Stricter limits on guest user operations
- If the special privileged access password (default administrative password) has not been changed, the following operations that use a special privileged access password will be restricted.
- Users without administrator rights cannot switch to the privileged EXEC mode.
- Factory settings cannot be restored using CLI/ GUI operations.
- Connections as a TFTP server cannot be received.
- To perform the above operations, change the special privileged access password (default administrative password).
- If the special privileged access password (default administrative password) has not been changed, the following operations that use a special privileged access password will be restricted.
- Countermeasure for Brute-Force Attacks
- As a countermeasure against brute-force attacks, login restrictions are applied after a login fails.
- If an incorrect password is entered three successive times when logging into the switch via the console, Web GUI, or other means, login is disabled for one minute thereafter, even if the correct password is entered.
- If the password is entered incorrectly, wait at least one minute before trying to log in again.
2 Applicable models and revisions
User account management has been improved in the following models and revisions.
| Models | Revisions |
| SWX3220-16MT SWX3220-16TMs | Rev. 4.02.10 or later |
| SWX3200-52GT SWX3200-28GT | Rev. 4.00.25 or later |
| SWX3100-18GT SWX3100-10G | Rev. 4.01.29 or later |
| SWX2322P-16MT | Rev. 2.06.10 or later |
| SWX2320-16MT | Rev. 2.05.10 or later |
| SWX2310-52GT SWX2310-28GT SWX2310-18GT SWX2310-10G | Rev. 2.04.11 or later |
| SWR2310-28GT SWR2310-18GT SWR2310-10G | Rev. 2.04.12 or later |
| SWX2310P-28GT SWX2310P-18G SWX2310P-10G | Rev. 2.02.24 or later |
| SWR2311P-10G | Rev. 2.02.25 or later |
| SWP2-10SMF SWP2-10MMF | Rev. 2.03.16 or later |
3 Precautions when updating firmware
If the firmware is updated with stronger user account management functionality, be sure to register an administrator account according to the following procedure before using the switch.
- Register the administrator account with the previous firmware running, which has not been updated with stronger user account management functionality.
- If an administrator account already exists, then no account registration is necessary.
- However, if a password was not specified for the administrator account, be sure to specify a password.
- It is not a problem if the user name for the administrator account is the default “admin”.
Yamaha>enable Yamaha#configure terminal Yamaha(config)#username (username) privilege on password (password)
- Create guest user
If necessary, create a guest user as follows.- If using the username command, create it with the privilege option disabled (off).
Yamaha(config)#username (username) privilege off password (password)
- If using the username command, create it with the privilege option disabled (off).
- Change the special privileged access password (administrative password)
- The default special privileged access password (administrative password) setting is “admin”.
- To change the special privileged access password (administrative password) using a command, use the enable password command.
Yamaha(config)#enable password (special privileged access password)
- Update the firmware as described in
- Firmware update“update the firmware to the updated version”.
4 Related Documentation
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
Maintenance and operation functions
- User account management
- LED control
- Boot data management
- Viewing unit information
- System self-diagnostic
- Cable diagnostics
- Config management
- Remote access control
- Time management
- SNMP
- RMON
- SYSLOG
- Firmware update
- L2MS control
- Mail notification
- LLDP
- LLDP automatic setting
- Terminal monitoring
- Performance observation
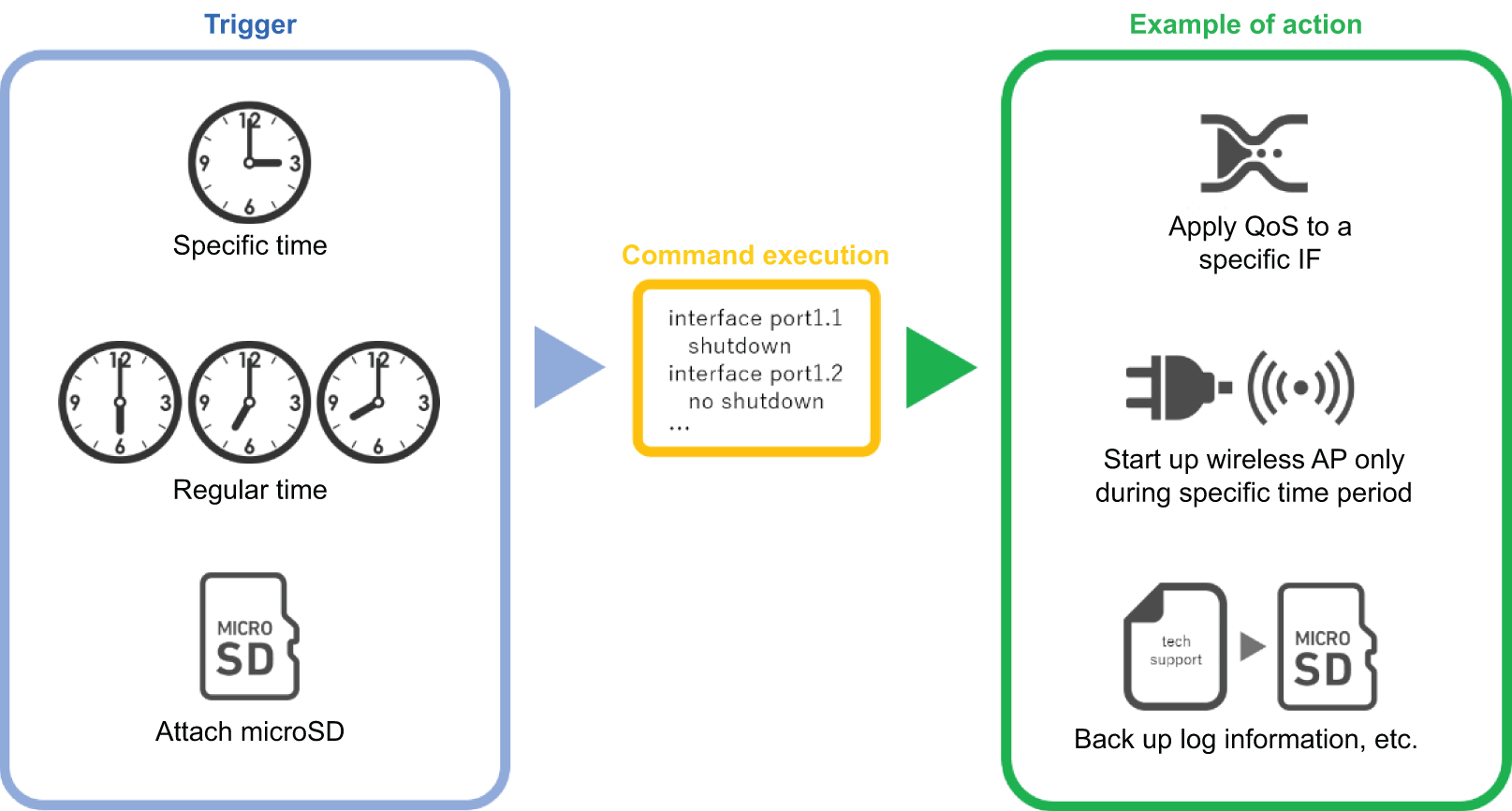
- Scheduling function
- Dante optimization setting function
- List of preset settings
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
- User account management
User account management
1 Function Overview
This product provides the functions shown below for managing user accounts.
- Functions for setting user information
- Functions for user authentication by user name and password
2 Definition of Terms Used
Default administrative user
Users with administrator rights specified in default factory settings.
Username: admin and Password: admin
Administrative user
Users with administrator rights.
Administrative users are users with the privilege option switched on using the username command.
Guest user
Users without administrator rights and that require entering the special privileged access password (administrative password) in order to access the privileged EXEC mode.
Guest users are users with the privilege option switched off using the username command.
Special privileged access password (administrative password)
The password used to assign administrator rights and specified using the enable password command.
Unnamed user
Users with a blank username setting.
Rev. 2.03.14 or earlier firmware versions permitted using unnamed user accounts under factory default settings, but unnamed user accounts were eliminated newer firmware versions with stronger user account management functionality.
3 Function Details
3.1 User account function settings
3.1.1 Setting user information
Use the username command to specify the following user information.
- User name
- Password
- Assignment of administrator rights
With factory default settings, the administrative username and password are both “admin”.
3.1.2 Setting the special privileged access password (administrative password)
Special privileged access passwords (administrative passwords) are set using the enable password command.
Special privileged access passwords (administrative passwords) are used for the following applications.
- To initialize devices
- To transition users without administrator rights to the privileged EXEC mode.
- To use a TFTP client to send a config file or firmware to the switch
The factory default special privileged access password (default administrative password) setting is admin, but the operations described above cannot be performed if the special privileged access password (default administrative password) is set to the default setting.
To perform any of those operations, change the special privileged access password (default administrative password) in advance.
3.1.3 Administrator rights
User login operations can be restricted depending on whether or not the user has administrator rights.
- Users with administrator rights can change device settings or update firmware.
- Users without administrator rights can only view device information without changing any settings.
Specifically, the following differences apply depending on whether or not the user has administrator rights.
| Console | Web GUI | |||
|---|---|---|---|---|
| Administrative user (with rights) | Guest user (without rights) | Administrative user (with rights) | Guest user (without rights) | |
| Show device information | ✓ | ✓ | ✓ | ✓ |
| View settings | ✓ | - | ✓ | Limited (*1) |
| Change settings | ✓ | - | ✓ | - |
| Restart or initialize devices | ✓ | - | ✓ | - |
| Update the firmware | ✓ | - | ✓ | - |
*1: Cannot view passwords or other security-related settings.
Once the enable command is executed and the special privileged access password (administrative password) is entered, the privileged EXEC mode can be accessed to perform operations equivalent to an administrative user, even if logged in as a guest user.
For information about the rights required to execute each command, refer to the command reference.
3.1.4 Password encryption
Specified passwords can be encrypted using the password-encryption command.
To encrypt a password, specify the password-encryption enable setting.
Once a password has been encrypted, it cannot be restored to an unencrypted character string state, even by specifying the password-encryption disable setting.
Encryption applies to the passwords specified by the following commands.
- enable password command
- username command
3.2 User authentication
3.2.1 When logging in to the console
When the following login prompt appears after connecting to the console, log in by entering the specified username and password.
Username: Password:
For factory default settings, log in by entering “admin” as the default administrative username (and “admin” as the password).
After using “admin” to log in, the password must be changed to specify a new password.
Username: admin Password: ... (Enter “admin”) SWP2 Rev.2.03.01 (Tue Mar 13 08:41:39 2018) Copyright (c) 2018 Yamaha Corporation. All Rights Reserved. Please change the default password for admin. New Password: ... (Enter new password.) New Password(Confirm): ... (Enter the same password again.) Saving ... Succeeded to write configuration
If an incorrect password is entered three successive times, login by that same user is restricted for one minute.
Username: User Password: % Incorrect username or password, or login as User is restricted. Password: % Incorrect username or password, or login as User is restricted. Password: % Incorrect username or password, or blocked upon 3 failed login attempts for User. % Please try again later.
If a login restriction occurs, the following message is output in the INFO level SYSLOG.
| Connection method | Output message |
| Serial console | Login access from serial console as {username} was restricted |
| TELNET | Login access from TELNET as {username} was restricted: {IP address} |
| SSH | Login access from SSH as {username} was restricted: {IP address} |
| Web GUI | Login access from HTTP as {username} was restricted: {IP address} |
Note that if a user with a login restriction enters an incorrect password again, the remaining time until the restriction is cancelled is reset to one minute again.
3.2.2 Logging into the Web GUI
When the following login form appears after accessing the Web GUI, log in by entering the specified username and password.
For factory default settings, log in by entering “admin” as the default administrative username (and “admin” as the password).
If logging in with factory default settings, a Web GUI language selection screen is displayed after logging in.
If prompted to change the password after using “admin” to log in, specify a new password.
3.3 What to do if you forget your login password
If the product is rebooted connected to the serial console and “I” (uppercase letter I) is entered during the booting process, the product can be rebooted with factory default settings.
BootROM - X.XX Booting from SPI flash SWP2 BootROM Ver.1.00 #### Enter “I” as soon as the boot ROM version is displayed. #### Initialize or not ?(y/n) y Loading config0 because can’t read config in SD card. Starting .............................................. Loading configuration ... Done! SWP2 Rev.2.03.01 (Tue Mar 13 08:41:39 2018) Copyright (c) 2018 Yamaha Corporation. All Rights Reserved.
4 Related Commands
The related commands are shown below.
For details, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Setting the special privileged access password (administrative password) | enable password |
| Encrypt password | password-encryption |
| Set user | username |
| Show user information | show users |
5 Examples of Command Execution
5.1 Adding a user
The following example assigns administrator rights to the user “yamaha” and specifies the password “yamaha_pass”.
Yamaha#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Yamaha(config)#username yamaha privilege on password yamaha_pass Yamaha(config)#exit Yamaha#exit Username: yamaha Password: SWP2 Rev.2.03.01 (Tue Mar 13 08:41:39 2018) Copyright (c) 2018 Yamaha Corporation. All Rights Reserved. Yamaha>enable Yamaha#
6 Points of Caution
- If no administrative user (user with administrator rights) exists in startup-config when the product is booted, then a default administrative user (with username “admin”and password “admin”) will be added automatically.
For example, that would occur in the following case.
- Product is booted with factory default settings configured
- Firmware is updated to a newer version than Rev.2.03.14 after the product was operated using Rev. 2.03.14 or older firmware only by an unnamed user.
- If a user with no password is specified in startup-config when the product is booted, then a password with the same character string as the username will be added automatically.
For example, that would occur in the following case.
- Firmware is updated to a newer version than Rev. 2.03.14 after Rev. 2.03.14 or older firmware was used to specify a user with no password.
Setting with Rev. 2.03.14 or earlier firmware version
username yamaha1 username yamaha2 privilege on
Setting after updating firmware to a newer version than Rev. 2.03.14
username yamaha1 password yamaha1 username yamaha2 privilege on password yamaha2
- Firmware is updated to a newer version than Rev. 2.03.14 after Rev. 2.03.14 or older firmware was used to specify a user with no password.
- If the password (admin) for the default administrative user admin is left unchanged, then the following restrictions are applied.
- Switches cannot be accessed by TELNET, SSH, HTTP, or HTTPS from a network segment other than the maintenance VLAN.
- Login by users other than the default administrative user is not permitted.
Username: yamaha Password: % Please login as user "admin".
- The following commands cannot be executed. Similar setting changes cannot be performed via the Web GUI either.
- ip address / no ip address
* However, only the ip address dhcp command can only be executed - auto-ip / no auto-ip
- ipv6 / no ipv6
- ipv6 address / no ipv6 address
- management interface / no management interface
- ip address / no ip address
7 Related Documentation
LED control
1 Function Overview
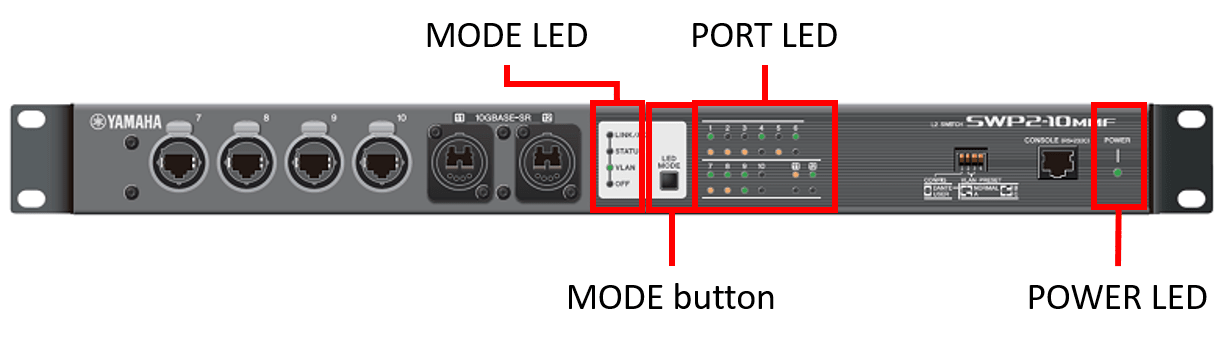
This L2 switch uses LEDs to indicate the status of the LAN/SFP+ ports.
LED type
| LED type | Description |
|---|---|
| POWER LED | Indicates the power status. |
| Port LEDs | Indicate the LAN/SFP cable connection and usage status. |
| MODE button | Switch LED mode. |
The location of each LED and button is shown below.
2 Definition of Terms Used
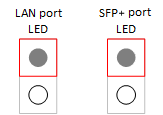
- Explanation of port LED illumination
The port LED illumination used in subsequent explanations is described below.
Port LED illumination
3 Function Details
3.1 Port LEDs
3.1.1 Switching between display modes
This product provides the four display modes shown below.
| Mode name | MODE LED light status | Function overview |
|---|---|---|
| LINK/ACT mode | 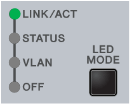 | The upper LED of the LAN/SFP+ port shows the link status, and the lower LED shows the connection speed. |
| STATUS mode | 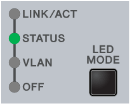 | The error status of the LAN/SFP+ port is shown. |
| VLAN mode | 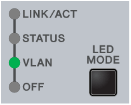 | The VLAN ID set for the LAN/SFP+ port is shown. |
| OFF mode | 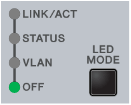 | The LAN/SFP+ port LEDs are unlit in order to decrease the power consumption. |
Use the MODE button to switch between display modes.
Display mode switching follows the flow shown below.
Display mode switching (when the default LED mode is LINK/ACT)
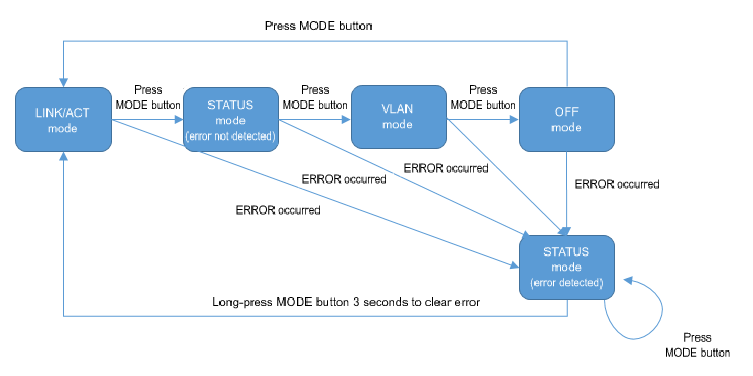
The display mode after system boot and the display mode after error resolve depend on the default LED mode setting.
When an error is detected by the following functions, the port LED display automatically switches to STATUS mode.
- Loop detection
- SFP optical reception level monitoring
When an error has been detected, the unit remains in STATUS mode even if the MODE switch is pressed. (The switch will not function until all errors have been resolved.)
In this state, if you long-press the MODE button for three seconds, all error states are reset, and the unit switches to the display that is specified by the default LED mode setting.
(For details, refer to LED display in STATUS mode.)
3.1.2 LED display in LINK/ACT mode
The port LEDs will display as shown below in LINK/ACT mode.
- LAN/SFP+ port link status
- LAN port connection speed
The LED display for the link status is shown below.
LAN/SFP+ port link status LED display
| Linking down | Linking up | Forwarding data |
|---|---|---|
 (unlit) | 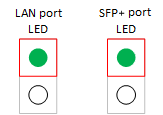 (lit green) | 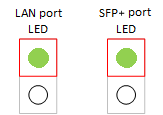 (flashing green) |
The LED display for the connection speed is shown below.
LAN/SFP+ port connection speed LED display
| 10BASE-T | 100BASE-T | 1000BASE-T | 10000BASE-T |
|---|---|---|---|
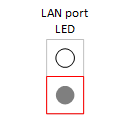 (unlit) | 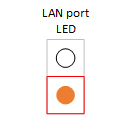 (lit orange) | 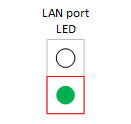 (lit green) | (none) |
| (none) | (none) | (none) | 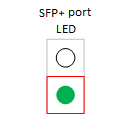 (lit green) |
3.1.3 LED display in STATUS mode
In STATUS mode, the port LEDs indicate error statuses generated by the following functions of this product.
- Loop detection
- SFP optical reception level monitoring
Port LED display when an error occurs
| Normal state | Loop detected or SFP optical reception level fault | |
|---|---|---|
| LAN port |  (unlit) |  (upper flashes orange) |
| SFP+ port |  (unlit) |  (upper flashes orange) |
When this product detects an error, it forcibly switches to STATUS mode.
An error is determined by each function in the following cases.
- Loop detection
- A loop was detected and the port was blocked.
- A loop was detected and the port was shut down.
- SFP optical reception level monitoring
- The SFP+ optical reception level fell below the normal range.
- The SFP+ optical reception level exceeded the normal range.
To determine the cause of the error, you can use the show error port-led command.
In STATUS mode when an error has occurred, the LEDs will automatically switch to the default LED mode in the following states.
- All of the following errors were resolved.
- Blocked status due to loop detection was resolved.
- Shutdown status due to loop detection was resolved.
- The monitoring time has elapsed following shutdown due to loop detection.
- In a shutdown state due to loop detection, the unit linked up after the no shutdown command was executed.
- SFP+ optical reception level recovered.
- The MODE switch was long-pressed (for three seconds), forcibly resetting (clearing) the error status.
3.1.4 LED display in VLAN mode
In VLAN mode, the port LEDs display the VLAN association status.
The port LED light status is shown below.
Port LED light status in VLAN mode
| VLAN association status for LAN/SFP+ port | Port LED light status |
|---|---|
| Associated with one VLAN | 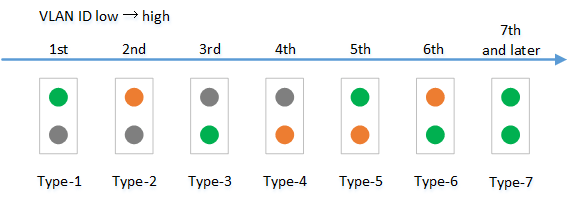 Expressed as one of six specific light patterns, starting with the newest of the VLAN IDs. All VLAN IDs from #7 onwards will be indicated using the same light pattern. |
| Is not associated with any VLAN |  (OFF) |
| Associated with multiple VLANs |  (Both upper and lower port LEDs are lit orange.) |
- The default VLAN (VLAN #1) is not shown. It is not counted as an associated VLAN.
- The VLAN association status does not depend on the link status of each LAN/SFP+ port. Ports in linkdown status will be shown.
- Only VLAN IDs for which associated LAN/SFP+ ports exist are shown.
If only the VLAN ID is defined (without an associated LAN/SFP+ port), the VLAN ID is not shown.
3.1.5 LED display in OFF mode
If the default LED mode is OFF mode, the port LEDs are all unlit regardless of the link status.
Even if the default LED mode is OFF mode, the unit automatically transitions to STATUS mode when an error occurs, indicating the error status.
3.1.6 Changing the LED mode after system boot
The LED mode after system boot (the default LED mode) for this product can be specified.
The default value for the default LED mode is set to LINK/ACT mode, but can be changed using the led-mode default command.
Use the show led-mode command to check the default LED mode and the LED mode currently displayed.
When STATUS mode is cleared during error detection, the unit will switch to the default LED mode that was set.
3.1.7 Other port LED displays
Regardless of the LED mode status, the LEDs of all ports will display as follows during initialization at startup and during firmware update.
Other port LED displays
| Updating firmware | Initializing | |
|---|---|---|
| LAN port |  (flashing green) |  (unlit) |
| SFP+ port |  (flashing green) |  (lit orange) |
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Show LAN/SFP+ port status | show interface |
| Show setting status of loop detection | show loop-detect |
| Show VLAN information | show vlan brief |
| Set default LED mode | led-mode default |
| Show LED mode | show led-mode |
| Show port error status | show error port-led |
5 Examples of Command Execution
5.1 Check LAN/SFP+ port status
Use the show interface command to check the LAN/SFP+ port status.
Yamaha#show interface
show interface
Interface port1.1
Link is UP
Hardware is Ethernet
HW addr: ac44.f23d.0b2c
ifIndex 5001, MRU 1522
Speed-Duplex: auto(configured), 1000-full(current)
Auto MDI/MDIX: on
Vlan info :
Switchport mode : access
Ingress filter : enable
Acceptable frame types : all
Default Vlan : 1
Configured Vlans : 1
Interface counter:
input packets : 317111
bytes : 31387581
multicast packets: 317074
output packets : 162694
bytes : 220469213
multicast packets: 162310
broadcast packets: 149
drop packets : 0
:
(Information for all LAN/SFP+ ports is shown)
5.2 Check LAN/SFP+ port loop detection status
Check the LAN/SFP+ port loop status.
Yamaha#show loop-detect loop-detect: Enable loop-detect: Enable port loop-detect port-blocking status ------------------------------------------------------- port1.1 enable enable Normal port1.2 enable enable Normal port1.3 enable enable Normal port1.4 enable enable Normal port1.5 enable enable Normal port1.6 enable enable Normal : : : : ------------------------------------------------------- (*): Indicates that the feature is enabled.
5.3 Set the default LED mode
Set the default LED mode to OFF mode.
Yamaha#configure terminal Yamaha(config)#led-mode default off … (Set default LED mode) Yamaha(config)#exit Yamaha#show led-mode … (Show LED mode) default mode : off current mode : off
6 Points of Caution
- None
7 Related Documentation
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
- Boot data management
Boot data management
1 Function Overview
As system boot information, this product manages the information shown in the table below.
System boot information: items managed
| Management item | Description |
|---|---|
| System boot time | Time that the system booted up |
| Run-time firmware update | Firmware version currently running, and date generated |
| Firmware information for previous startup | Version and generated date of the firmware for the previous startup |
| Reason for boot | Reason why the system booted up. The following reasons for boot are recorded:
|
This product stores the current boot information and information on the previous four boots, for a total of five boot records.
2 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Show boot information | show boot |
| Clear boot information | clear boot list |
3 Examples of Command Execution
3.1 Show boot information
- This shows the current boot information.
Yamaha>show boot 0 Running EXEC: SWP2 Rev.2.03.01 (Tue Mar 13 08:41:39 2018) Previous EXEC: SWP2 Rev.2.03.01 (Tue Mar 13 08:41:39 2018) Restart by reload command
- This shows a list of the boot history.
Yamaha>show boot list No. Date Time Info --- ---------- -------- ------------------------------------------------- 0 2018/03/15 09:50:29 Restart by reload command 1 2018/03/14 20:24:40 Power-on boot --- ---------- -------- -------------------------------------------------
3.2 Clear boot information
- This clears the boot information.
Yamaha#clear boot list
4 Points of Caution
None
5 Related Documentation
None
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
- Viewing unit information
Viewing unit information
1 Function Overview
This product provides the following functions that can be used to obtain product information, operating information, and so on.
- Use commands to show chassis information
- Obtain technical support information remotely
Technical support information includes a wide variety of data analysis information, including not only product information and operating information for this product, but also configuration information, and process operating status information.
The function can be used to show all information for a unit at the same time.
2 Function Details
2.1 Showing chassis information by using commands
This function shows chassis information by entering a command in the console.
The following chassis information can be shown.
List of Chassis Information Shown
| Information Shown | Description | Command |
|---|---|---|
| Product Information | Shows the product name, model number, product ID, and other information about the main unit. If an SFP module is inserted, product information about the module is also shown. | show inventory |
| Operating information | Shows product program operating information, such as boot software information, CPU usage rate, memory usage rate, and boot time. | show environment |
| Process list | Shows key information about the system and lists processes being executed. | show process |
| Memory usage status | Indicates the memory usage status for each process. | show memory |
| Disk usage status | Shows the percent of disk space used by the system. | show disk-usage |
| Technical support information | Shows all available operating information as data analysis information necessary for technical support. | show tech-support |
2.1.1 Showing product information
Shows product information for the main unit and SFP module using the show inventory command. Product information includes the following information.
- Name
- Description (DESCR)
- Vendor
- Product ID (PID)
- Version ID (VID)
- Serial No. (SN)
2.1.2 Showing operating information
Shows the system operating status using the show environment command. The system operating status includes the following information.
- Boot version
- Firmware revision
- Serial No.
- MAC address
- CPU usage rate
- Memory usage rate
- Firmware file
- CONFIG mode
- VLAN preset (only in DANTE mode)
- Serial baud rate
- Boot time
- Current time
- Elapsed time from boot
2.1.3 Showing technical support information
Shows technical support using the show tech-support command. Technical support information includes results from executing the following commands.
List of Executed Commands
| Command | Executability |
|---|---|
| show running-config | ✓ |
| show startup-config | ✓ |
| show environment | ✓ |
| show system-diagnostics | ✓ |
| show clock detail | ✓ |
| show disk-usage | ✓ |
| show dipsw | ✓ |
| show inventory | ✓ |
| show boot all | ✓ |
| show logging | ✓ |
| show process | ✓ |
| show memory | ✓ |
| show users | ✓ |
| show interface | ✓ |
| show frame-counter | ✓ |
| show vlan brief | ✓ |
| show spanning-tree mst detail | ✓ |
| show etherchannel status detail | ✓ |
| show loop-detect | ✓ |
| show mac-address-table | ✓ |
| show l2ms detail | ✓ |
| show qos queue-counters | ✓ |
| show ddm status | ✓ |
| show errdisable | ✓ |
| show auth status | ✓ |
| show auth supplicant | ✓ |
| show error port-led | ✓ |
| show ip interface brief | ✓ |
| show ip forwarding | ✓ |
| show ipv6 interface brief | ✓ |
| show ipv6 forwarding | ✓ |
| show ip route | ✓ |
| show ip route database | ✓ |
| show ipv6 route | ✓ |
| show ipv6 route database | ✓ |
| show arp | ✓ |
| show ipv6 neighbors | ✓ |
| show ip igmp snooping groups | ✓ |
| show ip igmp snooping interface | ✓ |
| show ipv6 mld snooping groups | ✓ |
| show ipv6 mld snooping interface | ✓ |
| show radius-server local certificate status | ✓ |
| show radius-server local nas | ✓ |
| show radius-server local user | ✓ |
| show radius-server local certificate list | ✓ |
| show radius-server local certificate revoke | ✓ |
2.2 Obtaining technical support information remotely
This product can obtain technical support information (output results from show tech-support) by remote access via the Web GUI or TFTP.
2.2.1 Web GUI
Use the following procedure to configure a network environment that enables remote access, so that the product can use http server functionality.
- Decide the VLAN to use for maintenance.
- Specify an IPv4 address for the maintenance VLAN. Use the ip address command to specify the address.
- Permit the maintenance VLAN to access the http server. To specify a different VLAN than for management interface command settings, use the http-server interface command.
Execute the following operation by accessing the Web GUI.
- Show technical support information on the Web GUI
- On the [TECHINFO] menu, click the [Show in browser] button to show show tech-support command results in a sub-window.
- To stop showing the results, click the web browser close button.
- Obtain technical support information from the Web GUI.
- On the [TECHINFO] menu, click the [Obtain as text file] button to automatically start downloading the file.
- The file is saved with a file name in the following format.
- techinfo_YYYYMMDDhhmmss.txt (where “YYYYMMDDhhmmss” is the date/time the command was executed)
2.2.2 TFTP
Use the following procedure to configure a network environment that enables remote access, so that the product can use tftp server functionality.
- Decide the VLAN to use for maintenance.
- Specify an IPv4 address for the maintenance VLAN. Use the ip address command to specify the address.
- Permit access from the maintenance VLAN to the tftp server. To specify a different VLAN than for management interface command settings, use the tftp-server interface command.
If using a tftp client, specify techinfo in the remote path for obtaining technical support information.
3 Related Commands
Related commands are indicated below.
For command details, refer to the command reference.
List of related commands
| Operations | Operating Command |
|---|---|
| Show product information | show inventory |
| Show operating information | show environment |
| Process list | show process |
| Memory usage status | show memory |
| Disk usage status | show disk-usage |
| Show technical support information | show tech-support |
| Save technical support information | copy tech-support sd |
4 Examples of Command Execution
4.1 Showing product information
The following shows product information for the main unit and SFP module.
Yamaha>show inventory NAME : L2 switch DESCR : SWP2 Vendor: Yamaha PID : SWP2 VID : 0000 SN : SMF00000 NAME : SFP1 DESCR : 10G Base-LR Vendor: Yamaha PID : YSFP-10G-LR VID : V1.0 SN : Z5H00000YJ NAME : SFP2 DESCR : 10G Base-LR Vendor: Yamaha PID : YSFP-10G-LR VID : V1.0 SN : Z5H00001YJ Yamaha>
4.2 Showing operating information
The following shows the system operating status.
Yamaha>show environment SWP2 BootROM Ver.1.00 SWP2 Rev.2.03.01 (Fri Sep 7 00:00:00 2018) main=SWP2 ver=00 serial=S00000000 MAC-Address=ac44.f200.0000 CPU: 7%(5sec) 8%(1min) 8%(5min) Memory: 18% used Startup firmware: exec0 Configration mode: DANTE VLAN preset: Normal Serial Baudrate: 9600 Boot time: 2018/10/01 06:14:46 +00:00 Current time: 2018/10/01 06:49:23 +00:00 Elapsed time from boot: 0days 00:34:41 Yamaha>
4.3 Showing technical support information
The following shows technical support information.
Yamaha#show tech-support # # Information for Yamaha Technical Support # *** show running-config *** ! ! - Running Configuration - ! Current Time: Fri Jan 1 00:00:00 JST 2021 ! dns-client enable ! vlan database vlan 2 name VLAN0002 vlan 3 name VLAN0003 ! interface port1.1 switchport switchport mode access ... *** show startup-config *** ... *** show environment *** ... *** show disk-usage *** ... *** show dipsw *** ... ... ... # # End of Information for Yamaha Technical Support #
5 Points of Caution
None
6 Related Documentation
None
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
- System self-diagnostic
System self-diagnostic
1 Function Overview
This product includes system self-diagnostic function.
The system self-diagnostic function detects the following types of errors.
- Startup process errors
- Hardware component errors
- Interface (Ethernet port)
- RTC
- SFP
2 Definition of Terms Used
Real-time clock (RTC)
Device used to manage time
Packet processor
Device used to process packets.
3 Function Details
3.1 Diagnostics
Three types of system self-diagnostic functionality, either bootup diagnostics, on-demand diagnostics, or health monitoring diagnostics, are available depending on when diagnostics are performed.
The features of each type are indicated below.
- Bootup diagnostics
- Automatically executed whenever the system starts up.
- Detects startup process errors and hardware component errors (RTC, etc.).
- On-demand diagnostics
- Can be executed at user-specified times set using the system-diagnostics on-demand execute command.
- Detects hardware component (interface) errors.
- All ports are shut down during diagnostics and the system is rebooted when finished.
- Health monitoring diagnostics
- Running continuously in the background during system operation.
- Detects hardware component (SFP) errors.
- Health monitoring diagnostic results are displayed via the GUI and LED indicators (only some test results are indicated via the LED indicators).
Each diagnosis runs multiple tests. The tests performed for each diagnosis are indicated below.
For a detailed list of tests performed, refer to 4 Test Details.
| Test Type | Bootup diagnostics | On-demand diagnostics | Health monitoring diagnostics |
|---|---|---|---|
| Loading Test | ✓ | ||
| RTC Test | ✓ | ||
| Packet Processor Test | ✓ | ||
| PHY Test | ✓ | ||
| SFP Test | ✓ |
3.2 Diagnostic results displayed
Diagnostic results can be checked using the show system-diagnostics command.
Though the system is automatically rebooted after on-demand diagnostics, diagnostic results can be confirmed after rebooting.
3.3 Deleting on-demand diagnostic results
On-demand diagnostic results can be deleted using the clear system-diagnostics on-demand command.
4 Test Details
Details about each test item are indicated below.
4.1 Loading test
This verifies the software module loading status.
A “Pass” result is output if all modules are successfully loaded, whereas a “Fail” result is output if even one module fails to load.
The show system-diagnostics command does not indicate information about modules that failed to load.
To identify which module failed to load, use the show logging command to search the following log. Note: In this example, the module name is indicated by “XXXX” characters.
[ HAMON]:err: An unexpected error has occurred. (XXXX deamon)
4.2 RTC test
This verifies access to the RTC register.
A time value is obtained from the RTC two times, resulting in “Pass” if the time value changed or “Fail” if the time values are identical.
A “Fail” result also occurs if the test fails to obtain a time value from the RTC (or load the register).
4.3 Packet processor test
This verifies access to the packet processor register.
A “Pass” result occurs if the value written in the packet processor register matches the loaded value, whereas a “Fail” result occurs if the values do not match.
A “Fail” result also occurs if the test fails to access the register.
4.4 PHY test
This verifies access to the PHY register.
A “Pass” result occurs if the value written in the PHY register matches the loaded value, whereas a “Fail” result occurs if the values do not match.
A “Fail” result also occurs if the test fails to access the register.
4.5 SFP test
This monitors the SFP module optical input level.
It generates a warning if the optical input level exceeds a certain range.
5 Related Commands
Related commands are indicated below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Display system self-diagnostic results | show system-diagnostics |
| Execute on-demand diagnostics | system-diagnostics on-demand execute |
| Delete on-demand diagnostic results | clear system-diagnostics on-demand |
6 Examples of Command Execution
6.1 Displaying system self-diagnostic results
- Check the system self-diagnostic results as follows.
Yamaha#Test results: (P = Pass, F = Fail, U = Untested, N = Normal, W = Warning) - Bootup Loading Test: Pass RTC Test: Pass Packet Processor Test: Pass - On-demand Last on-demand diagnostics information: Date : 2021/07/07 09:00:00 +00:00 BootROM : Ver.1.01 Firmware : Rev.2.03.14 PHY Test: Port 1 2 3 4 5 6 7 8 9 10 -------------------------------------------- P P P P P P P P P P - Health monitoring SFP Test: Port 11 12 ------------ N N
6.2 Executing on-demand diagnostics
- Execute on-demand diagnostics as follows.
Yamaha#system-diagnostics on-demand execute The system will be rebooted after diagnostics. Continue ? (y/n) y on-demand diagnostics completed (pass). reboot immediately...
6.3 Deleting on-demand diagnostic results
- Delete on-demand diagnostic results as follows.
Yamaha#clear system-diagnostics on-demand
7 Points of Caution
- All ports are automatically shut down and rebooted whenever on-demand diagnostics is executed. Therefore, use particular caution before executing on-demand diagnostics while the system is being operated.
- If online diagnostics is executed remotely, such as via Telnet or the web console, simplified results cannot be displayed before rebooting because all ports are shut down during diagnostics. Use the show system-diagnostics command to check diagnostic results after rebooting.
8 Related Documentation
None
Cable diagnostics
1 Function Overview
The cable diagnostic function can be used to easily check whether or not the LAN cable connected to the LAN port has a faulty connection/circuit.
It can be used to troubleshoot network problems or as an easy way to check cables when setting up networks.
2 Definition of Terms Used
TDR (Time Domain Reflector)
The TDR is used to measure the length of LAN cables or the location of damage based on the reflected signals from a pulse signal sent through the LAN cables.
3 Function Details
3.1 How to diagnose cables
The cable diagnostic function can easily diagnose LAN cables using the time domain reflection (TDR) method.
Cable diagnostics is started by executing the cable-diagnostics tdr execute interface command.
If the show cable-diagnostics tdr command is executed after the diagnostics process is finished, the following diagnostic results are displayed.
| Item | Description |
|---|---|
| Cable status | The following cable states can be detected. ・ OK: The cable is electrically connected. ・ Open: Either no device is connected on the opposite end or the cable is faulty. ・ Short: A short circuit occurred. Results are displayed for each pair. |
| Distance to cable fault | If the cable status is “Open” or “Short”, then the distance to the fault is displayed. Results are displayed for each pair. |
Results from executing cable diagnostics the previous time can be checked using the show cable-diagnostics tdr command.
Only the immediately previous diagnostic results are retained and then overwritten the next time the cable diagnostics command is executed again.
The immediately previous results can be deleted using the clear cable-diagnostics tdr command.
4 Related Commands
Related commands are indicated below.
For command details, refer to the command reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Execute cable diagnostics | cable-diagnostics tdr execute interface |
| Display cable diagnostics | show cable-diagnostics tdr |
| Clear cable diagnostic results | clear cable-diagnostics tdr |
The following commands included in smart switches can be used in the same way as the commands above.
- test cable-diagnostics tdr interface
- show test cable-diagnostics tdr
- clear test cable-diagnostics tdr
5 Examples of Command Execution
5.1 Executing cable diagnostics
Diagnose of the LAN cable connected to port 1.1 as follows.
Yamaha# test cable-diagnostics tdr interface port1.1 The port will be temporarily down during test. Continue? (y/n): y % To check result, enter “show cable-diagnostics tdr”
5.2 Checking previous diagnostic results
Display the previous diagnostic results as follows.
Yamaha# show test cable-diagnostics tdr
Last run on Tue May 31 18:12:13 2022
Port Pair Status Fault distance
-------------------------------------------
port1.1 1 OK -
2 OK -
3 Open 15 m
4 Open 15 m
6 Points of Caution
- This function performs simplified diagnostics. Note that it cannot be used to for precision diagnosis of more specialized equipment.
- Cables 10 m or longer can be diagnosed. Cables shorter than 10 m cannot be diagnosed in some cases.
- Communication is temporarily stopped during cable diagnostics.
- Diagnostics cannot be performed if a shutdown command is specified for a corresponding port or the port is shut down either because a loop was detected or for any other reason.
- Diagnostics cannot be performed properly in some cases if the port on the opposite end is linked at a speed less than 1 Gbps.
- Diagnostics cannot be performed properly if PoE power is supplied at a corresponding port.
- If a stack is configured, commands cannot be executed from member switches in the stack.
7 Related Documentation
- None
Config management
1 Function Overview
This product uses the following config information to maintain the value of settings.
Table 1.1 Config types
| Config type | Description | User operations possible |
|---|---|---|
| Running config (running-config) | The currently-running setting values. Managed in RAM. | Refer to Save to startup config (in USER mode) Save some functions to backup config (in DANTE mode) |
| Startup config (startup-config) | In USER mode, the setting values saved in ROM. In Dante mode, the same setting values as the default config. | Refer to Update by running config (in USER mode) |
| Backup config (backup-config) | Setting values for some functions saved in DANTE mode. Managed in ROM. | Update by running config (in DANTE mode) |
| Default config (default-config) | The default setting values. Managed in ROM. Created based on the VLAN preset that is selected by the settings of DIP switches #2/#3 at startup. | No operations possible |
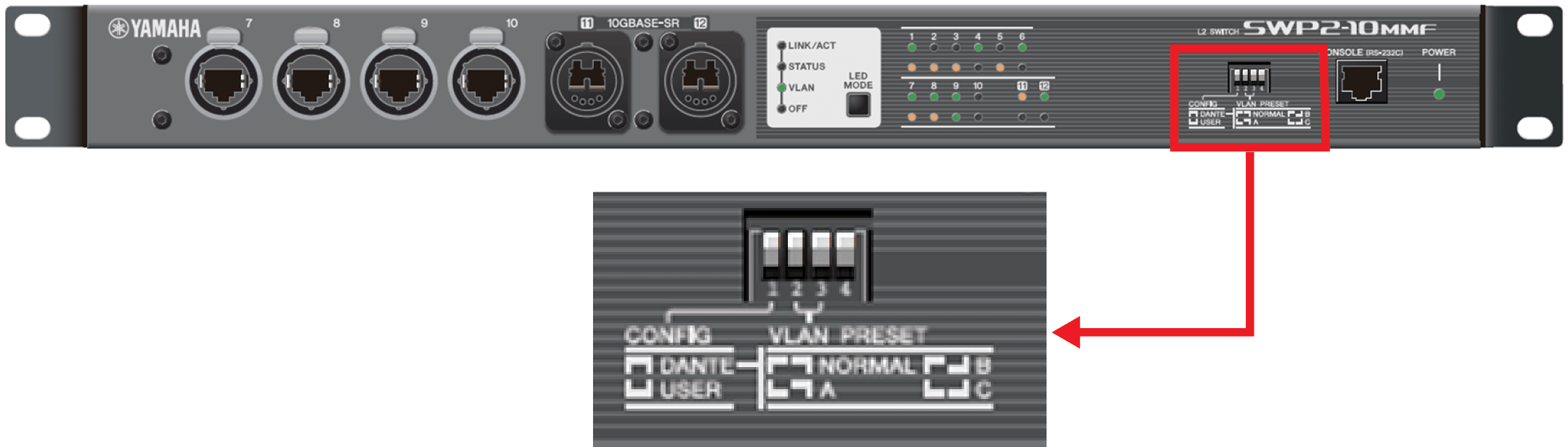
This product is equipped with a four-switch DIP switch .
Each switch is assigned a function, and by setting the switches beforehand, the operation of this product can be modified without using commands from a PC or changing settings in the GUI.
The functions assigned to the DIP switches cannot be changed using commands or the GUI.
2 Definition of Terms Used
- CONFIG mode
This specifies the mode when this product starts up.
3 Function Details
3.1 Running config
running-config is the settings that are currently operating; since it is maintained in RAM, it is destroyed at reboot.
On this product, commands executed in configuration mode are immediately applied to running-config, and the unit operates according to these settings.
The contents of running-config can be viewed by using the show running-config command.
3.2 Startup config
startup-config is settings that are saved in Flash ROM, and the contents are preserved through reboot.
When this product is started, the settings of startup-config are applied as the initial settings of running-config.
If you attempt to start up in a state where startup-config does not exist, such as after executing the cold start command, the default-config is automatically applied.
If operating in USER mode, the settings of running-config can be saved to startup-config by using the copy running-config startup-config command or the write command.
The contents of startup-config can be erased by the erase startup-config command or viewed by the show startup-config command.
If operating in DANTE mode, some of the settings of running-config can be saved by the backup-config command.
The contents of startup-config can be erased by the erase startup-config command or viewed by the show startup-config command.
3.3 Default config
default-config contains settings saved in internal Flash ROM that are needed for this product to operate minimally as a switch. Like startup-config, the contents are preserved even after a restart.
The factory settings are maintained as default-config.
If startup-config does not exist when the system starts, default-config is copied to startup-config, and applied to running-config.
The contents of default-config cannot be viewed.
3.4 DIP switch control
The functions assigned to the DIP switches are as follows.
The settings of the DIP switches are applied to the various functions when this product starts up. If the DIP switch settings are changed after this product starts up, they take effect at next startup.
With the factory settings, the DIP switches are all set to the “ up (OFF)” position.
3.4.1 DIP switch #1: Select CONFIG mode
Selects the CONFIG mode as either DANTE mode or USER mode.
Table 3.1 DIP switch #1 settings
| Setting position | Content of setting |
|---|---|
| Up (OFF) | Start up in DANTE mode. |
| Down (ON) | Start up in USER mode. |
- Operation when DANTE mode is selected
When the system starts up, it always boots with the preset specified by DIP switches #2/#3.
If the system booted in DANTE mode, the settings cannot be savedby using the copy or write commands.
However, settings that are necessary for maintenance, such as the IPv4 address, can be saved using the backup-config command. (For details, refer to the Command Reference.)
- Operation when USER mode is selected
Only when the system starts up for the first time (or after initialization), it boots with the preset specified by DIP switches #2/#3.
If the system booted in USER mode, the settings can be savedby using the copy or write commands.
In this mode, data saved by the user can be used.
3.4.2 DIP switch #2/#3: Select preset
These select the VLAN preset at system boot.
Applying the preset to the system depends on the setting of DIP switch #1.
For specific preset setting values, refer to Maintenance and operation functions: List of SWP2 preset settings.
Table 3.2 DIP switch #2/#3 settings
| Setting position | VLAN preset type | |
|---|---|---|
| #2 | #3 | |
| Up (OFF) | Up (OFF) | Normal |
| Down (ON) | Up (OFF) | A |
| Up (OFF) | Down (ON) | B |
| Down (ON) | Down (ON) | C |
3.4.3 DIP switch #4
No functions are allocated to this switch at present.
3.5 Controlling the config file via TFTP
If this product’s TFTP server function is enabled, a TFTP client installed on a PC or other remote terminal can be used to perform the following.
- Acquire the currently running running-config and startup-config
- Apply a previously prepared settings file as startup-config
In order for the TFTP server to function correctly, an IP address must be specified for the VLAN.
Acquisition and settings of the settings file from the remote terminal is done in binary mode, specifying the following as the remote path for acquiring or sending the settings file.
Also, specify the administrative password in the form “/PASSWORD” appended to the end of the remote path.
However, the config file cannot be obtained or specified if the default administrative password is still specified. The administrative password setting must be changed in advance.
The startup-config settings are applied as running-config after the system is restarted.
Table 3.3 Remote path for applicable files (No automatic restart)
| Target CONFIG | Target file | Remote path | Get (GET) | Setting (PUT) | Automatic restart |
|---|---|---|---|---|---|
| running-config | CONFIG file (.txt) | config | ✓ | ✓ | - |
| startup-config for USER mode | CONFIG file (.txt) | config0 | ✓ | ✓ | - |
| All settings (.zip) | config0-all | ✓ | ✓ | - | |
| startup-config for DANTE mode | CONFIG file (.txt) | config1 | ✓ | - | - |
| All settings (.zip) | config1-all | ✓ | - | - |
If you want to restart the system automatically after applying the CONFIG file, specify the following remote path.
The currently running configuration is applicable.
Table 3.4 Remote path for applicable files (with automatic restart)
| Target CONFIG | Target file | Remote path | Get (GET) | Setting (PUT) | Automatic restart |
|---|---|---|---|---|---|
| Currently running startup-config (USER mode only) | CONFIG file (.txt) | reconfig | - | ✓ | ✓ |
| All settings (.zip) | reconfig-all | - | ✓ | ✓ |
When applying (PUT) a CONFIG file, confirm that the target CONFIG and the type of the target file are correct.
If an incorrect file is specified, it cannot be reflected correctly.
In the case of running-config, it is necessary to add the following at the start of the CONFIG file.
! ! Switch Configuration !
4 Related Commands
The related commands are shown below.
For details, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Save running config | copy running-config startup-config |
| Save running config | write |
| Back up applicable functions | backup-config |
| Erase startup config | erase startup-config |
| Erase backup of applicable functions | erase backup-config |
| Show startup config | show startup-config |
| Show backup config | show backup-config |
5 Examples of Command Execution
5.1 Save running config
Save running-config.
Yamaha#copy running-config startup-config Succeeded to write configuration Yamaha#
Yamaha# write Succeeded to write configuration Yamaha#
5.2 Erase startup config
Erase startup config.
Yamaha#erase startup-config Succeeded to erase configuration Yamaha#
5.3 Show startup config
Show startup config.
Yamaha#show startup-config ! ! Default Configuration (SWP2) ! qos enable qos dscp-queue 0 0 qos dscp-queue 1 0 ...
6 Points of Caution
None
7 Related Documentation
None
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
- Remote access control
Remote access control
1 Function Overview
This product lets you restrict access to the following applications that implement network services.
- TELNET server
- SSH server
- HTTP server / secure HTTP server
- TFTP server
- SNMP server
2 Definition of Terms Used
None
3 Function Details
The following four functions are provided to limit access to network services.
- Control whether to leave the service in question running in the background on the system (start/stop control)
- Change reception port number
- Limit access destinations for services currently running
- Limit the source IP addresses that can access services currently running
The following functions that correspond to each network service are shown in the table below.
Network service access control
| Network service | Start/stop control | Change reception port number | Limit access destinations | Limit access sources |
|---|---|---|---|---|
| TELNET server | ✓ | ✓ | ✓ | ✓ |
| SSH server | ✓ | ✓ | ✓ | ✓ |
| HTTP server Secure HTTP server | ✓ | ✓ | ✓ | ✓ |
| TFTP server | ✓ | ✓ | ✓ | - |
| SNMP server | -(Always booted) | -(Always 161) | - | ✓ |
- Multiple instances of a network service cannot be started.
If the start control is applied to the same service that is currently running, the service will restart. Any connected sessions will be disconnected as a result.
- Limiting access destinations for network services is done for the VLAN interface.
- Limiting access sources for network services is done by specifying access source IP addresses and whether to permit or deny access.
- The default settings for the network services are shown in the table below.
Network service Start/stop status Reception port number Access destination restriction Access source restriction TELNET server run 23 Only default management VLAN (VLAN #1) permitted Allow all SSH server stop 22 Only default management VLAN (VLAN #1) permitted Allow all HTTP server run 80 Only default management VLAN (VLAN #1) permitted Allow all Secure HTTP server stop 443 TFTP server stop 69 Only default management VLAN (VLAN #1) permitted Allow all SNMP server run 161 Allow all Allow all
4 Related Commands
Related commands are shown below.
For details, refer to the Command Reference.
List of related commands
| Network service | Operations | Operating commands |
|---|---|---|
| Common | Management VLAN | management interface |
| TELNET server | Start/stop | telnet-server |
| Change reception port number | telnet-server enable (use argument to specify port number) | |
| Access control | telnet-server interface | |
| IP address access control | telnet-server access | |
| Show settings | show telnet-server | |
| SSH server | Start/stop | ssh-server |
| Change reception port number | ssh-server enable (use argument to specify port number) | |
| Access control | ssh-server interface | |
| IP address access control | ssh-server access | |
| Check whether client is alive | ssh-server client alive | |
| Show settings | show ssh-server | |
| Generate host key | ssh-server host key generate | |
| Clear host key | clear ssh-server host key | |
| Show public key | show ssh-server host key | |
| HTTP server | Start/stop HTTP server | http-server |
| Change HTTP server reception port number | http-server enable (use argument to specify port number) | |
| Start/stop secure HTTP server | http-server secure | |
| Change secure HTTP server reception port number | http-server secure enable (use argument to specify port number) | |
| Access control | http-server interface | |
| IP address access control | http-server access | |
| Show settings | show http-server | |
| TFTP server | Start/stop | tftp-server |
| Access control | tftp-server interface | |
| SNMP server | Access control by IP address and community name | snmp-server access |
5 Examples of Command Execution
5.1 TELNET server access control
This example restricts access to the TELNET server.
Change the TELNET server’s reception port to 1024.
Change the management VLAN to VLAN #1000 and allow access. Access from other than the management VLAN is denied.
Access to the TELNET server is allowed only for a client from 192.168.100.1.
If you specify telnet-server access, access from IP addresses that do not meet the conditions is denied.
Yamaha(config)#telnet-server enable 1024 ... (Change reception port to 1024, and restart the TELNET server)
Yamaha(config)#management interface vlan1000 ... (Permit access for VLAN #1000 as a management VLAN)
Yamaha(config)#telnet-server access permit 192.168.100.1 ... (Permit access only from 192.168.100.1) Yamaha(config)
Yamaha(config)#end
Yamaha#show telnet-server ... (Confirm status of settings)
Service:Enable
Port:1024
Management interface(vlan):1000
Interface(vlan):None
Access:
permit 192.168.100.1
5.2 SSH server access control
This example restricts access to the SSH server.
Generate the SSH server host key.
Register a user name and password.
Login from an SSH client is possible only for a registered user and password.
Change the SSH server’s reception port to 1024.
Change the management VLAN to VLAN #1000 and allow access for VLAN #2.
This allows access only from the management VLAN VLAN #1000 and from VLAN #2.
If you specify ssh-server access, access from IP addresses that do not meet the conditions is denied.
Yamaha#ssh-server host key generate ... (Generate host key) Yamaha#show ssh-server host key ... (Check contents of key) ssh-dss (Omitted) ssh-rsa (Omitted) Yamaha# Yamaha#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Yamaha(config)#username user1 password pw1 ... (Register user name and password) Yamaha(config)#ssh-server enable 1024 ... (Change reception port to 1024, and restart SSH server) Yamaha(config)#management interface vlan1000 ... (Allow access for #1000 as management VLAN) Yamaha(config)#ssh-server interface vlan2 ... (Allow access for VLAN #2) Yamaha(config)#end Yamaha#show ssh-serverr ... (Check status of settings) Service:Enable Port:1024 Hostkey:Generated Client alive :Disable Management interface(vlan):1000 Interface(vlan):2 Access:None Yamaha#
5.3 HTTP server access restriction
This example makes it possible to restrict HTTP server access.
The HTTP server reception port is changed to 8000, and access is permitted from VLAN #2.
This allows access only from the default management VLAN VLAN #1 and from VLAN #2.
Access to the HTTP server is allowed only for a client from 192.168.100.1.
If you specify http-server access, access from IP addresses that do not meet the conditions is denied.
Yamaha(config)#http-server enable 8000 ... (Change reception port to 8000, and restart the HTTP server)
Yamaha(config)#http-server interface vlan2 ... (Permit access for VLAN #2)
Yamaha(config)#http-server access permit 192.168.100.1 ... (Permit access only from 192.168.100.1)
Yamaha(config)#end
Yamaha#show http-server ... (Check status of settings)
HTTP :Enable(8000)
HTTPS:Disable
Management interface(vlan):1
Interface(vlan):2
Access:
permit 192.168.100.1
5.4 TFTP server access restriction
This example restricts TFTP server access.
The TFTP server reception port is changed to 2048, and access is permitted from VLAN #10.
Allow access only from the default management VLAN VLAN #1 and from VLAN #10.
Yamaha(config)#tftp-server enable 2048 ... (Change reception port to 2048, and restart the TFTP server) Yamaha(config)#tftp-server interface vlan10 ... (Permit access for VLAN #10)
5.5 SNMP server access restrictions
This restricts access to the SNMP server.
Access to “public” communities is restricted to clients from 192.168.100.0/24.
In addition, access to “private” communities is restricted to clients from 192.168.100.1.
Yamaha(config)#snmp-server access permit 192.168.100.0/24 community public ... (Access to communities named “public” is only allowed from 192.168.100.0/24) Yamaha(config)#snmp-server access permit 192.168.100.1 community private ... (Access to communities named “private” is only allowed from 192.168.100.1)
6 Points of Caution
If the password (admin) for the default administrative user admin is left unchanged, then the following restrictions are applied.
- Switches cannot be accessed by TELNET, SSH, HTTP, or HTTPS from a network segment other than the maintenance VLAN.
The following restrictions apply if a TFTP server is accessed from a TFTP client.
- Access is denied if the special privileged access password (administrative password) is still set to the default setting. Special privileged access passwords (administrative passwords) must be changed in advance.
- If the IPv4 primary and IPv4 secondary addresses for a VLAN being accessed are the same segment, then the IPv4 secondary address cannot be accessed.
- If accessing the VLAN with an IPv6 address, then only the IPv6 address specified last can be accessed.
Because the internal address is reset if the switch is started, that means only the bottom IPv6 address listed in the order they were configured can be accessed.
- Only the IP address of the VLAN with the closest routing to the TFTP client can be accessed.
For example, a TFTP client located on VLAN 1 cannot access VLAN 2 IP addresses for the switch.
7 Related Documentation
Time management
1 Function Overview
This product provides the functions shown below for managing the date and time.
- Manual (user-configured) date/time information setting function
- Automatic date/time setting information function via network
- Time zone setting function
- Function for setting “summer time” (or “daylight saving time” (DST) or “daylight time”) settings
2 Definition of Terms Used
UTC (Coordinated Universal Time)
This is an official time used when recording worldwide times.
UTC is used as a basis to determine standard time in all countries around the world.
For instance, Japan (JST, or Japan standard time) is nine hours ahead of Coordinated Universal Time, and is thus shown as “+0900 (JST)”.
SNTP (Simple Network Time Protocol)
This is a simple protocol to correct clocks by using SNTP packets.
This protocol is defined in RFC4330.
3 Function Details
3.1 Manually setting the date and time
Use the clock set command to directly enter clock setting values.
3.2 Automatically setting the date and time
Date and time information is collected from a specified time server, and set in this product.
Defined in RFC4330, SNTP (Simple Network Time Protocol) is used as a communication protocol.
Up to two time servers can be specified using either an IPv4 address, IPv6 address, or a fully qualified domain name (FQDN).
Port number 123 is used for the SNTP client. (This setting cannot be changed by the user.)
The ntpdate command can be used to select one of two methods for automatically setting date and time settings.
- One-shot update (a function to update when a command is inputted)
- Interval update (a function to update in a 1–24-hour cycle from command input)
If clock settings are synchronized with two time servers specified, queries are processed in the order they are displayed by the show ntpdate command, which is NTP server 1 and then NTP server 2.
Queries to NTP server 2 are only processed if synchronization with NTP server 1 fails.
Given default settings, one hour is specified as the interval update cycle.
However, when the default time cannot be set right after booting up the system, the time server will be queried in a one-minute cycle, regardless of the interval cycle time.
Synchronization with the time server operates with one sampling (the frequency of replies from the server) and with a timeout of 1 second.
Synchronization is blocked during command execution, and an error message is outputted if a timeout occurs.
3.3 Time zone settings
In order to manage the time for the region considered as the “base of daily life”, the “clock timezone” command is used to manage the time zone of the users, and reflect this into the time.
The time zone can be set in ±1 hour increments for Coordinated Universal Time (UTC), from -12 hours to +13 hours.
The default time zone value for this product is +9.0.
3.4 Summer time setting
Users can set “summer time” (or “daylight saving time” (DST) or “daylight time”) settings using the clock summer-time command.
The following parameter settings are specified.
- Time zone name
The time zone name is displayed when summer time is in effect.
- Summer time starting and ending times
The following two methods can be used to specify time setting values.
- Recurring
If summer time occurs every year for the same period, then this specifies the week and day of the month it occurs.
- Specific dates
This specifies the specific dates summer time is applied.
- Recurring
- Offset
This specifies how long (minutes) to extend the summer time period.
The setting range is from 1 to 1,440 minutes. The setting value is 60 minutes unless specified otherwise.
Overlapping summer time periods cannot be specified.
Summer time settings can be checked using the show clock detail command.
4 Related Commands
Related commands are shown below.
For details, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Set clock manually | clock set |
| Set time zone | clock timezone |
| Set summer time settings (recurring) | clock summer-time recurring |
| Set summer time settings (specific date) | clock summer-time date |
| Show current time | show clock |
| Set NTP server | ntpdate server |
| Synchronize time from NTP server (one-shot update) | ntpdate oneshot |
| Synchronize time from NTP server (update interval) | ntpdate interval |
| Show NTP server time synchronization settings | show ntpdate |
5 Examples of Command Execution
5.1 Manually setting the time
In this example, the time zone is set to JST and the current time is set to 2014.01.21 15:50:59.
Yamaha#configure terminal Yamaha(config)#clock timezone JST … (Set time zone) Yamaha(config)#exit Yamaha#clock set 15:50:59 Jan 21 2014 … (Set time) Yamaha#show clock … (Show current time) 15:50:59 JST Tue Jan 21 2014
5.2 Automatically setting the time
In this example, the time zone is set to +9.00 and the local address 192.168.1.1 and ntp.nict.jp are specified as the NTP servers.
Also, the NTP server update cycle is changed to once every 24 hours.
Yamaha#configure terminal Yamaha(config)#clock timezone +9:00 … (Set time zone) Yamaha(config)#ntpdate server ipv4 192.168.1.1 … (Set NTP server) Yamaha(config)#ntpdate server name ntp.nict.jp … (Set NTP server) Yamaha(config)#ntpdate interval 24 … (Set NTP server update cycle to 24 hours) Yamaha(config)#exit Yamaha#show clock … (Show current time) 10:03:20 +9:00 Mon Dec 12 2016 Yamaha#show ntpdate … (Show NTP time synchronization settings) NTP server 1 : 192.168.100.1 NTP server 2 : ntp.nict.jp adjust time : Mon Dec 12 10:03:15 2016 + interval 24 hours sync server : 192.168.100.1
5.3 Summer time setting
5.3.1 Recurring
In this example, summer time is set to occur every year starting from 2 AM on the second Sunday of March to 2 AM on the first Sunday of November.
Yamaha#configure terminal Yamaha(config)#clock summer-time JDT recurring 2 Sun Mar 2:00 1 Sun Nov 2:00 … (Set summer time settings) Yamaha(config)#exit Yamaha#show clock detail … (Check summer time settings) Fri Jan 1 00:00:20 JST 2021 Summer Time Type : Recurring Offset : 60 (min) From : Sun Mar 14 02:00:00 JST 2021 … (Show the specific date settings for the next (or current) summer time period) To : Sun Nov 7 02:00:00 JDT 2021
5.3.2 Specific dates
In this example, the settings specify starting summer time at 2 AM on March 14, 2021, and ending it on November 7, 2021.
Yamaha#configure terminal Yamaha(config)#clock summer-time JDT date Mar 14 2021 2:00 Nov 7 2021 2:00 … (Set summer time settings) Yamaha(config)#exit Yamaha#show clock detail … (Check summer time settings) Fri Jan 1 00:02:54 JST 2021 Summer Time Type : Date Offset : 60 (min) From : Sun Mar 14 02:00:00 JST 2021 To : Sun Nov 7 02:00:00 JDT 2021
6 Points of Caution
None
7 Related Documentation
SNMP
1 Function Overview
Setting SNMP (Simple Network Management Protocol) makes it possible to monitor and change network management information for SNMP management software.
In this instance, this product will operate as an SNMP agent.
This product supports communication using SNMPv1, SNMPv2c, and SNMPv3. In terms of management information bases (MIB), it supports RFC1213 (MIB-II) and private MIBs (Yamaha switches).
SNMPv1 and SNMPv2 protocols send notification of the group name (referred to as a “community”) to recipients and only communicate between hosts that belong to that same community. In that case, different community names can be specified for two access modes, either the read-only or read-write mode.
In this way, community names function as a kind of password, but they carry inherent security risks because they must be sent over a network using plain text. The use of SNMPv3 is recommended when more secure communications are required.
SNMPv3 offers communication content authentication and encryption. SNMPv3 improves security by eliminating the concept of community and instead using so-called “security models”, including the user-based security model (USM) and view-based access control model (VACM).
SNMP messages that notify the status of this product are called “traps.” This product transmits standard SNMP traps. In SNMPv1, trap requests that do not ask for an answer with the confirmation of receipt from the recipient are specified as the notification message format. However, with SNMPv2c and SNMPv3, either an “inform” request asking for an answer from the recipient, or a trap request can be selected.
Since this product does not specifically specify a default community name value for read-only and transmission traps used for SNMPv1 and SNMPv2c protocols, be sure to specify an appropriate community name. However, as described above, community names are sent over the network in plain text, so be careful to never use a login password or administrator password as the community name.
By default, no access is possible in each SNMP version. The transmission host for the trap is not set, so traps will not be sent anywhere.
This product can restrict access to the SNMP server. Specifying access restrictions can restrict access from unintended hosts.
2 Definition of Terms Used
None
3 Function Details
The main characteristics of each SNMP version and the router setting policies are explained below.
For specific examples of settings, see 5 Examples of Command Execution below.
3.1 SNMPv1
Community names are used for authentication between the SNMP manager and agents.
Switches managed by SNMPv1 are managed by dividing them into zones, referred to as “communities”.
- Accessing the MIB objects
Community names specified using the snmp-server community command are used to permit access.
Access is possible from a VLAN interface whose IP address has been specified.
- SNMP traps
The status of switches can be sent to hosts specified using the snmp-server host command.
The snmp-server enable trap command is used to specify the kind of trap to send.
The snmp-server startup-trap-delay command is used to specify when to send the trap during startup.
3.2 SNMPv2c
As with SNMPv1, community names are used for authentication between the SNMP manager and agents.
The snmp-server community command is used to specify the community names used to access switches by SNMPv2c.
The “GetBulk” and “Inform” requests are also now supported from this version.
These requests are used to efficiently retrieve multiple MIB objects, and to confirm replies to notification packets sent from this product.
- Accessing the MIB objects
Community names specified using the snmp-server community command are used to permit access.
Access is possible from a VLAN interface whose IP address has been specified.
- SNMP traps
The status of switches can be sent to hosts specified using the snmp-server host command.
Also, the settings of this command can be used to select whether the transmitted message format is a trap or inform request.
Inform requests are used to request confirmation of reply to the recipient.
The snmp-server startup-trap-delay command is used to specify when to send the trap during startup.
3.3 SNMPv3
SNMPv3 offers all the functionality of SNMPv2, but with more robust security functions.
SNMPv3 can authenticate and encrypt SNMP packets sent across the network to protect packets from eavesdropping, spoofing, falsification, replay attacks, and other risks and achieve security levels not possible with SNMPv1 or SNMPv2C functionality, such as community names or SNMP manager IP addresses.
- Security
SNMPv3 offers the following security functionality.
- USM (User-based Security Model)
USM is a model for maintaining security at the message level. It offers authentication and encryption based on shared key cryptography and prevents falsification of message streams.
- Security level
The security level can be specified using the parameter settings for the group to which users belong.
Security levels are classified based on a combination of authentication and encryption, as indicated below.
- noAuthNoPriv: no authentication and encryption
- AuthNoPriv: authentication only
- AuthPriv: authentication and encryption
- User authentication
For authentication, HMAC is used in the procedure to authenticate the integrity (whether data has been falsified or not) and the source.
A hash is used in the authentication key to confirm whether the message has been falsified, and whether the sender is the user themselves.
Both HMAC-MD5-96 and HMAC-SHA-96 are supported as hash algorithms.
- Encryption
With SNMPv3, SNMP messages are encrypted for the purpose of preventing leakage of managed information.
Both the DES-CBC and AES128-CFB encryption schemes are supported.
The snmp-server user command can be used to specify usernames, corresponding group names, user authentication methods, and encryption methods.
The necessary authentication and encryption settings can be made according to the security level specified in the group settings.
- Security level
- VACM (View-based Access Control Model)
VACM is a model for controlling access to SNMP messages.
- Group
With VACM, the access policies mentioned below are defined per group, not per user.
Use the snmp-server user command with the optional “group” setting to specify user group affiliation. The MIB views set here that are accessible to the specified groups can be configured.
- MIB view
With SNMPv3, a collection of accessible MIB objects can be defined for each group. When defined, the collection of MIB objects is called the “MIB view”. The “MIB view” is expressed as a collected view sub-tree that shows the object ID tree.
Use the snmp-server view command to specify the MIB view. Whether the MIB view should be included or excluded in each view sub-tree can be selected.
- Access policies
With VACM, set the MIB view that will permit reading and writing for each group.
Use the snmp-server group command to set the group name, security level, and MIB view.
The MIB view is the MIB view specified using the snmp-server view command.
- Group
- USM (User-based Security Model)
- SNMP traps
The status of switches can be sent to hosts specified using the snmp-server host command.
In order to transmit a trap, the snmp-server user command must first be used to configure the user.
Also, the settings of this command can be used to select whether the transmitted message format is a trap or inform request.
Inform requests are used to request confirmation of reply to the recipient.
The snmp-server startup-trap-delay command is used to specify when to send the trap during startup.
3.4 Restricting SNMP server access
Hosts able to access the product’s SNMP server can be specified using the snmp-server access command.
Access from unintended hosts can be restricted by only allowing access from the intended SNMP manager.
Default settings accept access from all hosts. Specify access restrictions based on the operating environment.
For more details about access restrictions, refer to Remote access control.
3.5 Private MIB
This product supports yamahaSW, which is a proprietary private MIB for switch management.
This private MIB allows the obtaining of information for Yamaha’s proprietary functions, and for more detailed information about the switch.
For information about supported private MIBs and how to obtain private MIBs, refer to the following SNMP MIB reference.
4 Related Commands
Related commands are indicated below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Set host that receives SNMP notifications | snmp-server host |
| Set how long to wait for notification messages to be transmitted when starting up the system. | snmp-server startup-trap-delay |
| Set notification type to transmit | snmp-server enable trap |
| Set system contact | snmp-server contact |
| Set system location | snmp-server location |
| Set SNMP communities | snmp-server community |
| Set SNMP view | snmp-server view |
| Set SNMP group | snmp-server group |
| Set SNMP user | snmp-server user |
| SNMP server access settings | snmp-server access |
| Show SNMP community information | show snmp community |
| Show SNMP view settings | show snmp view |
| Show SNMP group settings | show snmp group |
| Show SNMP user settings | show snmp user |
5 Examples of Command Execution
5.1 SNMPv1 setting example
This example makes SNMPv1-based network monitoring possible under the following conditions.
- Set the read-only community name “public.”
- Set the trap destination as “192.168.100.11”, and set trap community name to “snmptrapname”.
- Hosts that can access communities named “public” are restricted to only 192.168.100.0/24.
Yamaha(config)# snmp-server community public ro ... 1 Yamaha(config)# snmp-server host 192.168.100.11 traps version 1 snmptrapname ... 2 Yamaha(config)# snmp-server access permit 192.168.100.0/24 community public ... 3
5.2 SNMPv2c setting example
This example makes SNMPv2c-based network monitoring possible under the following conditions.
- Set the community name that enables reading/writing “private.”
- Specify the notification message destination as “192.168.100.12”, the notification type as “inform” request format, and the notification destination community name as “snmpinformsname”.
- Hosts that can access communities named “private” are restricted to only 192.168.100.12.
Yamaha(config)# snmp-server community private rw ...1 Yamaha(config)# snmp-server host 192.168.100.12 informs version 2c snmpinformsname ...2 Yamaha(config)# snmp-server access permit 192.168.100.12 community private ...3
5.3 SNMPv3 setting example
This example makes SNMPv3-based network monitoring possible under the following conditions.
- Specify the view that shows the internet node (1.3.6.1) and below as “most”.
- Specify the view that shows the mib-2 node (1.3.6.1.2.1) and below as “standard”.
- Create the user group “admins” and assign full access rights to the “most” view for all users in the “admins” group.
- Create the user group “users” and assign read-only access rights for the “standard” view to users in the “users” group.
- Create an “admin1” user that belongs to the “admins” group.
Set the password to “passwd1234”, using the “HMAC-SHA-96” authentication algorithm.
Set the encryption password to “passwd1234”, using the “AES128-CFB” encryption algorithm.
- Create an “user1” user that belongs to the “users” group.
Set the password to “passwd5678”, using the “HMAC-SHA-96” authentication algorithm.
- Send notifications in trap format (without response confirmation) to 192.168.10.3.
- Send notifications in inform request format to 192.168.20.3.
Yamaha(config)# snmp-server view most 1.3.6.1 include ... 1 Yamaha(config)# snmp-server view standard 1.3.6.1.2.1 include ... 2 Yamaha(config)# snmp-server group admins priv read most write most ... 3 Yamaha(config)# snmp-server group users auth read standard ... 4 Yamaha(config)# snmp-server user admin1 admins auth sha passwd1234 priv aes passwd1234 ... 5 Yamaha(config)# snmp-server user user1 users auth sha passwd5678 ... 6 Yamaha(config)# snmp-server host 192.168.10.13 traps version 3 priv admin1 ... 7 Yamaha(config)# snmp-server host 192.168.20.13 informs version 3 priv admin1 ... 8
6 Points of Caution
- Check the SNMP version that can be used with the SNMP manager beforehand. It is necessary to configure this product in accordance with the SNMP version that will be used.
- This product is not compatible with the following functions related to SNMPv3.
- Proxy function
- Access to MIB objects after the SNMPv2 subtree (1.3.6.1.6). Changing SNMPv3-related settings via SNMP is also not supported.
- Character string specifications for the community name, username, password, and group name are as follows.
- The character string indicated enclosed in single or double quotation marks is used.
- Cases with characters located outside single or double quotation marks are not supported.
- If a character string is enclosed in single or double quotation marks, the single or double quotation marks on both ends are not included in the character count.
- The group name is assigned to the character string used with the snmp-server user command.
- It is not assigned to the character string used with the snmp-server group command.
- The use of \ is not supported.
- The use of only single/double quotation marks is not supported.
- The character string indicated enclosed in single or double quotation marks is used.
- SNMP server access restrictions specified using the snmp-server access command only apply to SNMPv1 and SNMPv2c access. They do not apply to SNMPv3 access.
7 Related Documentation
RMON
1 Function Overview
By making settings for the RMON (Remote network MONitering) function, you can monitor and record the traffic volume and error occurrences for each interface.
Since the settings for the RMON function and the data obtained by the RMON function are held as an MIB, they can be retrieved and edited from the SNMP manager.
The RMON function of this product supports the following groups defined in RFC2819.
- Ethernet statistics group
- History group
- Alarm group
- Event group
2 Definition of Terms Used
- RMON MIB
MIB for the RMON function, defined in RFC2819
- Ethernet statistics group
MIB group defined as group 1 of the RMON MIB.
This holds a table for monitoring Ethernet statistical information.
The information in the table includes counters for the number of packets, the number of errors, etc.
The etherStatsTable is the applicable MIB for this product.
- History group
MIB group defined as group 2 of the RMON MIB.
At a specified interval, it measures the same information as the Ethernet statistical information group, and has a table for saving the history of this information.
The MIBs relevant for this product are the historyControlTable and the etherHistoryTable.
- Alarm group
MIB group defined as group 3 of the RMON MIB.
At the specified interval, the statistical information of the Ethernet statistical information group is compared with the threshold values.
If the sampled values exceed the threshold values, the event defined for the event group is generated.
The alarmTable is the applicable MIB for this product.
- Event group
MIB group defined as group 9 of the RMON MIB.
This is the action taken in response when the alarm group conditions are met.
The eventTable is the applicable MIB for this product.
3 Function Details
The operating specifications for operation of the RMON function are shown below.
3.1 Common between groups
The specifications common between groups are given below.
- In order to enable the RMON function on this product, the system-wide RMON function must be enabled.
- Use the rmon command to make settings.
- This is enabled by default.
- You can also set this by using the private MIB ysrmonSetting(1.3.6.1.4.1.1182.3.7.1).
3.2 Ethernet statistics group
The operating specifications for the Ethernet statistics group are given below.
- Make settings by using the rmon statistics command on an interface.
- Starting at the point at which you specified the rmon statistics command, statistical information is collected, and the etherStatsTable of the RMON MIB will be available for retrieval.
- This can be specified for a physical interface.
- A maximum of eight rmon statistics commands can be specified for the same interface.
- If an rmon statistics command is deleted, the collected statistical information is also deleted.
- If an rmon statistics command is overwritten, the previously collected statistical information is deleted, and collection is started once again.
- If the RMON function is disabled system-wide, collection of statistical information is halted.
If the RMON function is subsequently enabled system-wide, the previously collected statistical information is deleted, and collection is started once again.
- The supported OIDs in the Ethernet statistical information group are as follows.
rmon(1.3.6.1.2.1.16) +- statistics(1.3.6.1.2.1.16.1) +- etherStatsTable(1.3.6.1.2.1.16.1.1) + etherStatsEntry(1.3.6.1.2.1.16.1.1.1) { etherStatsIndex } +- etherStatsIndex(1.3.6.1.2.1.16.1.1.1.1) (read-only) +- etherStatsDataSource(1.3.6.1.2.1.16.1.1.1.2) (read-create) | Interface being monitored +- etherStatsDropEvents(1.3.6.1.2.1.16.1.1.1.3) (read-only) | Number of packets dropped +- etherStatsOctets(1.3.6.1.2.1.16.1.1.1.4) (read-only) | Number of octets received +- etherStatsPkts(1.3.6.1.2.1.16.1.1.1.5) (read-only) | Number of packets received +- etherStatsBroadcastPkts(1.3.6.1.2.1.16.1.1.1.6) (read-only) | Number of broadcast packets received +- etherStatsMulticastPkts(1.3.6.1.2.1.16.1.1.1.7) (read-only) | Number of multicast packets received +- etherStatsCRCAlignErrors(1.3.6.1.2.1.16.1.1.1.8)(read-only) | Number of FCS error packets received +- etherStatsUndersizePkts(1.3.6.1.2.1.16.1.1.1.9) (read-only) | umber of undersize packets received (packets smaller than 64 octets) +- etherStatsOversizePkts(1.3.6.1.2.1.16.1.1.1.10) (read-only) | Number of oversize packets received (packets larger than 1518 octets) +- etherStatsFragments(1.3.6.1.2.1.16.1.1.1.11) (read-only) | Number of fragment packets received (packets smaller than 64 octets with abnormal FCS) +- etherStatsJabbers(1.3.6.1.2.1.16.1.1.1.12) (read-only) | Number of jabber packets received (packets larger than 1518 octets with abnormal FCS) +- etherStatsCollisions(1.3.6.1.2.1.16.1.1.1.13) (read-only) | Number of collisions +- etherStatsOwner(1.3.6.1.2.1.16.1.1.1.20) (read-create) | Owner name +- etherStatsStatus(1.3.6.1.2.1.16.1.1.1.21) (read-create) Status of statistics group
3.3 History group
The operating specifications for the history group are shown below.
- Make settings by using the rmon history command on an interface.
- Starting at the point at which you specified the rmon history command, historical information is collected, and the etherHistoryTable of the RMON MIB will be available for retrieval.
- This can be specified for a physical interface.
- A maximum of eight rmon history commands can be specified for the same interface.
- If an rmon history command is deleted, the collected historical information is also deleted.
- If an rmon history command is overwritten, the previously collected historical information is deleted, and collection is started once again.
- If the RMON function is disabled system-wide, collection of historical information is halted.
If the RMON function is subsequently enabled system-wide, the previously collected historical information is deleted, and collection is started once again.
- The supported OIDs in the Ethernet history group are as follows.
rmon(1.3.6.1.2.1.16) +- history(1.3.6.1.2.1.16.2) +- historyControlTable(1.3.6.1.2.1.16.2.1) | + historyControlEntry(1.3.6.1.2.1.16.2.1.1) { historyControlIndex } | +- historyControlIndex(1.3.6.1.2.1.16.2.1.1.1) (read-only) | +- historyControlDataSource(1.3.6.1.2.1.16.2.1.1.2) (read-create) | | Interface being monitored | +- historyControlBucketsRequested(1.3.6.1.2.1.16.2.1.1.3)(read-create) | | Number of history control buckets requested for the history group | +- historyControlBucketsGranted(1.3.6.1.2.1.16.2.1.1.4) (read-only) | | Number of history control buckets for the history group | +- historyControlInterval(1.3.6.1.2.1.16.2.1.1.5) (read-create) | | Interval for saving the history of the history group | +- historyControlOwner(1.3.6.1.2.1.16.2.1.1.6) (read-create) | | Owner name | +- historyControlStatus(1.3.6.1.2.1.16.2.1.1.7) (read-create) | Status of history group | +- etherHistoryTable(1.3.6.1.2.1.16.2.2) + etherHistoryEntry(1.3.6.1.2.1.16.2.2.1) { etherHistoryIndex, etherHistorySampleIndex } +- etherHistoryIndex(1.3.6.1.2.1.16.2.2.1.1) (read-only) +- etherHistorySampleIndex(1.3.6.1.2.1.16.2.2.1.2) (read-only) +- etherHistoryIntervalStart(1.3.6.1.2.1.16.2.2.1.3) (read-only) | Interval for saving the history of the history group +- etherHistoryDropEvents(1.3.6.1.2.1.16.2.2.1.4) (read-only) | Number of packets dropped +- etherHistoryOctets(1.3.6.1.2.1.16.2.2.1.5) (read-only) | Number of octets received +- etherHistoryPkts(1.3.6.1.2.1.16.2.2.1.6) (read-only) | Number of packets received +- etherHistoryBroadcastPkts(1.3.6.1.2.1.16.2.2.1.7) (read-only) | Number of broadcast packets received +- etherHistoryMulticastPkts(1.3.6.1.2.1.16.2.2.1.8) (read-only) | Number of multicast packets received +- etherHistoryCRCAlignErrors(1.3.6.1.2.1.16.2.2.1.9)(read-only) | Number of FCS error packets received +- etherHistoryUndersizePkts(1.3.6.1.2.1.16.2.2.1.10)(read-only) | Number of undersize packets received (packets smaller than 64 octets) +- etherHistoryOversizePkts(1.3.6.1.2.1.16.2.2.1.11) (read-only) | Number of oversize packets received (packets larger than 1518 octets) +- etherHistoryFragments(1.3.6.1.2.1.16.2.2.1.12) (read-only) | Number of fragment packets received (packets smaller than 64 octets with abnormal FCS) +- etherHistoryJabbers(1.3.6.1.2.1.16.2.2.1.13) (read-only) | Number of jabber packets received (packets larger than 1518 octets with abnormal FCS) +- etherHistoryCollisions(1.3.6.1.2.1.16.2.2.1.14) (read-only) | Number of collisions +- etherHistoryUtilization(1.3.6.1.2.1.16.2.2.1.15) (read-only) Estimated network utilization
3.4 Alarm group
The operating specifications for the alarm group are shown below.
- Use the rmon alarm command to make settings.
- From the point that the rmon alarm command is specified, sampling occurs at the specified interval.
- If an rmon alarm command is overwritten, the previous sampling data is deleted, and sampling is started once again.
- If the RMON function is disabled system-wide, sampling is halted.
If the RMON function is subsequently enabled system-wide, the previous sampling data is deleted, and sampling is started once again.
- Only etherStatsEntry(.1.3.6.1.2.1.16.1.1.1) MIB objects that have a counter type can be specified as the object of alarm group monitoring.
- If the Ethernet statistical information group used by the rmon alarm command is deleted, the rmon alarm command is also deleted.
- If the event group used by the rmon alarm command is deleted, the rmon alarm command is also deleted.
- The supported OIDs in the alarm group are as follows.
rmon(1.3.6.1.2.1.16) +- alarm(1.3.6.1.2.1.16.3) +- alarmTable(1.3.6.1.2.1.16.3.1) + alarmEntry(1.3.6.1.2.1.16.3.1.1) { alarmIndex } +- alarmIndex(1.3.6.1.2.1.16.3.1.1.1) (read-only) +- alarmInterval(1.3.6.1.2.1.16.3.1.1.2) (read-create) | Sampling interval +- alarmVariable(1.3.6.1.2.1.16.3.1.1.3) (read-create) | MIB object being monitored +- alarmSampleType(1.3.6.1.2.1.16.3.1.1.4) (read-create) | Sampling type +- alarmValue(1.3.6.1.2.1.16.3.1.1.5) (read-only) | Monitored value +- alarmStartupAlarm(1.3.6.1.2.1.16.3.1.1.6) (read-create) | Threshold value used to determine first alarm +- alarmRisingThreshold(1.3.6.1.2.1.16.3.1.1.7) (read-create) | Upper threshold value +- alarmFallingThreshold(1.3.6.1.2.1.16.3.1.1.8) (read-create) | Lower threshold value +- alarmRisingEventIndex(1.3.6.1.2.1.16.3.1.1.9) (read-create) | Event index when upper threshold is passed +- alarmFallingEventIndex(1.3.6.1.2.1.16.3.1.1.10) (read-create) | Event index when lower threshold is passed +- alarmOwner(1.3.6.1.2.1.16.3.1.1.11) (read-create) | Owner name +- alarmStatus(1.3.6.1.2.1.16.3.1.1.12) (read-create) Status of alarm group
Alarm detection is determined by an upper threshold value and a lower threshold value. If the threshold value is crossed, the specified event is executed.
If an alarm is detected, the alarm will not be detected again until the value crosses the opposite threshold.
The following cases are explained as examples.
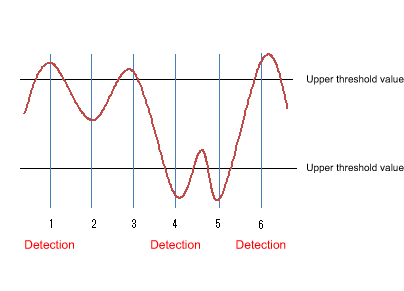
- At point 1, the upper threshold value is crossed, so an alarm is detected.
The threshold value that is used for the very first decision can be specified by STARTUP.
In the example above, we will assume that the STARTUP value is “1” (using only the upper threshold value (risingAlarm)) or “3” (using both the upper threshold value and the lower threshold value (risingOrFallingAlarm)).
- At point 2, an alarm is not detected.
- At point 3, the upper threshold value is crossed, but since the opposite threshold was not previously crossed, an alarm is not detected.
- At point 4, the lower threshold value is crossed, and since the upper threshold was previously crossed, an alarm is detected.
- At point 5, the lower threshold value is exceeded, but since the opposite upper threshold was not previously crossed, an alarm is not detected.
- At point 6, the upper threshold value is crossed, and since the lower threshold was previously crossed, an alarm is detected.
3.5 Event group
The operating specifications for the event group are shown below.
- Use the rmon event command to make settings.
- The following operations can be specified for the event group.
- Record to log
- Send SNMP trap
- Record to log and send SNMP trap
- If trap transmission is specified, the following SNMP commands must be set in order to transmit the SNMP trap.
- snmp-server host
- snmp-server enable trap rmon
- When trap transmission is specified, the following operations are performed.
- SNMPv1、SNMPv2c
- Traps are sent only to hosts whose community name specified by the rmon event command matches the community name specified by the snmp-server host command.
- SNMPv3
- Traps are sent only to hosts whose community name specified by the rmon event command matches the user name specified by the snmp-server host command.
- SNMPv1、SNMPv2c
- The supported OIDs in the event group are as follows.
rmon(1.3.6.1.2.1.16) +- event(1.3.6.1.2.1.16.9) +- eventTable(1.3.6.1.2.1.16.9.1) + eventEntry(1.3.6.1.2.1.16.9.1.1) { eventIndex } +- eventIndex(1.3.6.1.2.1.16.9.1.1.1) (read-only) +- eventDescription(1.3.6.1.2.1.16.9.1.1.2) (read-create) | Event description +- eventType(1.3.6.1.2.1.16.9.1.1.3) (read-create) | Type of event +- eventCommunity(1.3.6.1.2.1.16.9.1.1.4) (read-create) | Community name +- eventLastTimeSent(1.3.6.1.2.1.16.9.1.1.5) (read-only) | Event execution time +- eventOwner(1.3.6.1.2.1.16.9.1.1.6) (read-create) | Owner name +- eventStatus(1.3.6.1.2.1.16.9.1.1.7) (read-create) Status of event group
3.6 Setting by SetRequest from an SNMP manager
The same content as the commands of each group can be specified by using SetRequest from an SNMP manager.
The procedure for making settings from an SNMP manager is as follows.
As an example, we explain how to make new settings for the Ethernet statistics information (etherStatsTable) group to port1.1 using index number 1.
Similar operations can be used to make settings for a supported MIB on other groups.
- Make SNMP settings to allow the MIB to be written.
For details, refer to the SNMP technical reference.
- For etherStatsStatus.1, specify “2” (createRequest).
The “.1” of etherStatsStatus.1 is the etherStatsTable index.
- For etherStatsDataSource.1, specify iFindex.5001 as the interface to be monitored.
ifIndex.5001 indicates port1.1.
- Specifying “owner” is optional, but if you do, specify the text string in etherStatsOwner.1.
- For etherStatsStatus, specify “1” (valid).
When you perform the above steps, the following commands are specified for port1.1.
We assume that “RMON” was set as the “owner” setting.
rmon statistics 1 owner RMON
Below we show how to disable the RMON function system-wide from the SNMP manager.
- Make SNMP settings to allow the MIB to be written.
For details, refer to the SNMP technical reference.
- For ysrmonSetting(1.3.6.1.4.1.1182.3.7.1), specify “2” (disabled).
When you perform the above steps, the following commands are specified.
rmon disable
To specify enable, set ysrmonSetting(1.3.6.1.4.1.1182.3.7.1) to “1” (enabled).
4 Related Commands
Related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| RMON function settings | rmon |
| Set RMON Ethernet statistical information group | rmon statistics |
| Set RMON history group | rmon history |
| Set RMON event group | rmon event |
| Set RMON alarm group | rmon alarm |
| Show RMON function status | show rmon |
| Show RMON Ethernet statistical information group status | show rmon statistics |
| Show RMON history group status | show rmon history |
| Show RMON event group status | show rmon event |
| Show RMON alarm group status | show rmon alarm |
| Clear RMON Ethernet statistical information group counters | rmon clear counters |
5 Examples of Command Execution
5.1 Set Ethernet statistical information group
Make Ethernet statistical information group settings for port 1.1, and from the SNMP manager, retrieve the MIB of the Ethernet statistical information group.
- Enable the Ethernet statistical information group setting for port1.1.
The index of the Ethernet statistical information group is “1.”
Yamaha(config)#interface port1.1 Yamaha(config-if)#rmon statistics 1 ... (Enable the Ethernet statistical information group setting)
- From the SNMP manager, make SNMP settings that the MIB of the Ethernet statistical information group can be retrieved.
In this example, we use “private” access on SNMPv1 or SNMPv2c.
Yamaha(config)#snmp-server community private rw ... (Set the readable/writable community name to "private")
- From the SNMP manger, it will be possible to retrieve the etherStatsTable(.1.3.6.1.2.1.16.1.1) with the community name “private.”
5.2 Set history group
Make settings for the history group of port1.1 and retrieve the MIB of the history group from the SNMP manager.
- Enable the port1.1 history group setting.
The index of the history group is “1.”
Yamaha(config)#interface port1.1 Yamaha(config-if)#rmon history 1 ... (Enable the history group setting)
- From the SNMP manager, make SNMP settings that the MIB of the history group can be retrieved.
In this example, we use “private” access on SNMPv1 or SNMPv2c.
Yamaha(config)#snmp-server community private rw ... (Set the readable/writable community name to "private")
- From the SNMP manger, it will be possible to retrieve the etherHistoryTable(.1.3.6.1.2.1.16.2.2) with the community name “private.”
5.3 Set alarm event group
Use the alarm group to monitor the statistical information values of the Ethernet statistical information group.
The conditions for monitoring are as follows.
- The MIB to be monitored is port1.1’s etherStatsPkts(.1.3.6.1.2.1.16.1.1.1.5).
- The sampling interval is 180 seconds.
- The sampling type is delta.
- The upper threshold value is 2000.
- The lower threshold value is 1000.
When the above monitoring conditions are matched, the following event group is executed.
- Record to log and send SNMP trap
- Community name is “RMON”
- Make the required settings for SNMP trap transmission.
Yamaha(config)#snmp-server host 192.168.100.3 traps version 2c RMON ... (Specify the transmission destination for traps) Yamaha(config)#snmp-server enable trap rmon ... (Enable transmission of RMON function traps)
- Make event group settings.
The index of the event group is “1.”
Yamaha(config)#rmon event 1 log-trap RMON ... (Enable the event group setting)
- In order to set the alarm group’s monitoring target MIB object, enable the port1.1 Ethernet statistical information group setting.
The index of the Ethernet statistical information group is “1.”
Yamaha(config)#interface port1.1 Yamaha(config-if)#rmon statistics 1 ... (Enable the Ethernet statistical information group setting)
- Set the alarm group with the listed conditions.
The index of the alarm group is “1.”
Yamaha(config)#rmon alarm 1 etherStatsPkts.1 interval 180 delta rising-threshold 3000 event 1 falling-threshold 2000 event 1 ... (Enable the alarm group)
6 Points of Caution
None
7 Related Documentation
SYSLOG
1 Function Overview
This product provides the SYSLOG functions shown below as a means to ascertain the operating state.
- Functions to collect, reference, and delete the log that is accumulated inside this product
- Functions for output to the console simultaneously with logging
- Functions for transmitting to a previously-registered notification destination (SYSLOG server) simultaneously with logging
Logging, output to console, and notifications to the SYSLOG server are performed according to the output level specified by the user. Processing occurs only for the permitted messages.
Logging occurs in RAM, and is automatically backed up to flash ROM or can be backed up manually.
Notifications to the SYSLOG server are done simultaneously with logging, but only if a SYSLOG server has been registered.
2 Definition of Terms Used
None
3 Function Details
The SYSLOG function is described below.
- Logging occurs in RAM, and can accumulate up to 10,000 items.
The following two methods for backing up to a flash ROM are available.
- Automatic backup performed every hour since system boot
- Manual backup performed by the save logging command
- The accumulated log can be viewed by the show logging command.
It can also be deleted by the clear logging command.
The show logging command shows the information in RAM.
For the log information of this product, it is assumed that the information in RAM always matches the information in flash ROM.
(When the system starts, the log information in flash ROM is applied to RAM, and the service is started. The log information in RAM is not deleted following execution of a backup.)
- Log transmission occurs only if the notification destination (SYSLOG server) has been registered.
You can use the logging host command to register up to two notification destinations.
Specify the notification destination either by IP address or FQDN.
As the port number of the notification destination, the default port number 514 is used. (This setting cannot be freely set by the user.)
Logging facility values included in log notifications can be set using the logging facility command. The factory default setting is local0(16).
The logging format command can be used to change the format of log notifications to not include the header section (time stamp and host name). The following are log examples.
- Without the format specified (no logging format)
<134>Jan 1 00:00:00 Yamaha [ IMI]:inf: Configuration file is saved in “config0”
- With the format specified (logging format legacy)
<134>[ IMI]:inf: Configuration file is saved in “config0”
- Without the format specified (no logging format)
- The level of log that is transmitted (SYSLOG priority) can be set using the logging trap command.
This product allows you to enable or disable output for each level of log.
With the factory settings, the output level enables only Information and Error.
4. List of related commands
Related commands are shown below.
For details, refer to the Command Reference.
List of related commands
| Function name | Command name |
|---|---|
| Set log output level | logging trap |
| Set log console output | logging stdout |
| Set log notification destination (SYSLOG server) | logging host |
| Change the log notification format | logging format |
| Back up log | save logging |
| Clear log | clear logging |
| Show log | show logging |
| Sets the logging facility value | logging facility |
5 Examples of Command Settings
- Enable debug-level log output, and start log output to the SYSLOG server (192.168.1.100) with facility value 10.
Also output informational-level log to the console.
Yamaha(config)# logging trap debug … (Enable debug level log output) Yamaha(config)# logging facility 10 … (Sets the facility value to 10) Yamaha(config)# logging host 192.168.1.100 … (Register SYSLOG server) Yamaha(config)# logging stdout info … (Output informational-level log to the console)
- Stop notifications to the SYSLOG server.
Yamaha(config)# no logging host
- Save and show the accumulated log information.
Yamaha# save logging … (Save log from RAM to ROM) Yamaha# show logging … (Show accumulated log) 2018/03/08 20:42:46: [ SESSION]:inf: Login succeeded as (noname) for HTTP: 192.168.1.40 2018/03/09 10:06:42: [ NSM]:inf: Interface port1.1 changed state to down 2018/03/09 10:09:48: [ SESSION]:inf: Logout timer expired as (noname) from HTTP: 192.168.1.40 2018/03/09 16:19:36: [ NSM]:inf: Interface port1.2 changed state to up :
- Clear the accumulated log information.
Yamaha# clear logging … (Clear all accumulated logs) Yamaha# show logging … (Show log) (Since they were cleared, nothing is shown)
6 Points of Caution
None
7 Related Documentation
None
Firmware update
1 Function Overview
This product offers the following three firmware update functions, in order to correct problems in the program and to add new functionality.
- Firmware updates can be transmitted and applied to this product from a remote terminal such as a PC.
- This product’s built-in HTTP client can access an HTTP server, to download and apply the latest firmware.
These update functions can be used to upgrade or downgrade the version of firmware used on this product.
During firmware updating, all port LEDs flash green, regardless of the LED display mode setting.
When successfully finished writing the updated firmware, the system is automatically rebooted in order to apply the new firmware.
For instructions on how to specify rebooting the system, refer to 3.3 Reboot After Writing.
2 Definition of Terms Used
None
3 Function Details
3.1 Update by transmitting the firmware update
This function transmits firmware updates to this product from a remote terminal, such as a PC, and applies it as boot firmware.
The update process is executed using a TFTP client or the Web GUI.
3.1.1 Using a TFTP client to update the firmware
Firmware can be updated by using a TFTP client installed on a computer or other remote terminal to transmit the updated firmware to this device.
In order to operate this product’s TFTP server, use the steps shown below to set up a network environment that allows remote access.
- Decide on the VLAN that will be used for maintenance.
- Set the IPv4 address on the maintenance VLAN. Set it using the ip address command.
- Permit access from the maintenance VLAN to the TFTP server. Use the tftp-server interface command or the management interface command to specify that setting.
- Enable the TFTP server. Enable the server using the tftp-server enable command.
Follow the rules below when sending the firmware update using the TFTP client.
- Set the transmission mode to “binary mode”.
- As shown in the table below, specify the remote path to which the firmware update is sent.
- Specify the administrative password in the form “/PASSWORD” at the end of the remote path.
However, the firmware update cannot be applied if the administrative password is still set to the default setting. The administrative password setting must be changed in advance.
For a firmware update using a TFTP client, the following three types of update can be performed.
Updated firmware
| Type | Remote path |
|---|---|
| Internal firmware | exec |
If there is no problem with the firmware update that was sent, the firmware update will be saved.
3.1.2 Updating the firmware by specifying a local file in the Web GUI
Specify the firmware update located on the terminal accessing the Web GUI, and applies it to this product.
This function does not do a version comparison with the existing firmware, and will overwrite the specified firmware regardless of version.
To update firmware by specifying a local file, click [Maintenance] - [Firmware update] in the Web GUI on the computer. (Refer to the part shown in a red frame on the screenshot below.)
Refer to the help contents within the GUI for the specific operation method.
Initial screen on the Web GUI for updating firmware using a PC
3.2 Using an HTTP client to update the firmware
This method of firmware update uses an HTTP client to obtain the firmware update from a specified URL, and then apply it to this product.
This function assumes that the firmware version will be upgraded. Downgrading to a previous version will only be permitted if “revision-down” is allowed.
The firmware cannot be rewritten with the same version of firmware.
An HTTP client can be used to update the firmware using the methods below.
- Use the firmware-update command in the CLI (command-line interface).
- Execute update firmware via the network in the Web GUI.
Updating the firmware with an HTTP client is done by using the settings value shown in the table below.
Firmware update using an HTTP client: setting parameters
| Setting parameter | Explanation |
|---|---|
| Download source URL | Sets the source URL from which the firmware is downloaded. A URL of up to 255 characters in length can be set. The URL must be entered in the form “http://<server IPv4/IPv6 address or host name>/<path name>”. If an IPv6 address is specified, it must be enclosed in square brackets. For server port numbers other than 80, the port number must be specified within the URL address, in the form “http://server IP address or host name:port number/path name.” Default value settings are specified in the following location. |
| Proxy Server URL | Specifies the proxy server to use for updating firmware. Specify it either as an IPv4/IPv6 address or FQDN. FQDNs can be up to 255 characters long. No proxy server is specified in default settings. Proxy servers must be specified as an IPv4/IPv6 address or in the form “http://<host name>/<path name port number>.” If an IPv6 address is specified, it must be enclosed in square brackets. |
| Permit downward revision | Sets whether the current version of firmware can be downgraded to a previous version. The default value is “Don’t allow”. Overwriting the firmware with the same version of firmware is not permitted. |
| Timeout | Specifies the timer for monitoring the completion of the processes shown below. ・ Check whether firmware version is new/old. ・ Download it from the designated URL. The monitoring timer can be set from 100 seconds to 86,400 seconds, but the default setting is 300 seconds. |
For instructions on using the firmware-update command, refer to “5 Examples of Command Execution” or the “Command Reference”.
To update firmware over the network using the Web GUI, execute [Maintenance] - [Firmware update] on the Web GUI. (Refer to the part shown in a red frame on the screenshot below.)
Refer to the help contents within the GUI for the specific operation method.
Initial Web GUI Screen for Updating Firmware via the Network
3.3 Reboot after writing
When successfully finished writing the firmware update, the system is automatically rebooted.
However, the system is not rebooted if the “no-reboot” option is specified for firmware-update execute command.
If the firmware-update reload-time command is specified without specifying the “no-reboot” option, then the system is rebooted according to the reboot time setting.
The revision after the next reboot can be confirmed by executing the show firmware-update command.
4 Related Commands
Related commands are shown below.
For details, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Set firmware update site | firmware-update url |
| Set proxy server | firmware-update http-proxy |
| Execute firmware update | firmware-update execute |
| Set firmware download timeout duration | firmware-update timeout |
| Permit downward revision | firmware-update revision-down |
| Show firmware update function settings | show firmware-update |
| Set firmware update reboot time | firmware-update reload-time |
5 Examples of Command Execution
5.1 Using an HTTP client to update the firmware
In this example, the firmware update is stored on the local HTTP server, and this product is set to manage the firmware in order to perform the update.
- Changes the firmware download URL to http://192.168.100.1/swp2.bin.
- Leaves the proxy server setting blank.
- The downward revision setting is left disabled.
- The timeout value is left at 300 sec.
- A reboot time is not specified, but the system is rebooted immediately after updates.
- The download URL is changed, and the firmware update settings are confirmed.
Yamaha(config)#firmware-update url http://192.168.100.1/swp2.bin … (Sets the download destination URL) Yamaha(config)#exit Yamaha#show firmware-update … (Shows the firmware update function setting) url:http://192.168.100.1/swp2.bin http-proxy: - timeout: 300 (seconds) revision-down: Disable firmware revision for next boot: - reload-time: - - The firmware update is executed.
Yamaha#firmware-update execute … (Executes firmware update) Found the new revision firmware Current Revision: Rev.2.03.01 New Revision: Rev.2.03.02 Downloading... Update to this firmware? (y/n)y … (Enters y value) Updating... Finish (Reboots automatically) - Pressing “CTRL+C” during the firmware update process will interrupt the update.
Yamaha#firmware-update execute Found the new revision firmware Current Revision: Rev.2.03.01 New Revision: Rev.2.03.02 Downloading... … (“Ctrl-C” entered) ^CCanceled the firmware download
5.2 Using an HTTP client to update the firmware (in a proxy server environment)
This updates the firmware by specifying a proxy server.
- The initial download URL setting is left unchanged.
- The proxy server is set to http://192.168.100.1:8080.
- The downward revision setting is left disabled.
- The timeout value is left at 300 sec.
- A reboot time is not specified, but the system is rebooted immediately after updates.
- Specify the HTTP proxy settings and confirm the firmware update settings.
Yamaha(config)#firmware-update http-proxy http://192.168.100.1 8080 … (Sets the HTTP proxy server) Yamaha(config)#exit Yamaha#show firmware-update … (Shows firmware update function settings) url: http://www.rtpro.yamaha.co.jp/firmware/revision-up/swx3220.bin http-proxy: http://192.168.100.1:8080 timeout: 300 (seconds) revision-down: Disable firmware revision for next boot: - reload-time: - - The firmware update is executed.
Yamaha#firmware-update execute … (Executes firmware update) Found the new revision firmware Current Revision: Rev.2.03.01 New Revision: Rev.2.03.02 Downloading... Update to this firmware? (y/n)y … (Enters y value) Updating... Finish (Reboots automatically)
6 Points of Caution
None
7 Related Documentation
L2MS control
1 Function Overview
L2MS (Layer2 Management Service) is a function that manages Yamaha network devices at the layer 2 level.
L2MS is configured with one L2MS manager unit (referred to as “manager” below) that manages multiple L2MS agent units (referred to as “agents” below).
Connections for the manager and agents are described below.
L2MS connections
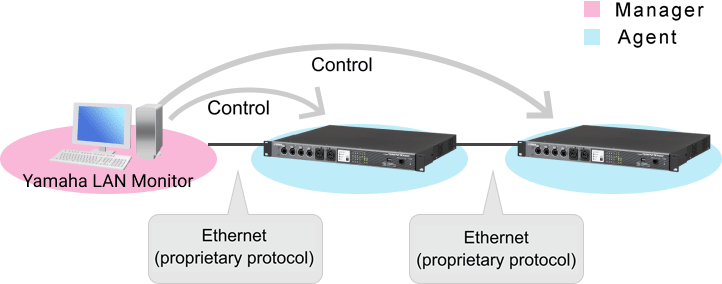
Yamaha LAN Monitor on the computer is used as the manager.
From Yamaha LAN Monitor, you can monitor information for Yamaha switches and Yamaha wireless LAN access points, and monitor and control connected devices.
The SWP2 operates as an agent.
The manager and agents are connected via Ethernet cables, and use a proprietary protocol (L2MS) for communication.
The principal functionality of Yamaha LAN Monitor is as follows.
For details on use, refer to Yamaha LAN Monitor.
- Ascertains the network topology, allowing you to visualize the entire network.
- Allows you to check the port status, bandwidth usage, and PoE power supply status of Yamaha switches and Yamaha wireless LAN access points.
- Allows you to monitor the status of each Dante-enabled device existing on the network.
- Recall Dante Controller with one click, allowing you to unify the Dante network from a single computer.
- Allows you to check the existence (live/dead monitoring) of network cameras and other terminals.
- By stopping and resuming the PoE supply of a Yamaha PoE switch, allows you to automatically or manually restart devices that are connected to a Yamaha PoE switch.
- Provides a snapshot function that is helpful for automatically detecting network abnormalities and for ascertaining the cause when a problem occurs.
- Allows you to attach labels that clarify the role of each device.
2 Definition of Terms Used
- Manager
The device that manages Yamaha network devices that are operating as L2MS and switch control function agents.
It manages the Yamaha switches in the network.
- Agent
A Yamaha switch that is managed by the L2MS and switch control function manager.
Its settings can be viewed or changed from the manager.
3 Function Details
3.1 L2MS protocol
The proprietary communication protocol used by L2MS is the same protocol as the communication used by the switch control functionality supported by the SWX/SWR series and WLX series.
This means that the manager is able to manage the SWX/SWR series.
L2MS control is performed using the L2 frames described below.
Contents of the L2MS protocol’s L2 frames
| Item | Value |
|---|---|
| Destination MAC | 01:a0:de:00:e8:12 – 01:a0:de:00:e8:15 |
| Ethertype | 0xe812, 0xe813 |
If there is a firewall between the manager and agent, the firewall must be set to pass these L2 frames.
3.2 Agent ownership
One agent cannot be simultaneously controlled by multiple managers.
For this reason, you must ensure that there is one manager in a network.
If an agent receives a query frame after boot, that agent will be managed by the manager that transmitted that query frame.
This state is canceled by any of the following conditions.
- If a query frame was not received for 30 seconds.
- If the manager was restarted.
3.3 About the Web GUI and IP address settings
With the factory settings, the IP address is set to DHCP.
The IP address is assigned from the DHCP server in the network.
If there is no DHCP server, the Auto IP function automatically generates an IPv4 link local address.
Access to the Web GUI is available via the Web GUI button in the “Device detail” view of Yamaha LAN Monitor.
If the Web GUI is not shown, it might be that the IP address and subnet settings of the Yamaha switch or Yamaha wireless LAN access point do not match the settings of the computer. Check the IP address and subnet settings.
The IP address settings of the agents can be made from the “Device settings” dialog box of Yamaha LAN Monitor.
3.4 Information notified from the agent
An agent that is managed by the manager informs the manager when its own state changes or if a fault is detected.
Information from an agent is shown in the manager’s device details, or in the notification area or the history area.
For details on the messages that are output to SYSLOG, refer to “7. SYSLOG message list.”
- The information sent by the SWP2 is as follows.
- Port link-up/down
- Loop detection
- SFP optical reception level fault
- Egress queue usage ratio fault
4 Related Commands
Related commands are shown below.
For details, refer to the Command Reference.
List of L2MS-related commands
| Operations | Operating commands |
|---|---|
| Show L2MS information | show l2ms |
| Set L2MS control frame transmission/reception | l2ms filter enable |
5 Examples of Command Execution
5.1 Set terminal management function
This indicates whether the unit is managed by the manager.
If it is managed, the manager’s MAC address is shown.
Yamaha#show l2ms Role : Agent Status : Managed by Manager (3c52.82da.eee7)
5.2 Set L2MS control frame transmission/reception
Make settings so that L2MS control frames are not transmitted and received on port 1.5.
Yamaha(config)#interface port1.5 Yamaha(config-if)#l2ms filter enable
6 Points of Caution
6.1 Regarding device configuration
If agents are used in a series connection, the maximum number of agent units that can be connected is eight units counting from the manager.
Counting agents from the manager, a ninth or subsequent agent unit cannot be connected in series.
If nine or more agent units are connected in series, counting from the manager, L2MS communication will be delayed, possibly preventing agents from being correctly detected or controlled.
If a switch made by a different manufacturer exists in the L2MS communication route, such as if a switch made by a different manufacturer is inserted between the manager and an agent, it might not be possible to correctly control the agent.
If you are configuring a network that includes a switch made by a different manufacturer, verify operation beforehand.
6.2 Regarding use in conjunction with other functions
6.2.1 Use in Conjunction with a VLAN
If using a VLAN, ports used for L2MS communication must be specified as an access port or as a trunk port assigned by the native VLAN.
L2MS communication is not possible via a trunk port not assigned by the native VLAN.
6.2.2 Use in conjunction with mirroring
When the mirroring function is used, L2MS communication sent and received at the monitor port is also copied.
For this reason, connecting a manager or agent to the mirror port might cause L2MS to not operate correctly; do not make such a connection.
6.2.3 Use with ACL
L2MS communication is not subject to ACL control.
Although the ACL discards frames that are not specified in the permission list (tacit rejection), L2MS communication is not subject to control, and therefore will be forwarded without being discarded.
6.2.4 Use in Conjunction with STP or Loop Detection Functionality
L2MS communication is not possible on ports blocked by STP or loop detection functionality.
If link switching is performed by STP, the manager is unable to correctly recognize the topology, which could prevent finding an agent or cause a route error when an agent is found.
In such cases, execute the l2ms reset command after STP has finished switching the link to reset agent management.
6.2.5 Use in Conjunction with Link Aggregation
If link aggregation is used, L2MS communication is considered to be occurring on “the lowest-numbered linked-up port associated with the logical interface.”
If link aggregation is used in conjunction with the monitoring function for connected terminals and a terminal is discovered at the end of a logical interface connection, then the terminal is considered to be connected to “the lowest-numbered linked-up port associated with the logical interface” and the corresponding port number is shown.
In Configuration 1, L2MS communication is assumed to be occurring between respective ports 1.1.
In Configuration 2, L2MS communication is assumed to be occurring between manager port1.1 and agent port1.1.
7. SYSLOG Message List
L2MS outputs the following SYSLOG messages.
Output messages appended with the "[ L2MS]” prefix.
| Category | Output Level | Message | Meaning |
|---|---|---|---|
| Start | informational | Start L2MS(Slave) | The L2MS unit was started as an agent. |
| Slave Management | informational | Start management by manager(addr) | Slave was managed by the manager. |
| Release from manager(addr) | Slave was excluded from management by manager. | ||
| Restart | informational | Restart by manager request. | This restarts the switch as requested by a manager. |
| Config Management | informational | Sent config to manager (addr) | Config file was sent to the manager. |
| Received config from manager (addr) | Config file was received from the manager. | ||
| Restart for update settings. | The unit will restart in order to update the received config file. | ||
| Manager Duplication | informational | L2MS manager duplication detected. ( addr, port X ) | An L2MS manager duplication was detected. (MAC address, port number where duplication was detected) |
| L2MS manager duplication resolved. ( addr, port X ) | The L2MS manager duplication was resolved. (MAC address, port number where duplication was detected) |
8 Related Documentation
None
Mail notification
1 Function Overview
Mail notification is a function in which information detected by the terminal monitoring function is conveyed via email.
By making the following settings, you can be notified of the information detected by various functions.
- Specify the mail server used when sending the mail.
- Specify the mail template.
2 Definition of Terms Used
- Mail template
A definition that collects the following information needed when sending mail.
- Mail server to use
- Sender’s mail address
- Recipient’s mail address
- Subject of mail
- Content of notification
- Transmission wait time
3 Function Details
3.1 Operation
With the mail server settings and mail template settings having been made correctly, when a notification event occurs for a function that supports mail notification, the mail notification function will enter the send-standby state.
The mail notification function that is now in the send-standby state will wait until the mail transmission wait time specified for each mail template has elapsed.
When the mail transmission wait time has elapsed, the mail notification function combines the notification events that have occurred during the wait time into a single mail, and sends it to the recipient.
3.2. Mail server setting
This can be set in List of registered mail servers in the Web GUI’s [Advanced settings]-[Mail notification].
Press the New button or the Setting button of an existing setting to move to Mail server settings.
In Mail server settings, make the following settings.
- Account identification name
A name that distinguishes the mail server settings. This may be omitted.
- SMTP server address
- Port number of the SMPT server
- SMTP encryption
You can choose to encrypt with SMTP over SSL or with STARTTLS - SMTP authentication
When performing MTP authentication, enter the user name and password
3.3 Mail template settings
This can be set in List of mail notification settings in the Web GUI’s [Advanced settings]-[Mail notification].
Press the New button or the Setting button of an existing setting to move to Mail notification settings.
In Mail notification settings, make the following settings.
- Sender (From)
- Recipient (To)
- Subject
If Use prescribed subject has a check mark, the subject line of the mail will be Notification from (device name).
- Content of notification
- Mail transmission wait time

3.4 Functions that support mail notification
The following functions support mail notification.
Terminal monitoring function
The following notification events will be the subject of mail notification.
| Category | Type | Description |
|---|---|---|
| Ping monitoring | Up detection | Terminal up was detected |
| Down detection | Terminal down was detected | |
| Frame reception amount monitoring | Up detection | Terminal up was detected |
| Down detection | Terminal down was detected | |
| LLDP monitoring | Up detection | Terminal up was detected |
| Down detection | Terminal down was detected |
3.5 Mail body example
The body of a notification mail includes content such as the following.
For details, refer to the technical reference for each function.
Up to 100 items can be shown in one notification mail.
Model: SWP2 *Model name Revision: Rev.2.03.01 *Firmware version Name: SWP2_XXXXXXXX *Host name Time: 2018/01/01 12:34:56 *Mail transmission time Template ID: 1 *Mail template ID <<<<<<<<<<<<<<<<<< Terminal Monitoring Information >>>>>>>>>>>>>>>>>>> [via Ping] Date Status IP Address Description ---------------------------------------------------------------------------- 2017/06/13 Thu 10:42:56 UP 192.168.100.155 IP_Camera_1 2017/06/13 Thu 10:51:00 DOWN 192.168.100.155 IP_Camera_1 2017/06/13 Thu 10:54:02 UP 192.168.100.10 Wireless_AP_1 2017/06/13 Thu 11:29:27 UP 192.168.100.155 IP_Camera_1 2017/06/13 Thu 11:30:31 DOWN 192.168.100.10 Wireless_AP_1 [via Bandwidth Usage] Date Status Interface Description ---------------------------------------------------------------------------- 2017/06/13 Thu 10:45:43 UP port1.4 IP_Camera_2 2017/06/13 Thu 10:45:56 UP port1.6 Note_PC_1 2017/06/13 Thu 10:50:00 DOWN port1.6 Note_PC_1 2017/06/13 Thu 10:53:27 DOWN port1.4 IP_Camera_2 [via LLDP] Date Status Interface Description ---------------------------------------------------------------------------- 2017/06/13 Thu 10:53:56 UP port1.3 Note_PC_2 2017/06/13 Thu 11:11:54 DOWN port1.3 Note_PC_2 2017/06/13 Thu 11:14:24 UP port1.3 Note_PC_2
4 Related Commands
| Operations | Operating commands |
|---|---|
| SMTP mail server settings | mail server smtp host |
| Setting the SMTP mail server name | mail server smtp name |
| Trigger setting of email notification | mail notify trigger |
| Email sending template setting mode | mail template |
| Email sending server ID settings | send server |
| Email sending sender email address settings | send from |
| Email sending recipient email address settings | send to |
| Email sending subject settings | send subject |
| Email sending wait time settings | send notify wait-time |
| Certificate sending email settings | mail send certificate |
| Certificate notification email settings | mail send certificate-notify |
| Certificate expiration notification timing settings | mail certificate expire-notify |
| Show email sending information | show mail information |
5 Points of Caution
The following are precautions related to SMTP authentication.
- The SMTP authentication only supports the LOGIN method.
- PLAIN, CRAM-MD5, and other methods are not supported.
Notes on firmware that does not support the email notification function command.
- If you upgrade from firmware that does not support the command to firmware does support it, the settings configured with Web GUI will continue to be used as the command settings.
- When returning to firmware that does not support the command, the settings that have been changed in the firmware that supports the command cannot continue to be used. Therefore, after revision downgrade, resetting is required.
- If you have not changed the settings, you can keep them as they are.
6 Related Documentation
LLDP
1 Function Overview
LLDP is a protocol for passing device management information between a device and its neighboring devices.
This is a simple protocol in which a device unidirectionally advertises its own information and neighbor devices receive this information. However, since LLDP-compliant devices maintain the information received from neighbor devices as MIB objects, the user can access this information via SNMP and ascertain what type of devices are connected to which interfaces are.
2 Definition of Terms Used
- LLDP
Link Layer Discovery Protocol.
This is defined in IEEE 802.1ab.
- LLDP-MED
LLDP for Media Endpoint Devices.
This is defined in ANSI/TIA-1057.
3 Function Details
3.1 Operating Specifications
3.1.1 Basic Specifications
This product supports the following operations.
- LLDP frames are transmitted from any LAN/SFP+ port to convey information about the device itself.
- LLDP frames are received at any LAN/SFP+ port to obtain information about neighboring devices.
- Information transmitted via LLDP about the device itself, and information obtained via LLDP about neighbor devices, etc., can be referenced via SNMP.
LLDP sends and receives information using Type, Length, and Value (TLV) attributes.
For details on the TLV information sent by this product, refer to 3.2 TLV list.
This product’s LLDP supports the following MIBs of SNMP. For details, refer to 3.3 Supported MIBs.
- LLDP-MIB
- LLDP-V2-MIB
- LLDP-EXT-MED-MIB
The following settings are required in order to use the LLDP function.
- Use the lldp run command to enable the system-wide LLDP function.
- Use the lldp-agent command to create an LLDP agent for the applicable interface.
- Use the set lldp command to specify the LLDP frame transmit/receive mode.
With the default settings of this product, the LLDP function is disabled.
LLDP frames are always transmitted without tags, regardless of the VLAN settings of the transmitting switch port.
They are also transmitted without tags from a trunk port without a native VLAN.
3.1.2 Transmitted information settings
Use the following commands to specify the LLDP frames that are transmitted from the device itself. There are also some TLVs (required TLVs) that are transmitted regardless of the settings of the following commands.
- tlv-select basic-mgmt command (basic management TLV)
- tlv-select ieee-8021-org-specific command (IEEE 802.1 TLV)
- tlv-select ieee-8023-org-specific command (IEEE 802.3 TLV)
- tlv-select med command (LLDP-MED TLV)
The system name and description that are transmitted in the basic management TLVs are specified by the lldp system-name command and the lldp system-description command.
The type of management address is set by the set management-address-tlv command.
3.1.3 Transmission timer setting
The interval at which LLDP frames are sent is specified by the set timer msg-tx-interval command.
The multiplier for calculating the hold time (TTL) for device information is set by the set msg-tx-hold command.
The TTL for LLDP transmission is the result of the following calculation. The default is 121 seconds.
- TTL = ( value set by the “set timer msg-tx-interval” command ) × ( value set by the “set msg-tx-hold” command ) + 1 (second)
When a neighbor device is connected to a LAN/SFP+ port for which LLDP frame transmission is enabled, LLDP frames are transmitted rapidly at a fixed interval according to the high-speed transmission interval setting.
The transmission interval and the number of transmissions for high speed transmission are set by the set timer msg-fast-tx command and the set tx-fast-init.
If from a state in which LLDP frame transmission is enabled, the set lldp command is used to disable it, this product transmits a shut-down frame, notifying the neighbor device that LLDP frame transmission has stopped.
Subsequently, even if LLDP frame transmission is once again enabled, LLDP frame transmission to the neighbor device is stopped for a time.
The stopped duration until the next transmission occurs after transmitting the shutdown frame is set by the set timer reinit-delay command.
3.1.4 Maximum connected devices setting
The maximum number of connected devices that can be managed by the corresponding port is set by the set too-many-neighbors limit command.
The default value for the maximum number of connected devices is 5 devices.
3.1.5 Checking LLDP information
LLDP interface settings and received information about neighbor devices can be checked by using the show lldp interface command or the show lldp neighbors command.
To clear the LLDP frame counter, use the clear lldp counters command.
3.1.6 Other functions using LLDP
- Link to AP
This function sends and receives proprietary LLDP frames between Yamaha switches and Yamaha wireless AP to automatically specify settings based on information in the LLDP notifications.
The AP link function is specified using the lldp auto-setting command.
For details, refer to LLDP automatic setting.
- Dante optimization setting
This function automatically specifies settings optimized for the Dante digital audio network.
The Dante optimization setting function is specified using the lldp auto-setting command.
For details, refer to Dante optimization setting function.
- Monitoring LLDP receiving intervals
This function monitors whether specific connected terminals are live or dead.
For details, refer to Terminal monitoring.
- Voice VLAN
With the voice VLAN function, LLDP-MED can be used to specify voice traffic settings for IP telephony.
For details, refer to VLAN.
3.2 TLV list
The TLVs supported by this product are listed below.
- Required TLVs
- Basic management TLVs
- IEEE 802.1 TLV
- IEEE 802.3 TLV
- LLDP-MED TLV
For the detailed specification of each TLV, refer to IEEE 802.1ab (LLDP) and ANSI/TIA-1057 (LLDP-MED).
The TLVs that are transmitted by this product are explained below.
3.2.1 Required TLVs
If LLDP frame transmission is enabled, these TLVs are always transmitted.
Three TLVs are transmitted: chassis ID, port ID, and TTL.
The required TLVs are shown below.
Required TLVs
| Type | Description | Length | Value (only fixed values are listed) |
|---|---|---|---|
| Chassis ID | Chassis ID | 6 Byte | MAC address of the device |
| Port ID | Port ID | 7–8 bytes | Port name (portX.X) |
| Time To Live (TTL) | Time to keep device information (seconds) | 2 Byte |
3.2.2 Basic management TLVs
These TLVs are transmitted if LLDP frame transmission is enabled and the tlv-select basic-mgmt command is specified.
System-related management information is transmitted, such as name, system capabilities, and address.
The basic management TLVs are as follows.
Basic management TLVs
| Type | Description | Length | Value (only fixed values are listed) |
|---|---|---|---|
| Port Description | Port description text string | 0–255 bytes | |
| System Name | System name text string Default: Host name | 0–255 bytes | |
| System Description | System description text string Default: device name + firmware revision | 0–255 bytes | |
| System Capabilities | The functions supported by the system | 2 Byte | 0x0004 (bridge) |
| The system’s functions that are in an enabled state | 2 Byte | 0x0004 (bridge) | |
| Management Address | The management address IP address (4 bytes) or MAC address (6 bytes) | 4 or 6 Byte | |
| Interface sub-type | 1 Byte | 0x02 (ifIndex) | |
| Interface number | 4 Byte | ifIndex value |
3.2.3 IEEE 802.1 TLV
These TLVs are transmitted if LLDP frame transmission is enabled and the tlv-select ieee-8021-org-specific command is specified.
These transmit information such as VLAN and link aggregation for the corresponding port.
The IEEE 802.1 TLVs are shown below.
IEEE 802.1 TLV
| Type | Description | Length | Value (only fixed values are listed) |
|---|---|---|---|
| Port VLAN ID | Port VLAN number | 2 Byte | |
| Port and Protocol VLAN ID | Support for protocol VLAN, and whether enabled or disabled | 1 Byte | 0x00 (no support) |
| Protocol VLAN number | 2 Byte | 0x0000 | |
| Protocol Identity | Byte string that identifies the protocol | 0–255 bytes | |
| Link Aggregation | Link aggregation capability and status | 1 Byte | |
| ifIndex number of aggregation logical interface | 4 Byte | ||
| VLAN Name | Name of VLAN to which the port is associated | 0–32 bytes |
3.2.4 IEEE 802.3 TLV
These TLVs are transmitted if LLDP frame transmission is enabled and the tlv-select ieee-8023-org-specific command is specified.
Auto negotiation support information etc. for the corresponding port is transmitted.
The IEEE 802.3 TLVs are shown below.
IEEE 802.3 TLV
| Type | Description | Length | Value (only fixed values are listed) |
|---|---|---|---|
| MAC/PHY Configuration/Status | Auto negotiation support, and whether enabled or disabled | 1 Byte | |
| Communication methods for which auto negotiation is possible | 2 Byte | ||
| Operational MAU Type Communication speed and duplex mode (IETF RFC 4836) | 2 Byte | ||
| Link Aggregation | Aggregation ability presence/absence and status | 1 Byte | |
| Aggregation logical interface ifIndex number | 4 Byte | ||
| Maximum Frame Size | Maximum frame size | 2 Byte |
3.2.5 LLDP-MED TLV
These TLVs are transmitted if LLDP frame transmission is enabled and the tlv-select med command is specified.
These transmit information such as network policy information.
The LLDP-MED TLVs are shown below.
LLDP-MED TLV
| Type | Description | Length | Value (only fixed values are listed) |
|---|---|---|---|
| LLDP-MED Capabilities | LLDP-MED TLVs that can be transmitted | 2 Byte | 0x0003 (LLDP-MED Capabilities, Network Policy) |
| Device type | 1 Byte | 0x04 (Network Connectivity) | |
| Network Policy | Application types | 1 Byte | 0x01 (Voice) |
| Voice VLAN information | 3 Byte |
Network Policy is transmitted only from a port that is set as voice VLAN.
3.3 Supported MIB
For supported private MIBs, refer to the following SNMP MIB reference.
4 Related Commands
Related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Enable LLDP function | lldp run |
| Set system description text string | lldp system-description |
| Set system name | lldp system-name |
| Create LLDP agent | lldp-agent |
| Set LLDP transmission/reception mode | set lldp |
| Set management address type | set management-address-tlv |
| Set basic management TLV | tlv-select basic-mgmt |
| Set IEEE-802.1 TLV | tlv-select ieee-8021-org-specific |
| Set IEEE-802.3 TLV | tlv-select ieee-8023-org-specific |
| Set LLDP-MED TLV | tlv-select med |
| Set LLDP frame transmission interval | set timer msg-tx-interval |
| Set duration to stop transmission following LLDP transmission stop until transmission is once again possible | set timer reinit-delay |
| Set multiplier for calculating the time to maintain device information (TTL) | set msg-tx-hold |
| Set LLDP frame transmission interval for high-speed transmission term | set timer msg-fast-tx |
| Set number of LLDP frames transmitted for high-speed transmission term | set tx-fast-init |
| Set maximum number of devices that can be managed by an individual port | set too-many-neighbors limit |
| Show interface status | show lldp interface |
| Show connected device information for all interfaces | show lldp neighbors |
| Clear LLDP frame counters | clear lldp counters |
| Set Dante optimization function and AP link function using LLDP | lldp auto-setting |
5 Examples of Command Execution
5.1 Set LLDP frame transmission/reception
For port1.1, enable LLDP frame transmission/reception.
Basic management TLVs, IEEE 802.1 TLVs, IEEE 802.3 TLVs, and LLDP-MED TLVs are transmitted.
Set the LLDP frame transmission interval to 60 seconds. Set the LLDP frame TTL to 181 seconds.
Set “SWITCH1” as the name of the transmitting system.
Specify 10 as the maximum number of connected devices managed by the port.
Yamaha#configure terminal Yamaha(confif)#lldp system-name SWITCH1 ... (Set system name) Yamaha(config)#interface port1.1 Yamaha(config-if)#lldp-agent ... (Create LLDP agent, change modes) Yamaha(lldp-agent)#tlv-select basic-mgmt ... (Set basic management TLV) Yamaha(lldp-agent)#tlv-select ieee-8021-org-specific ... (Set IEEE 802.1 TLV) Yamaha(lldp-agent)#tlv-select ieee-8023-org-specific ... (Set IEEE 802.3 TLV) Yamaha(lldp-agent)#tlv-select med ... (Set LLDP-MED TLV) Yamaha(lldp-agent)#set timer msg-tx-interval 60 ... (Set transmission interval) Yamaha(lldp-agent)#set msg-tx-hold 3 ... (Set multiplier for TTL calculation: TTL = 60 x 3 + 1 = 181 seconds) Yamaha(lldp-agent)#set too-many-neighbors limit 10 ... (Set maximum number of connected units) Yamaha(lldp-agent)#set lldp enable txrx ... (Set LLDP transmission/reception mode) Yamaha(lldp-agent)#exit Yamaha(config-if)#exit Yamaha(config)#lldp run ... (Enable LLDP function) Yamaha(config)#exit
5.2 Show LLDP interface status
Show the port1.1 LLDP interface status.
Yamaha#show lldp interface port1.1 ... (Show interface information) Agent Mode : Nearest bridge Enable (tx/rx) : Y/Y Message fast transmit time : 1 Message transmission interval : 30 Reinitialization delay : 2 MED Enabled : Y Device Type : NETWORK_CONNECTIVITY LLDP Agent traffic statistics Total frames transmitted : 0
5.3 Show LLDP connected device information
Show LLDP connected device information.
Yamaha#show lldp neighbors ... (Show information for connected devices)
Interface Name : port1.1
System Name : SWP2
System Description : SWP2 Rev.2.03.01
Port Description : port1.3
System Capabilities : L2 Switching
Interface Numbering : 2
Interface Number : 5003
OID Number :
Management MAC Address : ac44.f230.0000
Mandatory TLVs
CHASSIS ID TYPE
IP ADDRESS : 0.0.0.0
PORT ID TYPE
INTERFACE NAME : port1.3
TTL (Time To Live) : 41
8021 ORIGIN SPECIFIC TLVs
Port Vlan id : 1
PP Vlan id : 0
Remote VLANs Configured
VLAN ID : 1
VLAN Name : default
Remote Protocols Advertised :
Multiple Spanning Tree Protocol
Remote VID Usage Digestt : 0
Remote Management Vlan : 0
Link Aggregation Status :
Link Aggregation Port ID :
8023 ORIGIN SPECIFIC TLVs
AutoNego Support : Supported Enabled
AutoNego Capability : 27649
Operational MAU Type : 30
Power via MDI Capability (raw data)
MDI power support : 0x0
PSE power pair : 0x0
Power class : 0x0
Type/source/priority : 0x0
PD requested power value : 0x0
PSE allocated power value : 0x0
Link Aggregation Status :
Link Aggregation Port ID :
Max Frame Size : 1522
LLDP-MED TLVs
MED Capabilities :
Capabilities
Network Policy
MED Capabilities Dev Type : End Point Class-3
MED Application Type : Reserved
MED Vlan id : 0
MED Tag/Untag : Untagged
MED L2 Priority : 0
MED DSCP Val : 0
MED Location Data Format : ECS ELIN
Latitude Res : 0
Latitude : 0
Longitude Res : 0
Longitude : 0
AT : 0
Altitude Res : 0
Altitude : 0
Datum : 0
LCI length : 0
What : 0
Country Code : 0
CA type : 0
MED Inventory
6 Points of Caution
None
7 Related Documentation
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
- LLDP automatic setting
LLDP automatic setting
1 Function Overview
The LLDP automatic setting function automatically sets settings based on information in LLDP notifications in proprietary LLDP frames sent and received between Yamaha switches and Yamaha wireless AP.
The following functionality can be achieved by LLDP automatic settings.
- RADIUS server automatic settings
- This automatic specifies information about RADIUS servers currently operating at the Yamaha wireless AP in the Yamaha switch. That makes it easy to configure an authentication function in Yamaha wireless APs as a RADIUS server or in Yamaha switches as a RADIUS client.
- Yamaha wireless AP dead/alive monitoring
- This uses LLDP to automatically monitor whether Yamaha wireless APs connected to the product are dead or alive.
To determine Yamaha switch and wireless AP models that support LLDP automatic setting function, refer to the following.
2 Definition of Terms Used
LLDP
Link Layer Discovery Protocol。
This is defined in IEEE 802.1AB.
3 Function Details
3.1 Key specifications
If LLDP automatic setting function is enabled, proprietary LLDP frames will be sent and received between Yamaha switches and Yamaha wireless AP.
LLDP automatic settings are specified using the lldp auto-setting command.
LLDP automatic setting function is disabled in default settings.
In order to use this function, reception of LLDP frames must be enabled.
For this reason, check in advance that the following settings have been made.
- Enable LLDP functionality for the overall system using the lldp run command.
- Create LLDP agents at applicable interfaces using the lldp-agent command.
- Specify the LLDP frame transmit/receive mode using the set lldp command.
LLDP frame transmission and reception are enabled in product default settings.
3.2 RADIUS server automatic settings
This function automatically specifies information in the product about RADIUS servers currently operating at Yamaha wireless APs (clusters). That makes it easy to configure an authentication function in Yamaha wireless APs as a RADIUS server or in Yamaha switches as a RADIUS client.
Authentication settings for each port on the product must be set manually by the user based on the given environment. For more details about authentication settings, refer to Port authentication functions in the technical reference.
3.2.1 RADIUS server information sent by Yamaha wireless APs
Yamaha wireless APs send RADIUS server information based on the following criteria.
- LLDP and LLDP automatic settings are enabled
- Cluster functionality is enabled
- Cluster leader APs are functioning as a RADIUS server
- Cluster follower APs are functioning as RADIUS client that connects to a leader AP RADIUS server.
For details about Yamaha wireless AP settings, refer to the Yamaha wireless AP technical reference.
If the criteria for sending information are satisfied, Yamaha wireless APs send notifications with the following RADIUS server information at regular intervals.
- IP address of the RADIUS server
- UDP port number for RADIUS server authentication
- Shared password for communicating with RADIUS server
3.2.2 RADIUS server entry control
If the product LLDP automatic setting function is enabled and RADIUS server information is received from a Yamaha wireless AP, then a radius-server host command with an optional dynamic string added to the end is automatically specified in the running-config.
In the remaining explanation below, the radius-server host command appended by an optional dynamic string is referred to as a “dynamic entry”, whereas the manually specified radius-server host command is referred to as a “static entry”.
Dynamic entries appended with the optional dynamic string are not saved in the startup-config file, even if the write command is executed.
After dynamic entry is set by automatic settings, static entry can be set by manually deleting the dynamic option.
However, static entry cannot be changed to dynamic entry by manually adding the dynamic option.
- Example of Dynamic Entry of radius-server host Command
radius-server host 192.168.100.241 auth-port 1234 key EXAMPLE dynamic
Dynamic entries specified by LLDP automatic settings are appended with LLDP reception port number and validity period information.
If identical RADIUS server information is received from multiple ports, the RADIUS server information received from the port with the smallest port number is retained.
The TTL (Time to Live) value included in the received LLDP frame is specified as the validity period.
The default TTL value for LLDP frames sent from Yamaha wireless APs is 120 seconds.
If new RADIUS server information is received within TTL seconds, then the validity period is updated, whereas if new RADIUS server information is not received within TTL seconds, then the dynamic entry is deleted.
However, if an LLDP shutdown frame with TTL = 0 is received, then the dynamic entry is immediately deleted.
The show radius-server command can be used to confirm RADIUS server information, with the automatically specified RADIUS server host marked with an asterisk and
the LLDP reception port number (LLDP received port) and validity period (Expires) information also listed.
- Example of using the show radius-server command to show dynamic entry information
SWX#show radius-server Server Host : 192.168.100.241* LLDP Received port : port1.2 Expires : 00:00:33 Authentication Port : 1234 Secret Key : EXAMPLE Timeout : 10 sec Retransmit Count : 5 Deadtime : 0 min * - Assigned by LLDP.
A total of up to 8 RADIUS server information entries, including dynamic and static entries, can be specified for the product.
Using static entries is prioritized over using dynamic entries.
Therefore, even if the maximum number of RADIUS server information entries are already specified, new static entries can be specified if there are any dynamic entries among existing entries.
In that case, the dynamic entry with the highest LLDP reception port number is deleted.
3.2.3 Precautions
If the above functionality is used, note the following precautions.
- Connection to Yamaha wireless AP unit
- To enable automatic setting of RADIUS server information, Yamaha switches must be connected directly to Yamaha wireless AP that support LLDP automatic setting functionality.
- For Yamaha switches not directly connected to a Yamaha wireless AP, specify RADIUS server settings manually.
- Characters permitted in shared passwords for communicating with RADIUS servers
- Question mark and space characters cannot be used. Do not use those characters when setting shared passwords (RADIUS server, client, or secret) for Yamaha wireless AP units.
- Set response wait time for the entire RADIUS server
- If multiple RADIUS servers are configured, set the auth timeout server-timeout command setting value, which sets the total wait time for all RADIUS servers, to a value equal to or larger than the product of the radius-server timeout command setting value times the radius-server retransmit command setting value plus one times the number of RADIUS servers. For command details, refer to the command reference.
3.3 Yamaha wireless AP dead/alive monitoring
When a Yamaha switch receives a request from a Yamaha wireless AP to start dead/alive monitoring, it automatically starts monitoring by LLDP whether the Yamaha wireless AP is dead or alive.
Yamaha wireless APs send dead/alive monitoring requests based on the following criteria.
- LLDP and LLDP automatic settings are enabled
If the dead/alive monitoring request is received with the LLDP automatic setting function enabled in the Yamaha switch, then an LLDP reception interval monitoring setting is registered for the LLDP reception port.
If no LLDP frame was received during a given period of dead/alive monitoring at the port where the setting was registered, then notification is sent that a communication interruption was detected at the SNMP trap and L2MS trap.
For details, refer to the technical reference for Terminal monitoring.
3.3.1 Precautions
If the above functionality is used, note the following precaution.
- If dead/alive monitoring is no longer necessary, such as after the Yamaha wireless AP connection port was changed, manually delete the settings that became unnecessary after the Yamaha wireless AP connection port was changed.
4 Related Commands
Related commands are indicated below.
For details, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Enable LLDP automatic settings | lldp auto-setting |
| Enable LLDP function | lldp run |
| Create LLDP agent | lldp-agent |
| Set LLDP transmission/reception mode | set lldp |
| Set LLDP frame transmission interval | set timer msg-tx-interval |
| Set RADIUS server host | radius-server host |
| Set response wait time for a single RADIUS server | radius-server timeout |
| Set number of times to retransmit request to RADIUS server | radius-server retransmit |
| Show RADIUS server setting status | show radius-server |
| Set response wait time for the entire RADIUS server | auth timeout server-timeout |
5 Setting Examples
For instructions on how to configure respective Yamaha switch and wireless AP settings, function refer to the following.
6 Points of Caution
See the precautions indicated for each function.
7 Related Documentation
Terminal monitoring
1 Function Overview
The terminal monitoring function checks the dead-or-alive state of specific terminals connected to the network switch.
The operating specifications for the terminal monitoring function are shown below.
Terminal monitoring function overview
Examples of an L2MS manager with an Yamaha LAN Monitor and an L2MS agent with an intelligent L2 switch are shown below.

As dead/alive monitoring methods, the following three types are provided.
- Monitoring by ping
Ping (ICMP Echo request/reply) is issued at regular intervals to a terminal that has an IP address, and the terminal is determined to be down if there is no longer a response.
The user can specify the ping response wait time and the number of failures before the connection is determined to be down.
- Frame reception amount monitoring
The frame reception amount is monitored at regular intervals for an individual port, and the terminal is determined to be down if the traffic falls below a specified amount.
The user can specify the monitoring start threshold value and the threshold value at which a down condition is determined.
Monitoring starts when the traffic exceeds the monitoring start threshold value, and a down condition is determined when the traffic falls below the down decision threshold.
- LLDP reception interval monitoring
The LLDP received at regular intervals by an individual port is monitored.
Using the TTL which is a required item in the data portion of an LLDP packet, a down condition is determined if LLDP is not received within the TTL interval.
If monitoring detects a terminal fault (down), the following processing is automatically performed.
- Alert shown in dashboard screen
An indication that a fault (down) occurred for the monitored terminal is displayed in the alert screen of the dashboard.
- Alert shown in LAN map screen
The L2MS trap function is used to notify the L2MS manager.
When the L2MS manager receives a notification, it uses the LAN map screen to indicate an error (down) occurred in a monitored terminal.
By the user’s choice, the following operations can be applied in parallel.
- Fault detection notification by mail
Notification that a monitored terminal has experienced a fault is sent to the desired recipient.
- Notification to the SNMP manager
A trap is sent to the SNMP manager specified by a command.
2 Definition of Terms Used
None
3 Function Details
3.1 Monitoring by ping (ICMP Echo request/reply)
Specifications for terminal monitoring by ping are given below.
- The interval of ICMP Echo request transmission from the network switch is fixed at 5 seconds.
- The ICMP Echo request that is transmitted has the following format.
- As the ID field of the ICMP header, the unique ID assigned to each monitored terminal is specified.
- As the sequence field of the ICMP header, a number that is sequentially incremented from 0 is specified.
- The validity of the ICMP Echo reply is checked as follows.
- Whether the ID field of the ICMP header contains the ID that was specified when sending the request
- Whether the sequence field of the ICMP header contains the sequence number that was specified when sending the request
- The wait time for ICMP Echo reply can be changed in the range of 1–60 sec, and the default is 2 sec.
- The number of failures to receive the ICMP Echo reply from the monitored terminal after which a fault is determined can be set in the range of 1–100, and the default is twice.
- Monitoring via ping can be done for a maximum of 64 units.
- If sending an email notification or SNMP trap is enabled, they are sent in the following cases.
- When a terminal is detected to be down (sent every 24 hours while down)
- When a terminal is detected to be up (sent when monitoring is started or restored)
3.2 Monitoring by frame reception amount
The way in which this device monitors by frame reception amount is described below.
Overview of frame reception amount monitoring
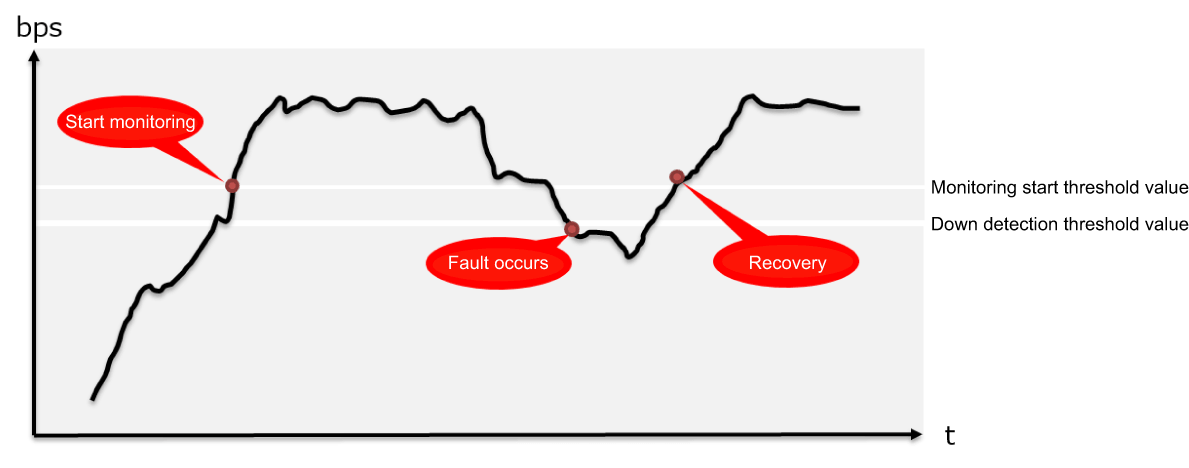
- At one-second intervals, the number of octets received at the port is referenced, and the number of octets received during one second is calculated.
- All ports are the object of observation.
- Using the number of octets received during one second and the link speed, the reception throughput (bps) and reception ratio (%) are calculated.
- Monitoring by frame reception amount starts when the monitoring start threshold value (bps) specified by the user is exceeded.
- After monitoring has started, a fault (down) is detected if the amount falls below the down detection threshold value (bps) specified by the user.
- If sending an email notification or SNMP trap is enabled, they are sent in the following cases.
- When a terminal is detected to be down
- When a terminal is detected to be up (sent when monitoring is started or restored)
3.3 Monitoring by LLDP
- Using the TTL which is a required item in the data portion of an LLDP frame, a down condition is determined if LLDP is not received within the TTL time.
- Monitoring starts when an LLDP frame is first received.
- This monitoring can be specified individually by port.
- If sending an email notification or SNMP trap is enabled, they are sent in the following cases.
- When a terminal is detected to be down
- When a terminal is detected to be up (sent when monitoring is started or restored)
- When a terminal stopped LLDP functionality
4 Related Commands
This function does not support settings via commands.
5. Settings via the Web GUI
Terminal monitoring settings can be done from [Advanced settings]-[Terminal monitoring] of the Web GUI.
Details on the settings in each screen can be referenced via the Web GUI help.
5.1 Terminal monitoring top page
The top page of terminal monitoring is shown below.
Terminal monitoring top page
- If you want to newly add a terminal for monitoring, press the New icon.
- If you want to change a currently-specified monitored terminal, press the [Setting] button in the list.
If you want to delete a currently-specified monitored terminal, select the check box of that terminal, and press the [Delete] button.
- If you want to ascertain the current state of the monitored terminal for which you are making settings, press the [Update] button to acquire the latest state.
5.2 Adding or modifying a monitored terminal
The method for adding a new monitored terminal, or for making changes, is shown below for each method of monitoring.
- Monitoring by ping
- Monitoring frame input volumes
- Monitoring LLDP receiving intervals
- Use the traffic observation function when deciding the monitoring start threshold value and the down detection threshold value settings for frame input volume monitoring.
- If you want mail notification to be sent in the event of a fault, you must separately make mail notification settings.
For details, refer to Technical reference: [Maintenance and operation functions] - [Mail notification] and to Web GUI help: [Advanced settings] - [Mail notification].
5.3. Checking the state of a monitored terminal
The state of a specified monitored terminal can be checked in the terminal monitoring gadget of the dashboard.
Dashboard terminal monitoring gadget
- For each monitored terminal, this shows the monitoring target, model name, monitoring type, and status.
- The following three states are shown as the state of the monitored terminal.
- Idle: Monitoring is not yet being performed:
- Up: The monitored terminal is operating correctly:
- Down: The monitored terminal is not operating correctly:
- Idle: Monitoring is not yet being performed:
- When you place the mouse cursor on the status field, the status of the monitored terminal is shown.
- If you click the [Idle] , [Up], or [Down] button in the upper part of the dashboard, only the monitored terminals that are in the corresponding state are shown. (The [All] button shows terminals of all states.)
- If not even one monitor terminal is registered, the display indicates “No monitored terminals are registered.”
6 Points of Caution
None
7 Related Documentation
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
- Performance observation
Performance observation
1 Function Overview
This product provides a mechanism for constantly observing the system’s performance.
An overview of the function is given below.
Performance observation
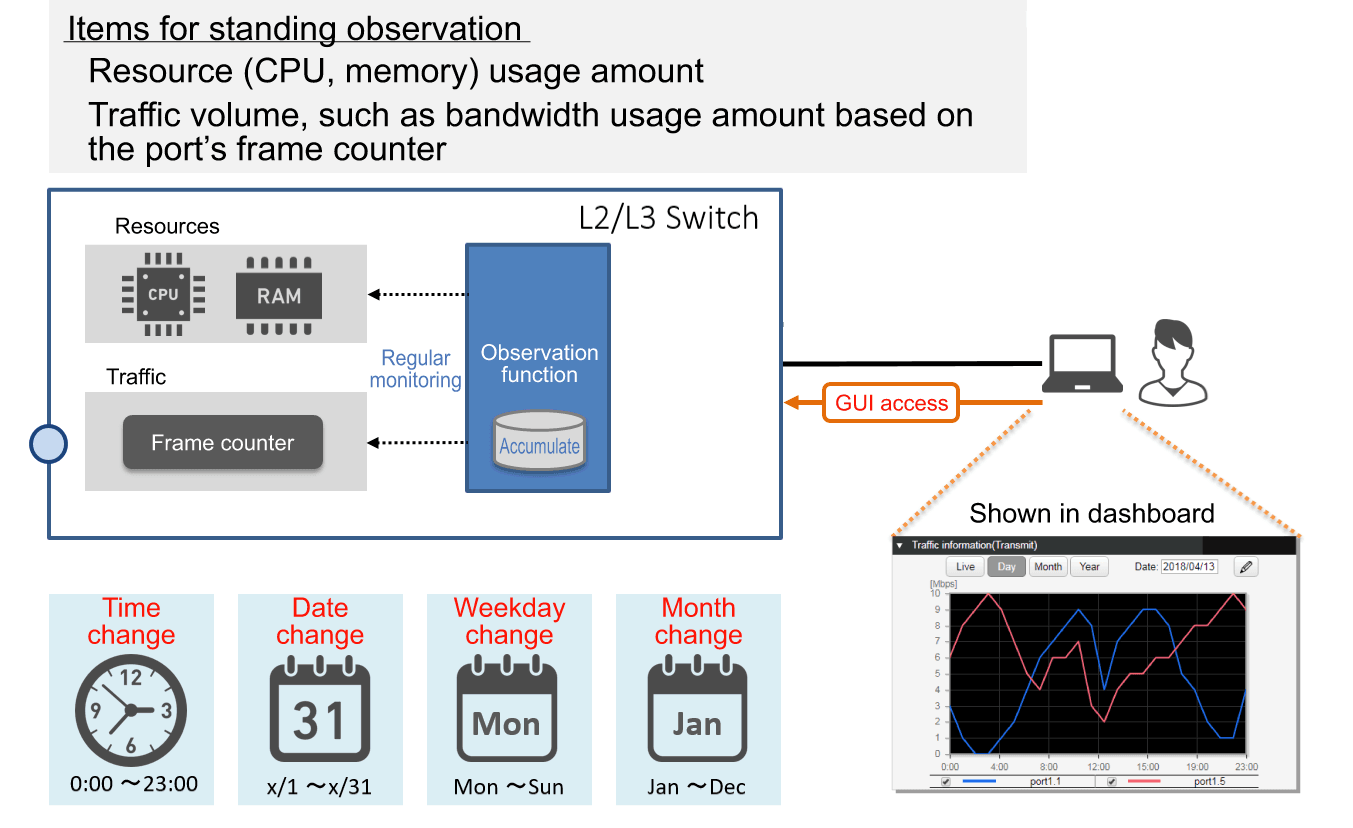
This product constantly observes the following two types of data.
- Resource usage: CPU and memory usage
- Traffic amount: The amount of communication port bandwidth used (transmission/reception)
Based on the results of observation, one year’s worth of the following change data is accumulated inside this product.
- Hourly change: Change for each hour (e.g. 0:00, 1:00, ...)
- Daily change: Change for each day of each month (e.g. 1/1, 1/2, ...)
- Weekly change: Change for each day of the week (e.g. SUN, MON, ...)
- Monthly change: Change for each month (e.g. Jan, Feb, ...)
By accessing this product via the Web GUI, the maintainer can view the various types of change data including live data in the dashboard.
This function can be utilized for the following purposes:
- Ascertain the short-term communication status
- Predict long-term future demand for network facilities
2 Definition of Terms Used
None
3 Function Details
3.1 Resource and traffic usage observation
Starting immediately after boot, this device automatically observes the CPU and memory and the transmit/receive throughput of each port every second.
The observed data is normalized using a moving average, and one year of data is saved in RAM.
4 Related Commands
This function does not support settings via commands.
5. Settings via the Web GUI
Performance observation can be controlled from the following pages of the Web GUI.
- Viewing the resource usage amount
- This can be viewed in the [Dashboard] item [Resource information (graph)].
- Viewing the traffic usage amount
- This can be viewed in the [Dashboard] item [Traffic information (graph)].
Details on how to view and make settings in each screen can be referenced via the Web GUI help.
5.1 Viewing the resource usage amount
The resource information (graph) screen is shown below.
Example when Live is selected for resource information (graph)
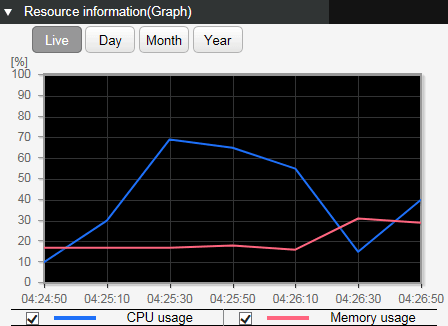
- The graph rendering can be changed using the following buttons.
Current status: Live
The various current usage ratios are obtained at one-second intervals and shown on the graph.
Hourly change: Day
The various usage ratios for the specified day are shown at one-hour intervals on the graph.
To specify the day, use the day-specifying box in the upper right of the gadget.
Daily change: Month
The various usage ratios for the specified month are shown at one-day intervals.
To specify the month, use the month-specifying box in the upper right of the gadget.
Monthly change: Year
The various usage ratios for the specified year are shown at one-month intervals.
To specify the year, use the select box in the upper right of the gadget.
- It is not currently possible to reference changes in the day of the week.
- If the CPU and memory usage ratios exceed 80%, then a warning message is shown on the dashboard.
If the ratio falls below 80% after having exceeded 80%, the warning is automatically cleared.
5.2 Viewing the traffic usage amount
The traffic usage amount (graph) screen is shown below.
Example of when traffic usage amount (graph) Day is selected / Example of transmission traffic
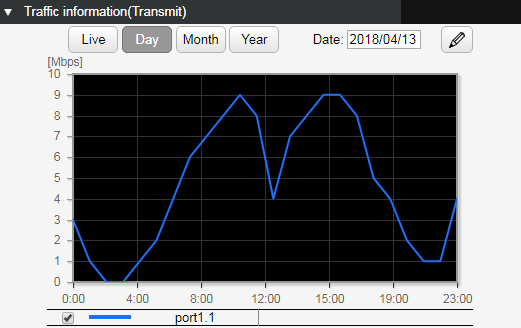
- The traffic usage amount of each port can be shown separately for transmission and reception.
- The graph rendering can be changed using the following buttons.
Current status: Live
The various current usage ratios are obtained at one-second intervals and shown on the graph.
The most recent two minutesof the obtained data is held and rendered on the graph.
Hourly change: Day
The various usage ratios for the specified day are shown at one-hour intervals on the graph.
To specify the day, use the day-specifying box in the upper right of the gadget.
Daily change: Month
The various usage ratios for the specified month are shown at one-day intervals.
To specify the month, use the month-specifying box in the upper right of the gadget.
Monthly change: Year
The various usage ratios for the specified year are shown at one-month intervals.
To specify the year, use the select box in the upper right of the gadget.
- It is not currently possible to reference changes in the day of the week.
- To select the interface to be shown, click the interface select button (
), and then make a selection in the following screen.
- If the traffic usage ratio exceeds 60%, a warning message is shown on the dashboard.
If the ratio falls below 50% after having exceeded 60%, the warning is automatically cleared.
6 Points of Caution
None
7 Related Documentation
None
Scheduling function
1 Function Overview
Scheduling functionality is used to execute specific processes when any particular time or event occurs.
This functionality enables the following types of actions using a Yamaha switch.
- Apply QoS to a specific VLAN only during a specific period.
- Supplies PoE power to wireless LAN access points only during the specified period.
- Periodically saves “tech-support” information in microSD memory.
2 Definition of Terms Used
- Trigger
General term for conditions/criteria, such as that the internal clock time matches a specified time or that a specific event occurs.
- Time Trigger
Condition that the internal clock time matches a specified time.
- Event Trigger
Condition that a specific event occurs.
- Action
Action executed when a trigger is activated.
3 Function Details
Scheduling functionality involves specifying triggers and actions, which are the two parameter settings for executing specific process actions when a particular specified time or event trigger occurs.
3.1 Time Trigger
Time triggers can be specified in terms of year, month, day, hour, minute, and second.
Time triggers are specified using the schedule command.
Available setting parameters are indicated below.
| Type | Setting Method | Setting Value Example | |
|---|---|---|---|
| Date | Month 1 - 12 | One specific month (such as only December) | 12 |
| Multiple specific months (such as only January and February) | 1,2 | ||
| Range from specific month to December (such as February to December) | 2- | ||
| Range from specific month to specific month (such as February to July) | 2-7 | ||
| Range from January to specific month (such as January to July) | -7 | ||
| Every month | * | ||
| Day 1 - 31 | One specific day (such as day 1 only) | 1 | |
| Multiple specific days (such as days 1 and 2 only) | 1,2 | ||
| Range from specific day to last day (such as day 2 to month-end) | 2- | ||
| Range from specific day to specific day (such as days 2 to 7) | 2-7 | ||
| Range from day 1 to specific day (such as days 1 to 7) | -7 | ||
| Every day | * | ||
| Specific day-of-week only (such as Monday only) | mon | ||
| Multiple specific days of the week only (such as Saturday and Sundays only) | sat,sun | ||
| Range from specific day-of-week to specific day-of-week (such as Monday to Friday) | mon-fri | ||
| Range from Sunday to specific day-of-the-week (such as Sunday to Friday) | -fri | ||
| Hours, Minutes, Seconds | Hour 0 - 23 | Specific hour only (such as 23:00 only) | 23 |
| Multiple specific hours only (such as 01:00 and 22:00 only) | 1,22 | ||
| Range from specific hour to 23:00 (such as 02:00 to 23:00) | 2- | ||
| Range from specific hour to specific hour (such as 02:00 to 21:00) | 2-21 | ||
| Range from hour 00:00 to specific hour (such as 00:00 to 21:00) | -21 | ||
| Each hour | * | ||
| Minute 0 - 59 | One specific minute only (such as minute 59 only) | 59 | |
| Multiple specific minutes only (such as minutes 1 and 50 only) | 1,50 | ||
| Range from specific minute to minute 59 (such as minutes 2 to 59) | 2- | ||
| Range from specific minute to specific minute (such as minutes 2 to 50) | 2-50 | ||
| Range from minute 0 to specific minute (such as minutes 0 to 50) | -50 | ||
| Each minute | * | ||
| Second 0 - 59 | One specific second only (such as second 59 only) May be omitted | 59 | |
3.2 Event Triggers
Either of the following events can be specified as an event trigger.
Event triggers are specified using the schedule command.
Events that can be specified are indicated below.
| Type | Description |
|---|---|
| startup | Action is executed when startup occurs. |
| sd-attached | Action is executed when a microSD card is inserted. |
3.3 Actions
Processes executed when a time trigger or event trigger is activated are called actions.
To specify actions, use the schedule template command to switch to the schedule template mode and then specify the action using the cli-command command or script command.
The following two actions are available.
| Operation | Command for settings | Description |
|---|---|---|
| Execute Specified Commands | cli-command command | Execute the specified commands in ascending order of ID numbers. |
| Execute Specified Script | script command | Execute the character strings in the first 100 lines of the specified file /(model)/schedule/script.txt in external memory (microSD) as a command. |
4 Related Commands
Related commands are indicated below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operating Mode | Command | Description |
|---|---|---|
| Global Configuration Mode | schedule | Specifies a schedule template ID that specifies the trigger and defines the action. |
| schedule template | Specifies the schedule template ID and switches to the schedule template mode. | |
| Schedule Template Mode | description | Specifies description of the schedule template. |
| action | Enables/disables schedule template Use disable to temporarily disable schedule function. | |
| cli-command | Defines command executed when trigger is activated. | |
| script | Enables execution of commands indicated in specified file in external memory. |
5 Setting Examples
5.1 Supplying PoE Power to Wireless LAN Access Points Only During Specified Hours
Supply PoE power to wireless LAN access points connected to port1.1 and port1.2 on weekdays only between 8:00 and 17:00.
Yamaha# Yamaha# configure terminal Yamaha(config)# schedule 1 time */mon-fri 8:00:00 1 Yamaha(config)# schedule template 1 Yamaha(config-schedule)# cli-command 1 configure terminal Yamaha(config-schedule)# cli-command 2 interface port1.1-2 Yamaha(config-schedule)# cli-command 3 power-inline enable Yamaha(config-schedule)# exit Yamaha(config)# Yamaha(config)# schedule 2 time */mon-fri 17:00:00 2 Yamaha(config)# schedule template 2 Yamaha(config-schedule)# cli-command 1 configure terminal Yamaha(config-schedule)# cli-command 2 interface port1.1-2 Yamaha(config-schedule)# cli-command 3 power-inline disable Yamaha(config-schedule)# end Yamaha#
5.2 Obtaining Internal Information when microSD Memory is inserted
Automatically saves tech-support in microSD memory when microSD card is inserted.
Yamaha# Yamaha# configure terminal Yamaha(config)# schedule 1 event sd-attached 1 Yamaha(config)# schedule template 1 Yamaha(config-schedule)# cli-command 1 copy tech-support sd Yamaha(config-schedule)# end Yamaha#
6 Unavailable Commands
The following commands cannot be executed for the schedule function.
- backup system
- baudrate select
- boot prioritize sd / no boot prioritize sd
- certificate user
- Commands that begin with “clock”
- cold start
- copy radius-server local
- crypto pki generate ca / no crypto pki generate ca
- disable
- enable password
- exit
- firmware-update execute
- firmware-update sd execute
- logout
- Commands that begin with “ntpdate” or “no ntpdate”
- password / no password
- password-encryption / no password-encryption
- ping /ping6
- quit
- reload
- remote-login
- restart
- restore system
- schedule / no schedule
- schedule template / no schedule template
- Commands that begin with “show”
- ssh
- ssh-server host key generate
- Commands that begin with “stack” or “no stack”
- startup-config select / no startup-config select
- telnet
- traceroute / traceroute6
7 SYSLOG
The schedule function outputs the following syslog messages.
| Level | Output | Description |
|---|---|---|
| Info | [SCHEDULE]:inf:ID:X command is done | The schedule template ID:X command was executed when the trigger was activated. |
| [SCHEDULE]:inf:ID:X script is done | The schedule template ID:X script was executed when the trigger was activated. | |
| Error | [SCHEDULE]:err:ID:X cmd[ID][COMMAND] is prohibited to execute | Execution of the prohibited command COMMAND in schedule template ID:X was suppressed. |
| [SCHEDULE]:err:ID:X cmd[ID][COMMAND] is failed to execute | Command failed in schedule template ID:X due to invalid command format or in parameter setting. | |
| [SCHEDULE]:err:ID:X microSD is not mounted | Script execution failed at schedule template ID:X because microSD was not inserted. | |
| [SCHEDULE]:err:ID:X failed to get the schedule forlder path | Script execution failed at schedule template ID:X because the expected directory containing the script was not found. | |
| [SCHEDULE]:err:ID:X script is not found | Script execution failed at schedule template ID:X because the script file was not found. | |
| [SCHEDULE]:err:ID:X failed to add action to queue | Action failed at schedule template ID:X because action was discarded due to the many actions waiting for execution in the queue. |
8 Points of Caution
- When actions are executed, the cli-command executes actions in ascending ID number order.
- When actions are executed, even a command specified by the cli-command results in an execution error, the remaining commands are executed.
- If both a cli-command and script command are specified in the same schedule template, then the script command is executed and the cli-command is not executed.
- If multiple triggers are activated simultaneously, then actions are executed in ascending order of schedule template ID number.
- The following precautions apply for devices that include a stack.
- A “startup” event trigger is not activated in stack member switches.
- A “sd-attached” event trigger is not activated in stack member switches.
- The trigger is not activated if a stack is enabled and is in the standalone state.
- If the trigger activation time elapses due to the time setting being set manually by the clock set command or being changed by NTP, then any existing triggers scheduled to be activated within 59 seconds of when the current time setting was changed will be activated.
- If the trigger activation time was changed backward manually by the clock set command or by NTP, then the time triggers are checked again starting from the time to which it was set back.
- This function can be used to periodically save the configuration, but periodic rewriting will consume ROM capacity more quickly. ROM failures due to frequent rewriting are not warranted for free repairs, even if they occur during the warranty period.
9 Related Documentation
- None
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
- Dante optimization setting function
Dante optimization setting function
1 Function Overview
Dante optimization settings is a function that makes it easy to specify the optimal environment for the Dante digital audio network.
This allows the user to easily make settings such as QoS settings, IGMP snooping settings, flow control disable settings, and EEE disable settings.
The items set by the Dante optimization setting function are as follows.
| Object of setting | Function | Command |
|---|---|---|
| Entire system | Disable flow control | flowcontrol disable |
| Enable QoS | qos enable | |
| Optimize transmission queue by DSCP value | qos dscp-queue | |
| VLAN interface | Enable IGMP snooping | ip igmp snooping enable |
| Enable IGMP query transmission function | ip igmp snooping querier | |
| Set IGMP query transmission interval | ip igmp snooping query-interval | |
| Disable IGMP packet TTL value checking function | ip igmp snooping check ttl disable | |
| LAN/SFP+ port | Set QoS trust mode to DSCP | qos trust dscp |
| Disable flow control | flowcontrol disable | |
| Disable EEE | eee disable |
Use the Dante optimization setting function after you have made all of the basic switch settings (such as VLAN and IP).
If you make new changes to the settings, the Dante optimization settings will not follow.
2 Definition of Terms Used
- Dante
A digital audio network specification developed by the Audinate Corporation.
3 Function Details
This function provides automatic optimization settings using LLDP.
3.1 Automatic optimization settings using LLDP
By receiving special LLDP frames from certain Dante-enabled devices made by Yamaha, optimal settings for using Dante can be automatically applied.
Automatic optimization settings via LLDP are set by the lldp auto-setting command.
By default, this product is set to disable automatic optimization settings via LLDP.
Certain Dante-enabled devices made by Yamaha transmit Yamaha-proprietary LLDP frames that include the following content.
- EEE (Energy-Efficient Ethernet) disable setting
- Flow control disable setting
- Diffserve base QoS setting
- IGMP snooping settings
If this function is enabled and the corresponding LLDP frame is received, the following settings are automatically applied to running-config.
- [System-wide]
flowcontrol disable ... (Disable flow control) qos enable ... (Enable QoS) qos dscp-queue 0 0 ... (DSCP-transmit queue ID conversion table setting, same for below) qos dscp-queue 1 0 qos dscp-queue 2 0 qos dscp-queue 3 0 qos dscp-queue 4 0 qos dscp-queue 5 0 qos dscp-queue 6 0 qos dscp-queue 7 0 qos dscp-queue 8 2 qos dscp-queue 9 0 qos dscp-queue 10 0 qos dscp-queue 11 0 qos dscp-queue 12 0 qos dscp-queue 13 0 qos dscp-queue 14 0 qos dscp-queue 15 0 qos dscp-queue 16 0 qos dscp-queue 17 0 qos dscp-queue 18 0 qos dscp-queue 19 0 qos dscp-queue 20 0 qos dscp-queue 21 0 qos dscp-queue 22 0 qos dscp-queue 23 0 qos dscp-queue 24 0 qos dscp-queue 25 0 qos dscp-queue 26 0 qos dscp-queue 27 0 qos dscp-queue 28 0 qos dscp-queue 29 0 qos dscp-queue 30 0 qos dscp-queue 31 0 qos dscp-queue 32 0 qos dscp-queue 33 0 qos dscp-queue 34 0 qos dscp-queue 35 0 qos dscp-queue 36 0 qos dscp-queue 37 0 qos dscp-queue 38 0 qos dscp-queue 39 0 qos dscp-queue 40 0 qos dscp-queue 41 0 qos dscp-queue 42 0 qos dscp-queue 43 0 qos dscp-queue 44 0 qos dscp-queue 45 0 qos dscp-queue 46 5 qos dscp-queue 47 0 qos dscp-queue 48 0 qos dscp-queue 49 0 qos dscp-queue 50 0 qos dscp-queue 51 0 qos dscp-queue 52 0 qos dscp-queue 53 0 qos dscp-queue 54 0 qos dscp-queue 55 0 qos dscp-queue 56 7 qos dscp-queue 57 0 qos dscp-queue 58 0 qos dscp-queue 59 0 qos dscp-queue 60 0 qos dscp-queue 61 0 qos dscp-queue 62 0 qos dscp-queue 63 0
- [VLAN interface that received LLDP]
interface vlanX *Access VLAN is the object ip igmp snooping enable ip igmp snooping enable ... (Enable IGMP snooping) ip igmp snooping query-interval 30 ... (Set query transmission interval) ip igmp snooping querier ... (Set query) ip igmp snooping check ttl disable ... (Disable TTL value check function for IGMP packets)
- [LAN/SFP+ port that received LLDP]
interface portX.X qos trust dscp ... (Set DSCP trust mode) flowcontrol disable ... (Disable flow control) eee disable ... (Disable EEE)
In the case of USER mode, if you use the copy running-config startup-config command or the write command to save, the settings also apply to the startup-config that is used at next startup.
Even if the port to which the device is connected experiences a link-down state after automatic optimization settings, the automatically added settings are maintained.
This function can be used only for a physical interface (LAN/SFP+ port). It cannot be used with a link aggregated logical interface.
This does not apply to the trunk port.
In order to use this function, reception of LLDP frames must be enabled.
For this reason, make the following settings beforehand.
- Use the lldp run command to enable the system-wide LLDP function.
- Use the lldp-agent command to create an LLDP agent for the applicable interface.
- Use the set lldp command to specify the LLDP frame transmit/receive mode.
With the default settings of this product, LLDP frame transmission and reception is disabled.
4 Related Commands
Related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Set Dante automatic optimization settings function using LLDP | lldp auto-setting |
| Enable LLDP function | lldp run |
| Create LLDP agent | lldp-agent |
| Set LLDP transmission/reception mode | set lldp |
| Set flow control (system) | flowcontrol |
| Enable QoS | qos |
| Set DSCP - transmission queue ID conversion table | qos dscp-queue |
| Enable/disable IGMP snooping | ip igmp snooping |
| Set IGMP query transmission function | ip igmp snooping querier |
| Set IGMP query transmission interval | ip igmp snooping query-interval |
| Set IGMP packet TTL value checking function | ip igmp snooping check ttl disable |
| Set flow control (interface) | flowcontrol |
| Set QoS trust mode | qos trust |
| Set EEE | eee disable |
5 Examples of Command Execution
5.1 Automatic optimization settings using LLDP
Enable automatic optimization settings using LLDP.
Enable LLDP transmission and reception on port1.1.
Yamaha#configure terminal Yamaha(config)#interface port1.1 Yamaha(config-if)#lldp-agent ... (Create LLDP agent, change modes) Yamaha(lldp-agent)#set lldp enable txrx ... (Set LLDP transmission/reception mode) Yamaha(lldp-agent)#exit Yamaha(config-if)#exit Yamaha(config)#lldp run ... (Enable LLDP function) Yamaha(config)#lldp auto-setting enable ... (Enable automatic optimization settings via LLDP)
6 Points of Caution
- Note that if you use this function when settings such as QoS settings, flow control settings, EEE settings, and IGMP snooping have already been made, those settings are overwritten by Dante-optimized settings.
- It is assumed that you will use the Dante optimization setting function after you have made all of the basic switch settings (such as VLAN and IP).
If you make new changes to the settings (such as adding a VLAN), the Dante optimization settings will not follow.
- The setting values requested from Dante-enabled devices must be consistent between all devices. If the values are different, operation cannot be guaranteed.
- In general, IGMP snooping operates as version “3”.
7 Related Documentation
- SWP2 Series Technical Data (Basic Functions)
- Maintenance and operation functions
- List of preset settings
List of preset settings
The default settings of the SWP2 series are shown here, first the setting values of preset common parameters, followed by the setting values for specific preset types.
SWP2 Preset Common Parameters
System-wide default settings
| Category | Setting item | Setting value |
|---|---|---|
| Terminal settings | Console timeout | 600 seconds |
| Number of VTYs | 8 | |
| Number of lines displayed | 24 | |
| Password | Default administrative user | User name: admin Password: admin |
| Control password | admin | |
| Password encryption | Don’t encrypt | |
| Time management | Time zone | UTC±0 |
| NTP server | None | |
| NTP update cycle | Once per hour | |
| SNMP | Operation | Disabled |
| RMON | Operation | Enabled |
| SYSLOG | Debug level log output | OFF |
| Information level log output | ON | |
| Error level log output | ON | |
| SYSLOG server | None | |
| Firmware update | Download URL | firmware-update url http://www.rtpro.yamaha.co.jp/firmware/revisionup/swp2.bin |
| Permit downward revision | Don’t allow | |
| Timeout | 300 sec | |
| LLDP | Operation | Disabled |
| Automatic setting function | Disabled | |
| L2MS | Operation | Enabled (cannot be changed) |
| Role | Agent (cannot be changed) | |
| Stack | Operation | - |
| SYSLOG | Debug level log output | OFF |
| Information level log output | ON | |
| Error level log output | ON | |
| SYSLOG server | None | |
| Access control | Telnet server status | Start |
| Telnet server access | allow only VLAN #1 | |
| SSH server status | Don’t start | |
| TFTP server status | Don’t start | |
| HTTP server status | Start | |
| HTTP server access | Allow only VLAN #1 | |
| Secure HTTP server status | Don’t start | |
| Management VLAN | VLAN interface | VLAN #1 |
| Interface control | Link aggregation | None |
| Port authentication | Disabled | |
| Port security | Disabled | |
| PoE power supply | Enabled | |
| Layer2 function | Automatic MAC address acquisition | Enabled |
| Automatic MAC address acquisition ageing time | 300 seconds | |
| Spanning tree | Enabled | |
| Proprietary loop detection | Enabled | |
| Multiple VLAN | None | |
| Layer 3 function | Static routing | None |
| Routing between VLANs | Disabled | |
| Policy-based routing | - | |
| OSPF | - | |
| RIP | - | |
| VRRP | - | |
| IP multicast | IGMP snooping | Enabled |
| MLD snooping | Enabled | |
| IGMP | - | |
| PIM | - | |
| DNS client | Operation | Enabled |
| Traffic control | QoS | Enabled |
| QoS (DSCP-transmission queue ID conversion table)
| DSCP:8 → transmission queue:2 Other than above → transmission queue:0 | |
| Flow control (IEEE 802.3x) | Disabled | |
| ACL | None | |
| AP layer function | DHCP server | - |
| DHCP relay | - | |
| DNS relay | - | |
| RADIUS server | Disabled | |
| Web GUI | Language setting | English |
Common settings for each LAN/SFP+ port
| Category | Setting item | Setting value |
|---|---|---|
| Basic settings | Speed/communication mode setting | auto |
| Cross/straight automatic detection | Enabled | |
| MRU | 1,522 Byte | |
| Port description | None | |
| EEE | Disabled | |
| Port Mode | Depends on the preset | |
| Associated VLAN ID | Depends on the preset | |
| L2MS | L2MS filter | Depends on the preset |
| L2 switching | Spanning tree | Depends on the preset |
| Proprietary loop detection | Enabled | |
| Traffic control | QoS trust mode | DSCP |
| Flow control (IEEE 802.3x) | Disabled | |
| Storm control | Disabled | |
| LLDP Agent | Transmission/reception mode | Disabled |
| PoE power supply | Power supply operation | - |
| Power supply priority | - |
SWP2 Preset Type: Normal
Settings for the LAN/SFP+ ports
| Interface | L2MS Filter | LAG (Static) | Port Mode | VLAN | STP |
|---|---|---|---|---|---|
| port1.1 | Disable | - | Access | 1(default) | Disable |
| port1.2 | Disable | - | Access | 1(default) | Disable |
| port1.3 | Disable | - | Access | 1(default) | Disable |
| port1.4 | Disable | - | Access | 1(default) | Disable |
| port1.5 | Disable | - | Access | 1(default) | Disable |
| port1.6 | Disable | - | Access | 1(default) | Disable |
| port1.7 | Disable | - | Access | 1(default) | Disable |
| port1.8 | Disable | - | Access | 1(default) | Disable |
| port1.9 | Disable | - | Access | 1(default) | Disable |
| port1.10 | Disable | - | Access | 1(default) | Disable |
| port1.11 | Disable | - | Access | 1(default) | Enable |
| port1.12 | Disable | - | Access | 1(default) | Enable |
- Settings for VLAN
- VLAN #1 (for Dante and Control)
- IPv4 Address : DHCP
- IGMP Snooping: Enable
- Querier : Enable
- Querier-Interval : 30 sec
- Fast-leave : Disable
- Check TTL : Disable
- VLAN #1 (for Dante and Control)
SWP2 Preset Type: A
Settings for the LAN/SFP+ ports
| Interface | L2MS Filter | LAG (Static) | Port Mode | VLAN | STP |
|---|---|---|---|---|---|
| port1.1 | Disable | - | Access | 1(default) | Disable |
| port1.2 | Disable | - | Access | 1(default) | Disable |
| port1.3 | Disable | - | Access | 1(default) | Disable |
| port1.4 | Disable | - | Access | 1(default) | Disable |
| port1.5 | Disable | - | Access | 2 | Disable |
| port1.6 | Disable | - | Access | 2 | Disable |
| port1.7 | Disable | - | Access | 1(default) | Disable |
| port1.8 | Disable | - | Access | 1(default) | Disable |
| port1.9 | Disable | - | Access | 2 | Disable |
| port1.10 | Disable | - | Access | 2 | Disable |
| port1.11 | Disable | sa1 | Trunk | 1(native), 2 | Enable |
| port1.12 | Disable |
- Settings for VLAN
- VLAN #1 (for Dante)
- IPv4 Address : DHCP
- IGMP Snooping: Enable
- Querier : Enable
- Querier-Interval : 30 sec
- Fast-leave : Disable
- Check TTL : Disable
- VLAN #2 (for Control)
- IGMP Snooping: Disable
- VLAN #1 (for Dante)
SWP2 Preset Type: B
Settings for the LAN/SFP+ ports
| Interface | L2MS Filter | LAG (Static) | Port Mode | VLAN | STP |
|---|---|---|---|---|---|
| port1.1 | Disable | - | Access | 1(default) | Disable |
| port1.2 | Disable | - | Access | 1(default) | Disable |
| port1.3 | Disable | - | Access | 1(default) | Disable |
| port1.4 | Disable | - | Access | 1(default) | Disable |
| port1.5 | Disable | - | Access | 2 | Disable |
| port1.6 | Disable | - | Access | 2 | Disable |
| port1.7 | Disable | - | Access | 1(default) | Disable |
| port1.8 | Disable | - | Access | 2 | Disable |
| port1.9 | Disable | sa1 | Trunk | 1(native), 2 | Enable |
| port1.10 | Disable | ||||
| port1.11 | Disable | sa2 | Trunk | 1(native), 2 | Enable |
| port1.12 | Disable |
- Settings for VLAN
- VLAN #1 (for Dante)
- IPv4 Address : DHCP
- IGMP Snooping: Enable
- Querier : Enable
- Querier-Interval : 30 sec
- Fast-leave : Disable
- Check TTL : Disable
- VLAN #2 (for Control)
- IGMP Snooping: Disable
- VLAN #1 (for Dante)
SWP2 Preset Type: C
Settings for the LAN/SFP+ ports
| Interface | L2MS Filter | LAG (Static) | Port Mode | VLAN | STP |
|---|---|---|---|---|---|
| port1.1 | Disable | - | Access | 1(default) | Disable |
| port1.2 | Disable | - | Access | 1(default) | Disable |
| port1.3 | Disable | - | Access | 1(default) | Disable |
| port1.4 | Enable | - | Access | 2 | Disable |
| port1.5 | Enable | - | Access | 2 | Disable |
| port1.6 | Enable | - | Access | 2 | Disable |
| port1.7 | Disable | - | Access | 1(default) | Disable |
| port1.8 | Disable | - | Access | 1(default) | Disable |
| port1.9 | Enable | - | Access | 2 | Disable |
| port1.10 | Enable | - | Access | 2 | Disable |
| port1.11 | Disable | - | Access | 1(default) | Disable |
| port1.12 | Enable | - | Access | 2 | Disable |
- Settings for VLAN
- VLAN #1 (for Dante)
- IPv4 Address : DHCP
- IGMP Snooping: Enable
- Querier : Enable
- Querier-Interval : 30 sec
- Fast-leave : Disable
- Check TTL : Disable
- VLAN #2 (for Control)
- IGMP Snooping: Enable
- Querier : Enable
- Querier-Interval : 30 sec
- Fast-leave : Disable
- Check TTL : Disable
- IGMP Snooping: Enable
- VLAN #1 (for Dante)
- SWP2 Series Technical Data (Basic Functions)
- Interface control functions
Interface control functions
- SWP2 Series Technical Data (Basic Functions)
- Interface control functions
- Interface basic functions
Interface basic functions
1 Function Overview
Here we explain the basic interface functions of this product.
2 Definition of Terms Used
None
3 Function Details
3.1 Interface types
This product can handle the five interface types shown in the table below.
Interface list
| Interface types | Interface ID | Explanation |
|---|---|---|
| LAN port | port | A physical port of this product. There are two types: a fixed LAN port and an SFP+ port. This interface is expressed as port followed by “stack ID” + “.” + “port number printed on the chassis.” Specifying LAN port #1: port1.1 |
| SFP+ port | ||
| VLAN interface | vlan | A user-defined VLAN. This interface is expressed as vlan followed by “VLAN ID.” Specifying VLAN1: vlan1 |
| Static logical interface | sa | This is the user-defined link aggregation. Multiple LAN/SFP+ ports can be grouped together and used as one interface. This interface is expressed as “sa” or “po,” followed by “logical link ID.” Specifying the LACP logical interface for logical link ID #1: po1 |
| LACP logical interface | po |
3.2 Interface control
The interface on this product can be controlled as shown in the table below.
Interface control items
| Control items | Commands | Explanation |
|---|---|---|
| Set description | description | Sets the description text for the applicable interface. |
| Enable/disable | shutdown | Enables/disables the interface. |
| Communication speed/communication mode | speed-duplex | Sets the communication speed and communication mode for the interface. (Select from the following values.) - Auto negotiation - 10 Gbps / full duplex - 1 Gbps / full duplex - 100 Mbps / full duplex - 100 Mbps / half duplex - 10 Mbps / full duplex - 10 Mbps / half duplex |
| MRU | mru | Sets the maximum frame size that can be received by the interface, within a range of 64–10,240 bytes. |
| Cross/straight automatic detection (Auto MDI/MDI-X function) | mdix | This function automatically determines the connection-destination port type (MDI or MDI-X), and allows interconnection regardless of the cable type (cross or straight). xx |
| Speed downshift | - | This function automatically drops the speed and tries to link, when a LAN cable is connected for which 1000BASE-T cannot be used. This function is always enabled for LAN ports. (Cannot be disabled.) |
| EEE | power | Specifies whether EEE (Energy-Efficient Ethernet) is used. This is standard for IEEE 802.3az. |
Command control of the interface is performed as shown on the table below.
Interface control functionality chart
| Interface name | Set description | Enable/disable | Communication speed/communication mode | MRU | Cross/straight automatic detection | EEE |
|---|---|---|---|---|---|---|
| LAN port | ✓ | ✓ | ✓ (*1) | ✓ | ✓ | ✓ |
| SFP+ port | ✓ | ✓ | ✓ (*2) | ✓ | - | - |
| VLAN interface | ✓ | - | - | - | - | - |
| Static logical interface | ✓ | ✓ | - | - | - | - |
| LACP logical interface | ✓ | ✓ | - | - | - | - |
*1: As the communication speed / communication mode setting for a LAN port, it is not possible to select 10 Gbps / full-duplex.
*2: The communication speed / communication mode setting for an SFP+ port will be either auto negotiation or 10 Gbps / full-duplex.
3.3 LAN/SFP+ port defaults
Initially, this product’s LAN/SFP+ ports will be in the following state.
- All LAN/SFP+ ports function as access ports (ports that handle untagged frames), and belong to the default VLAN (VLAN #1).
- The following functions are enabled for the default VLAN (VLAN #1) to which all LAN/SFP+ ports belong.
- MSTP: Multiple Spanning Tree Protocol
- IGMP Snooping
- IPv4 address (192.168.100.240/24)
- Access from a TELNET client
- Access from a web client
3.4 Port mirroring
This product provides a port mirroring function, which copies the data traffic from a selected LAN/SFP+ port to another specified port.
The communication status can be analyzed by collecting the copied packets.
The product enables specifying up to one sniffer port.
The monitoring direction (send/received, send only, or receive only) can be selected for monitoring ports.
The mirror command can be used to set the port mirroring.
The port mirroring setting is disabled in default settings.
3.5 Frame counter
This product counts the number of frames transmitted/received for each LAN/SFP+ port. (This is called a “frame counter”.)
To reference the frame counter, use the show frame counter command.
The table below shows the display items for the frame counter and their maximum values.
Received frame counter display items
| Display item | Explanation | Maximum value |
|---|---|---|
| Octets | Number of octets received | 18,446,744,073,709,551,615 |
| Packets (*1) | Number of packets received | 34,359,738,360 |
| Broadcast packets (*2) | Number of broadcast packets received | 4,294,967,295 |
| Multicast packets (*2) | Number of multicast packets received | 4,294,967,295 |
| Unicast packets (*2) | Number of unicast packets received | 4,294,967,295 |
| Undersize packets (*2) | Number of undersize packets received (packets smaller than 64 octets) | 4,294,967,295 |
| Oversize packets (*2) | Number of oversize packets received (packets larger than 1,523 octets (*3)) | 4,294,967,295 |
| Fragments (*2) | Number of fragment packets received (packets smaller than 64 octets whose CRC is incorrect) | 4,294,967,295 |
| Jabbers (*2) | Number of jabber packets received (packets larger than 1,523 octets whose CRC is incorrect (*3)) | 4,294,967,295 |
| FCS errors (*2) | Number of FCS error packets received | 4,294,967,295 |
| RX errors | Number of reception errors | 4,294,967,295 |
| Drop packets (*4) | Number of packets dropped from the reception buffer | 4,294,967,295 |
(*1): Packets is the total value of the (*2) packets.
(*3): This will change, depending on the MRU that is set for the LAN/SFP+ port.
(4): This is shown only if tail drop is disabled.
Transmitted frame counter display items
| Display item | Explanation | Maximum value |
|---|---|---|
| Octets | Number of octets transmitted | 18,446,744,073,709,551,615 |
| Packets (*1) | Number of packets transmitted | 12,884,901,885 |
| Broadcast packets (*2) | Number of broadcast packets transmitted | 4,294,967,295 |
| Multicast packets (*2) | Number of multicast packets transmitted | 4,294,967,295 |
| Unicast packets (*2) | Number of unicast packets received | 4,294,967,295 |
| TX errors | Number of transmission errors | 4,294,967,295 |
| Collisions | Number of collision occurrences | 4,294,967,295 |
| Drop Packets(*3) | Number of tail-dropped transmission packets | 536,870,911 |
(*1): The packet value is the total of the (*2) packets.
(3): This is shown only if tail drop is enabled.
Transmitted/received frame counter display items
| Display item | Explanation | Maximum value |
|---|---|---|
| 64 octet packets | Number of packets with 64 octet length transmitted/received | 4,294,967,295 |
| 65–127 octet packets | Number of packets with 65–127 octet length transmitted/received | 4,294,967,295 |
| 128–255 octet packets | Number of packets with 128–255 octet length transmitted/received | 4,294,967,295 |
| 256–511 octet packets | Number of packets with 256–511 octet length transmitted/received | 4,294,967,295 |
| 512–1,023 octet packets | Number of packets with 512–1,023 octet length transmitted/received | 4,294,967,295 |
| 1,024–MAX octet packets | Number of packets with 1,024–maximum octet length (*1) transmitted/received | 4,294,967,295 |
(*1): This will change, depending on the MRU that is set for the LAN/SFP+ port.
The frame counter can also be cleared by using the clear counters command.
When you execute the show interface command to show the state of the LAN/SFP+ ports, the number of transmitted/received frames is shown, but this information is shown based the information of the frame counter.
The number of frames transmitted/received that is displayed using the show interface command and how the frame counter is handled are shown below.
Number of frames transmitted/received that is displayed by the show interface command, and how the frame counter is handled
| Display item | Information on the frame counter referred to | |
|---|---|---|
| input | packets | Received frame counter packets |
| bytes | Received frame counter octets | |
| multicast packets | Received frame counter multicast packets | |
| drop packets(*1) | Received frame counter drop packets | |
| output | packets | Transmitted frame counter packets |
| bytes | Transmitted frame counter octets | |
| multicast packets | Transmitted frame counter multicast packets | |
| broadcast packets | Transmitted frame counter broadcast packets | |
| drop packets(*1) | Transmitted frame counter drop packets | |
(*1) If tail drop is enabled this shows only the transmission information; if it is disabled this shows only the reception information.
3.6 SFP+ module optical receive level monitoring
This product provides functionality for monitoring the optical receive level of an SFP+ module connected to the SFP+ port.
If a fault occurs in an SFP+ module’s optical receive level, this product’s port lamp indications change to a dedicated state, and a SYSLOG message is output.
An optical receive level fault state can be forcibly cleared by holding down the MODE switch for three seconds.
When the optical receive level returns to the normal range, this product’s port lamp indications will recover, and a SYSLOG message is output.
A SYSLOG message is not output if the corresponding port’s link status goes down, or if the optical receive level fault state is forcibly cleared.
The SFP+ module’s optical receive level monitoring settings can be made using the sfp-monitor command.
By default, SFP+ module optical receive level monitoring is enabled.
3.7 Transmit queue usage monitoring
If the transmit queue’s usage ratio becomes high (above 60%, above 100%), a SYSLOG message is output.
A SYSLOG message is also output when the transmit queue’s usage ratio returns to the normal range (below 50%).
The tx-queue-monitor command can be used to specify the transmission queue usage monitoring setting (for the overall system or individual LAN/SFP ports).
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
Basic interface functions: list of related commands
| Operations | Operating commands |
|---|---|
| Set description | description |
| Shutdown | shutdown |
| Set communication speed and communication mode | speed-duplex |
| Set MRU | mru |
| Set cross/straight automatic detection | mdix auto |
| Set EEE | eee |
| Show EEE capabilities | show eee capabilities |
| Show EEE status | show eee status |
| Set port mirroring | mirror |
| Show port-mirroring status | show mirror |
| Show interface status | show interface |
| Show brief interface status | show interface brief |
| Show frame counter | show frame-counter |
| Clear frame counters | clear counters |
| Show SFP+ status | show ddm status |
| Set SFP+ module optical receive level monitoring | sfp-monitor rx-power |
| Set transmission queue usage monitoring setting (system) | tx-queue-monitor usage-rate |
| Set transmission queue usage monitoring setting (LAN/SFP ports) | tx-queue-monitor usage-rate |
| Show the transmission queue usage monitoring setting | show tx-queue-monitor |
| Resets interface | interface reset |
5 Examples of Command Execution
5.1 Basic LAN port settings
Some examples of basic LAN port settings are shown below.
For details on how to make the settings, refer to the Command Reference.
- Set the description text for LAN port #1 (port1.1).
Yamaha(config)#interface port1.1 Yamaha(config-if)#description Connected to rtx1200-router
- Disable LAN port #1 (port1.1).
Yamaha(config)#interface port1.1 Yamaha(config-if)#shutdown
- Enable LAN port #1 (port1.1).
Yamaha(config)#interface port1.1 Yamaha(config-if)#no shutdown
- Set the communication speed and communication mode for LAN port #1 (port1.1) to 100Mbps/Full.
Yamaha(config)#interface port1.1 Yamaha(config-if)#speed-duplex 100-full
5.2 Set port mirroring
In this example, we will set LAN port #1 to monitor the frames transmitted/received by LAN port #4 and the frames transmitted by LAN port #5.
The roles of the ports are shown below.
- Sniffer port: LAN port #1 (port1.1)
- Monitoring port: LAN port #4 (port1.4), LAN port #5 (port1.5)
- Specifies the monitoring port setting for LAN port #1 (port 1.1), which is a sniffer port.
Yamaha(config)#interface port1.1 Yamaha(config-if)#mirror interface port1.4 direction both ... (monitor transmitted/received frames) Yamaha(config-if)#mirror interface port1.5 direction transmit ... (monitor transmitted frames)
- Checks the port mirroring setting.
Yamaha#show mirror Sniffer Port Monitored Port Direction ============= ============== ========== port1.1 port1.4 both port1.1 port1.5 transmit
5.3 Show LAN/SFP+ port information
- Confirm the status of LAN port #1 (port1.1).
Yamaha#show interface port 1.1 Interface port1.1 Link is UP Hardware is Ethernet HW addr: 00a0.deae.b89f Description: Connected to router ifIndex 5001, MRU 1522 Speed-Duplex: auto(configured), 1000-full(current) Auto MDI/MDIX: on Vlan info : Switchport mode : access Ingress filter : enable Acceptable frame types : all Default Vlan : 1 Configured Vlans : 1 Interface counter: input packets : 0 bytes : 0 multicast packets: 0 output packets : 0 bytes : 0 multicast packets: 0 broadcast packets: 0 drop packets : 0
6 Points of Caution
None
7 Related Documentation
None
Link aggregation
1 Function Overview
Link aggregation is a function used to combine multiple LAN/SFP ports that connect network devices, and handle them as a single logical interface.
Link aggregation is a technology that is useful when multiple communications occur. Communications can be distributed by using a load balance function within the combined lines.
If one LAN/SFP port fails within the lines that were combined using link aggregation, and communications cannot be made, the other ports will continue communicating.
Link aggregation function overview
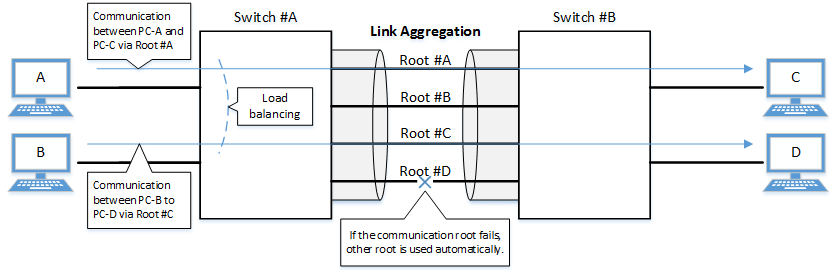
The link aggregation functions in this switch are shown below.
Link aggregation functions
| Functions provided | Contents |
|---|---|
| Static link aggregation | Link aggregation for manually setting the LAN/SFP ports to combine. This begins to operate as a logical interface when the LAN/SFP ports link up. |
| LACP link aggregation | Link aggregation that uses LACP to combine the LAN/SFP ports. This begins to operate as a logical interface when the negotiation via LACP between the connected devices is successful. |
2 Definition of Terms Used
- LACP
Abbreviation for “Link Aggregation Control Protocol”. This is a technology standardized in IEEE802.1AX-2008, and is also called EtherChannel.
- Load balance
This is a function to distribute forwarded frames between the LAN/SFP ports that are associated with the logical interface.
As a distribution rule, the L2/L3/L4 information within frames is used.
3 Function Details
3.1 Static/LACP link aggregation: common specifications
The common specifications for the static/LACP link aggregation functions of this switch are shown below.
- The link aggregation on this switch can be defined for 127 interfaces, including both static and LACP.
A single logical interface can be associated with up to eight LAN/SFP ports.
- The settings shown below must be the same for each of the LAN/SFP ports contained within.
- Port mode (access/trunk [including native VLAN settings])
- Associated VLAN
- QoS trust mode (including port priority and default CoS settings)
- Executes the following process when a LAN/SFP port is associated with a logical interface.
- LAN/SFP ports that are linked up will be linked down.
The logical interface’s default value will be set to shutdown, in order to safely integrate the logical interface into the system.
- MSTP settings will be discarded and will revert to their defaults.
When dissociating a LAN/SFP port from the logical link, the MSTP settings for the relevant port will revert to their defaults as well.
- LAN/SFP ports that are linked up will be linked down.
- The following operations can be performed for the logical interface.
- Add description text (description command)
- Enable/disable the interface (shutdown command)
- Another LAN/SFP port cannot be associated with a logical interface in operation.
To associate a LAN/SFP port, make sure to shut down the logical interface before associating.
- LAN/SFP ports that are associated with a logical interface that is in operation cannot be removed.
When dissociating a LAN/SFP port, make sure to shut down the logical interface before dissociating.
LAN/SFP ports that have been dissociated from a logical interface will be in shutdown mode. Enable the ports as necessary (using “no shutdown”).
- Load balance settings can be made on the logical interface. The rules that can be set for this are shown below.
The default value when defining a logical interface is the destination/source MAC address.
- Destination MAC address
- Source MAC address
- Destination/source MAC address
- Destination IP address
- Source IP address
- Destination/source IP address
- Destination port number
- Source port number
- Destination/source port number
3.2 Static link aggregation
The operating specifications for static link aggregation are shown below.
- An interface number from 1–96 can be assigned to the static logical interface.
- Use the static-channel-group command to associate a LAN/SFP port with a static logical link interface.
- When associating a LAN/SFP port with an interface number for which there is no static logical interface, a new logical interface will be generated.
- When the associated port no longer exists as a result of removing a LAN/SFP port from a static logical interface, the relevant logical interface will be deleted.
- Use the show static-channel-group command to show the static logical link interface’s status.
3.3 LACP link aggregation
The operating specifications for LACP link aggregation are shown below.
Refer to “3.1 Static/LACP link aggregation: common specifications” for the common specifications of static link aggregation.
- An interface number from 1–127 can be assigned to the LACP logical interface.
- Use the channel-group command to associate a LAN/SFP port with an LACP logical link interface.
- When associating an LAN/SFP, specify the following operating modes. (It is recommended to specify “active mode”.)
- Active mode
The LACP frame will be voluntarily transmitted, and negotiation with the opposing device’s port will begin.
- Passive mode
The LACP frame will not be voluntarily transmitted, but will instead be transmitted when a frame is received from the opposing device.
- Active mode
- When associating a LAN/SFP port with an interface number for which there is no LACP logical interface, a new logical interface will be generated.
- When the associated port no longer exists as a result of removing a LAN/SFP port from an LACP logical interface, the relevant logical interface will be deleted.
- When associating an LAN/SFP, specify the following operating modes. (It is recommended to specify “active mode”.)
- The parameters that influence the operations of the LACP logical interface are shown below.
- LACP timeout
LACP timeout indicates the down time that was determined, when an LACP frame has not been received from the opposing device.
Specify either “Long” (90 sec.) or “Short” (3 sec.) using the lacp timeout command.
The LACP timeout value is stored in the LACP frame and transmitted to the opposing device.
The opposing device that received the frame will transmit the LACP frames it has stored at intervals equaling 1/3 of the LACP timeout value.
The default value when the logical interface is generated is “Long (90 sec.)”.
- LACP system priority
The LACP system priority is used when deciding which device will control the logical interface, when communicating with the opposing device. The LACP system priority and MAC address values (in combination referred to as the system ID) are exchanged with the interfacing device and the device with the highest LACP system priority level is assigned control. If both devices have the same LACP system priority level, the device with the lower MAC address is assigned control.
The device assigned control determines which LAN or SFP ports associated with the logical interface are enabled (activated).
LACP system priority values within the range 1 to 65535 can be specified using the lacp system-priority command, where the lower the setting value, the higher the priority level. The default value when the logical interface is generated is set to 32768 (0x8000).
- LACP port priority
LACP port priority is used to control active/standby for the LAN/SFP ports that are associated with the logical interface. If more than the maximum number of LAN/SFP ports (8 ports) is associated with a logical interface, then the port status is controlled based on the LACP port priority.
If ports have the same LACP port priority, then the port with the lower port number is given priority.
LACP system priority values within the range 1 to 65535 can be specified using the lacp port-priority command, where the lower the setting value, the higher the priority level. The default LACP port priority setting is 32768 (0x8000).
- LACP timeout
- LAN/SFP ports in half-duplex communication mode do not support LACP link aggregation.
- Half-duplex LAN/SFP ports that are associated with an LACP logical interface are never activated.
- The following describes actions that occur if LAN/SFP ports with different communication speeds are located on the same logical interface.
To configure link aggregation with a mixture of different communication speeds, enable multi-speed link aggregation.
- Actions if multi-speed link aggregation is enabled (lacp multi-speed enable)
- Activate all associated ports (up to a maximum 8 ports), regardless of communication speed.
- Load balancing treats all associated ports as equivalent.
- That increases the risk of a communication overflow occurring at a slow affiliated port.
- If there are more than the maximum 8 LAN/SFP ports, higher priority values are assigned to faster affiliated ports.
- If the other device cannot accept a different communication speed, then both interacting devices mutually exchange lists of affiliated ports and activate affiliated port that can be used by both devices.
Consequently, the process is limited by the device that cannot accept different communication speeds.
- Actions if multi-speed link aggregation is disabled (lacp multi-speed disable)
- Only affiliated ports with a communication speed the same as the port first linked up are activated.
- Other ports with a different communication speed remain in standby mode.
- If auto negotiation is enabled, only affiliated ports with a communication speed that is the same as the negotiation result of the first negotiation will be activated.
- If links go down for all the ports first linked up, then the link will go down for the LACP logical interface as well.
- Only affiliated ports with a communication speed the same as the port first linked up are activated.
- Actions if multi-speed link aggregation is enabled (lacp multi-speed enable)
- The show etherchannel command can be used to check the LACP logical interface status.
- The show etherchannel status detail command can be used to check the activation status of affiliated ports.
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating Commands |
|---|---|
| Set the static logical interface | static-channel-group |
| Show the static logical interface status | show static-channel-group |
| Set the LACP logical interface | channel-group |
| Set LACP system priority | lacp system-priority |
| Show LACP system priority | show lacp sys-id |
| LACP multi-speed link aggregation setting | lacp multi-speed |
| Set LACP timeout | lacp timeout |
| Clear LACP packet counter | clear lacp |
| Show LACP packet counter | show lacp counters |
| Show the status of the LACP logical interface | show etherchannel |
| Set load balance function rules | port-channel load-balance |
5 Examples of Command Execution
5.1 Setting the static logical interface
In this example, we will set link aggregation to use four LAN ports, in order to communicate between switches.
- Static logical interface setting example
- Static link aggregation is set to static.
The logical interface numbers are set to switch A: #2 and switch B: #5.
- The LAN ports associated with the logical interface are all access ports, and are associated with the VLAN #1000.
- Define [switch A] VLAN #1000, and associate it with LAN ports (#1, #2, #3, #4, #8).
Together with this, associate LAN ports (#1, #2, #3, #4) with the logical interface #2.
Yamaha(config)#vlan database ... (VLAN-ID #1000 definition) Yamaha(config-vlan)#vlan 1000 Yamaha(config-vlan)#exit Yamaha(config)#interface port1.8 ... (Set LAN port #8) Yamaha(config-if)#switchport access vlan 1000 ... (Set as access port, and associate with VLAN #1000) Yamaha(config-if)#interface port1.1 ... (Set LAN port #1) Yamaha(config-if)#switchport access vlan 1000 ... (Set as access port, and associate with VLAN #1000) Yamaha(config-if)#static-channel-group 2 ... (Associate with logical interface #2) Yamaha(config-if)#interface port1.2 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)#static-channel-group 2 Yamaha(config-if)#interface port1.3 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)#static-channel-group 2 Yamaha(config-if)#interface port1.4 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)#static-channel-group 2
- Confirm the setting status of [switch A] logical interface #2.
Yamaha#show static-channel-group % Static Aggregator: sa2 % Member: port1.1 port1.2 port1.3 port1.4
- Define [switch B] VLAN #1000, and associate it with LAN ports (#1, #2, #3, #4, #7).
Together with this, associate LAN ports (#1, #2, #3, #4) with the logical interface #5.
Yamaha(config)#vlan database Yamaha(config-vlan)#vlan 1000 Yamaha(config-vlan)#exit Yamaha(config)#interface port1.7 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)#interface port1.1 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)#static-channel-group 5 Yamaha(config-if)#interface port1.2 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)#static-channel-group 5 Yamaha(config-if)#interface port1.3 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)#static-channel-group 5 Yamaha(config-if)#interface port1.4 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)#static-channel-group 5
- Confirm the setting status of [switch B] logical interface #5.
Yamaha#show static-channel-group % Static Aggregator: sa5 % Member: port1.1 port1.2 port1.3 port1.4
- Enable [switch A] logical interface.
Yamaha(config)#interface sa2 ... (Set logical interface #2) Yamaha(config-if)#no shutdown ... (Enable logical interface)
- Enable [switch B] logical interface.
Yamaha(config)#interface sa5 ... (Set logical interface #5) Yamaha(config-if)#no shutdown ... (Enable logical interface)
- Confirm the setting status of [switch A] logical interface.
Yamaha#show interface sa2 Interface sa2 Link is UP ... (is enabled) Hardware is AGGREGATE ifIndex 4502, MRU 1522 Vlan info : Switchport mode : access Ingress filter : enable Acceptable frame types : all Default Vlan : 1000 Configured Vlans : 1000 Interface counter: input packets : 1020 bytes : 102432 multicast packets: 1020 output packets : 15 bytes : 1845 multicast packets: 15 broadcast packets: 0 - Confirm the setting status of [switch B] logical interface.
Yamaha#show interface sa5 Interface sa5 Link is UP Hardware is AGGREGATE ifIndex 4505, MRU 1522 Vlan info : Switchport mode : access Ingress filter : enable Acceptable frame types : all Default Vlan : 1000 Configured Vlans : 1000 Interface counter: input packets : 24 bytes : 2952 multicast packets: 24 output packets : 2109 bytes : 211698 multicast packets: 2109 broadcast packets: 0
5.2 Setting the LACP logical interface
In this example, we will set link aggregation to use four LAN ports, in order to communicate between switches.
- Set the LACP logical interface
- Use LACP for link aggregation.
The logical interface numbers are set to switch A: #10 and switch B: #20.
Set the switch A logical interface to active status, and the switch B logical interface to passive status.
- The LAN ports associated with the logical interface are all access ports, and are associated with the VLAN #1000.
- For load balance, set the destination/source IP address.
- Define [switch A] VLAN #1000, and associate it with LAN ports (#1, #2, #3, #4, #8).
Together with this, associate LAN ports (#1, #2, #3, #4) in active status with the logical interface #10.
The logical interface at this point in time will be in shutdown mode.
Yamaha(config)#vlan database Yamaha(config-vlan)#vlan 1000 ... (VLAN #1000 definition) Yamaha(config-vlan)#exit Yamaha(config)#interface port1.8 Yamaha(config-if)#switchport access vlan 1000 ... (Set as access port, and associate with VLAN #1000) Yamaha(config-if)#interface port1.1 Yamaha(config-if)#switchport access vlan 1000 ... (Set as access port, and associate with VLAN #1000) Yamaha(config-if)#channel-group 10 mode active ... (Associate with logical interface #10 in an active status) Yamaha(config-if)#interface port1.2 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)# channel-group 10 mode active Yamaha(config-if)#interface port1.3 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)# channel-group 10 mode active Yamaha(config-if)#interface port1.4 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)# channel-group 10 mode active
- Confirm the setting status of [switch A] logical interface #10.
Yamaha#show etherchannel % Lacp Aggregator: po10 % Member: port1.1 port1.2 port1.3 port1.4 Yamaha#show lacp sys-id ... (Check LACP system ID: set to the default value (0x8000)) % System 8000,00-a0-de-ae-b9-1f Yamaha#show interface po10 Interface po10 Link is DOWN ... (Link is down) Hardware is AGGREGATE ifIndex 4610, MRU 1522 Vlan info : Switchport mode : access Ingress filter : enable Acceptable frame types : all Default Vlan : 1000 Configured Vlans : 1000 Interface counter: input packets : 0 bytes : 0 multicast packets: 0 output packets : 0 bytes : 0 multicast packets: 0 broadcast packets: 0 - Define [switch B] VLAN #1000, and associate it with LAN ports (#1, #2, #3, #4, #7).
Together with this, associate LAN ports (#1, #2, #3, #4) in passive status with the logical interface #20.
The logical interface at this point in time will be in shutdown mode.
Yamaha(config)#vlan database Yamaha(config-vlan)#vlan 1000 ... (VLAN #1000 definition) Yamaha(config-vlan)#exit Yamaha(config)#interface port1.7 Yamaha(config-if)#switchport access vlan 1000 ... (Set as access port, and associate with VLAN #1000) Yamaha(config-if)#interface port1.1 Yamaha(config-if)#switchport access vlan 1000 ... (Set as access port, and associate with VLAN #1000) Yamaha(config-if)#channel-group 20 mode passive ... (Associate with logical interface #20 in a passive status) Yamaha(config-if)#interface port1.2 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)# channel-group 20 mode passive Yamaha(config-if)#interface port1.3 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)# channel-group 20 mode passive Yamaha(config-if)#interface port1.4 Yamaha(config-if)#switchport access vlan 1000 Yamaha(config-if)# channel-group 20 mode passive
- Confirm the setting status of [switch B] logical interface #20.
Yamaha#show etherchannel % Lacp Aggregator: po20 % Member: port1.1 port1.2 port1.3 port1.4 Yamaha#show lacp sys-id ... (Check LACP system ID: set to the default value (0x8000)) % System 8000,00-a0-de-ae-b8-7e Yamaha#show interface po20 Interface po20 Link is DOWN ... (Link is down) Hardware is AGGREGATE ifIndex 4620, MRU 1522 Vlan info : Switchport mode : access Ingress filter : enable Acceptable frame types : all Default Vlan : 1000 Configured Vlans : 1000 Interface counter: input packets : 0 bytes : 0 multicast packets: 0 output packets : 0 bytes : 0 multicast packets: 0 broadcast packets: 0 - Set the load balance of [switch A] to the destination/source IP address, and enable.
Yamaha(config)#port-channel load-labance src-dst-ip ... (Set load balancing) Yamaha(config)#interface po10 ... (Set logical interface #10) Yamaha(config-if)#no shutdown ... (Enable logical interface)
- Set the load balance of [switch B] to the destination/source IP address, and enable.
Yamaha(config)#port-channel load-labance src-dst-ip ... (Set load balancing) Yamaha(config)#interface po20 ... (Set logical interface #20) Yamaha(config-if)#no shutdown ... (Enable logical interface)
- Confirm the setting status of [switch A] logical interface.
Link up and confirm whether frames are being sent and received.
Yamaha#show interface po10 Interface po10 Link is UP Hardware is AGGREGATE ifIndex 4610, MRU 1522 Vlan info : Switchport mode : access Ingress filter : enable Acceptable frame types : all Default Vlan : 1000 Configured Vlans : 1000 Interface counter: input packets : 560 bytes : 58239 multicast packets: 560 output packets : 98 bytes : 12474 multicast packets: 98 broadcast packets: 0 Yamaha# Yamaha#show lacp-counter % Traffic statistics Port LACPDUs Marker Pckt err Sent Recv Sent Recv Sent Recv % Aggregator po10 , ID 4610 port1.1 50 47 0 0 0 0 port1.2 49 46 0 0 0 0 port1.3 49 46 0 0 0 0 port1.4 49 46 0 0 0 0 - Confirm the setting status of [switch B] logical interface.
Link up and confirm whether frames are being sent and received.
Yamaha#show interface po20 Interface po20 Link is UP Hardware is AGGREGATE ifIndex 4620, MRU 1522 Vlan info : Switchport mode : access Ingress filter : enable Acceptable frame types : all Default Vlan : 1000 Configured Vlans : 1000 Interface counter: input packets : 78 bytes : 9914 multicast packets: 78 output packets : 438 bytes : 45604 multicast packets: 438 broadcast packets: 0 Yamaha# Yamaha#show lacp-counter % Traffic statistics Port LACPDUs Marker Pckt err Sent Recv Sent Recv Sent Recv % Aggregator po20 , ID 4620 port1.1 55 57 0 0 0 0 port1.2 54 56 0 0 0 0 port1.3 54 56 0 0 0 0 port1.4 54 56 0 0 0 0
6 Points of Caution
- A host port that is associated with a private VLAN cannot be aggregated as a link aggregation logical interface.
- If access list settings exist for the received frame of a LAN/SFP port, the ports cannot be aggregated as a link aggregation logical interface.
7 Related Documentation
- LAN/SFP port control: Interface basic functions
- SWP2 Series Technical Data (Basic Functions)
- Interface control functions
- Port authentication functions
Port authentication functions
1 Function Overview
Port authentication is a function that authenticates devices or users.
This authenticates a device connected to the LAN/SFP+ port, and permits LAN access only for devices that succeeded in authenticating.
Devices that are not yet authenticated or that failed to authenticate can be denied access to the LAN, or permitted to access only a specific VLAN.
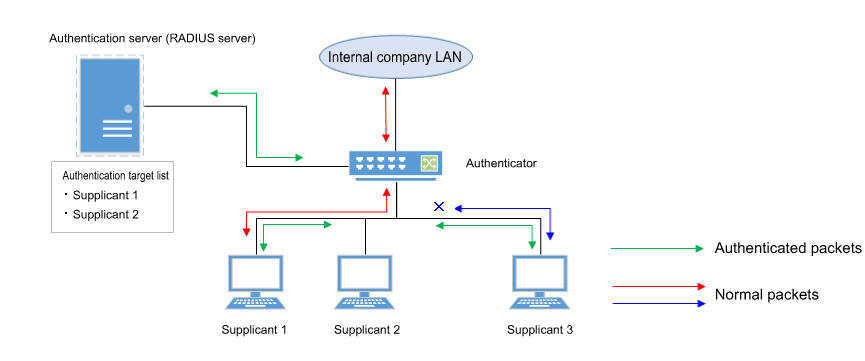
2 Definition of Terms Used
- IEEE 802.1X
The authentication standard used when connecting to the LAN.
- Authenticator
A device or software that authenticates a supplicant connected to a LAN/SFP+ port.
It mediates between the supplicant and the authentication server, controlling access to the LAN according to the success or failure of authentication.
- Supplicant
A device or software that connects to an authenticator and receives authentication.
- Authentication server
A device or software that authenticates a supplicant that is connected via the authenticator.
This manages authentication information such as user names, passwords, MAC addresses, and associated VLANs.
- EAP (Extended authentication protocol)
This is an authentication protocol that extends PPP, allowing various authentication methods to be used.
This is defined in RFC3748.
- EAP over LAN (EAPOL)
This is a protocol for conveying EAP packets between the supplicant and the authenticator.
- EAP over Radius
This is a protocol for conveying EAP packets between the authenticator and the authentication server (RADIUS server).
- EAP-MD5 (Message digest algorithm 5)
Client authentication using user name and password.
This uses an MD5 hash value to authenticate.
- EAP-TLS (Transport Layer Security)
This uses the digital certificates of the server and the client to authenticate.
With the transport layer encrypted, the digital certificates are exchanged and authenticated.
This is defined in RFC2716 and RFC5216.
- EAP-TTLS (Tunneled TLS)
This is an extended version of EAP-TLS.
This uses the digital signature of the server to establish a TLS communication route, and within this encrypted communication route uses a password to authenticate the client.
This is defined in RFC5281.
- EAP-PEAP (Protected EAP)
The principle of operation is equivalent to EAP-TTLS (the only difference is the protocol inside the encrypted tunnel).
This uses the digital signature of the server to establish a TLS communication route, and within this encrypted communication route uses a password to authenticate the client.
3 Function Details
The operating specifications for port authentication are shown below.
As port authentication functions, this product supports IEEE 802.1X authentication, MAC authentication, and web authentication.
The following table shows the distinctive features of each authentication method.
Port authentication method features
| MAC authentication | IEEE 802.1X authentication | Web authentication | |
|---|---|---|---|
| Authenticated element | MAC address | User name and password (EAP-MD5, EAP-TTLS, EAP-PEAP) | User name and password |
| Authenticated object (supplicant) | Device | Device or user | Device or user |
| Functionality needed by supplicant | None | IEEE 802.1X authentication | Web browser |
| Operation when authenticating | None | User name and password entry (EAP-MD5, EAP-TTLS, EAP-PEAP) | User name and password entry |
This product assumes a RADIUS server as the authentication server.
Note that the port authentication functionality of this product has the following limitations.
- The number of supplicants that can be authenticated is one for each port in single host mode or multi-host mode, and in multi-supplicant mode is a maximum of 512 for the entire system.
- It cannot be used on a private VLAN port.
- It cannot be used on a voice VLAN port.
- If port authentication is enabled, a spanning tree topology change will occur according to the authentication result.
If you want to avoid this, specify “spanning-tree edgeport” for the authentication port to which the supplicant will be connected.
- Web authentication can be used only in multi-supplicant mode.
- Web authentication cannot be used together with a guest VLAN.
- Trunk ports can only be used in multi-supplicant mode.
- Trunk ports cannot use dynamic or guest VLANs.
- If L2MS functionality is shared via a trunk port, the presence of a native VLAN must be specified.
- If the following supplicant VLAN is changed by a dynamic VLAN, then the authentication function may not work properly.
- DHCP server
- L2MS compatible device
3.1 IEEE 802.1X authentication
IEEE 802.1X authentication uses EAP to authenticate in units of devices or users.
The supplicant receiving authentication must support IEEE 802.1X authentication.
This product operates as an authenticator that communicates with the supplicant using EAP over LAN, and with the RADIUS server using EAP over RADIUS.
The authentication process itself occurs directly between the supplicant and the RADIUS server.
As authentication methods, this product supports EAP-MD5, EAP-TLS, EAP-TTLS, and EAP-PEAP.
The features of each authentication method are shown in the following table.
Features of each authentication method
| Client authentication method | Server authentication method | Ease of implementation | Degree of safety | |
|---|---|---|---|---|
| EAP-MD5 | User name and password entry | No authentication | Easy | Low |
| EAP-TLS | Client certificate | Server certificate | Complex | High |
| EAP-TTLS | User name and password entry | Server certificate | Medium | Medium |
| EAP-PEAP | User name and password entry | Server certificate | Medium | Medium |
Make settings for the supplicant and the RADIUS server as appropriate for the authentication method you use.
The basic procedure for IEEE 802.1X authentication is shown in the following diagram.
Basic procedure for IEEE 802.1X authentication
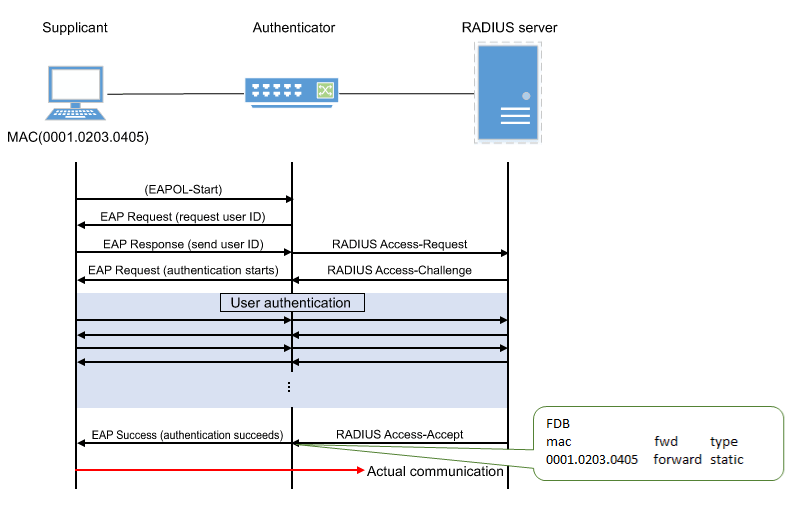
The supplicant is connected to the LAN, and transmits a communication start message (EAPOL-Start) message to start authentication.
When authentication succeeds, authentication success (Success) notification is sent to the supplicant, and the supplicant’s MAC address is registered in the FDB, allowing the supplicant to access the network.
If authentication fails, an authentication failure (Failure) notification is sent to the supplicant, and network access is denied for the supplicant.
(Even without authentication, it is possible to allow access to a specific VLAN if a guest VLAN has been specified.)
3.2 MAC authentication
MAC authentication uses the MAC address of a device to authenticate an individual device.
Since the supplicant does not need special functionality to be authenticated, authentication is possible even for devices that do not support IEEE 802.1X.
The basic procedure for MAC authentication is shown in the following diagram.
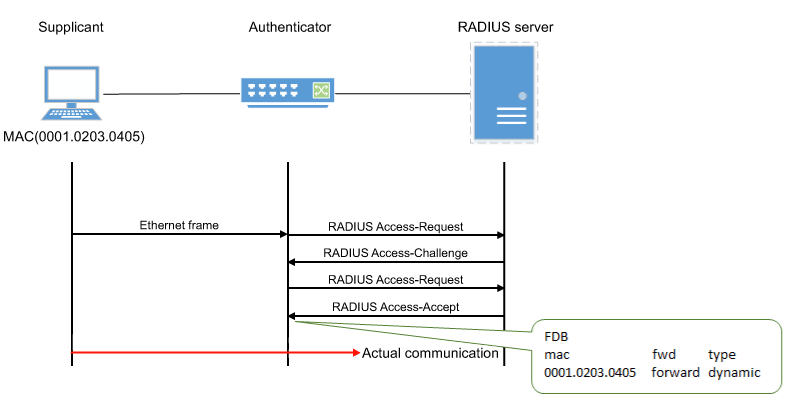
When this product receives any Ethernet frame from the supplicant, it queries the RADIUS server with the supplicant’s MAC address as the user name and password.
EAP-MD5 is used as the authentication mode between this product and the RADIUS server.
When authentication succeeds, the supplicant’s MAC address is registered in the FDB, allowing the supplicant to access the network.
However, it can be registered as a static entry by specifying MAC authenticated static registration (using the auth-mac static command).
If authentication fails, the supplicant is denied network access.
(Even without authentication, it is possible to allow access to a specific VLAN if a guest VLAN has been specified.)
The supplicant’s MAC address must be registered as the user name and password in the RADIUS server, in one of the following formats.
- XX-XX-XX-XX-XX-XX (hyphen delimited)
- XX:XX:XX:XX:XX:XX (colon delimited)
- XXXXXXXXXXXX (not delimited)
This product lets you use the auth-mac auth-user command to change the format of the MAC address query that is made to the RADIUS server.
Specify the appropriate command according to the format of the MAC addresses that are registered in the RADIUS server.
3.3 Web authentication
Web authentication is a function that authenticates a user when a user name and password are entered from the supplicant’s web browser.
HTTP is supported as the communication method between the web browser and the switch.
Because web authentication performs authentication by communicating via HTTP, it is necessary for IP communication between this product and the supplicant to be possible even before authentication.
Either the DHCP server must assign an IP address to the supplicant, or the supplicant must specify an IP address statically.
Web authentication operates only in multi-supplicant mode.
Also, this cannot be used together with a guest VLAN.
The basic procedure for web authentication is shown in the following diagram.
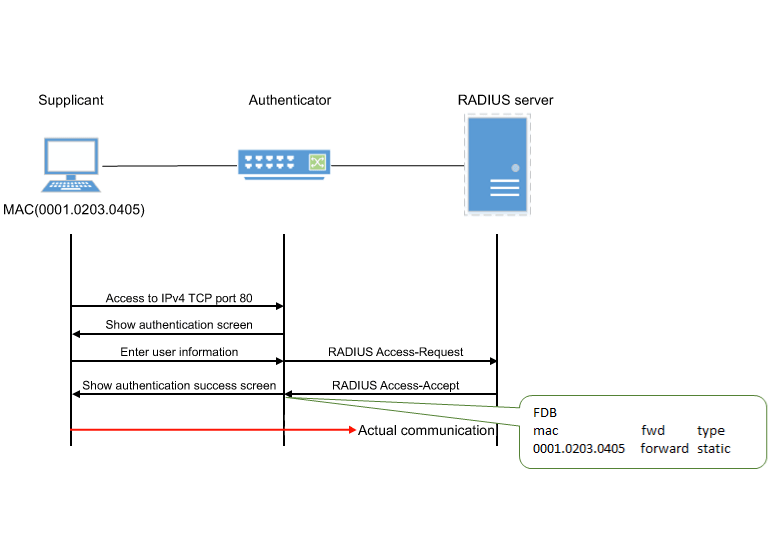
This product queries the RADIUS server using the user name and password that were entered in the supplicant’s web browser.
EAP-MD5 is used as the authentication mode between this product and the RADIUS server.
When authentication succeeds, the supplicant’s MAC address is registered in the FDB, allowing the supplicant to access the network.
If authentication fails, the supplicant is denied network access.
3.3.1 Operations on the supplicant
When the supplicant’s web browser accesses IPv4 TCP port 80, the following authentication screen appears.
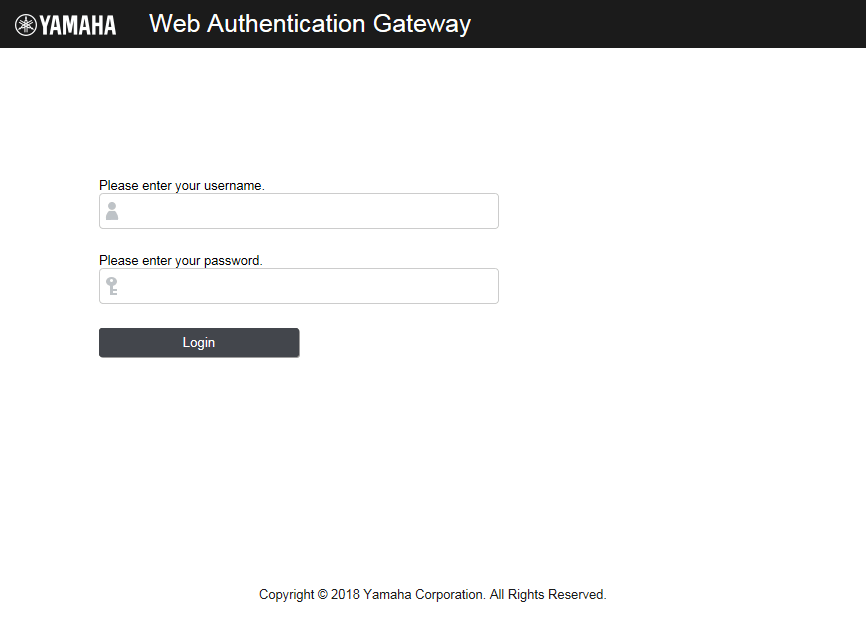
To be authenticated, enter a user name and password, and click the “log in” button.
The supplicant’s MAC address is registered in the FDB, allowing the supplicant to access the network.
If authentication fails three times in succession, authentication is temporarily restricted.
3.4 Using multiple authentication functions
This product lets you use IEEE 802.1X authentication, MAC authentication, and web authentication together on the same port.
When switches are used in combination, each switch is successively authenticated in the authentication order specified using the auth order command. With default settings, IEEE 802.1X authentication is prioritized.
For web authentication, switches are authenticated by entering an ID and password in the Web Authentication screen, where the authentication method is changed to web authentication.
If multiple authentication methods are being used simultaneously, operation is as follows.
If both IEEE 802.1X authentication and MAC authentication are used, with IEEE 802.1X authentication prioritized
If both IEEE 802.1X authentication and MAC authentication are used, with MAC authentication prioritized
If both web authentication and IEEE 802.1X/MAC authentication are used
- If authentication succeeds with any one of the methods, authentication has succeeded.
- If the reauthentication setting is enabled, then reauthentication is performed using the method with which authentication succeeded.
- If multiple authentication methods are used, forwarding control settings received via an unauthenticated port will be discarded.
- If both IEEE 802.1X authentication and MAC authentication are being used and an EAPOL start signal is received from an unauthenticated supplicant, authentication will switch to IEEE 802.1X authentication even if MAC authentication is already in progress.
- If both IEEE 802.1X authentication and MAC authentication are being used, even if the first authentication method fails, authentication will switch to the next authentication method without entering the restriction period.
- If both IEEE 802.1X authentication and MAC authentication are being used and any Ethernet frame is received from a supplicant, the product transmits an EAP request.
- If web authentication is also being used, unauthenticated supplicants are registered in FDB as static/discard.
3.5 Host mode
This product lets you select the host mode for the port authentication function.
Host mode indicates how an applicable supplicant’s communication will be permitted on the authentication port.
This product lets you choose from the following host modes.
- Single host mode
This mode permits communication for only one supplicant for each LAN/SFP port.
Communication is permitted only for the first supplicant that successfully authenticates.
- Multi-host mode
This mode permits communication for multiple supplicants for each LAN/SFP port.
When a supplicant has successfully authenticated and is permitted to communicate, other supplicants connected to the same LAN/SFP port are likewise permitted to communicate on the same VLAN as the successfully authenticated supplicant.
- Multi-supplicant
This mode permits communication for multiple supplicants for each LAN/SFP port.
Each supplicant is distinguished by its MAC address, permitting communication in units of supplicants.
When using dynamic VLAN functions, you can specify the VLAN for each supplicant.
3.6 Dynamic VLANs
This product supports dynamic VLANs with IEEE 802.1X, MAC, or Web authentication.
Dynamic VLAN is a function that changes the authentication port’s associated VLAN according to the VLAN attribute values in authentication information in notifications received from the RADIUS server.
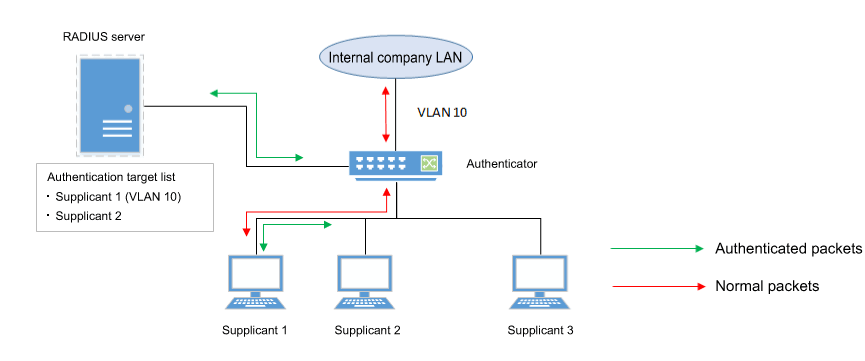
As shown in the illustration above, if a port’s associated VLAN is 1, and the received authentication data has a VLAN attribute of 10, then following successful authentication, the authentication port’s associated VLAN is 10, and communication on VLAN 10 is permitted.
For the RADIUS server, make settings so that the authentication information sent from the server includes the following attribute values.
- Tunnel-Type = VLAN (13)
- Tunnel-Medium-Type = IEEE-802 (6)
- Tunnel-Private-Group-ID = VLAN ID
If a dynamic VLAN is used, the following actions will occur in respective host modes.
- Single host mode
The authentication port’s associated VLAN is changed according to the VLAN attribute value of the supplicant that successfully authenticates.
- Multi-host mode
The authentication port’s associated VLAN is changed according to the VLAN attribute value of the supplicant that successfully authenticates.
Other supplicants that are connected to the same port are also permitted to communicate on the same VLAN.
- Multi-supplicant mode
The authentication port’s associated VLAN is changed according to the VLAN attribute value of the supplicant that successfully authenticates.
You can specify the VLAN for each supplicant.
3.7 VLAN for unauthenticated or failed-authentication ports
This product’s IEEE 802.1X authentication and MAC authentication allows you to specify a guest VLAN so that unauthenticated ports or ports that failed authentication will be assigned to a specific VLAN.
In multi-supplicant mode, you can specify this for each supplicant.
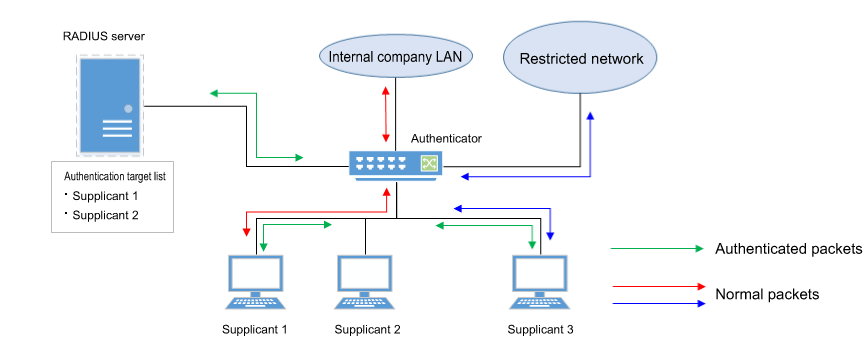
This is useful when you want to provide partial functionality on a limited network even to a supplicant that has not succeeded in authenticating, as shown in the illustration above.
3.8 EAP pass-through function
You can switch between enable and disable for EAP pass-through and configure whether EAPOL frames are to be forwarded.
The authentication function will be prioritized for interfaces on which the 802.1X authentication function is enabled, and EAP pass-through will not be applied.
3.9 Attribute values notified to RADIUS server
The RADIUS server can be notified of the NAS-Identifier attribute value.
Notifies the RADIUS server of the character string set by the auth radius attribute nas-identifier command as a NAS-Identifier attribute value.
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Set IEEE 802.1X authentication function for the entire system | aaa authentication dot1x |
| Set MAC authentication function for the entire system | aaa authentication auth-mac |
| Set web authentication function for the entire system | aaa authentication auth-web |
| Set IEEE 802.1X authentication function operating mode | dot1x port-control |
| Set unauthenticated port forwarding control for IEEE 802.1X authentication | dot1x control-direction |
| Set number of retransmitted EAPOL packets | dot1x max-auth-req |
| Set MAC authentication function | auth-mac enable |
| Set MAC address format setting for MAC authentication | auth-mac auth-user |
| MAC authenticated stack registration setting | auth-mac static |
| Set web authentication function | auth-web enable |
| Set redirect-destination URL following successful web authentication | auth-web redirect-url |
| Copy web authentication screen customization files | copy auth-web custom-file |
| Delete web authentication screen customization files | erase auth-web custom-file |
| Set host mode | auth host-mode |
| Authentication order setting | auth order |
| Set reauthentication | auth reauthentication |
| Set dynamic VLAN | auth dynamic-vlan-creation |
| Set guest VLAN | auth guest-vlan |
| Set restriction period following failed authentication | auth timeout quiet-period |
| Set reauthentication interval | auth timeout reauth-period |
| Set response wait time for the entire RADIUS server | auth timeout server-timeout |
| Set response wait time for the supplicant | auth timeout supp-timeout |
| Set RADIUS server host | radius-server host |
| Set response wait time for a single RADIUS server | radius-server timeout |
| Set number of times to retransmit request to RADIUS server | radius-server retransmit |
| Set shared password for RADIUS server | radius-server key |
| Set availability time restriction for RADIUS server | radius-server deadtime |
| Setting of NAS-Identifier attribute to be notified to RADIUS server | auth radius attribute nas-identifier |
| Show port authentication status | show auth status |
| Show RADIUS server setting status | show radius-server |
| Show supplicant status | show auth supplicant |
| Show statistical information | show auth statistics |
| Clear statistical information | clear auth statistics |
| Clear authentication state | clear auth state |
| Set time at which authentication state is cleared (system) | auth clear-state time |
| Set time at which authentication state is cleared (interface) | auth clear-state time |
| EAP pass-through settings | pass-through eap |
5 Examples of Command Execution
5.1 Set IEEE 802.1X authentication
Make settings so that IEEE 802.1X authentication can be used.
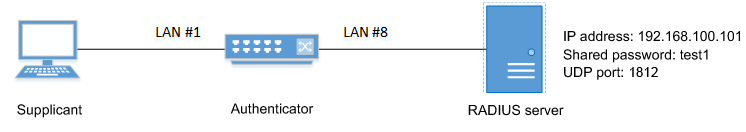
- We will use LAN port #1 as the authentication port to which the supplicant is connected.
- We will set the host mode to multi-supplicant mode.
- We will use VLAN #10 as the guest LAN.
- We will use 192.168.100.101 as the IP address of the RADIUS server that is connected.
- Define VLAN #10 as the guest VLAN.
Yamaha(config)#vlan database Yamaha(config-vlan)#vlan 10 ... (Define VLAN #10) Yamaha(config-vlan)#exit
- Enable the IEEE 802.1X authentication function for the entire system.
Yamaha(config)#aaa authentication dot1x
- Set IEEE 802.1X authentication for LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#dot1x port-control auto ... (Set IEEE 802.1X authentication operating mode to auto) Yamaha(config-if)#auth host-mode multi-supplicant ... (Set host mode to multi-supplicant mode) Yamaha(config-if)#auth guest-vlan 10 ... (Set VLAN as VLAN #10) Yamaha(config-if)#exit
- Set RADIUS server settings.
Yamaha(config)#radius-server host 192.168.100.101 key test1 (Set host as 192.168.100.101, and shared password “test1”) - Check RADIUS server settings.
Yamaha#show radius-server Server Host : 192.168.100.101 Authentication Port : 1812 Secret Key : test1 Timeout : 5 sec Retransmit Count : 3 Deadtime : 0 min
- Check port authentication settings.
Yamaha#show auth status [System information] 802.1X Port-Based Authentication : Enabled MAC-Based Authentication : Disabled WEB-Based Authentication : Disabled Clear-state time : Not configured Redirect URL : Not configured RADIUS server address : 192.168.100.101 (port:1812) [Interface information] Interface port1.1 (up) 802.1X Authentication : Force Authorized (configured:auto) MAC Authentication : Disabled (configured:disable) WEB Authentication : Enabled (configured:disable) Host mode : Multi-supplicant Dynamic VLAN creation : Disabled Guest VLAN : Enabled (VLAN ID:10) Reauthentication : Disabled Reauthentication period : 3600 sec MAX request : 2 times Supplicant timeout : 30 sec Server timeout : 30 sec Quiet period : 60 sec Controlled directions : In (configured:both) Protocol version : 2 Clear-state time : Not configured
5.2 Set MAC authentication
Make settings so that MAC authentication can be used.
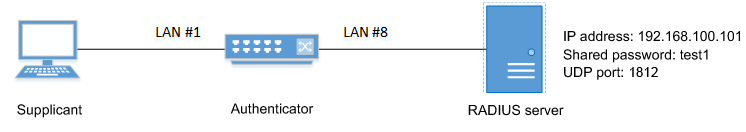
- We will use LAN port #1 as the authentication port to which the supplicant is connected.
- We will set the host mode to multi-supplicant mode.
- We will use 192.168.100.101 as the IP address of the RADIUS server that is connected.
- Enable the MAC authentication function for the entire system.
Yamaha(config)#aaa authentication auth-mac
- Set MAC authentication for LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#auth-mac enable ... (Enable MAC authentication) Yamaha(config-if)#auth host-mode multi-supplicant ... (Set host mode to multi-supplicant mode) Yamaha(config-if)#exit
- Set RADIUS server settings.
Yamaha(config)#radius-server host 192.168.100.101 key test1 (Set host as 192.168.100.101, and shared password “test1”) - Check RADIUS server settings.
Yamaha#show radius-server Server Host : 192.168.100.101 Authentication Port : 1812 Secret Key : test1 Timeout : 5 sec Retransmit Count : 3 Deadtime : 0 min
- Check port authentication settings.
Yamaha#show auth status [System information] 802.1X Port-Based Authentication : Disabled MAC-Based Authentication : Enabled WEB-Based Authentication : Disabled Clear-state time : Not configured Redirect URL : Not configured RADIUS server address : 192.168.100.101 (port:1812) [Interface information] Interface port1.1 (up) 802.1X Authentication : Force Authorized (configured:-) MAC Authentication : Enabled (configured:enable) WEB Authentication : Disabled (configured:disable) Host mode : Multi-supplicant Dynamic VLAN creation : Disabled Guest VLAN : Disabled Reauthentication : Disabled Reauthentication period : 3600 sec MAX request : 2 times Supplicant timeout : 30 sec Server timeout : 30 sec Quiet period : 60 sec Controlled directions : In (configured:both) Protocol version : 2 Clear-state time : Not configured Authentication status : Unauthorized
5.3 Set web authentication
Make settings so that web authentication can be used.
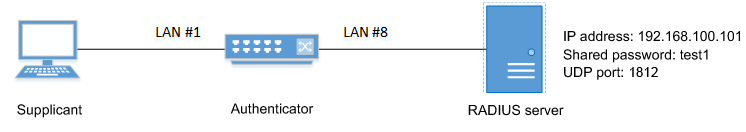
- We will use LAN port #1 as the authentication port to which the supplicant is connected.
- We will assume that 192.168.100.10 the IP address of the supplicant.
- We will use 192.168.100.101 as the IP address of the RADIUS server that is connected.
- Assign an IP address to the authenticator for IP communication.
Yamaha(config)#interface valn1 Yamaha(config-if)#ip address 192.168.100.240/24 Yamaha(config-if)#exit
- Enable the web authentication function for the entire system.
Yamaha(config)#aaa authentication auth-web
- Set web authentication for LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#auth host-mode multi-supplicant ... (Set host mode to multi-supplicant mode) Yamaha(config-if)#auth-web enable ... (Enable web authentication) Yamaha(config-if)#exit
- Set RADIUS server settings.
Yamaha(config)#radius-server host 192.168.100.101 key test1 (Set host as 192.168.100.101, and shared password “test1”) - Check RADIUS server settings.
Yamaha#show radius-server Server Host : 192.168.100.101 Authentication Port : 1812 Secret Key : test1 Timeout : 5 sec Retransmit Count : 3 Deadtime : 0 min
- Check port authentication settings.
Yamaha#show auth status [System information] 802.1X Port-Based Authentication : Disabled MAC-Based Authentication : Disabled WEB-Based Authentication : Enabled Clear-state time : Not configured Redirect URL : Not configured RADIUS server address : 192.168.100.101 (port:1812) [Interface information] Interface port1.1 (up) 802.1X Authentication : Force Authorized (configured:-) MAC Authentication : Disabled (configured:disable) WEB Authentication : Enabled (configured:enable) Host mode : Multi-supplicant Dynamic VLAN creation : Disabled Guest VLAN : Disabled Reauthentication : Disabled Reauthentication period : 3600 sec MAX request : 2 times Supplicant timeout : 30 sec Server timeout : 30 sec Quiet period : 60 sec Controlled directions : In (configured:both) Protocol version : 2 Clear-state time : Not configured
6 Points of Caution
Using dynamic VLAN in multi-supplicant mode will consume internal resources.
These resources are also used by the ACL and QoS functions. There may not be enough resources according to the settings.
Use caution, since communications may not be possible if there are not enough resources, even though authentication might succeed.
7 Related Documentation
None
- SWP2 Series Technical Data (Basic Functions)
- Interface control functions
- Port security functions
Port security functions
1 Function Overview
Port security is a function that limits communication to only permitted terminals, preventing access from illegal terminals.
2 Definition of Terms Used
None
3 Function Details
For ports for which the port security function is enabled, you can in advance register the MAC address of terminals that you want to allow to communicate, thereby allowing only the permitted terminals to communicate.
Conversely, if there is access from a terminal that is not registered (an illegal terminal), this is considered illegal access, and the packets are discarded.
Depending on the settings, the corresponding port can also be shut down.
The port security function cannot be used simultaneously with the port authentication function.
3.1 Limiting the terminals that can access
To limit the terminals that can access the port, simply enable the port security function and use the port-security mac-address command to register the MAC address of a terminal for which you want to allow communication.
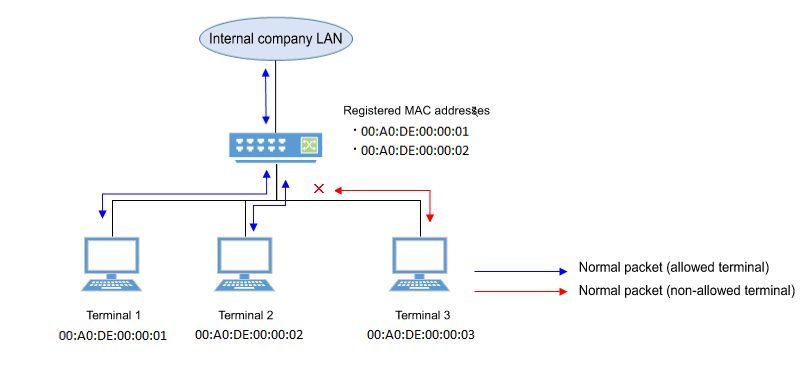
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Set port security function | port-security enable |
| Register allowed MAC addresses | port-security mac-address |
| Set operation for when security violation occurs | port-security violation |
| Show port security status | show port-security status |
5 Examples of Command Execution
5.1 Limiting the terminals that can access
Manually specify the MAC address so that only the permitted terminal can communicate.
- Enable port security on LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#port-security enable
- Register the MAC address that you want to permit.
Yamaha(config)#port-security mac-address 00A0.DE00.0001 forward port1.1 vlan 1 Yamaha(config)#port-security mac-address 00A0.DE00.0002 forward port1.1 vlan 1
- Check the port security status.
Yamaha#show port-security status Port Security Action Status Last violation --------- --------- ---------- --------- --------------------- port1.1 Enabled Discard Normal 00A0.DE00.0003 port1.2 Disabled Discard Normal port1.3 Disabled Discard Normal port1.4 Disabled Discard Normal port1.5 Disabled Discard Normal port1.6 Disabled Discard Normal port1.7 Disabled Discard Normal port1.8 Disabled Discard Normal port1.9 Disabled Discard Normal port1.10 Disabled Discard Normal
6 Points of Caution
- Use the no shutdown command to restore a port that has been shut down due to detection of unauthorized access.
The status of the show port-security status command does not return to the Normal state until the port links up (it remains in the Shutdown state). - If an incorrect port is specified with the port-security mac-address command, communication and violation frame detection will not be performed correctly.
7 Related Documentation
None
- SWP2 Series Technical Data (Basic Functions)
- Layer 2 functions
- SWP2 Series Technical Data (Basic Functions)
- Layer 2 functions
- Forwarding database (FDB)
Forwarding database (FDB)
1 Function Overview
The Forwarding Database (subsequently referred to as the FDB) manages the combination of destination MAC addresses, transmission ports, and VLANs.
This product uses the FDB to determine the forwarding destination port for the received frames.
- Enable/disable acquisition function
- Timeout adjustment for FDB entries acquired
- Timeout clear for FDB entries acquired
- Manual registration of FDB entries (static entries)
2 Definition of Terms Used
- FDB
Abbreviation of “Forwarding Database.”
This database manages the combination of destination MAC address, transmission port, and VLAN.
- FDB entry
- This is data registered in the FDB, and consists of multiple elements.
3 Function Details
3.1 FDB entry
On this product, the contents listed in the table below are registered as a single entry in the FDB.
Up to 16,384 addresses can be registered, including addresses registered via automatic acquisition and manual registration.
| Element managed | Description | |
|---|---|---|
| MAC address | Device MAC addresses can be either unicast or multicast. | |
| VLAN-ID (FID) | The VLAN ID to which a device is associated. This is a value from 1–4094. | |
| Forwarding destination interface ID | The interface on which the device exists. LAN/SFP ports are static/LACP logical interfaces. | |
| Action | The method of processing the frame addressed to the device. There are two processing methods, “discard” and “forward”. | |
| Entry registration type | dynamic | Entries registered through automatic acquisition |
| static | Entries registered manually via commands | |
| multicast | Entries acquired by IGMP/MLD Snooping | |
3.1.1 MAC address
This is one of the FDB key items; the VLAN-ID and MAC address are combined to become the record key.
Operation differs depending on whether the MAC address is unicast or multicast.
- Unicast
Since the forwarding destination interface ID must be uniquely determined for a given record key, duplication is not allowed.
(Multiple combinations of the same VLAN-ID and MAC address do not exist.)
- Multicast
Multiple forwarding destination interface IDs may exist for a given key record.
In this case, frames are sent to multiple forwarding destination interface IDs.
The MAC addresses of all received frames can be acquired, and the source MAC address is acquired and registered in the FDB.
However, if the transmission source MAC address is multicast, this is considered an invalid frame and is discarded without being registered.
Each VLAN interface created internally consumes one FDB entry.
Automatically acquired MAC address information is maintained until the ageing timeout.
If multiple multicast MAC addresses are specified, all are considered as one in this case.
VLAN port mac fwd type timeout 1 port1.1 0100.0000.1000 forward static 0 1 port1.2 0100.0000.1000 forward static 0 1 port1.3 0100.0000.1000 forward static 0 1 port1.4 0100.0000.1000 forward static 0 1 port1.5 0100.0000.1000 forward static 0 1 port1.6 0100.0000.1000 forward static 0
3.1.2 VLAN-ID
MAC address acquisition is done per VLAN, and the MAC address and VLAN are managed in the FBD as a pair.
For different VLANs, identical MAC addresses are also acquired.
3.1.3 Forwarding destination interface ID
The following IDs are registered.
- LAN/SFP port (port)
- Static/LACP logical interface (sa,po)
3.1.4 Action
This defines the action for a received frame that matches a key record.
If the MAC address is unicast, the actions are as follows.
- forward ... Forward to the forwarding destination interface ID.
- discard ... Discard without forwarding.
If the MAC address is multicast, the actions are as follows.
- forward ... Forward to the forwarding destination interface ID.
- discard ... Cannot be specified.
(The discard setting cannot be made if the MAC address is multicast.)
3.1.5 Registration types
- dynamic ... Registered and deleted automatically. The registration result does not remain in the config settings file.
- static ... Registered and deleted manually, and therefore remains in the config settings file.
- multicast ... Automatically registered and deleted by the IGMP/MLD snooping function. The registration result does not remain in the config settings file.
3.2 Automatic MAC address acquisition
Automatic MAC address acquisition refers to the active creation of FBD entries based on the information for the source MAC address of the received frame, and the reception port.
Entries registered through automatic acquisition are called “dynamic entries”.
A timer (ageing time) is used to monitor individual entries.
Entries for MAC addresses that have not received frames within a certain amount of time will be automatically deleted from FDB entries by an aging timer.
This prevents invalid device entries from being left over in the FDB due to power shutoff, being moved and so on.
If a frame is received within the specified amount of time, the monitoring timer will be reset.
The control specifications for automatic acquisition are shown below.
- Automatic MAC address acquisition can be enabled or disabled using the mac-address-table learning command. The setting is enabled by default.
- If automatic acquisition is changed from enabled to disabled, all dynamic entries that have been learned will be deleted. The acquisition function “disable” setting is useful when you want to flood all ports with all received frames.
- Aging timer settings for dynamic entries are specified using mac-address-table ageing-time command.
This value is set to 300 seconds by default.
- The actual time when entries are deleted by the aging time occurs within double the seconds specified as the timer setting value.
- Clear the dynamic entries that have been acquired by using the clear mac-address-table dynamic command. The entire contents of the FDB can be cleared at once; or a VLAN number can be specified and all MAC addresses acquired by that VLAN can be cleared from the FDB. Specifying the port number will clear all MAC addresses from the FDB that were acquired from that port.
- Use the show mac-address-table command to check the automatic acquisition status.
3.3 Setting MAC addresses manually
In addition to automatic acquisition using received frames, MAC addresses can be set on this product by using user commands.
Entries that have been registered by using commands are called “static entries”.
The specifications for manual settings are shown below.
- Use the mac-address-table static command to register static entries.
- When registering static entries, dynamic acquisition will not be performed on the corresponding MAC addresses.
Entries that have already been acquired will be deleted from the FDB, and will be registered as static entries.
- Use the no mac-address-table static command to delete static entries.
- Either “forward” or “discard” can be specified for the destination MAC address of a received frame.
- When forwarding is specified, either the LAN/SFP port forwarding destination or the static/LACP logical interface can be specified.
- When discarding is specified, frames received by the MAC address will not be forwarded to any port, and will be discarded.
- If registering a multicast MAC address, you cannot specify “discard.”
Also, the following MAC addresses cannot be registered.
- 0000.0000.0000
- 0100.5e00.0000–0100.5eff.ffff
- 0180.c200.0000–0180.c200.000f
- 0180.c200.0020–0180.c200.002f
- 3333.0000.0000–3333.ffff.ffff
- ffff.ffff.ffff
4 Related Commands
4.1 List of related commands
| Operations | Operating Commands |
|---|---|
| Enable/disable MAC address acquisition function | mac-address-table learning |
| Set dynamic entry ageing time | mac-address-table ageing-time |
| Clear dynamic entry | clear mac-address-table dynamic |
| Register static entry | mac-address-table static |
| Delete static entry | no mac-address-table static |
| Refer to MAC address table | show mac-address-table |
5 Examples of Command Execution
5.1 Referring to the FDB
Yamaha#show mac-address-table VLAN port mac fwd type timeout 1 port1.2 00a0.de11.2233 forward static 0 1 port1.1 1803.731e.8c2b forward dynamic 300 1 port1.1 782b.cbcb.218d forward dynamic 300
5.2 Deleting a dynamic entry
Deleting an FDB entry registered in the FBD (MAC address 00:a0:de:11:22:33)
Yamaha#clear mac-address-table dynamic address 00a0.de11.2233
5.3 Changing the dynamic entry ageing time
This example shows how to change the dynamic entry ageing time to 400 seconds.
Yamaha(config)#mac-address-table ageing-time 400
5.4 Registering a static entry
This example shows how frames addressed to a device associated with VLAN #10 (MAC address 00:a0:de:11:22:33) can be forwarded to LAN port 2 (port1.2).
Yamaha(config)#mac-address-table static 00a0.de11.2233 forward port1.2 vlan 10
This example shows how to discard the frames sent to a device associated with VLAN #10 (MAC address 00:a0:de:11:22:33).
Specifying the interface name (“port1.2” in the example) will have no effect on operations. Since this cannot be omitted, specify the LAN/SFP port.
Yamaha(config)#mac-address-table static 00a0.de11.2233 discard port1.2 vlan 10
5.5 Deleting a static entry
This example shows how to delete the forwarding settings sent to a device associated with VLAN #10 (MAC address 00:a0:de:11:22:33).
Yamaha(config)#no mac-address-table static 00a0.de11.2233 forward port1.2 vlan 10
6 Points of Caution
If the l2-unknown-mcast command is configured to discard unknown multicast frames, using the mac-address-table static command to passively forward a multicast MAC address will have no effect when registered.
7 Related Documentation
None
VLAN
1 Function Overview
VLAN (Virtual LAN) is technology that allows a LAN to be constructed virtually, without regard to the physical structure of connections.
This product lets you use VLANs to divide the LAN into multiple broadcast domains.
The VLANs that are supported by this product are shown below.
Supported VLAN types
| VLAN types | Summary |
|---|---|
| Port-based VLAN | Groups that can communicate are configured for each LAN/SFP+ port. |
| Tagged VLAN | Groups that can communicate are identified, based on the fixed-length tag information appended to the Ethernet frame. Multiple and different VLANs can be made to communicate by means of one LAN/SFP+ port. |
| Private VLAN | Groups that can communicate within the same VLAN can be divided up. This includes the following three VLAN types. - Primary VLAN - Isolated VLAN - Community VLAN |
| Multiple VLAN | LAN/SFP ports can be divided into multiple groups that can communicate. See here for multiple VLANs. |
| Voice VLAN | This allows audio and data to be handled separately on an access port. |
2 Definition of Terms Used
- Broadcast domain
This is a range in which broadcast frames can be delivered in a network, such as an Ethernet.
Devices that are connected by relaying a data link layer (MAC layer), such as switches, can belong to the same broadcast domain.
A broadcast domain generally refers to the network in an Ethernet.
3 Function Details
3.1 Defining a VLAN ID
On product, a maximum of 255 VLANs can be defined, with VLAN IDs ranging from 2–4094. (ID #1 is used as the default VLAN ID.)
VLAN IDs are defined using the vlancommand, after the vlan database command is used to enter VLAN mode.
For details, refer to the Command Reference.
3.2 VLAN settings for the LAN/SFP+ ports
The following settings must be configured after defining the VLANs to use, in order to make use of VLAN on this product.
- LAN/SFP+ port mode settings
- VLAN associations for LAN/SFP+ ports
- The LAN/SFP+ ports on this product are set to one of the following modes.
- Access port
This is a port that handles untagged frames. It can be associated with one VLAN.
- Trunk port
This is a port that handles both tagged and untagged frames.
It can be associated with multiple VLANs, and is mainly used to connect switches to one another.
This product only supports IEEE 802.1Q. (Cisco ISL is not supported.)
- Access port
- Use the switchport mode command to set the LAN/SFP+ port mode.
When setting the trunk port, use the input filter (“ingress-filter”) to control whether frames not belonging to the specified VLAN ID will be handled.
- Input filter enabled: only frames set to the specified VLAN ID will be handled.
- Input filter disabled: all VLAN IDs will be handled.
- Use the show interface switchport command to check the LAN/SFP+ port setting mode.
- Use the switchport access vlan command to set which VLANs belong to the access port.
- Use the switchport trunk allowed vlan command to set which VLANs belong to the trunk port.
As the trunk port can be associated with multiple VLANs, use the “all”, “none”, “except”, “add” and “remove” settings as shown below.
- add
Adds the specified VLAN ID.
VLAN IDs that can be added are limited by the IDs that are defined by the VLAN mode.
- remove
Deletes the specified VLAN ID.
- all
Adds all VLAN IDs specified by the VLAN mode.
The VLAN IDs added by the VLAN mode can also be added after this command is executed.
- none
The trunk port will not be associated with any VLAN.
- except
Adds all other VLAN IDs except for the ones specified.
The VLAN IDs added by the VLAN mode can also be added after this command is executed.
- add
- A VLAN that uses untagged frames (native VLAN) can be specified for the trunk port.
- Tagged audio frames can be transferred by specifying a voice VLAN for an access port.
- Use the show vlan command to check which VLANs belong to a LAN/SFP+ port.
3.3 VLAN access control
This product provides an VLAN access map function, to control access to the VLAN.
The VLAN access map can be associated with a standard/extended IP access control list and a MAC address control list as VLAN ID filtering parameters.
The VLAN access map is operated using the commands shown below.
- Create VLAN access map: vlan access-map command
- Set VLAN access map parameters: match access-list command
- Assign VLAN access map: vlan filter command
- Show VLAN access map: show vlan access-map command
3.4 Default VLAN
The default VLAN is VLAN #1 (vlan1), which exists in this switch by default.
As the default VLAN is a special VLAN, it always exists and cannot be deleted.
The following operations can be used to automatically delete the relevant port from the default VLAN.
- Setting the VLAN for an access port
- Setting any VLAN other than the default as the native VLAN for the trunk port
- Setting the native VLAN for the trunk port to “none”
3.5 Native VLAN
A native VLAN is a VLAN that associates untagged frames received by the LAN/SFP+ port that was set as a trunk port.
Defining a LAN/SFP+ port as a trunk port will set the default VLAN (VLAN #1) as the native VLAN.
Use the switchport trunk native vlan command when specifying a certain VLAN as the native VLAN.
The native LAN can be set to none, when setting the relevant LAN/SFP+ port to not handle untagged frames. (Specify “none” in the switchport trunk native vlan command.)
3.6 Private VLAN
This product can configure a private VLAN for further dividing up groups that can communicate within the same subnet.
The operating specifications are shown below.
- A private VLAN contains the following three VLAN types.
- Primary VLAN
This is the parent VLAN of the secondary VLAN.
Only one primary VLAN can be set per private VLAN.
- Isolated VLAN
This is a kind of secondary VLAN, which only sends traffic to a primary VLAN.
Only one primary VLAN can be set per private VLAN.
- Community VLAN
This is a kind of secondary VLAN, which only sends traffic to VLANs in the same community and to a primary VLAN.
Multiple community VLANs can be set for each private VLAN.
- Primary VLAN
- A primary VLAN may contain multiple promiscuous ports.
Access ports, trunk ports, or static/LACP logical interfaces are the ports that can be used as promiscuous ports.
- Only access ports can be used as host ports for a secondary VLAN (isolated VLAN, community VLAN).
- A secondary VLAN (isolated VLAN, community VLAN) can be associated with one primary VLAN.
Use the switchport private-vlan mapping command to create the association.
- An isolated VLAN can be associated with multiple promiscuous ports contained within a private VLAN.
- A community VLAN can be associated with multiple promiscuous ports contained within a private VLAN.
3.7 Voice VLAN
Voice VLAN is a function that can prevent audio from being adversely affected even when IP phone voice traffic is mixed with PC data traffic.

Some IP phones have two ports: a port for connection to the switch and a port for connection to the PC.
By connecting the switch to the IP phone, and the IP phone to the PC, it is possible to use one port of the switch to handle the IP phone audio traffic and the PC’s data traffic.
Using the voice VLAN function in this type of configuration allows the audio data and the PC data to be separated so that noise is less likely to occur on the IP phone, or to handle the audio data with a higher priority.
Use the switchport voice vlan command to make voice LAN settings.
Make settings so that one of the following is handled as voice traffic.
- Frames with the 802.1p tag
- Priority tagged frames (VLAN ID of 0, and a 802.1p tag that specifies only the CoS value)
- Untagged frames
When handling tagged frames as voice traffic, untagged frames are handled as data traffic.
By using LLDP, this product can automatically apply settings to a connected IP phone.
Conditions for automatic settings are as follows.
- LLDP-MED TLV transmission is enabled on the port for which voice VLAN is enabled.
- The IP phone to be connected supports settings via LLDP-MED.
If the above conditions are satisfied, voice VLAN information (tagged/untagged, VLAN ID, CoS value to be used, DSCP value) is notified via the LLDP-MED Network Policy TLV when an IP phone is connected to the corresponding port.
The IP phone will be able to transmit voice data in accordance with the information that was provided to it by this product.
The CoS value to be specified for the IP phone is set by the switchport voice cos command, and the DSCP value is set by the switchport voice dscp command.
In order to prioritize audio traffic handling, you must make QoS settings (enable QoS and set the trust mode) as appropriate for the settings of the IP phone.
Limitations for a voice VLAN are as follows.
- It can be used only for a physical interface that is specified as an access port.
It cannot be used with a link aggregated logical interface or a VLAN logical interface.
- The voice VLAN function cannot be used together with the port authentication function.
4 Related Commands
4.1 List of related commands
- The related commands are shown below.
Operations Operating commands Enter VLAN mode vlan database Define VLAN interface, or change a predefined VLAN vlan Define a private VLAN private-vlan Set the secondary VLAN for a private VLAN private-vlan association Create VLAN access map vlan access-map Set VLAN access map parameters match Assign VLAN access map to VLAN vlan filter Set access port (untagged port) switchport mode access Set associated VLAN of an access port (untagged port) switchport access vlan Set trunk port (tagged port) switchport mode trunk Set associated VLAN for trunk port (tagged port) switchport trunk allowed vlan Set native VLAN for trunk port (tagged port) switchport trunk native vlan Set ports for private VLAN (promiscuous port, host port) switchport mode private-vlan Configure VLAN for private VLAN port and host port switchport private-vlan host-association Configure VLAN for private VLAN port and promiscuous port switchport private-vlan mapping Configure voice VLAN switchport voice vlan Set CoS value for voice VLAN switchport voice cos Set DSCP value for voice VLAN switchport voice dscp Show VLAN information show vlan Show private VLAN information show vlan private-vlan Show VLAN access map show vlan access-map Show VLAN access map filter show vlan filter
5 Examples of Command Execution
5.1 Port-based VLAN settings
In this example, a port-based VLAN is configured for this product in order to allow communication between hosts A–B and hosts C–D.
Port VLAN setting example
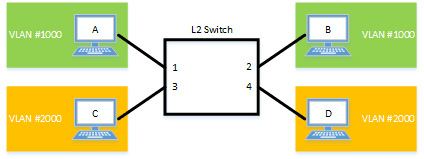
The LAN port settings for this product are as follows.
- Set LAN ports #1/#2 as access ports, and associate them with VLAN #1000.
- Set LAN ports #3/#4 as access ports, and associate them with VLAN #2000.
- Move to VLAN mode using the vlan database command, and define two VLANs using the vlan command.
Yamaha(config)# vlan database … (Move to VLAN mode) Yamaha(config-vlan)# vlan 1000 … (Create VLAN #1000) Yamaha(config-vlan)# vlan 2000 … (Create VLAN #2000) Yamaha(config-if)# exit
- Set LAN ports #1–2 as access ports, and associate them with VLAN #1000.
Yamaha(config)# interface port1.1-2 … (Move to interface mode) Yamaha(config-if)# switchport mode access … (Set as an access port) Yamaha(config-if)# switchport access vlan 1000 … (Set VLAN ID) Yamaha(config-if)# exit
- Set LAN ports #3–4 as access ports, and associate them with VLAN #2000.
Yamaha(config)# interface port1.3-4 Yamaha(config-if)# switchport mode access Yamaha(config-if)# switchport access vlan 2000 Yamaha(config-if)# exit
- Confirm the VLAN settings.
Yamaha#show vlan brief (u)-Untagged, (t)-Tagged VLAN ID Name State Member ports ======= ================ ======= =============================== 1 default ACTIVE port1.5(u) port1.6(u) port1.7(u) port1.8(u) 1000 VLAN1000 ACTIVE port1.1(u) port1.2(u) 2000 VLAN2000 ACTIVE port1.3(u) port1.4(u)
5.2 Tagged VLAN settings
In this example, a tagged VLAN is configured between #A and #B of this product, in order to communicate between hosts A–B and hosts C–D.
Tagged VLAN setting example

The LAN port settings for #A and #B of this product are as follows.
- Set LAN port #1 as an access port, and associate it with VLAN #1000
- Set LAN port #2 as an access port, and associate it with VLAN #2000
- Set LAN port #3 as a trunk port, and associate it with LAN #1000 and VLAN #2000
- [Switch #A/#B] Define VLAN.
Yamaha(config)#vlan database … (Move to vlan mode) Yamaha(config-vlan)#vlan 1000 … (Define vlan1000) Yamaha(config-vlan)#vlan 2000 … (Define vlan2000)
- [Switch #A/#B] Set LAN port #1 as the access port, and associate it with VLAN #1000.
Yamaha(config)#interface port1.1 … (Move to interface mode) Yamaha(config-if)#switchport mode access … (Set as an access port) Yamaha(config-if)#switchport access vlan 1000 … (Associate to vlan1000) Yamaha(config-if)#exit
- [Switch #A/#B] Set LAN port #2 as the access port, and associate it with VLAN #2000.
Yamaha(config)#interface port1.2 … (Move to interface mode) Yamaha(config-if)#switchport mode access … (Set as an access port) Yamaha(config-if)#switchport access vlan 2000 … (Associate to vlan2000) Yamaha(config-if)#exit
- [Switch #B] Set LAN port #3 as a trunk port, and associate it with VLAN #1000/#2000.
Yamaha(config)#interface port1.3 … (Move to interface mode) Yamaha(config-if)#switchport mode trunk … (Set as a trunk port) Yamaha(config-if)#switchport trunk allowed vlan add 1000 … (Add vlan1000) Yamaha(config-if)#switchport trunk allowed vlan add 2000 … (Add vlan2000) Yamaha(config-if)#exit
- Confirm the VLAN settings.
Yamaha#show vlan brief (u)-Untagged, (t)-Tagged VLAN ID Name State Member ports ======= ================================ ======= ====================== 1 default ACTIVE port1.3(u) 1000 VLAN1000 ACTIVE port1.1(u) port1.3(t) 2000 VLAN2000 ACTIVE port1.2(u) port1.3(t)
5.3 Private VLAN settings
This example makes private VLAN settings for this product, to achieve the following.
Hosts connected to ports 1–7 will connect to the Internet and other external lines, through the line to which port 8 is connected
Communications between hosts connected to ports 1–4 are blocked (isolated VLAN: VLAN #21)
Communications between hosts connected to ports 5–7 are permitted (community VLAN: VLAN #22)
Communications between hosts connected to ports 1–4 and ports 5–7 are blocked
Private VLAN setting example
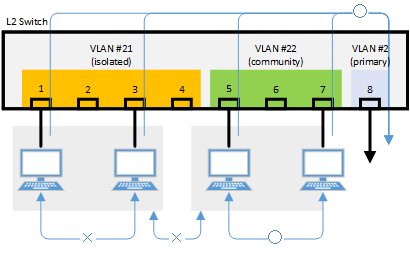
- Define the VLAN ID to be used for the private VLAN.
Yamaha(config)# vlan database … (Move to vlan) Yamaha(config-vlan)# vlan 2 … (Create VLAN) Yamaha(config-vlan)# vlan 21 Yamaha(config-vlan)# vlan 22 Yamaha(config-vlan)# private-vlan 2 primary … (Primary VLAN setting) Yamaha(config-vlan)# private-vlan 21 isolated … (Isolated VLAN setting) Yamaha(config-vlan)# private-vlan 22 community … (Community VLAN setting) Yamaha(config-vlan)# private-vlan 2 association add 21 … (Associate with Primary VLAN) Yamaha(config-vlan)# private-vlan 2 association add 22 Yamaha(config-vlan)# exit
- Configure the isolated VLAN (VLAN #21) for LAN ports 1–4.
Yamaha(config)#interface port1.1-4 … (Move to interface mode) Yamaha(config-if)#switchport mode access … (Set as an access port) Yamaha(config-if)#switchport access vlan 21 .. (Associate to VLAN #21) Yamaha(config-if)#switchport mode private-vlan host … (Set as host port of private VLAN) Yamaha(config-if)#switchport private-vlan host-association 2 add 21 Yamaha(config-if)#exit
- Configure the community VLAN (VLAN #22) for LAN ports 5–7.
Yamaha(config)#interface port1.5-7 … (Move to interface mode) Yamaha(config-if)#switchport mode access … (Set as an access port) Yamaha(config-if)#switchport access vlan 22 … (Associate to VLAN #22) Yamaha(config-if)#switchport mode private-vlan host … (Set as host port of private VLAN) Yamaha(config-if)#switchport private-vlan host-association 2 add 22 Yamaha(config-if)#exit
- Configure the primary VLAN (VLAN #2) for LAN port 8. (Promiscuous port)
Yamaha(config)#interface port1.8 … (Move to interface mode) Yamaha(config-if)#switchport mode access … (Set as an access port) Yamaha(config-if)#switchport access vlan 2 … (Associate to VLAN #2) Yamaha(config-if)#switchport mode private-vlan promiscuous … (Set as promiscuous port of private VLAN) Yamaha(config-if)#switchport private-vlan mapping 2 add 21 Yamaha(config-if)#switchport private-vlan mapping 2 add 22 Yamaha(config-if)#exit
- Confirm the VLAN settings.
Yamaha#show vlan brief (u)-Untagged, (t)-Tagged VLAN ID Name State Member ports ======= ================================ ======= ====================== 1 default ACTIVE 2 VLAN0002 ACTIVE port1.8(u) 21 VLAN0021 ACTIVE port1.1(u) port1.2(u) port1.3(u) port1.4(u) 22 VLAN0022 ACTIVE port1.5(u) port1.6(u) port1.7(u) Yamaha#show vlan private-vlan PRIMARY SECONDARY TYPE INTERFACES ------- --------- ---------- ---------- 2 21 isolated port1.1 port1.2 port1.3 port1.4 2 22 community port1.5 port1.6 port1.7
5.4 Voice VLAN settings
This example makes voice VLAN settings for this product, to achieve the following.
Connect an IP phone to port 1. Connect a PC to the other LAN port of the IP phone.
Using LLDP-MED, make the following settings from this product for the IP phone.
- As the voice traffic of the IP phone, transmit and receive 802.1q tagged frames of VLAN #2.
- Data communication of the PC transmits and receives untagged frames.
- When transmitting voice traffic, use a CoS value of 6.
- Define the VLAN ID to be used for the voice VLAN.
Yamaha(config)# vlan database … (Move to vlan mode) Yamaha(config-vlan)# vlan 2 … (Create VLAN) Yamaha(config-vlan)# exit
- Configure the voice VLAN for LAN port #1.
Yamaha(config)#interface port1.1 … (Move to interface mode) Yamaha(config-if)#switchport mode access … (Set as access port) Yamaha(config-if)#switchport voice vlan 2 … (Set voice traffic as tagged frames of VLAN #2) Yamaha(config-if)#switchport voice cos 6 … (Set voice traffic to a CoS value of 6) Yamaha(config-if)#exit
- Set the QoS for LAN port #1.
Yamaha(config)#qos enable … (Enable QoS) Yamaha(config)#interface port1.1 … (Move to interface mode) Yamaha(config-if)#qos trust cos ... (Set trust mode to CoS) Yamaha(config-if)#exit
- Set LLDP-MED transmission and reception for LAN port #1.
Yamaha(config)#interface port1.1 … (Move to interface mode) Yamaha(config-if)#lldp-agent ... (Create LLDP agent, transition modes) Yamaha(lldp-agent)#tlv-select med ... (Set LLDP-MED TLV) Yamaha(lldp-agent)#set lldp enable txrx ... (Set LLDP transmission/reception mode) Yamaha(lldp-agent)#exit Yamaha(config-if)#exit Yamaha(config)#lldp run … (Enable LLDP function) Yamaha(config)#exit
6 Points of Caution
A host port that is associated with a private VLAN cannot be aggregated as a link aggregation logical interface; this limitation is specific to host ports.
7 Related Documentation
Multiple VLAN
1 Function Overview
On a multiple VLAN, by associating a port with a multiple VLAN group, you can block traffic from ports that do not belong to the same multiple VLAN group.
You can also join a single port to multiple VLAN groups.
By using this function, it is easy to handle requests to block only traffic between terminals, such as the example below.
Example of using multiple VLANs
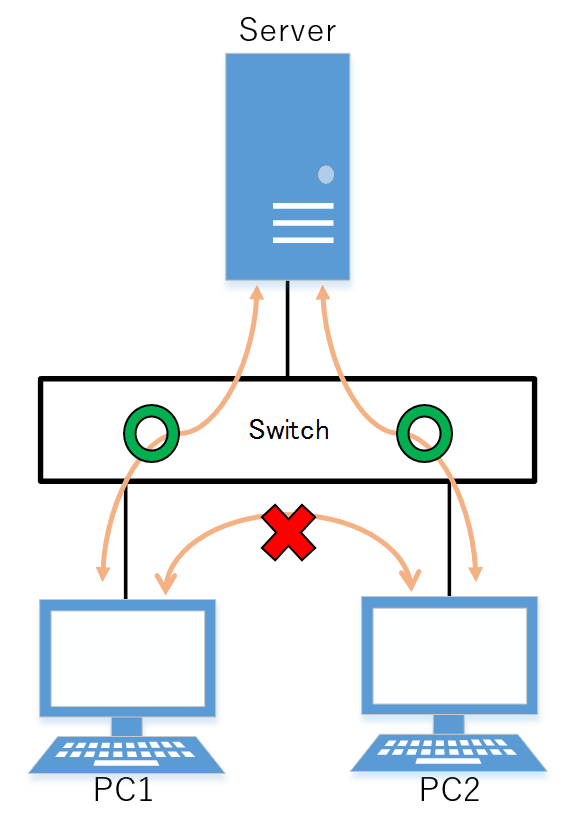
2 Definition of Terms Used
None
3 Function Details
3.1 Operating Specifications
Use the switchport multiple-vlan group command to configure a multiple VLAN group.
Multiple VLANs can be configured as LAN/SFP ports and link aggregation logical interfaces.
If you wish to configure a multiple VLAN group for a trunk port, this will be applied to all relevant VLANs that belong to the port in question.
The VLAN group settings will also be applied to a multicast frame.
This can be used together with the following functions. Control of traffic enable/disable for these functions is set according to the multiple VLAN settings.
- Port-based VLAN/tagged VLAN/voice VLAN
- Port authentication
A multiple VLAN can contain up to 256 groups.
Use the show vlan multiple-vlan group command to confirm the setting status for the interface of each multiple VLAN group.
3.2 Examples of traffic between multiple VLAN groups
Example of traffic for a multiple VLAN group
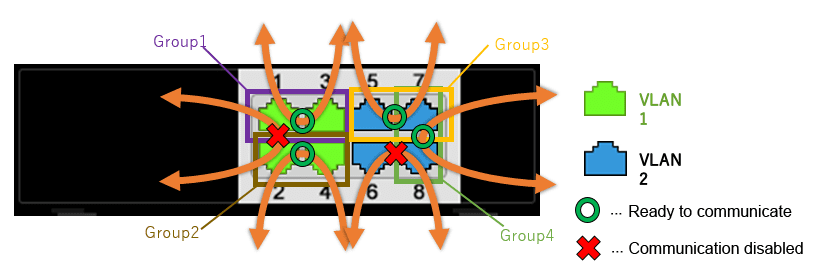
When using multiple VLAN group settings (Group #1 through #4) as shown in the diagram above, enabling/disabling traffic between specific ports A/B and the reasons for such as shown in the table below.
Traffic enabled/disabled between specific ports A/B
| Port number A (group) | Port number B (group) | Traffic enable/disable | Reason |
|---|---|---|---|
| port1.1 (Group 1) | port1.2 (Group 2) | Disabled | The multiple VLAN group is different |
| port1.1 (Group 1) | port1.3 (Group 1) | Enabled | Associated with multiple VLAN group #1 |
| port1.2 (Group 2) | port1.4 (Group 2) | Enabled | Associated with multiple VLAN group #2 |
| port1.5 (Group 3) | port1.7 (Group 3,4) | Enabled | Associated with multiple VLAN group #3 |
| port1.6 (no group) | port1.8 (Group 4) | Disabled | The multiple VLAN group is different |
| port1.7 (Group 3,4) | port1.8 (Group 4) | Enabled | Associated with multiple VLAN group #4 |
Also, traffic can be established between ports that are not associated with a multiple VLAN group, so long as it is within the same VLAN.
4 Related Commands
Related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Multiple VLAN group settings | switchport multiple-vlan group |
| Settings for the name of multiple VLAN group | multiple-vlan group name |
| Set YMPI frame transmission function when multiple VLANs are specified | multiple-vlan transfer ympi |
| Show multiple VLANs | show vlan multiple-vlan group |
5 Examples of Command Execution
5.1 Multiple VLAN settings
This configures multiple VLAN settings to achieve the following.
Hosts connected to ports 1–7 will connect to the Internet and other external lines, through the line to which port 8 is connected
Communications between hosts connected to ports 1–4 are blocked
Communications between hosts connected to ports 5–7 are permitted
Communications between hosts connected to ports 1–4 and ports 5–7 are blocked
Examples of multiple VLAN settings
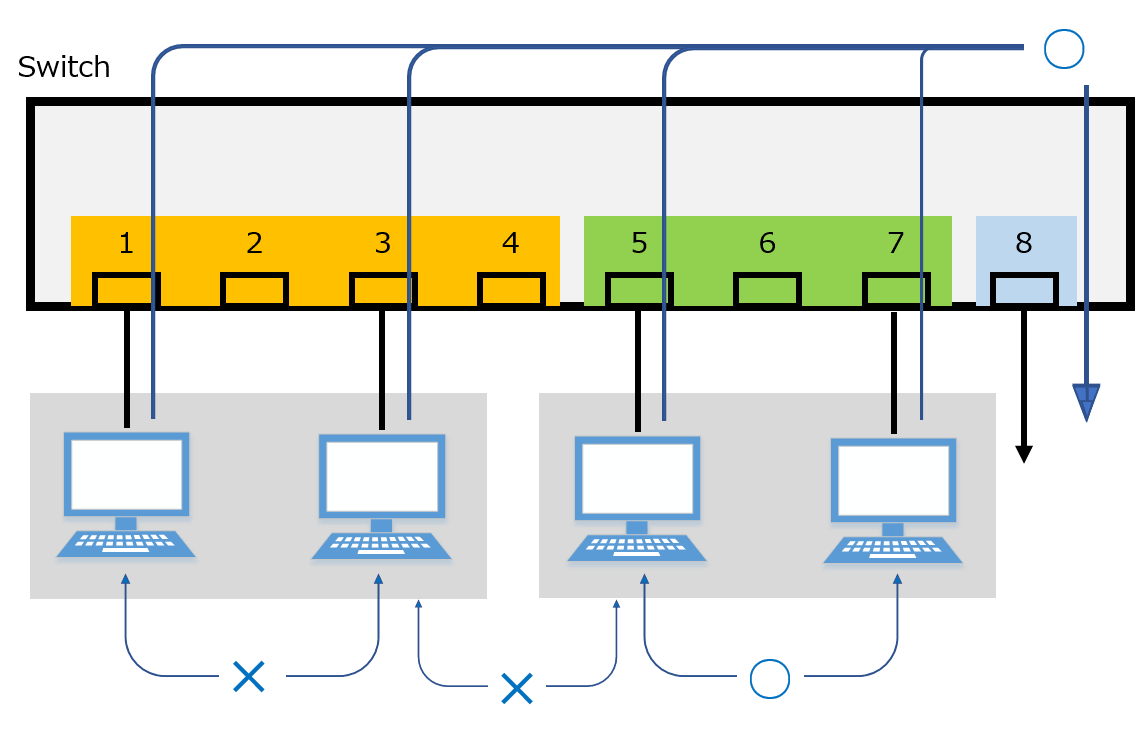
The multiple VLAN group settings are as follows.
- port1.1: Associated with multiple VLAN group #1
- port1.2: Associated with multiple VLAN group #2
- port1.3: Associated with multiple VLAN group #3
- port1.4: Associated with multiple VLAN group #4
- port1.5: Associated with multiple VLAN group #5
- port1.6: Associated with multiple VLAN group #5
- port1.7: Associated with multiple VLAN group #5
- port1.8: Associated with multiple VLAN groups #1, #2, #3, #4, #5
- This sets the name of multiple VLAN group #1 to “Network1”.
Yamaha(config)# multiple-vlan group 1 name Network1 …(settings for the name of multiple VLAN group #1)
- This sets the name of multiple VLAN group #5 to “Network5”.
Yamaha(config)# multiple-vlan group 1 name Network5 …(settings for the name of multiple VLAN group #5)
- Associates port1.1 through port1.4 with multiple VLAN groups #1 through #4 respectively.
Yamaha(config)# interface port1.1 … (transition to interface mode) Yamaha(config-if)# switchport multiple-vlan group 1 … (multiple VLAN group settings) Yamaha(config-if)# exit Yamaha(config)# interface port1.2 … (transition to interface mode) Yamaha(config-if)# switchport multiple-vlan group 2 … (multiple VLAN group settings) Yamaha(config-if)# exit Yamaha(config)# interface port1.3 … (transition to interface mode) Yamaha(config-if)# switchport multiple-vlan group 3 … (multiple VLAN group settings) Yamaha(config-if)# exit Yamaha(config)# interface port1.4 … (transition to interface mode) Yamaha(config-if)# switchport multiple-vlan group 4 … (multiple VLAN group settings) Yamaha(config-if)# exit
- This associates port1.5 through port1.7 with multiple VLAN group #5.
Yamaha(config)# interface port1.5–7 … (transition to interface mode) Yamaha(config-if)# switchport multiple-vlan group 5 … (specify multiple VLAN group) Yamaha(config-if)# exit
- This associates port1.8 with multiple VLAN groups #1, #2, #3, #4, #5.
Yamaha(config)# interface port1.8 … (transition to interface mode) Yamaha(config-if)# switchport multiple-vlan group 1–5 … (specify multiple VLAN group) Yamaha(config-if)# exit
- This checks the multiple VLAN group settings.
Yamaha>show vlan multiple-vlan group GROUP ID Name Member ports ======== ================================ ====================== 1 Network1 port1.1 port1.8 2 GROUP002 port1.2 port1.8 3 GROUP003 port1.3 port1.8 4 GROUP004 port1.4 port1.8 5 Network5 port1.5 port1.6 port1.7 port1.8
6 Points of Caution
The points of caution regarding this function are as follows.
- The function cannot be used in conjunction with a private VLAN.
- The multiple VLAN group to associate with a link aggregation logical interface must be the same.
- A multiple VLAN group is only applicable to forwarding between ports. Voluntary packets will not be affected by the settings of a multiple VLAN group.
- Even if a multiple VLAN is configured, communication may not work correctly due to the following influences.
- Block status of spanning tree
- IGMP snooping/MLD snooping status
- Blocked status of loop detection
- YMPI frames are transmitted for managing Yamaha wireless access points if multiple VLANs are specified.
Therefore, even if there are multiple Yamaha wireless access points associated with different VLAN groups, cluster management functionality or wireless LAN controller functionality can be used.
7 Related Documentation
- Layer 2 functions: VLAN
Spanning tree
1 Function Overview
The spanning tree is a function that maintains redundancies in the network routes while preventing loops.
Normally, the L2 switch floods the adjacent switch with the broadcast packets.
If the network is constructed as a loop, the switches will flood each other, causing the loop to occur.
This results in a major degradation of bandwidth and CPU resources in the switches.
The spanning tree determines the roles of each port and establishes a network construction where the broadcast packets do not keep traveling around, for networks that contain physical loops as well.
When there are problems linking, the problem is detected and the tree is reconstructed in order to restore the system.
This product supports STP, RSTP, and MSTP.
Spanning tree function overview
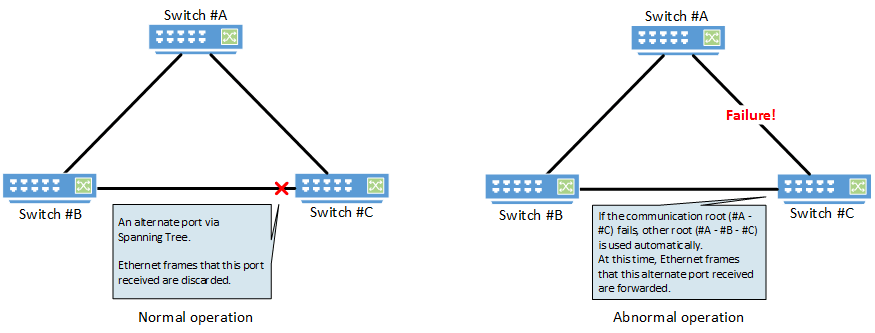
2 Definition of Terms Used
- RSTP:Rapid Spanning Tree Protocol (802.1w)
The spanning tree protocol (STP) exchanges BPDU (bridge protocol data unit) messages, in order to avoid loops.
This product supports IEEE802.1d and RFC4188.
- STP: Spanning Tree Protocol (802.1d)
The rapid spanning tree protocol (RSTP) is an extension of STP. It can recover the spanning tree more quickly than STP, when the network architecture has changed or when there is a problem linking.
This product supports IEEE802.1w and RFC4318.
- MSTP: Multiple Spanning Tree Protocol (802.1s)
Multiple spanning tree protocol (MSTP) is a further extension of STP and RSTP. It groups the VLAN into instances, and constructs a spanning tree for each group.
This can be used to distribute load within the network routes.
This product supports IEEE802.1s.
3 Function Details
This product supports the following functions in order to flexibly handle the construction of routes based on MSTP.
- Set priority
- Set bridge priority
- Set port priority
- Set path cost
- Set timeout
- Set forward delay time
- Set maximum aging time
- Specify edge port (Port Fast settings)
- BPDU guard
- BPDU filtering
- Route guard
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Set spanning tree for the system | spanning-tree shutdown |
| Set forward delay time | spanning-tree forward-time |
| Set maximum aging time | spanning-tree max-age |
| Set bridge priority | spanning-tree priority |
| Set spanning tree for an interface | spanning-tree |
| Set spanning tree link type | spanning-tree link-type |
| Set interface BPDU filtering | spanning-tree bpdu-filter |
| Set interface BPDU guard | spanning-tree bpdu-guard |
| Set interface path cost | spanning-tree path-cost |
| Set interface priority | spanning-tree priority |
| Set edge port for interface | spanning-tree edgeport |
| Show spanning tree status | show spanning-tree |
| Show spanning tree BPDU statistics | show spanning-tree statistics |
| Clear protocol compatibility mode | clear spanning-tree detected protocols |
| Move to MST mode | spanning-tree mst configuration |
| Generate MST instance | instance |
| Set VLAN for MST instance | instance vlan |
| Set priority of MST instance | instance priority |
| Set MST region name | region |
| Set revision number of MST region | revision |
| Set MST instance for interface | spanning-tree instance |
| Set interface priority for MST instance | spanning-tree instance priority |
| Set interface path cost for MST instance | spanning-tree instance path-cost |
| Show MST region information | show spanning-tree mst config |
| Show MSTP information | show spanning-tree mst |
| Show MST instance information | show spanning-tree mst instance |
5 Examples of Command Execution
5.1 MSTP setting example
Use this product to realize the architecture shown in the diagram below.
MSTP architecture diagram
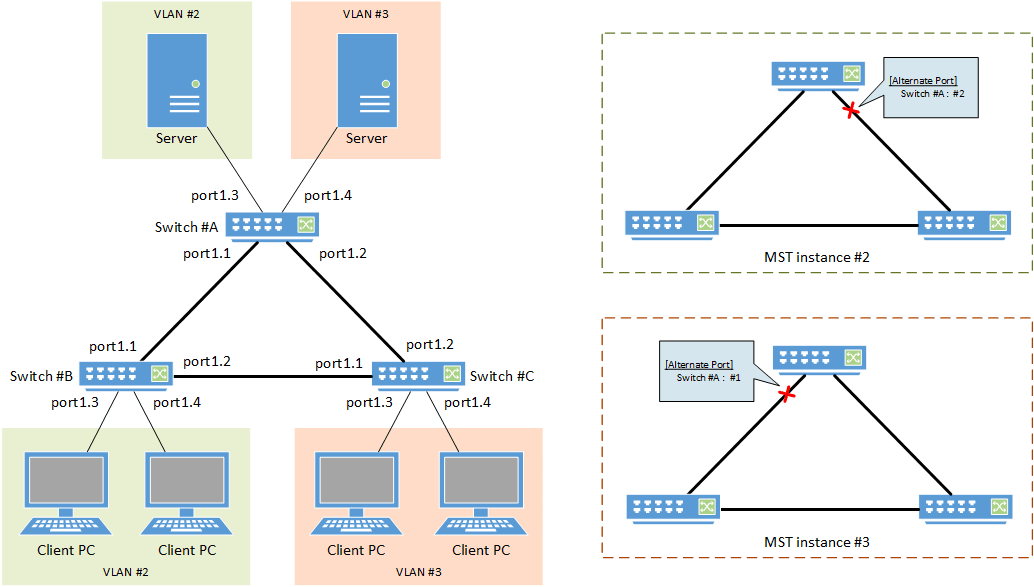
- In this example, MST instances are used to construct the spanning tree.
- A different route is set for each MST instance (VLAN), in order to distribute network load.
- The LAN port that is connected to the PC is set as the edge port.
- [Switch #A] Define VLAN #2 and VLAN #3.
Yamaha(config)#vlan database Yamaha(config-vlan)#vlan 2 ... (Define VLAN #2) Yamaha(config-vlan)#vlan 3 ... (Define VLAN #3) Yamaha(config-vlan)#exit
- [Switch #A] Set the CIST priority.
Yamaha(config)#spanning-tree priority 8192 ... (Set CIST priority to 8192)
- [Switch #A] Set the MST.
Yamaha(config)#spanning-tree mst configuration Yamaha(config-mst)#region Sample ... (Set MST region name to "Sample") Yamaha(config-mst)#revision 1 ... (Set MST revision number to 1) Yamaha(config-mst)#instance 2 vlan 2 ... (Define MST instance #2, and associate it with VLAN #2) Yamaha(config-mst)#instance 3 vlan 3 ... (Define MST instance #3, and associate it with VLAN #3) Yamaha(config-mst)#exit
- [Switch #A] Set LAN ports #1–#2 as trunk ports, and associate them with VLAN #2–#3.
Also, set the MST instances #2–#3.
Yamaha(config)#interface port1.1 Yamaha(config-if)#switchport mode trunk ... (Set as trunk port) Yamaha(config-if)#switchport trunk allowed vlan add 2,3 ... (Associate to VLAN #2–#3) Yamaha(config-if)#spanning-tree instance 2 ... (Set MST instance #2) Yamaha(config-if)#spanning-tree instance 3 ... (Set MST instance #3) Yamaha(config-if)#exit (Perform the above settings for LAN port #2 as well.)
- [Switch #A] Set LAN port #3 as the access port, and associate it with VLAN #2.
Also, set the MST instance #2, and make it an edge port.
Yamaha(config)#interface port1.3 Yamaha(config-if)#switchport mode access ... (Set as access port) Yamaha(config-if)#switchport access vlan 2 ... (Associate to VLAN #2) Yamaha(config-if)#spanning-tree instance 2 ... (Set MST instance #2) Yamaha(config-if)#spanning-tree edgeport ... (Set as edge port) Yamaha(config-if)#exit
- [Switch #A] Set LAN port #4 as the access port, and associate it with VLAN #3.
Also, set the MST instance #3, and make it an edge port.
Yamaha(config)#interface port1.4 Yamaha(config-if)#switchport mode access ... (Set as access port) Yamaha(config-if)#switchport access vlan 3 ... (Associate to VLAN #3) Yamaha(config-if)#spanning-tree instance 3 ... (Set MST instance #3) Yamaha(config-if)#spanning-tree edgeport ... (Set as edge port) Yamaha(config-if)#exit
- [Switch #B] Define VLAN #2 and VLAN #3.
Yamaha(config)#vlan database Yamaha(config-vlan)#vlan 2 ... (Define VLAN #2) Yamaha(config-vlan)#vlan 3 ... (Define VLAN #3) Yamaha(config-vlan)#exit
- [Switch #B] Set the CIST priority.
Yamaha(config)#spanning-tree priority 16384 ... (Set CIST priority to 16384)
- [Switch #B] Set the MST.
Yamaha(config)#spanning-tree mst configuration Yamaha(config-mst)#region Sample ... (Set MST region name to “Sample”) Yamaha(config-mst)#revision 1 ... (Set MST revision number to 1) Yamaha(config-mst)#instance 2 vlan 2 ... (Define MST instance #2, and associate with VLAN #2) Yamaha(config-mst)#instance 2 priority 8192 ... (Set MST instance #2 priority to 8192) Yamaha(config-mst)#instance 3 vlan 3 ... (Define MST instance #3, and associate with VLAN #3) Yamaha(config-mst)#instance 3 priority 16384 ... (Set MST instance #3 priority to 16384) Yamaha(config-mst)#exit
- [Switch #B] Set LAN ports #1–#2 as trunk ports, and associate them with VLAN #2–#3.
Also, set the MST instances #2–#3.
Yamaha(config)#interface port1.1 Yamaha(config-if)#switchport mode trunk ... (Set as trunk port) Yamaha(config-if)#switchport trunk allowed vlan add 2,3 ... (Associate to VLAN #2–#3) Yamaha(config-if)#spanning-tree instance 2 ... (Set MST instance #2) Yamaha(config-if)#spanning-tree instance 3 ... (Set MST instance #3) Yamaha(config-if)#exit (Perform the above settings for LAN port #2 as well.)
- [Switch #B] Set LAN port #3 as the access port, and associate it with VLAN #2.
Also, set the MST instance #2, and make it an edge port.
Yamaha(config)#interface port1.3 Yamaha(config-if)#switchport mode access ... (Set as access port) Yamaha(config-if)#switchport access vlan 2 ... (Associate to VLAN #2) Yamaha(config-if)#spanning-tree instance 2 ... (Set MST instance #2) Yamaha(config-if)#spanning-tree edgeport ... (Set as edge port) Yamaha(config-if)#exit (Perform the above settings for LAN port #4 as well.)
- [Switch #C] Define VLAN #2 and VLAN #3.
Yamaha(config)#vlan database Yamaha(config-vlan)#vlan 2 ... (Define VLAN #2) Yamaha(config-vlan)#vlan 3 ... (Define VLAN #3) Yamaha(config-vlan)#exit
- [Switch #C] Set the MST.
Yamaha(config)#spanning-tree mst configuration Yamaha(config-mst)#region Sample ... (Set MST region name to “Sample”) Yamaha(config-mst)#revision 1 ... (Set MST revision number to 1) Yamaha(config-mst)#instance 2 vlan 2 ... (Define MST instance #2, and associate with VLAN #2) Yamaha(config-mst)#instance 2 priority 16384 ... (Set MST instance #2 priority to 16384) Yamaha(config-mst)#instance 3 vlan 3 ... (Define MST instance #3, and associate with VLAN #3) Yamaha(config-mst)#instance 3 priority 8192 ... (Set MST instance #3 priority to 8192) Yamaha(config-mst)#exit
- [Switch #C] Set LAN ports #1–#2 as trunk ports, and associate them with VLAN #2–#3.
Also, set the MST instances #2–#3.
Yamaha(config)#interface port1.1 Yamaha(config-if)#switchport mode trunk ... (Set as trunk port) Yamaha(config-if)#switchport trunk allowed vlan add 2,3 ... (Associate to VLAN #2–#3) Yamaha(config-if)#spanning-tree instance 2 ... (Set MST instance #2) Yamaha(config-if)#spanning-tree instance 3 ... (Set MST instance #3) Yamaha(config-if)#exit (Perform the above settings for LAN port #2 as well.)
- [Switch #C] Set LAN port #3 as the access port, and associate it with VLAN #3.
Also, set the MST instance #3, and make it an edge port.
Yamaha(config)#interface port1.3 Yamaha(config-if)#switchport mode access ... (Set as access port) Yamaha(config-if)#switchport access vlan 3 ... (Associate to VLAN #3) Yamaha(config-if)#spanning-tree instance 3 ... (Set MST instance #3) Yamaha(config-if)#spanning-tree edgeport ... (Set as edge port) Yamaha(config-if)#exit (Perform the above settings for LAN port #4 as well.)
- Connect the LAN cable.
- [Switch #A] Check the CIST architecture.
Yamaha>show spanning-tree | include Root Id % Default: CIST Root Id 200100a0deaeb920 ... (The higher-priority switch #A is the CIST root bridge) % Default: CIST Reg Root Id 200100a0deaeb920 Yamaha>show spanning-tree | include Role % port1.1: Port Number 905 - Ifindex 5001 - Port Id 0x8389 - Role Designated - State Forwarding % port1.2: Port Number 906 - Ifindex 5002 - Port Id 0x838a - Role Designated - State Forwarding % port1.3: Port Number 907 - Ifindex 5003 - Port Id 0x838b - Role Designated - State Forwarding % port1.4: Port Number 908 - Ifindex 5004 - Port Id 0x838c - Role Designated - State Forwarding % port1.5: Port Number 909 - Ifindex 5005 - Port Id 0x838d - Role Disabled - State Discarding % port1.6: Port Number 910 - Ifindex 5006 - Port Id 0x838e - Role Disabled - State Discarding % port1.7: Port Number 911 - Ifindex 5007 - Port Id 0x838f - Role Disabled - State Discarding % port1.8: Port Number 912 - Ifindex 5008 - Port Id 0x8390 - Role Disabled - State Discarding % port1.9: Port Number 913 - Ifindex 5009 - Port Id 0x8391 - Role Disabled - State Discarding % port1.10: Port Number 914 - Ifindex 5010 - Port Id 0x8392 - Role Disabled - State Discarding
- [Switch #B] Check the CIST architecture.
Yamaha>show spanning-tree | include Root Id % Default: CIST Root Id 200100a0deaeb920 ... (The higher-priority switch #A is the CIST root bridge) % Default: CIST Reg Root Id 200100a0deaeb920 Yamaha>show spanning-tree | include Role % port1.1: Port Number 905 - Ifindex 5001 - Port Id 0x8389 - Role Rootport - State Forwarding % port1.2: Port Number 906 - Ifindex 5002 - Port Id 0x838a - Role Designated - State Forwarding % port1.3: Port Number 907 - Ifindex 5003 - Port Id 0x838b - Role Designated - State Forwarding % port1.4: Port Number 908 - Ifindex 5004 - Port Id 0x838c - Role Designated - State Forwarding % port1.5: Port Number 909 - Ifindex 5005 - Port Id 0x838d - Role Disabled - State Discarding % port1.6: Port Number 910 - Ifindex 5006 - Port Id 0x838e - Role Disabled - State Discarding % port1.7: Port Number 911 - Ifindex 5007 - Port Id 0x838f - Role Disabled - State Discarding % port1.8: Port Number 912 - Ifindex 5008 - Port Id 0x8390 - Role Disabled - State Discarding % port1.9: Port Number 913 - Ifindex 5009 - Port Id 0x8391 - Role Disabled - State Discarding % port1.10: Port Number 914 - Ifindex 5010 - Port Id 0x8392 - Role Disabled - State Discarding
- [Switch #C] Check the CIST architecture.
Yamaha>show spanning-tree | include Root Id % Default: CIST Root Id 200100a0deaeb920 ... (The higher-priority switch #A is the CIST root bridge) % Default: CIST Reg Root Id 200100a0deaeb920 Yamaha>show spanning-tree | include Role % port1.1: Port Number 905 - Ifindex 5001 - Port Id 0x8389 - Role Alternate - State Discarding ... (LAN #1 port of the lower-priority switch #C is the alternate CIST port) % port1.2: Port Number 906 - Ifindex 5002 - Port Id 0x838a - Role Rootport - State Forwarding % port1.3: Port Number 907 - Ifindex 5003 - Port Id 0x838b - Role Designated - State Forwarding % port1.4: Port Number 908 - Ifindex 5004 - Port Id 0x838c - Role Designated - State Forwarding % port1.5: Port Number 909 - Ifindex 5005 - Port Id 0x838d - Role Disabled - State Discarding % port1.6: Port Number 910 - Ifindex 5006 - Port Id 0x838e - Role Disabled - State Discarding % port1.7: Port Number 911 - Ifindex 5007 - Port Id 0x838f - Role Disabled - State Discarding % port1.8: Port Number 912 - Ifindex 5008 - Port Id 0x8390 - Role Disabled - State Discarding % port1.9: Port Number 913 - Ifindex 5009 - Port Id 0x8391 - Role Disabled - State Discarding % port1.10: Port Number 914 - Ifindex 5010 - Port Id 0x8392 - Role Disabled - State Discarding
- [Switch #A] Check the architecture of MST instance #2.
Yamaha>show spanning-tree mst instance 2 | include Root Id % Default: MSTI Root Id 200200a0deaeb879 ... (The higher-priority switch #B is the root bridge for MST instance #2) Yamaha>show spanning-tree mst instance 2 | include Role % port1.1: Port Number 905 - Ifindex 5001 - Port Id 0x8389 - Role Rootport - State Forwarding % port1.2: Port Number 906 - Ifindex 5002 - Port Id 0x838a - Role Alternate - State Discarding ... (LAN #2 port of lower-priority switch #A is the alternate port for MST instance #2) % port1.3: Port Number 907 - Ifindex 5003 - Port Id 0x838b - Role Designated - State Forwarding
- [Switch #B] Check the architecture of MST instance #2.
Yamaha>show spanning-tree mst instance 2 | include Root Id % Default: MSTI Root Id 200200a0deaeb879 ... (The higher-priority switch #B is the root bridge for MST instance #2) Yamaha>show spanning-tree mst instance 2 | include Role % port1.1: Port Number 905 - Ifindex 5001 - Port Id 0x8389 - Role Designated - State Forwarding % port1.2: Port Number 906 - Ifindex 5002 - Port Id 0x838a - Role Designated - State Forwarding % port1.3: Port Number 907 - Ifindex 5003 - Port Id 0x838b - Role Designated - State Forwarding % port1.4: Port Number 908 - Ifindex 5004 - Port Id 0x838c - Role Designated - State Forwarding
- [Switch #C] Check the architecture of MST instance #2.
Yamaha>show spanning-tree mst instance 2 | include Root Id % Default: MSTI Root Id 200200a0deaeb879 ... (The higher-priority switch #B is the root bridge for MST instance #2) Yamaha>show spanning-tree mst instance 2 | include Role % port1.1: Port Number 905 - Ifindex 5001 - Port Id 0x8389 - Role Rootport - State Forwarding % port1.2: Port Number 906 - Ifindex 5002 - Port Id 0x838a - Role Designated - State Forwarding
- [Switch #A] Check the architecture of MST instance #3.
Yamaha>show spanning-tree mst instance 3 | include Root Id % Default: MSTI Root Id 200300a0deaeb83d ... (The higher-priority switch C# is the root bridge for MST instance #3) Yamaha>show spanning-tree mst instance 3 | include Role % port1.1: Port Number 905 - Ifindex 5001 - Port Id 0x8389 - Role Alternate - State Discarding ... (The higher-priority switch C# is the root bridge for MST instance #3) % port1.2: Port Number 906 - Ifindex 5002 - Port Id 0x838a - Role Rootport - State Forwarding % port1.4: Port Number 908 - Ifindex 5004 - Port Id 0x838c - Role Designated - State Forwarding
- [Switch #B] Check the architecture of MST instance #3.
Yamaha>show spanning-tree mst instance 3 | include Root Id % Default: MSTI Root Id 200300a0deaeb83d ... (The higher-priority switch C# is the root bridge for MST instance #3) Yamaha>show spanning-tree mst instance 3 | include Role % port1.1: Port Number 905 - Ifindex 5001 - Port Id 0x8389 - Role Designated - State Forwarding % port1.2: Port Number 906 - Ifindex 5002 - Port Id 0x838a - Role Rootport - State Forwarding
- [Switch #C] Check the architecture of MST instance #3.
Yamaha>show spanning-tree mst instance 3 | include Root Id % Default: MSTI Root Id 200300a0deaeb83d ... (The higher-priority switch C# is the root bridge for MST instance #3) Yamaha>show spanning-tree mst instance 3 | include Role % port1.1: Port Number 905 - Ifindex 5001 - Port Id 0x8389 - Role Designated - State Forwarding % port1.2: Port Number 906 - Ifindex 5002 - Port Id 0x838a - Role Designated - State Forwarding % port1.3: Port Number 907 - Ifindex 5003 - Port Id 0x838b - Role Designated - State Forwarding % port1.4: Port Number 908 - Ifindex 5004 - Port Id 0x838c - Role Designated - State Forwarding
6 Points of Caution
- STP and RSTP on this product are supported by backward-compatibility provided by MSTP.
7 Related Documentation
- VLAN
- STP
- IEEE802.1d
- RFC4188
- RSTP
- IEEE802.1w
- RFC4318
- MSTP
- IEEE802.1s
- SWP2 Series Technical Data (Basic Functions)
- Layer 2 functions
- Proprietary loop detection
Proprietary loop detection
1 Function Overview
This product offers a proprietary system to detect whether there is a loop in the network environment that was configured.
A proprietary loop detection frame is sent from the LAN/SFP+ port, and the unit monitors whether the frame returns or not.
If the transmitted frame returns, the system determines that there is a loop in the port in question.
2 Definition of Terms Used
- LDF (Loop Detection Frame)
This is a Yamaha proprietary Ethernet frame that is used to detect loops.
3 Function Details
3.1 Loop detection operating specifications
The loop detection specifications for this product are shown below.
- In addition to enabling/disabling the entire system, the loop detection on this product can enable/disable individual LAN/SFP+ ports.
When detecting loops in LAN/SFP+ ports, the system-wide setting must be set to enable.
- Use the loop-detectcommand in global configuration mode for system-wide settings.
- Use the loop-detect command in the interface mode of the relevant port for individual LAN/SFP+ port settings.
- The default settings for the loop detection function are as shown below. (In the initial state, this function is not operating.)
- System-wide settings: disabled
- LAN/SFP+ port settings: enabled
- If the system-wide settings for loop detection and spanning tree protocol are both enabled, the LAN/SFP+ port settings give priority to spanning tree protocol.
- If the loop detection function is enabled for this product, the following operations are performed.
- Loop detection frames (hereafter “LDF”) are sent every two seconds from the linked-up LAN/SFP+ port.
The loop detection function cannot be used on static/LACP logical interfaces, and ports on which mirror settings have been made (mirror ports).
- When the transmitted loop detection frame receives itself, it determines that a loop has occurred, and the following operations are performed.
- Port Shutdown
When both the transmitting and the receiving LAN/SFP+ port is the same, the relevant port is shut down.
The linkup will be made five minutes after shutdown, and LDF transmission will resume. (If a loop has occurred, this operation will repeat.)
When a linkup to the relevant port is desired within five minutes of monitored time, the no shutdown command is used.
- Port Blocking
When the port number of the transmitting LAN/SFP+ port is smaller than the receiving port number, all frames except for LDF are blocked.
The LDF will be transmitted periodically, but LDF will not be forwarded from other devices.
For the LAN/SFP+ ports that were blocked, if the LDF that was transmitted does not return within five seconds, it is determined that the loop has been resolved, and normal communications are resumed.
- Port Detected
When the port number of the LAN/SFP+ port that was transmitted is larger than the port number during reception, blocking is occurring on another port, so communication continues as normal.
- Port Shutdown
- When a loop is detected, the port lamp display on this product changes to a dedicated status, and the following SYSLOG message is output.
- [LOOP]: inf: Detected Loop!: port1.1, 1.3 … (displayed in a five-second cycle, starting from the detection of the loop)
- The port lamp display on this product is restored as communications are resumed after the loop is resolved, and the following SYSLOG message is output.
- [LOOP]: inf: Recovered Loop! : port1.1, 1.3
- Loop detection frames (hereafter “LDF”) are sent every two seconds from the linked-up LAN/SFP+ port.
- The “detected” operation can be forcibly performed without performing shutdown/blocking of the LAN/SFP+ port on which the loop was detected.
- Use the loop-detect blocking-disable command for this setting.
- If this setting is “enabled”, port blocking will be implemented on the next largest port number. (Shutdown operations will not occur.)
- A force-clear can be performed on the loop detection status (detected, blocking) by using the loop-detect reset command. (On models equipped with a MODE button, this can be also done by holding down the MODE button for three seconds.)
If a linkdown has occurred on the port where a loop has been detected, the detection status will be cleared. (The port lamp display is restored, and the following syslog message is outputted.)
- The status of the loop detection function can be checked using the show loop-detect command. The following is displayed.
- System Enable/disable status
- Loop detection status (status for each LAN/SFP+ port)
- When an LDF is received by a LAN/SFP+ port when the loop detection function is disabled, the received frames from all other ports will be forwarded as-is.
However, frames will not be forwarded for static/LACP logical interfaces and ports on which mirror settings have been made (mirror ports).
- In the following kinds of situations, loops in hubs that are connected to this product might not be detected.
- Loops are being detected in a currently connected hub
- Loop detection frames are not being forwarded by a currently connected hub
3.2 Loop detection example
The following shows examples of loop detection in this product.
Loop detection example
| Loop detection case | Configuration example | Loop detection status |
|---|---|---|
| 1 |  | A loop is detected when the device receives the LDF that it has transmitted. port1.1 : Shutdown |
| 2 |  | When loops are detected in multiple ports on the same terminal, the port with the largest number is blocked. port1.1 : Detected port1.3 : Blocking |
| 3 | 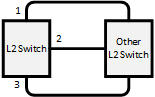 | The loop is avoided by blocking multiple ports. The blocking port is selected using the same rules as case 2. port1.1 : Detected port1.2 : Blocking port1.3 : Blocking |
| 4 | 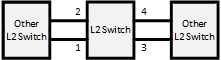 | When loops are detected in multiple groups, the port with the largest number in each group is blocked. port1.1 : Detected, port1.2 : Blocking port1.3 : Detected, port1.4 : Blocking |
| 5 | 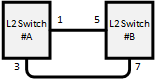 | When a loop occurs between two switches, one of the switches detects the loop. ○When detected in port1.3 of switch #A port1.1: Detected, port1.3: Blocking ○When detected in port1.7 of switch #B port1.5: Detected, port1.7: Blocking |
| 6 | 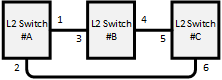 | Out of the six ports that are connected by cable, the port for which the loop is most quickly detected is the one that is blocked. ○When detected in port1.2 of switch #A port1.1: Detected, port1.2: Blocking ○When detected in port1.4 of switch #B port1.3: Detected, port1.4: Blocking ○When detected in port1.6 of switch #C port1.5: Detected, port1.6: Blocking |
| 7 | 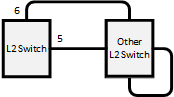 | Because the LDF transmitted from each port returns to these ports, port1.5 and port1.6 will both shut down. port1.5 : Shutdown port1.6 : Shutdown |
| 8 | 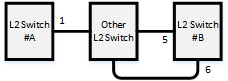 | Port1.6 of switch #B is blocked. Depending on the timing, port1.1 of switch #A will shut down, but the loop in port 1.1 of switch #A is resolved by blocking port1.6 of switch #B. xx xx Switch #A port1.1: Shutdown Switch #B port1.5: Detected Switch #B port1.6: Blocking |
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Enable/disable loop detection function (system) | loop-detect enable/disable |
| Enable/disable loop detection function (LAN/SFP+ port) | loop-detect enable/disable |
| Set port blocking for loop detection | loop-detect blocking enable/disable |
| Set port blocking connection time when a loop is detected | loop-detect blocking interval |
| Reset loop detection status | loop-detect reset |
| Refer to the setting status of loop detection | show loop-detect |
5 Examples of Command Execution
This example detects any loops occurring on this product using the following configuration, when the loop detection function is enabled.
[Example 1] Loop occurring within this product
[Example 2] Loop occurring in a third-party hub connected to this product
This sets LAN ports #1 and #3 to detect loops.
- Enable the loop detection function for the entire system.
Yamaha(config)#loop-detect enable ... (Enable the system-wide loop detection function)
- Enable the loop detection function for LAN ports #1 and #3.
Yamaha(config)#interface port1.1 Yamaha(config-if)#spanning-tree disable ... (Disable the spanning tree function for each LAN port) Yamaha(config-if)#loop-detect enable ... (Enable the loop detection function for each LAN port) Yamaha(config-if)#loop-detect blocking enable ... (Enable blocking) (Make the above settings for LAN port #3 as well.)
- The loop detection function for each LAN port and blocking are both enabled by default, so there is no need to set them.
- Confirm that the loop detection function has been set.
Confirm whether the loop detection function is enabled(*) for LAN ports #1 and #3.
Yamaha>show loop-detect loop-detect: Enable port loop-detect port-blocking status ------------------------------------------------------- port1.1 enable(*) enable Normal port1.2 enable enable Normal port1.3 enable(*) enable Normal port1.4 enable enable Normal port1.5 enable enable Normal port1.6 enable enable Normal port1.7 enable enable Normal port1.8 enable enable Normal port1.9 enable enable Normal : : : : ------------------------------------------------------- (*): Indicates that the feature is enabled.
- If a loop has been detected, the loop detection status can be checked.
- In the case of example 1:
Yamaha>show loop-detect loop-detect: Enable port loop-detect port-blocking status ------------------------------------------------------- port1.1 enable(*) enable Detected ... (The status of LAN port #1 is “Detected”) port1.2 enable enable Normal port1.3 enable(*) enable Blocking ... (The status of LAN port #3 is “Blocking”) port1.4 enable enable Normal port1.5 enable enable Normal port1.6 enable enable Normal port1.7 enable enable Normal port1.8 enable enable Normal port1.9 enable enable Normal : : : : ------------------------------------------------------- (*): Indicates that the feature is enabled.
- In the case of example 2:
Yamaha>show loop-detect loop-detect: Enable port loop-detect port-blocking status ------------------------------------------------------- port1.1 enable(*) enable Shutdown ... (The status of LAN port #1 is “Shutdown”) port1.2 enable enable Normal port1.3 enable(*) enable Normal port1.4 enable enable Normal port1.5 enable enable Normal port1.6 enable enable Normal port1.7 enable enable Normal port1.8 enable enable Normal port1.9 enable enable Normal : : : : ------------------------------------------------------- (*): Indicates that the feature is enabled.
- In the case of example 1:
6 Points of Caution
None
7 Related Documentation
- SWP2 Series Technical Data (Basic Functions)
- Layer 3 functions
- SWP2 Series Technical Data (Basic Functions)
- Layer 3 functions
- IPv4/IPv6 common settings
IPv4/IPv6 common settings
1 Function Overview
This product is compatible with the following network environment settings that are common to IPv4 and IPv6, mainly for the purpose of maintenance (configuring the settings of the switch).
- DNS client settings
2 Definition of Terms Used
None
3 Function Details
3.1 DNS client settings
This product supports DNS (Domain Name System) clients.
If a FQDN (Fully Qualified Domain Name) has been set for an NTP server or a syslog server, an inquiry is made to the DNS server to retrieve the IPv4/IPv6 address.
This product provides the following DNS client control functions.
- Set IP address of the DNS server
- Set default domain name
- Set query domain list
Inquiries to the DNS server are enabled by default, and the setting can be changed by using the dns-client enable/disable command.
3.1.1 Set IP address of the DNS server
Up to three IP addresses can be set for the DNS server, using the methods shown below.
- Manual setting using the dns-client name-server command
- This lets you specify the IPv4/IPv6 address.
- Automatic setting via DHCP
- The highest default gateway value takes priority if there is more than one.
This product always gives priority to the information that was set via commands.
Check the configured DNS servers by using the show dns-client command.
3.1.2 Set default domain
Only one default domain can be set using the methods shown below. The domain can be specified using up to 256 characters.
- Manual setting using the dns-client domain-name command
- Automatic setting via DHCP
- The highest default gateway value takes priority if there is more than one.
As with the IP addresses of the DNS server, this product gives priority to the information that was set via commands.
Check the default domain that was set by using the show dns-client command.
The use of a default domain is only allowed if there are no listings in the search domain list.
3.1.3 Set query domain list
This product uses a query domain list to manage the domain names used when inquiring with the DNS.
Up to six domain names can be set on the query domain list using the method below.
- Manual setting using the dns-client domain-list command
The query domain list that has been set can be checked using the show dns-client command.
The query domain list must be within 256 characters total for all domain names registered.
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Function types | Operations | Operating commands |
|---|---|---|
| DNS client settings | DNS client settings | dns-client enable/disable |
| Set DNS server address | dns-client name-server | |
| Set default domain name | dns-client domain-name | |
| Set query domain list | dns-client domain-list | |
| Show DNS client settings | show dns-client |
5 Examples of Command Execution
5.1 DNS client settings
Set DNS client settings for this product to prepare an environment for DNS queries.
- Specify 192.168.100.1 and 192.168.100.2 as the IP addresses of the servers for DNS queries.
- Specify example.com as the default domain used for DNS queries.
- Enable the DNS query functionality.
Yamaha(config)#dns-client enable
- Since this is specified as the default value, we do not need to do set this specifically.
- Specify the DNS servers.
Yamaha(config)#dns-client name-server 192.168.100.1 Yamaha(config)#dns-client name-server 192.168.100.2
- Set the default domain.
Yamaha(config)#dns-client domain-name example.com
- Check the DNS client information that was set.
Yamaha#show dns-client DNS client is enabled Default domain : example.com Domain list : Name Servers : 192.168.100.1 192.168.100.2 * - Values assigned by DHCP Client.
6 Points of Caution
None
7 Related Documentation
None
- SWP2 Series Technical Data (Basic Functions)
- Layer 3 functions
- IPv4 basic settings
IPv4 basic settings
1 Function Overview
This product is compatible with the following IPv4 network environment settings , mainly for the purpose of maintenance (configuring the settings of the switch).
- IPv4 address settings
- Route information settings
- ARP table settings
2 Definition of Terms Used
- IPv4 link local address
This is an address that is only valid within the same segment, within the range of 169.254.0.0/16 to 169.254.255.255/16.
3 Function Details
3.1 IPv4 address settings
This product lets you specify the IPv4 address and subnet mask for a VLAN interface.
As the setting method, both fixed settings and automatic settings via DHCP are supported.
- To set the fixed/automatic IPv4 address, use the ip address command.
- The actions when specifying automatic settings via DHCP are shown below.
- The HostName option (option code 12) can be added to the Discover/Request message.
- The lease time requested from the DHCP server is fixed at 72 hours. (The actual lease time will depend on the setting of the DHCP server.)
- If the no ip addresscommand is executed with automatic settings, a release message for the IPv4 address obtained is sent to the DHCP server.
- The information obtained from the DHCP server can be checked using the show dhcp lease.
- For IPv4 addresses, 1 primary address and 4 secondary addresses can be specified per VLAN interface.
A maximum of 8 IPv4 addresses can be specified for the entire system.
The IPv4 address that is allocated to a VLAN interface can be checked using the show ip interface command.
- In the initial state, automatic setting by DHCP is specified for the default VLAN (VLAN #1).
3.2 Auto IP function
As part of the IPv4 address setting functionality, this product provides an auto IP function which automatically generates IPv4 link local addresses based on the MAC address.
The auto IP function only works when an IPv4 address has not been allocated from the DHCP server. (The IPv4 address must be set to “DHCP” as a prerequisite.)
This function confirms whether the automatically-generated IPv4 link local address does not already exist on the network via ARP.
If it has been confirmed that the address does not already exist, the generated address will start to be used.
If the IPv4 address was allocated from the DHCP server after the IPv4 link local address was determined via auto IP, the IPv4 link local address is discarded, and the IP address obtained from the DHCP server is used.
- To enable the Auto IP function, use the auto-ip enable command.
- The Auto IP function can be enabled for only one VLAN interface. In the initial state, the default VLAN (VLAN #1) is enabled.
3.3 Route information settings
This product refers to a routing table when sending syslog messages and when sending out voluntary IPv4 packets as a IPv4 host for NTP-based time adjustments and so on.
This product uses the following functions to perform the routing table operations.
- Set VLAN interface route information
- Set default gateway
- Set static route information
- Show route information
3.3.1 VLAN interface route information
When setting an IPv4 address on this product for a VLAN interface, the correspondence between the network address and VLAN ID is automatically set as route information.
When releasing IPv4 addresses set for the VLAN interface, the above settings will be deleted.
3.3.2 Set default gateway
The destination for IPv4 packets sent to network addresses that are not set in the routing table can be set as the default gateway on this product.
- To set the default gateway, use the ip route command.
- To show the default gateway, use the show ip route command.
3.3.3 Set static route information
A static route to the destination network address (the gateway address to which packets will be sent) can be set on this product.
- Static route information is set using the ip route command.
- Static route information is displayed using the show ip route command.
3.3.4 Routing table and route selection
You will use the following two types of table to specify routing information.
- RIB (Routing Information Base: IP routing table)
- FIB (Forwarding Information Base: IP forwarding table)
The roles of each are explained below.
- RIB
RIB (Routing Information Base: IP routing table) is a database that stores various routing information.
- A route is registered in the RIB in the following cases.
- When an IPv4 address is assigned to a VLAN interface
- When a static route or a default gateway are specified manually
- When a default gateway is learned via a DHCP message
- To check the RIB, use the show ip route database command.
- A route is registered in the RIB in the following cases.
- FIB
FIB (Forwarding Information Base: IP forwarding table) is a database that is referenced when deciding how to forward IP packets.
Of the routes that are registered in the RIB, the FIB registers only the route that is determined to be “optimal” and is actually used for forwarding packets.
- The conditions by which a route is determined to be optimal are as follows.
- The corresponding VLAN interface is in the link up state
- If multiple routes to the same destination are registered in the RIB, only one is decided in the following order of priority
- A manually specified route takes priority over a route learned via a DHCP message.
- A route whose gateway has a higher IP address value takes priority
- To check the FIB, use the show ip route command.
- The conditions by which a route is determined to be optimal are as follows.
3.4 ARP table settings
When sending IPv4 packets, this product uses ARP (Address Resolution Protocol) to obtain the MAC addresses from the IPv4 addresses.
The correspondence between IPv4 address and MAC address is saved in the ARP table with the following specifications.
- The ARP entries saved in the ARP table manage the following information.
- IPv4 address
- MAC address
- VLAN interface
- Up to 508 entries are stored in the ARP table, including dynamic and static entries.
- With the default settings, dynamic entries saved in the ARP table are maintained for 300 sec.
The entry timeout value can be changed using the arp-ageing-timeout command.
- Dynamic entries saved in the ARP table can be cleared regardless of the timeout value, by using the clear arp-cache command.
- Settings for the static entries in the ARP table are made using the arp command. Up to 255 items can be registered.
- Use the show arp command to check the ARP table.
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Function types | Operations | Operating commands |
|---|---|---|
| IPv4 address settings | Set IPv4 address | ip address |
| Show IPv4 address | show ip interface | |
| Set dynamic IPv4 address by DHCP client | ip address dhcp | |
| Show DHCP client status | show dhcp lease | |
| Enable/disable Auto IP function | auto-ip enable/disable | |
| Route information settings | Set default gateway | ip route |
| Show default gateway | show ip route | |
| Set static route information | ip route | |
| Show static route information | show ip route | |
| Show route information | show ip route | |
| ARP table settings | Show ARP table | show arp |
| Set timeout for dynamic entries | arp-ageing-timeout | |
| Clear dynamic entries | clear arp-cache | |
| Set static entry | arp |
5 Examples of Command Execution
5.1 Set IPv4 network environment (DHCP)
In this example, the IPv4 addresses are set on this product, and an environment is set up for accessing the unit from a remote terminal.
- Maintenance for this product is done using the default VLAN (VLAN #1).
- The IPv4 address is set automatically by DHCP for the default VLAN (VLAN #1).
- Permit Web/TFTP access from hosts connected to VLAN #1.
- Check the IPv4 address that is currently set.
If the default settings are still in effect, the fixed IPv4 address (192.168.100.240/24) is set.
Yamaha#show ip interface brief Interface IP-Address Status Protocol vlan1 192.168.100.240/24 up up
- Specify DHCP for the default VLAN (VLAN #1).
Yamaha#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Yamaha(config)#interface vlan1 Yamaha(config-if)#ip address dhcp
- Check the information that was provided by the DHCP server.
Yamaha(config-if)#end Yamaha#show dhcp lease Interface vlan1 -------------------------------------------------------------------------------- IP Address: 192.168.1.3 Expires: YYYY/MM/DD 05:08:41 Renew: YYYY/MM/DD 19:08:41 Rebind: YYYY/MM/DD 02:38:41 Server: Options: subnet-mask 255.255.255.0 default-gateway 192.168.1.1 dhcp-lease-time 72000 domain-name-servers 192.168.1.1 dhcp-server-identifier 192.168.1.1 domain-name xxx.xxxxx.xx.xx
- Set the default VLAN (VLAN #1) to permit access from HTTP servers and TFTP servers.
Access using a remote host over the Web after settings are made.
Yamaha(config)#http-server interface vlan1 ... (Allow HTTP server access) Yamaha(config)#tftp-server interface vlan1 ... (Allow TFTP server access)
6 Points of Caution
None
7 Related Documentation
- SWP2 Series Technical Data (Basic Functions)
- Layer 3 functions
- IPv6 basic settings
IPv6 basic settings
1 Function Overview
This product is compatible with the following IPv6 network environment settings , mainly for the purpose of maintenance (configuring the settings of the switch).
- IPv6 address settings
- Route information settings
- Neighbor cache table settings
2 Definition of Terms Used
- RA (Router Advertisement)
This is a system that automatically sets address information and network settings for devices of the network that is associated with a router.
- IPv6 address
The IPv6 address is 128 bits expressed as hexadecimal. The address is divided into eight fields delimited by “:” with 16 bits in each field.
- 2001:02f8:0000:0000:1111:2222:0000:4444
The expression can be abbreviated according to the following rules.
- If the beginning of a field is a zero, the zero can be omitted.
- A field that consists of four zeros can be abbreviated as a single zero.
- Multiple fields consisting only of consecutive zeros can be abbreviated as “::” in only one location for the entire address.
Applying these rules to the above address, we get the following.
- 2001:2f8::1111:2222:0:4444
- IPv6 link local address
This is an address that is only valid within the same segment, and is in the following range.
- [Start]FE80:0000:0000:0000:0000:0000:0000:0000
- [End]FE80:0000:0000:0000:FFFF:FFFF:FFFF:FFFF
3 Function Details
3.1 IPv6 address settings
This product lets you specify the IPv6 address and prefix length for a VLAN interface.
As the setting method, both fixed settings and automatic settings via RA (router advertisement) are supported.
- In order to specify an IPv6 address, IPv6 functionality must be enabled for the corresponding VLAN interface.
- To enable IPv6 functionality, use the ipv6 enable command.
- When IPv6 functionality is enabled, an IPv6 link local address is automatically assigned.
- To set a fixed/automatic IPv6 address, use the ip address command.
- 5 global addresses (including automatically specified) and 1 link local address can be specified per VLAN interface.
A maximum of 8 IPv6 addresses can be specified for the entire system.
The IPv6 address that is allocated to a VLAN interface can be checked using the show ipv6 interface command.
3.2 Route information settings
This product refers to a routing table when sending syslog messages and when sending out voluntary IPv6 packets as a IPv6 host for NTP-based time adjustments and so on.
This product uses the following functions to perform the routing table operations.
- Set VLAN interface route information
- Set default gateway
- Set static route information
- Show route information
3.2.1 VLAN interface route information
When an IPv6 address is specified for a VLAN interface, the correspondence between the network address and the VLAN ID is automatically specified by this product as route information.
When IPv6 addresses set for the VLAN interface are released, the above settings are deleted.
3.2.2 Set default gateway
The destination for IPv6 packets sent to network addresses that are not set in the routing table can be set as the default gateway on this product.
- To set the default gateway, use the ipv6 route command.
- To show the default gateway, use the show ipv6 route command.
3.2.3 Set static route information
A static route to the destination network address (the gateway address to which packets will be sent) can be set on this product.
- Static route information is set using the ipv6 route command.
- Static route information is displayed using the show ipv6 route command.
3.2.4 Routing table and route selection
You will use the following two types of table to specify routing information.
- RIB (Routing Information Base: IP routing table)
- FIB (Forwarding Information Base: IP forwarding table)
The roles of each are explained below.
- RIB
RIB (Routing Information Base: IP routing table) is a database that stores various routing information.
- A route is registered in the RIB in the following cases.
- When an IPv6 address is assigned to a VLAN interface
- When a static route or a default gateway are specified manually
- To check the RIB, use the show ipv6 route database command.
- A route is registered in the RIB in the following cases.
- FIB (Forwarding Information Base: IP forwarding table) is a database that is referenced when deciding how to forward IP packets.
Of the routes that are registered in the RIB, the FIB registers only the route that is determined to be “optimal” and is actually used for forwarding packets.
- The conditions by which a route is determined to be optimal are as follows.
- The corresponding VLAN interface is in the link up state
- If multiple routes to the same destination are registered in the RIB, only one is decided in the following order of priority
- A route whose gateway has a higher IP address value takes priority
- To check the FIB, use the show ipv6 route command.
- The conditions by which a route is determined to be optimal are as follows.
3.3 Neighbor cache table settings
When sending IPv6 packets, this product uses Neighbor Discovery Protocol to obtain the MAC addresses from the IPv6 addresses.
The correspondence between IPv6 address and MAC address is saved in the neighbor cache table with the following specifications.
- The neighbor cache entries saved in the neighbor cache table manage the following information.
- IPv6 address
- MAC address
- VLAN interface
- Up to 124 entries are stored in the neighbor cache table, including dynamic and static entries.
- Dynamic entries saved in the neighbor cache table can be cleared by using the clear ivp6 neighbors command.
- Settings for the static entries in the neighbor cache table are made using the ipv6 neighbor command. Up to 63 items can be registered.
- Use the show ipv6 neighbor command to check the neighbor cache table.
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Function types | Operations | Operating commands |
|---|---|---|
| IPv6 address settings | Enable/disable IPv6 addresses | ipv6 enable/disable |
| Set IPv6 address | ipv6 address | |
| Show IPv6 address | show ipv6 interface | |
| Set RA setting for IPv6 address | ipv6 address autoconfig | |
| Route information settings | Set default gateway | ipv6 route |
| Show default gateway | show ipv6 route | |
| Set static route information | ipv6 route | |
| Show static route information | show ipv6 route | |
| Show route information | show ipv6 route | |
| Neighbor cache settings | Set static neighbor cache entry | ipv6 neighbors |
| Show neighbor cache table | show ipv6 neighbors | |
| Clear neighbor cache table | clear ipv6 neighbors |
5 Examples of Command Execution
5.1 Setting up a IPv6 network environment (fixed settings)
In this example, the IPv6 addresses are manually set on this product, and an environment is set up for accessing the unit from a remote terminal.
- Maintenance for this product is done using the default VLAN (VLAN #1).
- The IPv6 address is set manually for the default VLAN (VLAN #1).
- Permit Web/TFTP access from hosts connected to VLAN #1.
- This sets 2001:db8:1::2/64 for the default VLAN (VLAN #1).
Yamaha#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Yamaha(config)#interface vlan1 Yamaha(config-if)#ipv6 enable ... (Enable IPv6) Yamaha(config-if)#ipv6 address 2001:db8:1::2/64 ... (Set IPv6 address)
- Check the IPv6 address that was set.
Yamaha(config-if)#end Yamaha#show ipv6 interface brief Interface IP-Address Status Protocol vlan1 2001:db8:1::2/64 up up fe80::2a0:deff:fe:2/64 - Set the default VLAN (VLAN #1) to permit access from HTTP servers and TFTP servers.
Access using a remote host over the Web after settings are made.
Yamaha(config)#http-server interface vlan1 ... (Allow HTTP server access) Yamaha(config)#tftp-server interface vlan1 ... (Allow TFTP server access)
5.2 Setting up a IPv6 network environment (automatic settings using RA)
In this example, the IPv6 addresses are automatically set on this product, and an environment is set up for accessing the unit from a remote terminal.
- Maintenance for this product is done using the default VLAN (VLAN #1).
- The IPv6 address is set automatically by RA for the default VLAN (VLAN #1).
- Permit Web/TFTP access from hosts connected to VLAN #1.
- Specify RA for the default VLAN (VLAN #1).
Yamaha#configure terminal Enter configuration commands, one per line. End with CNTL/Z. Yamaha(config)#interface vlan1 Yamaha(config-if)#ipv6 enable ... (Enable IPv6) Yamaha(config-if)#ipv6 address autoconfig ... (Set RA)
- Check the IPv6 address that was obtained from RA.
Yamaha(config-if)#end Yamaha#show ipv6 interface brief Interface IP-Address Status Protocol vlan1 2001:db8::2a0:deff:fe:2/64 up up fe80::2a0:deff:fe:2/64 - Set the default VLAN (VLAN #1) to permit access from HTTP servers and TFTP servers.
Access using a remote host over the Web after settings are made.
Yamaha(config)#http-server interface vlan1 ... (Allow HTTP server access) Yamaha(config)#tftp-server interface vlan1 ... (Allow TFTP server access)
6 Points of Caution
None
7 Related Documentation
Static routing
1 Function Overview
With this product, static routing (static route information) can be used for route control in IP networks.
The administrator can explicitly store route information by entering a command.
Both static routes for IPv4 networks and static routes for IPv6 networks can be set.
There are the following two types of static route information.
| Type | Description |
|---|---|
| VLAN interface route information | Route information automatically stored by IP address setting by ip/ipv6 address command |
| Static route information | Route information stored by route setting by ip/ipv6 route command |
Use the show ip/ipv6 route command to display the routing table.
2 Definition of Terms Used
None
3 Function Details
3.1 VLAN interface route information
Route information that is automatically stored when the IP address is set using the ip/ipv6 address command.
This is the route information of the network directly connected to this product, and is associated with the interface.
Set 192.168.100.1/24 as the IP address to the VLAN1 interface and show the routing table.
Yamaha(config)# interface vlan1
Yamaha(config-if)# ip address 192.168.100.1/24
Yamaha(config-if)# exit
Yamaha(config)# exit
Yamaha#show ip route
Codes: C - connected, S - static
* - candidate default
C 192.168.100.0/24 is directly connected, vlan1
Gateway of last resort is not set
3.2 Static route information
Route information stored by route setting by ip/ipv6 route command.
You can set a static route for a specific network or set a default gateway.
When setting the default gateway, specify 0.0.0.0/0 as the destination network.
Up to 128 IPv4 static routes can be set using the ip route command.
Up to 32 IPv6 static routes can be set using the ipv6 route command.
Set the gateway of the route 172.16.0.0/16 to 192.168.100.254 and show the routing table.
Yamaha(config)# ip route 172.16.0.0/24 192.168.100.254
Yamaha(config)# exit
Yamaha# show ip route
Codes: C - connected, S - static
* - candidate default
S 172.16.0.0/24 [1/0] via 192.168.100.254, vlan1
C 192.168.100.0/24 is directly connected, vlan1
Gateway of last resort is not set
Set 192.168.100.200 as the default gateway and show the routing table.
Yamaha(config)# ip route 0.0.0.0/0 192.168.100.200
Yamaha(config)# exit
Yamaha# show ip route
Codes: C - connected, S - static
* - candidate default
Gateway of last resort is 192.168.100.200 to network 0.0.0.0
S* 0.0.0.0/0 [1/0] via 192.168.100.200, vlan1
S 172.16.0.0/24 [1/0] via 192.168.100.254, vlan1
C 192.168.100.0/24 is directly connected, vlan1
3.3 Show the routing table
There are two types of routing table: the IP forwarding table (FIB), which stores only the route information actually used in packet transfer, and the IP routing table (RIB), which stores all the route information.
All VLAN interface route information and static route information are stored in the IP routing table. Then, only the route information actually used in the packet transfer process is stored in the IP forwarding table.
Use the show ip/ipv6 route command to show the IP forwarding table and IP routing table.
In the routing table, VLAN interface route information and static route information are shown as follows.
| Type | Display |
|---|---|
| VLAN interface route information | C - connected |
| Static route information | S - static |
If no option is specified for show ip/ipv6 route, the IP forwarding table is displayed.
The IP routing table can be shown by specifying the database option with show ip/ipv6 route.
You can also specify other options to show only summary information or information for a specific route.
| Option | Description |
|---|---|
| IP address | Shows the route information used when forwarding packets to the specified IP address. |
| IP address and prefix | Shows route information that matches the specified information. |
| database | Shows all set route information (IP routing table). |
| summary | Shows IP routing table summary information |
For details on how to use the show ip route command, see the command reference.
3.4 Priority of route information (management distance)
Route information has a priority that is generally called Administrative Distance.
This is used when the route information to the same destination is stored in the VLAN interface route information and the static route information, to decide which one has priority.
The priority of route information can be applied not only to static routing but also to dynamic routing.
The priority of route information for static routing can be specified in the range from 1 to 255 by the option at the end of the ip route command.
The smaller the value, the higher the priority. In the initial state, the priority is as follows.
| Type | Initial priority value | How to change the priority |
|---|---|---|
| VLAN interface route information | None (higher priority than any other route information) | Setting cannot be changed. |
| Static route information | 1 | It can be specified in the range of 1-255 by the option at the end of the ip/ipv6 route command. |
3.5 Enabling the routing function
Use the ip/ipv6 forwarding command to enable/disable the routing function.
In the initial state, the routing function is disabled for both IPv4 and IPv6.
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Function types | Operations | Operating commands |
|---|---|---|
| Route information settings | Set static route information | ip route / ipv6 route |
| Show static route information | show ip route / show ipv6 route | |
| Show route information | show ip route / show ipv6 route | |
| Setting the routing function | Setting the routing function | ip forwarding / ipv6 forwarding |
| Status display of routing function | show ip forwarding / show ipv6 forwarding |
5 Points of Caution
None
6 Related Documentation
None
- SWP2 Series Technical Data (Basic Functions)
- IP multicast functions
IGMP Snooping
1 Function Overview
IGMP snooping is a function to suppress consumption of network bandwidth in a VLAN environment, by controlling any surplus multicast flooding.
On an L2 switch, since multicast packets are distributed per VLAN, if there is even one device in the VLAN that wants to receive the multicast packet, the packet will be distributed to all ports within the same VLAN.
Operations during multicast distribution (no IGMP snooping)
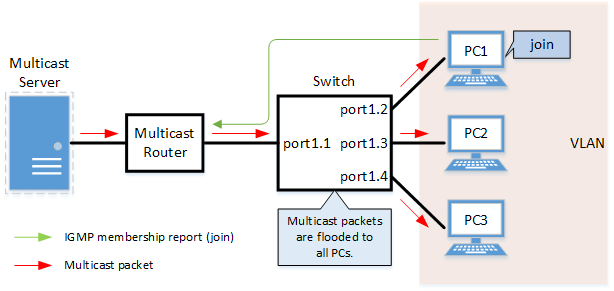
When using the IGMP snooping function, the IGMP messages exchanged between the receiving device and the multicast router are monitored (snooped), the packet from the relevant group will only be distributed to the port, to which the device that wants to receive the multicast packet is connected.
Operations during multicast distribution (using IGMP snooping)
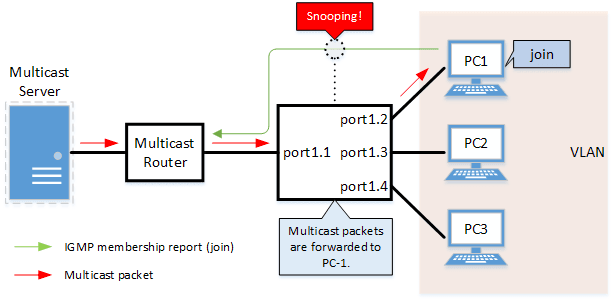
2 Definition of Terms Used
- IGMP (Internet Group Management Protocol)
This is a protocol to control multicast groups.
The multicast router can determine which hosts on the LAN are members of the multicast network, and the hosts can communicate which multicast group they belong to.
There are three protocol versions, respectively defined by IGMPv1 (RFC1112), IGMPv2 (RFC2236), and IGMPv3 (RFC3376).
- Multicast router port
This is the LAN/SFP port to which the multicast router is connected.
The LAN/SFP port that receives the IGMP general query is automatically acquired as the multicast router port.
- IGMP report control function
This is a function where the switch controls the data transmission load between the multicast router and the hosts.
The messages gathered by this product to perform control are shown below.
- IGMP reports replied to IGMP general queries by hosts, sent from the multicast router
- IGMP leave messages notified by the host
The report control function works with IGMPv1/v2/v3.
- Fast Leave function
If a LAN/SFP port receives an IGMPv2/v3 leave message, this function immediately disconnects the port from ports receiving multicast traffic (deletes the FDB entry necessary for transmission).
Normally, when processing IGMPv2/v3 messages, if a leave message is received, a group-specific query is to that port to confirm that the receiver exists, but if the fast-leave function is enabled, that action is not performed.
For this reason, the fast leave function is effective only when there is a single receiver under the control of the LAN/SFP port.
The fast-leave function operates only when an IGMPv2/v3 leave message is received.
- IGMP query transmission function (IGMP Querier)
This is a function to send IGMP general and specific queries.
It is used to make IGMP snooping function in an environment without a multicast router.
- Data Forwarding to Multicast Router Port Control Function
This function controls multicast data being forwarded to the multicast router port.
Normally, all multicast group data already acquired by the product is forwarded to the multicast router port, but if this function is enabled, then only multicast group data acquired by receiving an IGMP report via the multicast router port is forwarded.
If unnecessary multicast data flow between switches is restricting bandwidth, the problem can be mitigated by enabling this function in combination with the l2-unknown-mcast discard command.
3 Function Details
The operating specifications for IGMP snooping are shown below.
- This product offers snooping functions compatible with IGMP v1/v2/v3.
You can use the ip igmp snooping version command to make later versions operate on this product.
Version settings are made for the VLAN interface, and initial settings are for v3.
The difference in operations between the configured version and received frame versions are shown in the table below.
- If an IGMP query whose version is higher than the settings is received, the configured version will be lowered, and the query will be forwarded.
- If an IGMP report whose version is higher than the specified version is received, the relevant report will be discarded without being forwarded.
- If an IGMP query and report of a lower version than the specified version is received, it is forwarded unmodified as the received version.
- The settings to enable/disable IGMP snooping are made for the VLAN interface.
The default value is enabled.
- The IGMP snooping function can handle the following five operations.
- Multicast router port setting
- IGMP report control
- Fast-leave
- IGMP query transmission
- Data Forwarding to Multicast Router Port Control
- Although the multicast router port is automatically acquired on VLAN interfaces where IGMP snooping is set to “enable”, the ip igmp snooping mrouter interface command can also be used to make static settings.
The show ip igmp snooping mrouter command is used to check multicast router ports that are set for the VLAN interface.
- The IGMP report control function is specified using the ip igmp snooping report-suppression command for VLAN interfaces.
The default value is enabled.
When transmitting an IGMP report or IGMP leave message using the report control function, the IPv4 address allocated to the VLAN interface will be used for the source IPv4 address.
(The address will be set and transmitted as “0.0.0.0” if it has not been allocated.)
- The fast-leave function is set for the VLAN interface using the ip igmp snooping fast-leave command.
The default value is disabled.
- The IGMP query transmission function is supported in order to allow use of IGMP snooping in environments that do not have a multicast router.
The IGMP query transmission function controls the following two parameters.
- IGMP query transmission function Enable/disable
- The ip igmp snooping querier command is used for VLAN interfaces.
- The default value is disabled.
- IGMP query transmission interval
- This is executed using the ip igmp snooping query-interval command.
- The transmission interval can be set from 20–18,000 sec., and the default value is 125 sec.
- IGMP query transmission function Enable/disable
- When multiple devices transmit queries within a VLAN, the query is sent by the device with the lowest IPv4 address within the VLAN.
When this product receives a query from a device whose IPv4 address is lower than its own, the query transmission function will be halted.
The source iPv4 address that is set when a query is transmitted uses the IPv4 address allocated to the VLAN interface. If an IPv4 address has not been allocated, an IPv4 address allocated to a different VLAN interface is used instead.
(If no IPv4 addresses have been allocated to any VLAN interfaces, the address will be set and transmitted as “0.0.0.0”.)
- This product features a function that forces the TTL value of a received IGMP packet to change to “1” if the TTL value is invalid (a value other than “1”), instead of discarding the packet.
This is defined as the “TTL check function”, and it can be configured for a VLAN interface by using the ip igmp snooping check ttl command.
The default setting value for the TTL check function is enabled (packets with invalid TTL values are discarded).
- The data forwarding to multicast router port control function is specified for VLAN interfaces using the ip igmp snooping mrouter-port data-suppression command.
The default value is disabled.
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating Commands |
|---|---|
| Enable/disable IGMP snooping | ip igmp snooping |
| Set IGMP snooping fast-leave | ip igmp snooping fast-leave |
| Set multicast router port | ip igmp snooping mrouter interface |
| Set query transmission function | ip igmp snooping querier |
| Set IGMP query transmission interval | ip igmp snooping query-interval |
| Set IGMP snooping TTL check | ip igmp snooping check ttl |
| Set IGMP version | ip igmp snooping version |
| Setting the IGMP Report Control Function | ip igmp snooping report-suppression |
| Setting the Data Forwarding to Multicast Router Port Control Function | ip igmp snooping mrouter-port data-suppression |
| Show multicast router port information | show ip igmp snooping mrouter |
| Show IGMP multicast recipient information | show ip igmp snooping groups |
| Show an interface’s IGMP-related information | show ip igmp snooping interface |
| Clear IGMP group membership entries | clear ip igmp snooping |
5 Examples of Command Execution
5.1 IGMP snooping settings (with multicast router)
In an environment with a multicast router, enable the IGMP snooping function and join a multicast group.
Data is distributed only to PC1 and PC3.
IGMP snooping setting example (with multicast router)
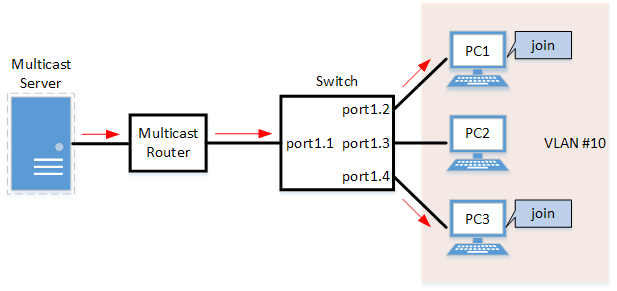
- LAN ports #1–#4 are set as access ports, and associated with VLAN #10.
- Since there is a multicast router, the IGMP query transmission function is left as “disabled”.
- Multicast router port acquisition is set to automatic acquisition only. (A static setting is not used.)
- The fast-leave function is enabled.
- Define VLAN #10, and set IGMP snooping.
Yamaha(config)# vlan database Yamaha(config-vlan)#vlan 10 ... (VLAN #10 definition) Yamaha(config-vlan)#exit Yamaha(config)#interface vlan10 Yamaha(config-if)#ip igmp snooping enable ... (Enable IGMP Snooping for VLAN #10) Yamaha(config-if)#no ip igmp snooping querier ... (Disable IGMP query transmission function for VLAN #10) Yamaha(config-if)#ip igmp snooping fast-leave ... (Enable IGMP Fast-leave function for VLAN #10)
- By default, IGMP snooping is enabled and IGMP query transmission is disabled, so there is no need to set them.
- Set LAN ports #1–#4 as access ports, and associate them with VLAN #10.
Yamaha(config)# interface port1.1 Yamaha(config-if)# switchport mode access Yamaha(config-if)# switchport access vlan 10 (Also perform the above settings for LAN ports #2-#4.)
- Confirm the multicast router port information. (It should be connected to LAN port #1.)
Yamaha#show ip igmp snooping mrouter vlan10 VLAN Interface IP-address Expires 10 port1.1(dynamic) 192.168.100.216 00:00:49
- Confirm the information for the multicast recipient.
Yamaha#show ip igmp snooping groups IGMP Snooping Group Membership Group source list: (R - Remote, S - Static) Vlan Group/Source Address Interface Flags Uptime Expires Last Reporter Version 10 239.0.0.1 port1.2 R 00:00:13 00:00:41 192.168.100.2 V3 10 239.0.0.1 port1.4 R 00:00:02 00:00:48 192.168.100.4 V3
5.2 IGMP snooping settings (without multicast router)
In an environment without a multicast router, enable the IGMP snooping function and join a multicast group.
Data is distributed only to PC1 and PC3.
IGMP snooping settings (without multicast router)
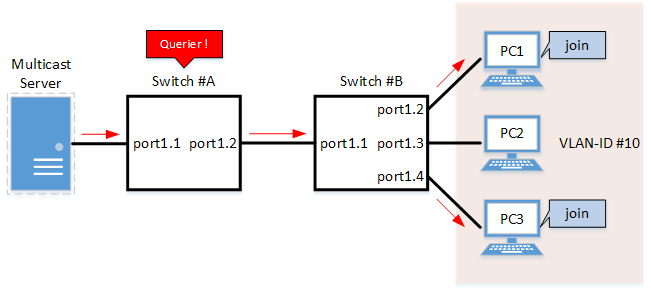
- Switch #A
- LAN ports #1–#2 are set as access ports, and associated with VLAN #10.
- The IGMP query transmission function is enabled.
The IGMP query transmission interval is set to 20 sec.
- Switch #B
- LAN ports #1–#4 are set as access ports, and associated with VLAN #10.
- Multicast router port acquisition is set to automatic acquisition only. (A static setting is not used.)
- The Fast-Leave function is enabled.
- Since there is a device that sets invalid TTL values in IGMP packets, disable the TTL check function.
- [Switch #A] Define VLAN #10, and set IGMP snooping.
Yamaha(config)# vlan database Yamaha(config-vlan)#vlan 10 ... (VLAN #10 definition) Yamaha(config-vlan)#exit Yamaha(config)#interface vlan10 Yamaha(config-if)#ip igmp snooping enable ... (Enable IGMP Snooping for VLAN #10) Yamaha(config-if)#ip igmp snooping querier ... (Enable IGMP query transmission function for VLAN #10) Yamaha(config-if)#ip igmp snooping query-interval 20 ... (Set 20 seconds as the IGMP query transmission interval for VLAN #10)
- Since IGMP snooping is enabled by default, we do not need to set this specifically.
- [Switch #A] Set LAN ports #1–#2 as access ports, and associate them with VLAN #10.
Yamaha(config)# interface port1.1 Yamaha(config-if)# switchport mode access Yamaha(config-if)# switchport access vlan 10 (Also perform the above settings for LAN port #2.)
- [Switch #B] Define VLAN #10, and set IGMP snooping.
Yamaha(config)# vlan database Yamaha(config-vlan)#vlan 10 ... (VLAN #10 definition) Yamaha(config-vlan)#exit Yamaha(config)#interface vlan10 Yamaha(config-if)#ip igmp snooping enable ... (Enable IGMP Snooping for VLAN #10) Yamaha(config-if)#no ip igmp snooping querier ... (Disable IGMP query transmission function for VLAN #10) Yamaha(config-if)#no ip igmp snooping check ttl ... (Disable TTL check function for VLAN #10) Yamaha(config-if)#ip igmp snooping fast-leave ... (Enable IGMP Fast-leave function for VLAN #10)
- By default, IGMP snooping is enabled and IGMP query transmission is disabled, so there is no need to set them.
- [Switch #B] Set LAN ports #1–#4 as access ports, and associate them with VLAN #10.
Yamaha(config)# interface port1.1 Yamaha(config-if)# switchport mode access Yamaha(config-if)# switchport access vlan 10 (Also perform the above settings for LAN ports #2-#4.)
- [Switch #B] Confirm the information for the multicast recipient. (It should be connected to LAN port #1.)
Yamaha#show ip igmp snooping mrouter vlan10 VLAN Interface IP-address Expires 10 port1.1(dynamic) 192.168.100.216 00:00:49
- [Switch #B] Confirm the information for the multicast recipient.
Yamaha#show ip igmp snooping groups IGMP Snooping Group Membership Group source list: (R - Remote, S - Static) Vlan Group/Source Address Interface Flags Uptime Expires Last Reporter Version 10 239.0.0.1 port1.2 R 00:00:13 00:00:41 192.168.100.2 V3 10 239.0.0.1 port1.4 R 00:00:02 00:00:48 192.168.100.4 V3
5.3 IGMP Snooping Setting (If Distributing Data in Both Directions)
In a configuration with two switches, both switches are connected to a multicast server and computer.
Each computer frequently switches between participating multicast groups to minimize the interruption time.
- IGMP Snooping Setting Example (If Distributing Data in Both Directions)
- Switch #A
- Sets LAN ports #1–#4 as access ports and associates them with VLAN #10.
- The IGMP query transmission function is enabled.
Sets the IGMP query transmission interval value to 20 sec.
- The Fast-Leave function is enabled.
- The IGMP report control function is disabled.
- Increasing the number of multicast servers or data distributions could cause port bandwidth restrictions, so the data forwarding to multicast router port control function is enabled to only forward the minimum data necessary.
It also discards unknown multicast frames.
- LAN port #1 is set as a static multicast router port for forwarding IGMP reports to non-queriers.
- Switch #B
- Sets LAN ports #1–#4 as access ports and associates them with VLAN #10.
- Multicast router port acquisition is set to automatic acquisition only. (A static setting is not used.)
- The Fast-Leave function is enabled.
- The IGMP report control function is disabled.
- Increasing the number of multicast servers or data distributions could cause port bandwidth restrictions, so the data forwarding to multicast router port control function is enabled to only forward the minimum data necessary.
It also discards unknown multicast frames.
- [Switch #A] Define VLAN #10 and specify IGMP snooping.
Yamaha(config)# vlan database Yamaha(config-vlan)#vlan 10 ... (Defines VLAN #10) Yamaha(config-vlan)#exit Yamaha(config)#interface vlan10 Yamaha(config-if)#ip igmp snooping enable ... (Enables IGMP snooping for VLAN #10) Yamaha(config-if)#ip igmp snooping querier ... (Enables the IGMP query transmission function for VLAN #10) Yamaha(config-if)#ip igmp snooping query-interval 20 ... (Sets the IGMP query transmission interval to 20 seconds for VLAN #10) Yamaha(config-if)#ip igmp snooping fast-leave ... (Enables the fast-leave function for VLAN #10) Yamaha(config-if)#ip igmp snooping report-suppression disable ... (Disables the report control function for VLAN #10) Yamaha(config-if)#ip igmp snooping mrouter-port data-suppression enable ... (Enables the data forwarding to multicast router port control function for VLAN #10) Yamaha(config-if)#ip igmp snooping mrouter interface port1.1 ... (Sets LAN port #1 as the multicast router port for VLAN #10)
- IGMP snooping does not need to be specified because it is enabled by default.
- [Switch #A] Set LAN ports #1–#4 as access ports and associate them with VLAN #10.
Yamaha(config)# interface port1.1 Yamaha(config-if)# switchport mode access Yamaha(config-if)# switchport access vlan 10 (Configures the settings above for LAN ports #2–#4 as well.)
- [Switch #A] Discard unknown multicast frames.
Yamaha(config)#l2-unknown-mcast discard
- [Switch #B] Define VLAN #10 and specify IGMP snooping.
Yamaha(config)# vlan database Yamaha(config-vlan)#vlan 10 ... (Defines VLAN #10) Yamaha(config-vlan)#exit Yamaha(config)#interface vlan10 Yamaha(config-if)#ip igmp snooping enable ... (Enables IGMP snooping for VLAN #10) Yamaha(config-if)#no ip igmp snooping querier ... (Disables the IGMP query transmission function for VLAN #10) Yamaha(config-if)#ip igmp snooping fast-leave ... (Enables the fast-leave function for VLAN #10) Yamaha(config-if)#ip igmp snooping report-suppression disable ... (Disables the report control function for VLAN #10) Yamaha(config-if)#ip igmp snooping mrouter-port data-suppression enable ... (Enables the data forwarding to multicast router port control function for VLAN #10)
- IGMP snooping is enabled and IGMP query transmission is disabled in default settings, so there is no need to specify those settings.
- [Switch #B] Set LAN ports #1–#4 as access ports, and associate them with VLAN #10.
Yamaha(config)# interface port1.1 Yamaha(config-if)# switchport mode access Yamaha(config-if)# switchport access vlan 10 (Configures the settings above for LAN ports #2–#4 as well.)
- [Switch #B] Discard unknown multicast frames.
Yamaha(config)#l2-unknown-mcast discard
- [Switch #A] Check the multicast router port information. (Connected to LAN port #1)
Yamaha#show ip igmp snooping mrouter vlan10 VLAN Interface IP-address Expires 10 port1.1(static) -- --
- [Switch #A] Check the multicast receiver information.
Yamaha#show ip igmp snooping groups IGMP Snooping Group Membership Group source list: (R - Remote, S - Static) Vlan Group/Source Address Interface Flags Uptime Expires Last Reporter Version 10 239.0.0.1 port1.1 R 00:00:02 00:00:48 192.168.100.3 V3 10 239.0.0.2 port1.1 R 00:00:02 00:00:48 192.168.100.4 V3 10 239.0.0.3 port1.3 R 00:00:04 00:00:46 192.168.100.1 V3 10 239.0.0.1 port1.4 R 00:00:03 00:00:47 192.168.100.2 V3
- [Switch #B] Check the multicast router port information. (Connected to LAN port #1)
Yamaha#show ip igmp snooping mrouter vlan10 VLAN Interface IP-address Expires 10 port1.1(dynamic) 192.168.100.240 00:00:25
- [Switch #B] Check the multicast receiver information.
Yamaha#show ip igmp snooping groups IGMP Snooping Group Membership Group source list: (R - Remote, S - Static) Vlan Group/Source Address Interface Flags Uptime Expires Last Reporter Version 10 239.0.0.1 port1.1 R 00:00:03 00:00:47 192.168.100.2 V3 10 239.0.0.3 port1.1 R 00:00:04 00:00:46 192.168.100.1 V3 10 239.0.0.1 port1.3 R 00:00:02 00:00:48 192.168.100.3 V3 10 239.0.0.2 port1.4 R 00:00:02 00:00:48 192.168.100.4 V3
6 Points of Caution
To change how unknown multicast frames are processed, use the l2-unknown-mcast command to specify settings.
To exclude specific multicast addresses from unknown multicast frames, specify the l2-unknown-mcast forward command.
When a topology change is detected, if you want to send a query regardless of the normal transmission interval, set the l2-mcast snooping tcn-query command.
7 Related Documentation
- L2 switching functions: VLAN
MLD Snooping
1 Function Overview
MLD snooping is a function to suppress consumption of network bandwidth in an IPv6 VLAN environment, by controlling any surplus multicast flooding.
On an L2 switch, since multicast packets are distributed per VLAN, if there is even one device in the VLAN that wants to receive the multicast packet, the packet will be distributed to all ports within the same VLAN.
Operations during multicast distribution (no MLD snooping)
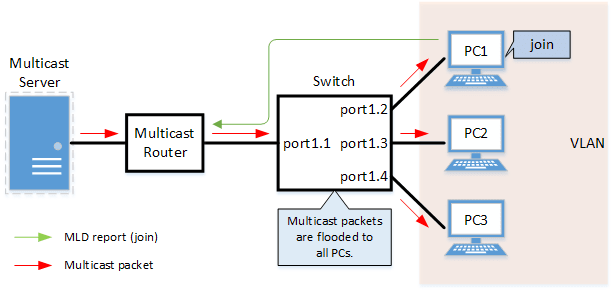
When using the MLD snooping function, the MLD messages exchanged between the receiving device and the multicast router are monitored (snooped), and the packet from the relevant group will only be distributed to the port, to which the device that wants to receive the multicast packet is connected.
Operations during multicast distribution (using MLD snooping)
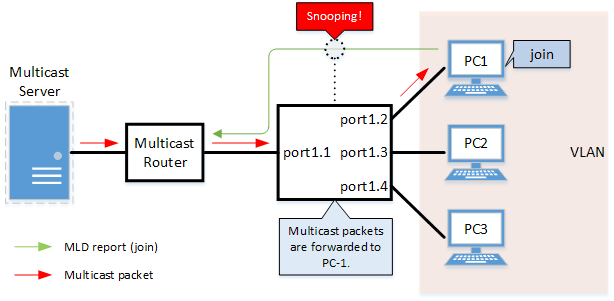
2 Definition of Terms Used
- MLD (Multicast Listener Discovery)
This is a protocol to control multicast groups using IPv6 (a sub-protocol of ICMPv6).
The multicast router can determine which hosts on the LAN are members of the multicast network, and the hosts can communicate which multicast group they belong to.
There are two protocol versions, respectively defined by , MLDv1 (RFC2710), and MLDv2 (RFC3810).
- Multicast router port
This is the LAN/SFP port to which the multicast router is connected.
The LAN/SFP port that receives the MLD general query is automatically acquired as the multicast router port.
- MLD report control function
This is a function where the L2 switch controls the data transmission load between the multicast router and the hosts.
The messages gathered by this product to perform control are shown below.
- MLD reports replied to MLD general queries by hosts, sent from the multicast router
- MLD Done messages notified by the host and MLD reports (Leave)
The report control function works with MLDv1/v2.
- MLD Fast Leave function
This function allows for the LAN/SFP port that received an MLDv1 Done and an MLDv2 report (Leave) to immediately stop receiving multicasts (deleting the necessary FDB entry).
Previously, when an MLDv1 Done message and an MLDv2 report (Leave) was received in the course of MLD leave processing, a group-specific query was sent to check for the existence of a receiver; but if the fast-leave function is enabled, this operation is not performed.
For this reason, the fast leave function is effective only when there is a single receiver under the control of the LAN/SFP port.
- MLD query transmission function (MLD Querier)
This is a function to send MLD general and specific queries.
It is used to make the MLD snooping function in an environment without a multicast router.
3 Function Details
The operating specifications for MLD snooping are shown below.
- This product offers snooping functions compatible with MLDv1/v2.
You can use the mld snooping version command to make later versions work on this product.
Version settings are made for the VLAN interface, and initial settings are for v2.
The difference in operations between the configured version and received frame versions are shown in the table below.- If an MLD query whose version is higher than the settings is received, the version will be lowered to the version that was configured, and the query will be forwarded.
- If an MLD report whose version is higher than the configured version is received, the relevant report will be discarded without being forwarded.
- The settings to enable/disable MLD snooping are made for the VLAN interface.
The initial setting for the default VLAN (VLAN #1) and the initial setting after a VLAN is generated are both enabled.
- The MLD snooping function can handle the following four operations.
- Multicast router port setting
- MLD report control
- MLD fast leave
- MLD query transmission
- Although the multicast router port is automatically acquired on VLAN interfaces where MLD snooping is set to "enable”, the mld snooping mrouter interface command can also be used to make static settings.
The show mld snooping mrouter command is used to check multicast router ports that are set for the VLAN interface.
- The MLD report control function is automatically enabled on VLAN interfaces for which MLD snooping has been set to “enable”.
The MLD report control function cannot be disabled.
When transmitting an MLD report or MLD Done message using the report control function, the IPv6 link local address allocated to the VLAN interface will be used for the source IPv6 address.
(The address will be set and transmitted as “::” if it has not been allocated.)
- The MLD fast-leave function is set for the VLAN interface using the mld snooping fast-leave command.
The initial setting for the default VLAN (VLAN #1) and the initial setting after a VLAN is generated are both disabled.
- The MLD query transmission function is supported in order to allow use of MLD snooping in environments that do not have a multicast router.
The MLD query transmission function controls the following two parameters.- MLD query transmission function enable/disable
- The mld snooping querier command is used for VLAN interfaces.
- The initial setting for the default VLAN (VLAN #1) and the initial setting after a VLAN is generated are both disabled.
- MLD query transmission interval
- This is set using the mld snooping query-interval command.
- The transmission interval can be set from 20–18,000 sec., and the default value is 125 sec.
- MLD query transmission function enable/disable
- When multiple devices transmit queries within a VLAN, the query is sent by the device with the lowest IPv6 address within the VLAN.
When this product receives a query from a device whose IPv6 address is lower than its own, the query transmission function will be halted.
The source iPv6 address that is set when a query is transmitted uses the IPv6 link local address allocated to the VLAN interface. If an IPv6 link local address has not been allocated, an IPv6 link local address allocated to a different VLAN interface is used instead.
(If no IPv6 link local addresses have been allocated to any VLAN interfaces, the query is not transmitted.)
4 Related Commands
Related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Enable/disable MLD snooping | ipv6 mld snooping |
| Set MLD snooping fast-leave | ipv6 mld snooping fast-leave |
| Set the multicast router port | ipv6 mld snooping mrouter interface |
| Set query transmission function | ipv6 mld snooping querier |
| Set the MLD query transmission interval | ipv6 mld snooping query-interval |
| Set the MLD version | ipv6 mld snooping version |
| Show multicast router port information | show ipv6 mld snooping mrouter |
| Show MLD multicast recipient information | show ipv6 mld snooping groups |
| Show an interface’s MLD-related information | show ipv6 mld snooping interface |
| Clear the MLD group membership entries | clear ipv6 mld snooping |
5 Examples of Command Execution
5.1 MLD snooping settings (with multicast router)
In an environment with a multicast router, this enables the MLD snooping function, and data is distributed only to PC1 and PC3 which are joined to a multicast group.
MLD snooping setting example (with multicast router)
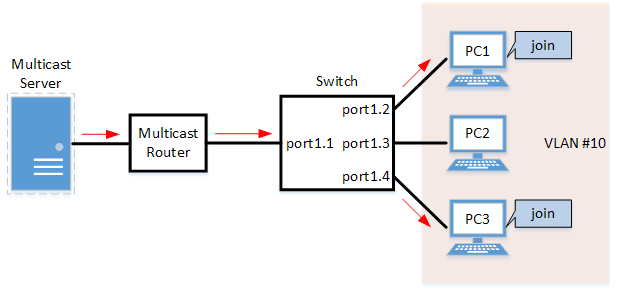
- LAN ports #1–#4 are set as access ports, and associated with VLAN #10.
- Since there is a multicast router, the MLD query transmission function is left as “disabled”.
- Multicast router port acquisition is set to automatic acquisition only. (A static setting is not used.)
- The MLD fast-leave function is enabled.
- Define VLAN #10, and set MLD snooping.
Yamaha(config)# vlan database Yamaha(config-vlan)#vlan 10 ... (definition of VLAN #10) Yamaha(config-vlan)#exit Yamaha(config)#interface vlan10 Yamaha(config-if)#ipv6 enable ... (enables IPv6 functionality on VLAN #10) Yamaha(config-if)#ipv6 mld snooping ... (enables MLD Snooping on VLAN #10) Yamaha(config-if)#no ipv6 mld snooping querier ... (disables the MLD query transmission function on VLAN #10) Yamaha(config-if)#ipv6 mld snooping fast-leave ... (enables the MLD Fast-leave function on VLAN #10)
- By default, MLD snooping is enabled and MLD query transmission is disabled, so there is no need to set them.
- Set LAN ports #1–#4 as access ports, and associate them with VLAN #10.
Yamaha(config)# interface port1.1 Yamaha(config-if)# switchport mode access Yamaha(config-if)# switchport access vlan 10 (the settings above are also applied to LAN ports #2–#4)
- Confirm the multicast router port information. (It should be connected to LAN port #1.)
Yamaha#show ipv6 mld snooping mrouter vlan10 VLAN Interface IP-address Expires 10 port1.1(dynamic) fe80::2a0:deff:feae:b879 00:00:43
- Confirm the information for the multicast recipient.
Yamaha#show ipv6 mld snooping groups MLD Connected Group Membership Vlan Group Address Interface Uptime Expires Last Reporter 10 ff15::1 port1.2 00:00:13 00:00:41 fe80::a00:27ff:fe8b:87e2 10 ff15::1 port1.4 00:00:02 00:00:48 fe80::a00:27ff:fe8b:87e4
5.2 MLD snooping settings (without multicast router)
In an environment without a multicast router, this enables the MLD snooping function, and data is distributed only to PC1 and PC3 which are joined to a multicast group.
MLD snooping settings (without multicast router)
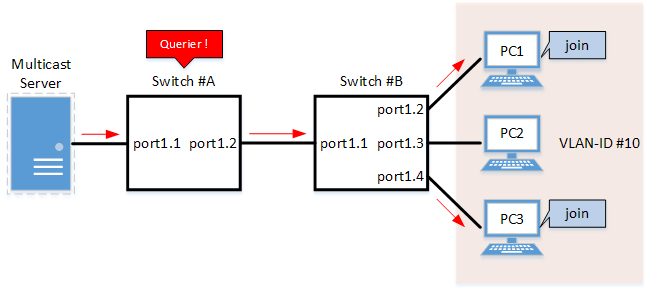
- Switch #A
- LAN ports #1–#2 are set as access ports, and associated with VLAN #10.
- The MLD query transmission function is enabled.
The MLD query transmission interval is set to 20 sec.
- Switch #B
- LAN ports #1–#4 are set as access ports, and associated with VLAN #10.
- Multicast router port acquisition is set to automatic acquisition only. (A static setting is not used.)
- The MLD fast-leave function is enabled.
- [Switch #A] Define VLAN #10, and set MLD snooping.
Yamaha(config)# vlan database Yamaha(config-vlan)#vlan 10 ... (definition of VLAN #10) Yamaha(config-vlan)#exit Yamaha(config)#interface vlan10 Yamaha(config-if)#ipv6 enable ... (enables IPv6 functionality on VLAN #10) Yamaha(config-if)#ipv6 mld snooping ... (enables MLD Snooping on VLAN #10) Yamaha(config-if)#ipv6 mld snooping querier ... (enables the MLD query transmission function on VLAN #10) Yamaha(config-if)#ipv6 mld snooping query-interval 20 ... (sets the MLD query transmission interval to 20 sec. on VLAN #10)
- Since MLD snooping is enabled by default, we do not need to set this specifically.
- [Switch #A] Set LAN ports #1–#2 as access ports, and associate them with VLAN #10.
Yamaha(config)# interface port1.1 Yamaha(config-if)# switchport mode access Yamaha(config-if)# switchport access vlan 10 (the settings above are also applied to LAN port #2)
- [Switch #B] Define VLAN #10, and set MLD snooping.
Yamaha(config)# vlan database Yamaha(config-vlan)#vlan 10 ... (definition of VLAN #10) Yamaha(config-vlan)#exit Yamaha(config)#interface vlan10 Yamaha(config-if)#ipv6 enable ... (enables IPv6 functionality on VLAN #10) Yamaha(config-if)#ipv6 mld snooping ... (enables MLD Snooping on VLAN #10) Yamaha(config-if)#no ipv6 mld snooping querier ... (disables the MLD query transmission function on VLAN #10) Yamaha(config-if)#ipv6 mld snooping fast-leave ... (enables the MLD Fast-leave function on VLAN #10)
- By default, MLD snooping is enabled and MLD query transmission is disabled, so there is no need to set them.
- [Switch #B] Set LAN ports #1–#4 as access ports, and associate them with VLAN #10.
Yamaha(config)# interface port1.1 Yamaha(config-if)# switchport mode access Yamaha(config-if)# switchport access vlan 10 (the settings above are also applied to LAN ports #2–4)
- [Switch #B] Confirm the information for the multicast recipient. (It should be connected to LAN port #1.)
Yamaha#show ipv6 mld snooping mrouter vlan10 VLAN Interface IP-address Expires 10 port1.1(dynamic) fe80::2a0:deff:feae:b879 00:00:43
- [Switch #B] Confirm the information for the multicast recipient.
Yamaha#show ipv6 mld snooping groups MLD Connected Group Membership Vlan Group Address Interface Uptime Expires Last Reporter 10 ff15::1 port1.2 00:00:13 00:00:41 fe80::a00:27ff:fe8b:87e2 10 ff15::1 port1.4 00:00:02 00:00:48 fe80::a00:27ff:fe8b:87e4
6 Points of Caution
If you want to change the handling of unknown multicast frames, use the l2-unknown-mcast command.
When a topology change is detected, if you want to send a query regardless of the normal transmission interval, set the l2-mcast snooping tcn-query command.
7 Related Documentation
- Layer 2 functions: VLAN
- Layer 3 functions: IPv6 basic settings
- SWP2 Series Technical Data (Basic Functions)
- Traffic control functions
ACL
1 Function Overview
The access list (ACL) is a conditional statement that determines whether to permit or to deny the frame.
If the access list is applied to the interface, only the permitted frame will be transferred, and the denied frame will be discarded.
As this allows for only specified frames to be selected for transfer, this feature is primarily used for security purposes.
This product supports three access list types, as shown in the table below.
Access list type
| Access list type | Deciding criteria | Access list ID | Purpose of use |
|---|---|---|---|
| IPv4 access list | Source IPv4 address Destination IPv4 address IP protocol type | 1–2000 | Filters access from specific hosts and networks. Filters specific IP protocol types such as TCP/UDP. |
| IPv6 access list | Source IPv6 address | 3001–4000 | Filters access from specific hosts and networks. |
| MAC access list | Source MAC address Destination MAC address | 2001–3000 | Filters access and data transfer from specific devices. |
2 Definition of Terms Used
- ACL
- Abbreviation of “Access Control List”.
- Wildcard mask
Information that specifies which portion of the specified IPv4 address or MAC address is read. This is used when specifying a range of IPv4 addresses or MAC addresses as ACL conditions.
- When the wildcard mask bit is “0”: check the corresponding bit
- When the wildcard mask bit is “1”: do not check the corresponding bit
Examples of settings using wildcard masks are shown below. (The underlined portion is the wildcard mask.)
- To specify conditions for subnet 192.168.1.0/24: 192.168.1.0 0.0.0.255 (specified as decimal)
- To specify conditions for vendor code 00-A0-DE-*-*-*: 00A0.DE00.0000 0000.00FF.FFFF (specified as hexadecimal)
3 Function Details
3.1 Generating an access list
Access lists for the number of IDs in each access list number can be generated. (Refer to the table in "1 Function Overview”.)
A maximum of 256 control parameters can be registered per list for access lists.
If the registered control conditions are not satisfied, forwarding occurs as usual.
3.2 Applying to the interface
The following table shows how access lists are applied to the input/output interfaces of this product.
Note that one access list can be applied to the IN and OUT respectively for an interface.
- Status of access list application to the interface
Access list type LAN/SFP port VLAN interface Static/LACP logical interface in out in out in out IPv4 access list ✓ ✓(*) ✓ ✓(*) ✓ - IPv6 access list ✓ ✓ ✓ ✓ ✓ - MAC access list ✓ - ✓ - ✓ - (*) As a limitation, an IPv4 access list that specifies a range of port numbers cannot be applied to the output (out) side of an interface.
The number of access lists that can be applied to the interface depends on the number of control parameters that are registered in the access lists.
On this product, a maximum of 512 control parameters can be registered to the interface.
Applying an access list to the interface will use resources “equivalent to the number of control parameters that are registered in the access list”.
However, control parameters may also be used internally within the system in some cases, and use resources accordingly.
3.3 Settings for the LAN/SFP port and logical interface
The steps for applying an access list to a LAN/SFP port and to a logical interface is shown below.
- Decide on the filtering parameters, and generate the access list.
- Add explanatory text as necessary.
- Check the access list.
- Apply the access list to the LAN/SFP port and logical interface.
- Check the applied access list.
A list of operation commands is given below.
Access list operation commands (when applied to the LAN/SFP port and logical interface)
| Access list type | Generate access list | Check access list | Apply access list | Check the applied access list |
|---|---|---|---|---|
| IPv4 access list | access-list | show access-list | access-group | show access-group |
| IPv6 access list | access-list | show access-list | access-group | show access-group |
| MAC access list | access-list | show access-list | access-group | show access-group |
3.4 VLAN interface settings
The steps for applying access lists to the VLAN interface are shown below.
- Decide on the filtering parameters, and generate the access list.
- Add explanatory text as necessary.
- Check the access list.
- Generate the VLAN access map.
- Set the access list for the VLAN access map.
- Check the VLAN access map.
- Apply the VLAN access map to the VLAN.
- Check the VLAN access map that was applied.
The operations in steps 1 and 2 are the same as those shown in 3.2.
The following is a list of operating commands for steps 3. and following.
VLAN access map operating command
| Access list type | VLAN access map generation | Settings for access list used with VLAN access map | VLAN access map confirmation | VLAN access map application | Confirmation of the applied VLAN access map |
|---|---|---|---|---|---|
| IPv4 access list | vlan access-map | match access-list | show vlan access-map | vlan filter | show vlan filter |
| IPv6 access list | vlan access-map | match access-list | show vlan access-map | vlan filter | show vlan filter |
| MAC access list | vlan access-map | match access-list | show vlan access-map | vlan filter | show vlan filter |
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Apply IPv4 access list | access-group |
| Generate IPv4 access list | access-list |
| Add IPv4 access list explanatory text | access-list description |
| Apply IPv4 access list | access-group |
| Generate IPv6 access list | access-list |
| Add IPv6 access list explanatory text | access-list description |
| Apply IPv6 access list | access-group |
| Generate MAC access list | access-list |
| Add MAC access list explanatory text | access-list description |
| Apply MAC access list | access-group |
| Show generated access list | show access-list |
| Show access list applied to interface | show access-group |
| Create VLAN access map | vlan access-map |
| Set VLAN access map parameters | match |
| Assign VLAN access map to VLAN | vlan filter |
| Show VLAN access map | show vlan access-map |
| Show VLAN access map filter | show vlan filter |
5 Examples of Command Execution
5.1 IPv4 access list settings
5.1.1 Example of application to a LAN port
■ Specify host
In this example, we will set LAN port #1 only to permit access from host:192.168.1.1 to host:10.1.1.1.
Add IPV4-ACL-EX access list explanatory text using #123 as the access list ID.
- Generate and confirm access list #123.
Yamaha(config)#access-list 123 permit any host 192.168.1.1 host 10.1.1.1 ... (Generate access list) Yamaha(config)#access-list 123 deny any any any Yamaha(config)#access-list 123 description IPV4-ACL-EX ... (Add access list explanatory text) Yamaha(config)#end Yamaha# Yamaha#show access-list 123 ... (Check access list) IPv4 access list 123 10 permit any host 192.168.1.1 host 10.1.1.1 20 deny any any any Yamaha# - Apply access list #123 to LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#access-group 123 in ... (Apply access list) Yamaha(config-if)#end Yamaha# Yamaha#show access-group ... (Check access list setting) Interface port1.1 : IPv4 access group 123 in
To change the access list (delete or add a setting), application of the list to the LAN port must be temporarily canceled.
For the setting indicated above, delete the setting that allows access from host: 192.168.1.1 to host: 10.1.1.1 and add a setting that allows access from host: 192.168.1.1 to host: 10.1.1.2.
- Temporarily cancel the application of access list #123 from LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#no access-group 123 in ... (Cancel application of access list)
- Delete, add, and then check the setting in access list #123.
Yamaha(config)#no access-list 123 10 ... (Delete from access list) Yamaha(config)#access-list 123 10 permit any host 192.168.1.1 host 10.1.1.2 ... (Add to access list) Yamaha(config)#end Yamaha# Yamaha#show access-list 123 ... (Check access list) IPv4 access list 123 10 permit any host 192.168.1.1 host 10.1.1.2 20 deny any any any - Apply access list #123 to LAN port #1 again.
Yamaha(config)#interface port1.1 Yamaha(config-if)#access-group 123 in ... (Apply access list)
■ Specify network
In this example, we will set LAN port #1 to permit access from network: 192.168.1.0/24 to host: 10.1.1.1.
The access list ID to be used is #123, and the access list explanatory text IPV4-ACL-EX is added.
- Generate and confirm access list #123.
Yamaha(config)#access-list 123 permit any 192.168.1.0 0.0.0.255 host 10.1.1.1 ... (Generate access list) Yamaha(config)#access-list 123 deny any any any Yamaha(config)#access-list 123 description IPV4-ACL-EX ... (Add access list explanatory text) Yamaha(config)#end Yamaha# Yamaha#show ip access-list ... (Check ACL) IPv4 access list 123 10 permit any 192.168.1.0/24 host 10.1.1.1 20 deny any any any Yamaha# - Apply access list #123 to LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#access-group 123 in ... (Apply access list) Yamaha(config-if)#end Yamaha# Yamaha#show access-group ... (Check access list setting) Interface port1.1 : IPv4 access group 123 in
To change the access list (delete or add a setting), application of the list to the LAN port must be temporarily canceled.
The specific procedure is the same as for specifying a host.
5.1.2 Example of application to the VLAN interface
■ Specify host
In this example, we will set VLAN #1000 only to permit access from host:192.168.1.1 to host:10.1.1.1.
We will use access list ID #123.
The VLAN access map to be used will be VAM-002, and access list #123 will be set.
- Generate and confirm access list #123.
Yamaha(config)#access-list 123 permit any host 192.168.1.1 host 10.1.1.1 ... (Generate access list) Yamaha(config)#access-list 123 deny any any any Yamaha(config)#end Yamaha# Yamaha#show access-list 123 ... (Check access list) IPv4 access list 123 10 permit any host 192.168.1.1 host 10.1.1.1 20 deny any any any - Generate VLAN access map VAM-002, and set access list #123.
Yamaha(config)#vlan access-map VAM-002 ... (Generate VLAN access map) Yamaha(config-vlan-access-map)#match access-list 123 ... (Register access list) Yamaha(config-vlan-access-map)#end Yamaha# Yamaha#show vlan access-map ... (Check VLAN access map and access list settings) Vlan access-map VAM-002 match ipv4 access-list 123 - Apply VLAN access map VAM-002 to VLAN #1000, and confirm the status.
Yamaha(config)#vlan filter VAM-002 1000 in ... (Apply VLAN access map to VLAN) Yamaha(config)#end Yamaha# Yamaha#show vlan filter ... (Check VLAN access map settings) Vlan filter VAM-002 is applied to vlan 1000 in
To change the access list (delete or add a setting), it is necessary to temporarily cancel applying the list to the VLAN interface and the setting in the VLAN access map.
For the setting indicated above, delete the setting that allows access from host: 192.168.1.1 to host: 10.1.1.1 and add a setting that allows access from host: 192.168.1.1 to host: 10.1.1.2.
- Temporarily cancel VLAN access map VAM-002 from being applied to VLAN #1000.
Yamaha(config)#no vlan filter VAM-002 1000 in ... (Delete application of VLAN access map from VLAN)
- Temporarily cancel the access list #123 setting in VLAN access map VAM-002.
Yamaha(config)#vlan access-map VAM-002 ... (Change VLAN access map) Yamaha(config-vlan-access-map)#no match access-list 123 ... (Unregister access list)
- Delete, add, and then check the setting in access list #123.
Yamaha(config)#no access-list 123 10 ... (Delete from access list) Yamaha(config)#access-list 123 10 permit any host 192.168.1.1 host 10.1.1.2 ... (Add to access list) Yamaha(config)#end Yamaha# Yamaha#show access-list 123 ... (Check access list) IPv4 access list 123 10 permit any host 192.168.1.1 host 10.1.1.2 20 deny any any any - Specify the access list #123 setting in VLAN access map VAM-002 again.
Yamaha(config)#vlan access-map VAM-002 ... (Change VLAN access map) Yamaha(config-vlan-access-map)#match access-list 123 ... (Register access list)
- Apply VLAN access map VAM-002 to VLAN #1000 again.
Yamaha(config)#vlan filter VAM-002 1000 in ... (Apply VLAN access map to VLAN)
■ Specify network
In this example, we will set VLAN port #1000 only to permit access from network:192.168.1.0/24 to host:10.1.1.1.
We will use access list ID #123.
The VLAN access map to be used will be VAM-002, and access list #123 will be set.
- Generate and confirm access list #123.
Yamaha(config)#access-list 123 permit any 192.168.1.0 0.0.0.255 host 10.1.1.1 ... (Generate access list) Yamaha(config)#access-list 123 deny any any any Yamaha(config)#end Yamaha# Yamaha#show access-list 123 ... (Check access list) IPv4 access list 123 10 permit any 192.168.1.0/24 host 10.1.1.1 20 deny any any any - Generate VLAN access map VAM-002, and set access list #123.
Yamaha(config)#vlan access-map VAM-002 ... (Generate VLAN access map) Yamaha(config-vlan-access-map)#match access-list 123 ... (Register access list) Yamaha(config-vlan-access-map)#end Yamaha# Yamaha#show vlan access-map ... (Check VLAN access map and access list settings) Vlan access-map VAM-002 match ipv4 access-list 123 - Apply VLAN access map VAM-002 to VLAN #1000, and confirm the status.
Yamaha(config)#vlan filter VAM-002 1000 in ... (Apply VLAN access map to VLAN) Yamaha(config)#end Yamaha# Yamaha#show vlan filter ... (Check VLAN access map settings) Vlan filter VAM-002 is applied to vlan 1000 in
To change the access list (delete or add a setting), it is necessary to temporarily cancel applying the list to the VLAN interface and the setting in the VLAN access map.
The specific procedure is the same as for specifying a host.
5.1.3 Allowing only TCP communication from one direction (example using TCP flags)
Given VLAN10 and VLAN20, this example controls TCP communication so that it occurs in one direction.
- Communication from VLAN10 to VLAN20 is possible by Telnet, etc.
- Communication from VLAN20 to VLAN10 is not possible by Telnet, etc.
- Generate access list #1.
Specify settings that only allow IPv4 TCP packets with an ACK or RST flag.Yamaha(config)#access-list 1 permit tcp any any ack ... (Set access list) Yamaha(config)#access-list 1 permit tcp any any rst Yamaha(config)#access-list 1 deny any any any Yamaha(config)#end Yamaha# Yamaha#show access-list ... (Check access list setting) IPv4 access list 1 10 permit tcp any any ack 20 permit tcp any any rst 30 deny any any any - Generate VLAN access map VAM-ESTABLISHED and specify access list #1.
Yamaha(config)#vlan access-map VAM-ESTABLISHED ... (Generate VLAN access map) Yamaha(config-vlan-access-map)#match access-list 1 ... (Register access list) Yamaha(config-vlan-access-map)#end Yamaha# Yamaha#show vlan access-map ... (Confirm VLAN access map setting) Vlan access-map VAM-ESTABLISHED match ipv4 access-list 1 - Apply VLAN access map VAM-ESTABLISHED to VLAN #20.
Yamaha(config)#vlan filter VAM-ESTABLISHED 20 in ... (Apply VLAN access map to VLAN) Yamaha(config)#end Yamaha# Yamaha#show vlan filter ... (Confirm application status to VLAN) Vlan filter VAM-ESTABLISHED is applied to vlan 20 in
5.2 IPv6 access list settings
5.2.1 Example of application to a LAN port
■ Specify host
In this example, specify settings that only permit LAN port #1 access from host: 2001:db8::1.
The access list ID to be used is #3001, and add access list explanatory text IPV6-ACL-EX.
- Generate and confirm access list #3001.
Yamaha(config)#access-list 3001 permit 2001:db8::1/128 ... (Generate access list) Yamaha(config)#access-list 3001 deny any Yamaha(config)#access-list 3001 description IPV6-ACL-EX ... (Add access list explanatory text) Yamaha(config)#end Yamaha# Yamaha#show access-list 3001 ... (Check access list) IPv6 access list 3001 10 permit 2001:db8::1/128 20 deny any - Apply access list #3001 to LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#access-group 3000 in ... (Apply access list) Yamaha(config-if)#end Yamaha# Yamaha#show access-group ... (Check access list setting) Interface port1.1 : IPv6 access group 3001 in
To change the access list (delete or add a setting), application of the list to the LAN port must be temporarily canceled. For the specific procedure, refer to 5.1.1 Example of application to a LAN port in 5.1 IPv4 access list settings.
■ Specify network
In this example, specify settings that only permit LAN port #1 access from network: 2001:db8::/64.
The access list ID to be used is #3001, and add access list explanatory text IPV6-ACL-EX.
- Generate and confirm access list #3001.
Yamaha(config)#access-list 3001 permit 2001:db8::/64 ... (Generate access list) Yamaha(config)#access-list 3001 deny any Yamaha(config)#access-list 3001 description IPV6-ACL-EX ... (Add access list explanatory text) Yamaha(config)#end Yamaha# show access-list 3001 ... (Check access list) IPv6 access list 3001 10 permit 2001:db8::/64 20 deny any - Apply access list #3001 to LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#access-group 3001 in ... (Apply access list) Yamaha(config-if)#end Yamaha# Yamaha#show access-group ... (Check access list setting) Interface port1.1 : IPv6 access group 3001 in
To change the access list (delete or add a setting), application of the list to the LAN port must be temporarily canceled. For the specific procedure, refer to 5.1.1 Example of application to a LAN port in 5.1 IPv4 access list settings.
5.2.2 Example of application to the VLAN interface
■ Specify host
In this example, specify settings that only permit VLAN #1000 access from host: 2001:db8::1.
We will use access list ID #3001.
The VLAN access map to be used will be VAM-001, and access list #3001 will be set.
- Generate and confirm access list #3001.
Yamaha(config)#access-list 3001 permit 2001:db8::1/128 ... (Generate access list) Yamaha(config)#access-list 3001 deny any Yamaha(config)#end Yamaha# Yamaha#show access-list 3001 ... (Check access list) IPv6 access list 3001 10 permit 2001:db8::1/128 20 deny any - Generate VLAN access map VAM-001, and set access list #3001.
Yamaha(config)#vlan access-map VAM-001 ... (Generate VLAN access map) Yamaha(config-vlan-access-map)#match access-list 3001 ... (Set access list) Yamaha(config-vlan-access-map)#end Yamaha# Yamaha#show vlan access-map ... (Check VLAN access map and access list settings) Vlan access-map VAM-001 match ipv6 access-list 3001 - Apply VLAN access map VAM-001 to VLAN #1000, and confirm the status.
Yamaha(config)#vlan filter VAM-001 1000 in ... (Apply VLAN access map to VLAN) Yamaha(config)#end Yamaha# Yamaha#show vlan filter ... (Check VLAN access map settings) Vlan filter VAM-001 is applied to vlan 1000 in
To change the access list (delete or add a setting), it is necessary to temporarily cancel applying the list to the VLAN interface and the setting in the VLAN access map. For the specific procedure, refer to 5.1.2 Example of application to the VLAN interface in 5.1 IPv4 access list settings.
■ Specify network
In this example, specify settings that only permit VLAN #1000 access from network: 2001:db8::/64.
We will use access list ID #3001.
The VLAN access map to be used will be VAM-001, and access list #3001 will be set.
- Generate and confirm access list #2.
Yamaha(config)#access-list 3001 permit 2001:db8::/64 ... (Generate access list) Yamaha(config)#access-list 3001 deny any Yamaha(config)#end Yamaha# Yamaha#show access-list 3001 ... (Check access list) IPv6 access list 3001 10 permit 2001:db8::/64 20 deny any - Generate VLAN access map VAM-001, and set access list #3001.
Yamaha(config)#vlan access-map VAM-001 ... (Generate VLAN access map) Yamaha(config-vlan-access-map)#match access-list 3001 ... (Set access list) Yamaha(config-vlan-access-map)#end Yamaha# Yamaha#show vlan access-map ... (Check VLAN access map and access list settings) Vlan access-map VAM-001 match ipv6 access-list 3001 - Apply VLAN access map VAM-001 to VLAN #1000, and confirm the status.
Yamaha(config)#vlan filter VAM-001 1000 in ... (Apply VLAN access map to VLAN) Yamaha(config)#end Yamaha# Yamaha#show vlan filter ... (Check VLAN access map settings) Vlan filter VAM-001 is applied to vlan 1000 in
To change the access list (delete or add a setting), it is necessary to temporarily cancel applying the list to the VLAN interface and the setting in the VLAN access map. For the specific procedure, refer to 5.1.2 Example of application to the VLAN interface in 5.1 IPv4 access list settings.
5.3 MAC access list settings
5.3.1 Example of application to a LAN port
■ Specify host
In this example, specify settings that only deny access to LAN port #1 from host: 00-A0-DE-12-34-56.
Add access list explanatory text MAC-ACL-EX using #2001 as the access list ID.
- Generate and confirm access list #2001.
Yamaha(config)#access-list 2001 deny host 00a0.de12.3456 any ... (Generate access list) Yamaha(config)#access-list 2001 description MAC-ACL-EX ... (Add access list explanatory text) Yamaha(config)#end Yamaha# Yamaha#show access-list 2001 ... (Check access list) MAC access list 2001 10 deny host 00A0.DE12.3456 any - Apply access list #2001 to LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#access-group 2001 in ... (Apply access list) Yamaha(config-if)#end Yamaha# Yamaha#show access-group ... (Check access list setting) Interface port1.1 : MAC access group 2001 in
To change the access list (delete or add a setting), application of the list to the LAN port must be temporarily canceled. For the specific procedure, refer to 5.1.1 Example of application to a LAN port in 5.1 IPv4 access list settings.
■ Specify vendor
In this example, specify settings that only deny access to LAN port #1 from vendor code: 00-A0-DE-*-*-* (00-A0-DE-00-00-00 – 00-A0-DE-FF-FF-FF).
Add access list explanatory text MAC-ACL-EX using #2001 as the access list ID.
- Generate and confirm access list #2001.
Yamaha(config)#access-list 2001 deny 00a0.de00.0000 0000.00ff.ffff any ... (Generate access list) Yamaha(config)#access-list 2001 description MAC-ACL-EX ... (Add access list explanatory text) Yamaha(config)#end Yamaha# Yamaha#show access-list 2001 ... (Check access list) MAC access list 2001 10 deny 00A0.DE00.0000 0000.00FF.FFFF any - Apply access list #2001 to LAN port #1.
Yamaha(config)#interface port1.1 Yamaha(config-if)#access-group 2001 in ... (Apply access list) Yamaha(config-if)#end Yamaha# Yamaha#show access-group ... (Check access list setting) Interface port1.1 : MAC access group 2001 in
To change the access list (delete or add a setting), it is necessary to temporarily cancel applying the list to the VLAN interface and the setting in the VLAN access map. For the specific procedure, refer to 5.1.2 Example of application to the VLAN interface in 5.1 IPv4 access list settings.
5.3.2 Example of application to the VLAN interface
■ Specify host
In this example, specify settings that only deny access to VLAN #1000 from host: 00-A0-DE-12-34-56.
Add access list explanatory text MAC-ACL-EX using #2001 as the access list ID.
The VLAN access map to be used will be VAM-003, and access list #2001 will be set.
- Generate and confirm access list #2000.
Yamaha(config)#access-list 2001 deny host 00a0.de12.3456 any ... (Generate access list #2001) Yamaha(config)#access-list 2001 description MAC-ACL-EX ... (Add access list explanatory text) Yamaha(config)#end Yamaha# Yamaha#show access-list ... (Check access list) MAC access list 2001 10 deny host 00A0.DE12.3456 any - Generate VLAN access map VAM-003, and set access list #2001.
Yamaha(config)# vlan access-map VAM-003 ... (Generate VLAN access map) Yamaha(config-vlan-access-map)# match access-list 2001 ... (Register access list) Yamaha(config-vlan-access-map)# end Yamaha# Yamaha#show vlan access-map ... (Check VLAN access map and access list settings) Vlan access-map VAM-003 match mac access-list 2001 - Apply VLAN access map VAM-003 to VLAN #1000, and confirm the status.
Yamaha(config)#vlan filter VAM-003 1000 in ... (Apply VLAN access map to VLAN) Yamaha(config)#end Yamaha# Yamaha#show vlan filter ... (Check VLAN access map settings) Vlan filter VAM-003 is applied to vlan 1000 in
To change the access list (delete or add a setting), it is necessary to temporarily cancel applying the list to the VLAN interface and the setting in the VLAN access map. For the specific procedure, refer to 5.1.2 Example of application to the VLAN interface in 5.1 IPv4 access list settings.
■ Specify vendor
In this example, specify settings that only deny access to VLAN #1000 from vendor code: 00-A0-DE-*-*-* (00-A0-DE-00-00-00 – 00-A0-DE-FF-FF-FF).
Add access list explanatory text MAC-ACL-EX using #2001 as the access list ID. We will use access list ID #2001.
The VLAN access map to be used will be VAM-003, and access list #2001 will be set.
- Generate and confirm access list #2001.
Yamaha(config)#access-list 2001 deny 00a0.de00.0000 0000.00ff.ffff any ... (Generate access list #2001) Yamaha(config)#access-list 2001 description MAC-ACL-EX ... (Add access list explanatory text) Yamaha(config)#end Yamaha# Yamaha#show access-list 2001 ... (Check access list) MAC access list 2001 10 deny 00A0.DE00.0000 0000.00FF.FFFF any - Generate VLAN access map VAM-003, and set access list #2001.
Yamaha(config)# vlan access-map VAM-003 ... (Generate VLAN access map) Yamaha(config-vlan-access-map)# match access-list 2001 ... (Register access list) Yamaha(config-vlan-access-map)# end Yamaha# Yamaha#show vlan access-map ... (Check VLAN access map and access list settings) Vlan access-map VAM-003 match mac access-list 2001 - Apply VLAN access map VAM-003 to VLAN #1000, and confirm the status.
Yamaha(config)#vlan filter VAM-003 1000 in ... (Apply VLAN access map to VLAN) Yamaha(config)#end Yamaha# Yamaha#show vlan filter ... (Check VLAN access map settings) Vlan filter VAM-003 is applied to vlan 1000 in
To change the access list (delete or add a setting), it is necessary to temporarily cancel applying the list to the VLAN interface and the setting in the VLAN access map. For the specific procedure, refer to 5.1.2 Example of application to the VLAN interface in 5.1 IPv4 access list settings.
6 Points of Caution
- LAN/SFP ports for which an access list is configured for received frames cannot belong to a logical interface.
- Access list settings for received frames on an interface cannot be applied to a LAN/SFP port that belongs to a logical interface. If access list settings exist for the received frame of a LAN/SFP port that belongs to a logical interface in startup config, the settings for the most recent port number will be applied to the logical interface.
- Fragment packets may not be judged correctly. Specifically, if layer 4 information (source port number, destination port number, and various TCP flags) is included in the conditions, since the information is not included in the second and subsequent fragment packets, correct judgment cannot be made. If there is a possibility of processing fragmented packets, do not include Layer 4 information in the conditions.
7 Related Documentation
- L2 switching functions: VLAN
QoS
1 Function Overview
QoS (Quality of Service) is a technology for reserving a specified bandwidth for communications over a network, guaranteeing a fixed speed of communication.
Application data is classified and grouped, and then forwarded by group priority level, referring to the DSCP in the IP header or the CoS in the IEEE802.1Q tag.
2 Definition of Terms Used
- CoS (IEEE 802.1p Class of Service)
This expresses priority as a 3-bit field in the VLAN tag header, with a value from 0–7.
Also called 802.1p user priority.
- IP Precedence
This expresses priority as a 3-bit field in the TOS field of the IP header, with a value from 0–7.
Used to indicate the traffic class of the frame in question, for the device that receives the frame.
- DSCP (Diffserv Code Point)
This expresses priority as a 6-bit field in the TOS field of the IP header, with a value from 0–63.
Since DSCP uses the same TOS field as IP precedence, it is compatible with IP-Precedence.
Used to indicate the traffic class of the frame in question, for the device that receives the frame.
- Default CoS
This is the CoS value that is assigned to an untagged frame for the purpose of internal processing.
- Transmission queue
This product has eight transmission queues per port. The transmission queues are numbered from ID 0–7, with larger ID numbers being given higher priority.
- Trust mode
This indicates what will be the basis for deciding (trusting) the transmission queue ID.
The CoS value or DSCP value of the incoming frames can be used to differentiate them, or a priority order specified for each reception port can be applied.
Settings can be configured for each LAN/SFP port and logical interface. Note that the settings for LAN/SFP ports that belong to a logical interface cannot be changed.
The default status (when QoS is enabled) is set to “CoS”.
- Transmission queue ID conversion table
This is a conversion table used when deciding on the transmission queue ID from either the CoS value or the DSCP value.
There are two kinds of transmission queue ID conversion tables, the CoS-transmission queue ID conversion table and the DSCP-transmission queue ID conversion table. Each kind is used with its own trust mode.
Mapping can be freely changed by the user.
- Port priority
This is the priority order assigned for each reception port. If the trust mode is “port priority,” frames received at that port are placed in the transmission queue according to the port’s priority setting.
- Class map
This defines the conditions by which packets are classified into traffic classes.
Packets can be associated and used with policy maps, and QoS processing (pre-marking, transmission queue specification, metering/policing/remarking) per traffic class can be defined.
- Policy map
This is an element for performing a QoS processing series on the reception port. This cannot be used by itself, but rather is associated and used with 1–8 class maps.
When a policy map is applied to a LAN/SFP+ port, traffic is classified per class map that is associated with the policy map for the packets received on the relevant port.
Also, QoS processing (pre-marking, transmission queue specification, metering/policing/remarking) set per traffic class can be performed.
- Policer
This is a group series of metering/policing/remarking settings.
There are two types of policers, an individual policer for metering that targets one traffic class, and a group policer that meters multiple traffic classes by putting them together.
3 Function Details
3.1 Enabling or disabling QoS control
When shipped from the factory, the QoS control of this product is set to disable.
To enable QoS control use the qos enable command. To disable this, use the no qos command.
Most QoS control commands cannot be executed if QoS is not enabled.
The QoS function status can be checked using the show qos command.
In order to enable QoS control, the system’s flow control must be disabled.
3.2 QoS processing flow
The QoS processing flow is shown below.
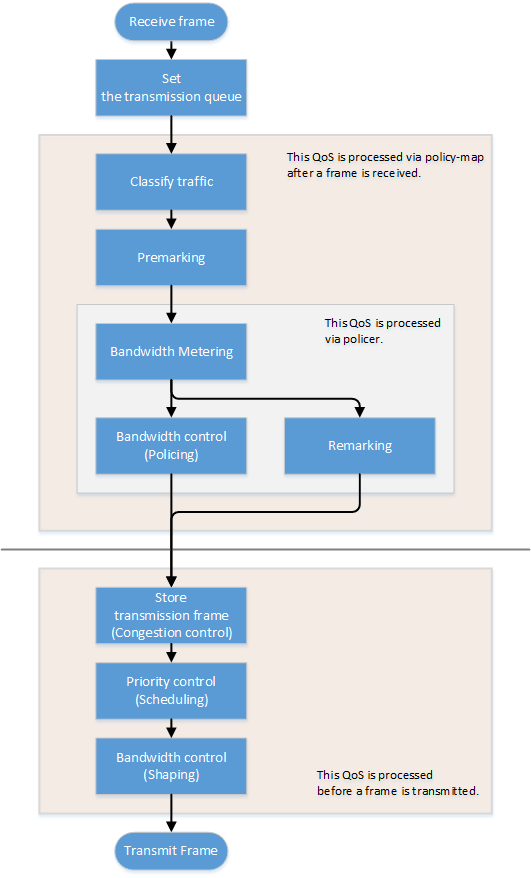
3.3 Transmission queue assignments
When this product receives a frame, it determines the initial value of the transmission queue ID according to the CoS value or DSCP value within the frame and the port priority of the reception port.
Of the factors such as the frame’s CoS value and DSCP value, and the port’s priority order, the port’s trust mode determines which factor will be the basis for determining the transmission queue.
The trust mode can be changed by the qos trust command. The default value (when QoS is enabled) is set to CoS. The transmission queue is assigned per trust mode, using the following rules.
When trust mode is “CoS”
- When the received frame is a frame with a VLAN tag, the CoS value within the tag is used to determine the transmission queue ID.
- When the received frame is a frame without a VLAN tag, the default CoS that is managed by this product is used to determine the transmission queue ID.
The default setting (when QoS is enabled) and the default CoS are set to “0”. This can be changed using the qos cos command.
- Conversion from the CoS value to the transmission queue ID is performed by the CoS-transmission queue ID conversion table.
One such table is maintained by the system, and with the default settings (when QoS is enabled), the settings are as follows. The setting can be changed using the qos cos-queue command.
CoS value Transmission queue ID Traffic Type 0 2 Best Effort 1 0 Background 2 1 Standard(spare) 3 3 Excellent Effort(Business Critical) 4 4 Controlled Load(Streaming Multimedia) 5 5 Video(Interactive Media) less than 100 msec latency and jitter 6 6 Voice(Interactive Media) less than 10 msec latency and jitter 7 7 Network Control(Reserved Traffic)
When trust mode is “DSCP”
- The DSCP in the IP header is used to determine the transmission queue ID.
- Conversion from the DSCP value to the transmission queue ID is performed by the DSCP-transmission queue ID conversion table.
One such table is maintained by the system, and with the default settings (when QoS is enabled), the settings are as follows. The setting can be changed using the qos dscp-queue command.
DSCP value Transmission queue ID Traffic Type 0 - 7 2 Best Effort 8 -15 0 Background 16 - 23 1 Standard(spare) 24 - 31 3 Excellent Effort(Business Critical) 32 - 39 4 Controlled Load(Streaming Multimedia) 40 - 47 5 Video(Interactive Media) less than 100 msec latency and jitter 48 - 55 6 Voice(Interactive Media) less than 10 msec latency and jitter 56 - 63 7 Network Control(Reserved Traffic)
When trust mode is “port priority”
- The transmission queue ID is determined by the port priority.
- By default (when QoS is enabled), port priority is set to 2. The setting can be changed using the qos port-priority-queue command.
If the trust mode is “CoS” or “DSCP,” the transmission queue ID might be reassigned due to QoS processing (see below) by the policy map.
In this case, the new transmission queue ID is reassigned based on the transmission queue ID conversion table that corresponds to the port’s trust mode.
- Pre-marking
- Refer to “Pre-marking” for details.
- Specify transmission queue
- When the trust mode is “CoS”, specify the CoS value that corresponds to the transmission queue ID, using the set cos-queue command.
- When the trust mode is “DSCP”, specify the DSCP value that corresponds to the transmission queue ID, using the set dscp-queue command.
- Remarking
- Refer to Metering/policing/remarking for details.
If the trust mode is “port priority,” the transmission queue ID cannot be changed by the policy map’s QoS processing. (It is not possible to apply a policy map that includes premarking, transmission queue specification, and remarking settings.)
3.4 Transmission queue assignments (frames sent from the switch itself)
As an exception to the transmission queue assignments, frames sent from the switch itself (CPU) are automatically assigned the transmission queue determined by the system. (They are not given transmission queue assignments based on the trust mode.)
The qos queue sent-from-cpu command can be used to change the transmission queue that is assigned, and by default the transmission queue ID is set to 7.
3.5 Traffic classification
Traffic classification is a function to classify received frames, based on a class map that defines the conditions of the IP header, TCP header, and so on.
The conditions that can be classified and the commands for settings are shown in the table below.
Conditions that can be classified, and commands for settings
| Classification condition | Condition-setting command | Class map setting mode | Number that can be registered per class map |
|---|---|---|---|
| Source/destination MAC address | access-list (*Note 3) | match access-list | 1 |
| Source/destination IP address | 1 | ||
| IP protocol type (*Note 1) | 1 | ||
| Ethernet frame type number | match ethertype | 1 | |
| CoS value for VLAN tag header | match cos | 8 | |
| Precedence value for IP header | match ip-precedence | 8 | |
| DSCP value for IP header | match ip-dscp | 8 | |
| VLAN ID (*Note 2) | match vlan, match vlan-range | 30 | |
*1: IPv6 is not subject to classification by IP protocol type.
*2: Does not include isolated or community VLANs in a private VLAN.
*3: Up to 39 conditions can be set in the access list for traffic classification.
- Traffic is classified per class map.
- One classification condition type can be set for one class map. Policer-based QoS processing (metering/policing/remarking) and pre-marking, as well as specifying the transmission queue can be done for frames that match the conditions.
- If classification conditions are not specified, all frames are classified into the corresponding traffic class.
- For classification based on CoS, IP precedence, DSCP, and the VLAN ID, multiple classifications can be made for one class map.
- Associating multiple class maps to a policy map will make it possible to classify complex traffic for the receiving port. Up to eight class maps can be associated to one policy map.
- Information for the class map that was set can be confirmed using the show class-map command.
- Information for the policy map that was set can be confirmed using the show policy-map command.
- Use the show qos map-status to check the port to which the policy map is applied, and the policy map to which the class map is associated.
3.6 Pre-marking
Pre-marking is a function to change (assign) the CoS, IP precedence, and DSCP values for received frames classified into traffic classes.
Pre-marking is set using the policy map and class mode settings shown below.
Pre-marking setting commands
| Pre-marking target | Command for settings |
|---|---|
| CoS | set cos |
| IP Precedence | set ip-precedence |
| DSCP | set ip-dscp |
- The DSCP values that can be premarked include the value recommended in the RFC and those not found in the RFC, for a total of four. (This rule also applies to DSCP values that are used in remarking.) )
- Only one pre-marking setting can be made for a class map. This cannot be used together when specifying a transmission queue (set cos-queue, set ip-dscp-queue).
- When pre-marking, the transmission queue will be reassigned based on the changed value and the transmission queue ID conversion table that corresponds to the trust mode.
3.7 Metering/policing/remarking
Bandwidth can be controlled by measuring the bandwidth used, and discarding or reprioritizing packets according to the measurement results.
The processing series for metering, policing and remarking is done per “policer”.
Processing summary for bandwidth control
| Process name | Summary |
|---|---|
| Metering | This measures how much bandwidth is being taken up by the classified traffic based on the traffic rate and burst size, and classifies this into three bandwidth classes (green, yellow and red). Actions such as discarding (policing) and remarking can be specified for each classified bandwidth class. |
| Policing | The bandwidth usage can be kept within a certain amount by discarding frames, using bandwidth class information. |
| Remarking | The CoS, IP precedence and DSCP value for a frame can be changed using the bandwidth class information. |
3.7.1 Policer types
There are two types of policers: an individual policer that performs metering/policing/remarking on one traffic class, and an aggregate policer that performs these actions on multiple aggregated traffic classes.
- Individual policer
Metering/policing/remarking is done per traffic class.
To make settings, use the policy map/class mode’s police command and remark-map command.
- Aggregate policer
Metering/policing/remarking is done on multiple traffic classes, which are aggregated.
The aggregate policer can be created using the aggregate-police command, and the content can be specified by the aggregate policer mode’s police command and remark-map command.
To apply a created aggregate policer to a traffic class, use the police-aggregate command.
- The commands used to make settings for an individual policer and an aggregate policer respectively are as follows.
Content of setting Individual policer Aggregate policer Create policer - aggregate-police Set policer (metering/policing/remarking)
police single-rate, police twin-rate (policy map / class mode)
police single-rate, police twin-rate (aggregate policer mode)
Apply policer to traffic class police-aggregate Detailed remarking settings remark-map (policy map / class mode)
remark-map (aggregate policer mode)
3.7.2 Metering settings
There are two types of metering: single rate policy (RFC2697) and twin rate policy (RFC2698).
The type of metering to use and the control parameters are specified using the police command (policy map/class mode or aggregate policer mode).
- Single rate policers (RFC2697)
Single rate policers separate the frames within a traffic class into three bandwidth classes: “green” (conforming), “yellow” (exceeding) or “red” (violating), based on the traffic rate (CIR) and burst size (CBS, EBS).
- Single rate policer control parameters
Parameter Explanation CIR (Committed Information Rate)
This is the amount of tokens that is periodically stored in buckets. The amount can be specified in the range of 1–102,300,000 kbps.
CBS (Committed Burst Size)
This is the amount of traffic that can be removed at one time from the first token bucket (a conforming token bucket). The amount can be specified in the range of 11–2,097,120 kByte.
EBS (Exceed Burst Size)
This is the amount of traffic that can be removed at one time from the second token bucket (an exceeding token bucket). The amount can be specified in the range of 11–2,097,120 kByte.
- Single rate policer control parameters
- Twin rate policer (RFC2698)
Twin rate policers separate the frames within a traffic class into three bandwidth classes: “green” (conforming), “yellow” (exceeding) or “red” (violating), based on the traffic rate (CIR, PIR) and burst size (CBS, PBS).
- Twin rate policer control parameters
Parameter Explanation CIR (Committed Information Rate)
This is the amount of tokens periodically stored in the second token bucket (confirming token bucket). The amount can be specified in the range of 1–102,300,000 kbps.
PIR (Peak Information Rate)
This is the amount of tokens periodically stored in the first token bucket (peak token bucket). The amount can be specified in the range of 1–102,300,000 kbps.
However, a value smaller than the CIR cannot be specified.
CBS (Committed Burst Size)
This is the amount of token traffic that can be removed at one time from the conforming token bucket. The amount can be specified in the range of 11–2,097,120 kByte.
PBS (Peak Burst Size)
This is the amount of token traffic that can be removed at one time from the peak token bucket. The amount can be specified in the range of 11–2,097,120 kByte.
- Twin rate policer control parameters
3.7.3 Metering action (policing/remarking) settings
To specify the action for a bandwidth class that was categorized by metering, use the police command (in policy map/class mode or aggregate policer mode).
This product lets you define the following actions for each bandwidth class.
Specifying bandwidth class actions
| Bandwidth class | Forward | Discard | Remark |
|---|---|---|---|
| Green | ✓ | - | - |
| Yellow | ✓ | ✓ | ○ (only one or the other) |
| Red | - | ✓ |
- To make detailed settings for remarking, use the remark-map command (policy map/class mode or aggregate policer mode).
As with pre-marking, remarking to DSCP values can use the value recommended by RFC (refer to separate table 1. “Standard PHB (RFC recommended value)” and up to four others in addition.
When remarking, the transmission queue will be reassigned based on the changed value and the transmission queue ID conversion table that corresponds to the trust mode.
- If metering is not done, all frames that have been classified into traffic classes will be handled as the green bandwidth class.
3.8 Storing in the transmission queue
Frames are stored in the transmission queue that is finally determined through a series of QoS processing.
In order to resolve transmission queue congestion, this product provides a system to select and discard frames.
- Tail drop
This product uses the tail drop method to resolve overflow in the transmission queue.
When the threshold values shown below for the bandwidth class that is classified by metering has been exceeded, the frame in question will be discarded.
Frames discarded by tail drop are counted by the frame counter.
Bandwidth class Tail drop threshold value (%) Green + Yellow 100% Red 60%
- Tail drop is disabled only if flow control is enabled.
It is not possible to change the threshold value.
- The extent of the transmission queue congestion can be checked using the show qos queue-counters command.
- The number of packets discarded by tail drop can be checked using the show interface, show frame-counter command.
3.9 Scheduling
Scheduling is used to determine what rules are used to send out the frames that are stored in the transmission queue.
Appropriate control of the scheduling along with the system to control congestion will help ensure QoS. (Inappropriate scheduling will result in degradation of QoS.)
This product supports two types of scheduling for the transmission queue, the strict priority system (SP) and the weighted round-robin (WRR) system.
SP and WRR can also be integrated in the interface and used together. (When doing so, SP will be given priority during processing.)
Strict priority system (SP)
The data with the highest priority in the queue will be transmitted first.
When a frame is stored in a high-priority queue, it can never be transmitted from a lower-priority queue.
Weighted round-robin system (WRR)
A weight is set for each queue, and frames are transmitted based on the ratio. A weight of 1–32 can be set.
Frames can also be transmitted from a lower-priority queue, within a specified percentage.
The transmission queue settings are made for the entire system, not for each interface.
Use the qos wrr-weight command to set the weight.
The default setting (when QoS is enabled) and the scheduling setting is “SP” for all queues.
3.10 Shaping
If a frame is forwarded from a broadband network to a narrowband network at the same transmission speed when connecting to a network with different bandwidth, the frame cannot be forwarded, which may result in insufficient bandwidth.
Shaping is a function that monitors the frame transmission speed, and restricts the forwarding rate to a specific amount by temporarily buffering frames with a speed that exceeds the limit, and then transmitting them.
Shaping on this product is realized by using a single token bucket.
Single token bucket
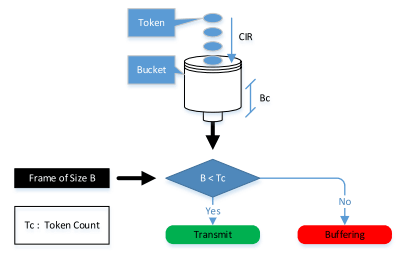
- Shaping can be specified for individual ports and for individual queues, respectively using the following commands.
Object of shaping Command for settings By port traffic-shape rate By transmission queue traffic-shape queue rate
- Specify the upper limit of the transmission rate (CIR) and the burst size (BC).
- The upper limit of the transmission rate (CIR) can be specified from 18–1,000,000 kbps.
- The burst size (BC) can be specified from 4–16,000 kbyte. However, this is specified in 4 Kbyte units.
- If shaping is used both by queue and by port, shaping by port is applied after shaping by queue.
- The default setting (when QoS is enabled) and the shaping setting is “disable” for all ports and all queues.
Separate table 1: Standard PHB (RFC recommended value)
| PHB | DSCP value | RFC | |
|---|---|---|---|
| Default | 0 | RFC2474 | |
| CS (Class Selector) | CS0 | 0 | RFC2474 |
| CS1 | 8 | ||
| CS2 | 16 | ||
| CS3 | 24 | ||
| CS4 | 32 | ||
| CS5 | 40 | ||
| CS6 | 48 | ||
| CS7 | 56 | ||
| AF (Assured Forwarding) | AF11 | 10 | RFC2597 |
| AF12 | 12 | ||
| AF13 | 14 | ||
| AF21 | 18 | ||
| AF22 | 20 | ||
| AF23 | 22 | ||
| AF31 | 26 | ||
| AF32 | 28 | ||
| AF33 | 30 | ||
| AF41 | 34 | ||
| AF42 | 36 | ||
| AF43 | 38 | ||
| EF (Expedited Forwarding) | 46 | RFC2598 | |
4 Related Commands
The related commands are shown below.
For details, refer to the Command Reference.
QoS-related commands
| Operations | Operating commands |
|---|---|
| Enable/disable QoS | qos enable |
| Set default CoS | qos cos |
| Change trust mode | qos trust |
| Generate policy map for ingress frames | policy-map |
| Apply policy map for ingress frames | service-policy input |
| Show status of QoS function setting | show qos |
| Show QoS information for LAN/SFP+ port | show qos interface |
| Show egress queue usage ratio | show qos queue-counters |
| Show policy map information | show policy-map |
| Show map status | show qos map-status |
| Set CoS - transmission queue ID conversion table | qos cos-queue |
| Set DSCP - transmission queue ID conversion table | qos dscp-queue |
| Set port priority order | qos port-priority-queue |
| Set priority order of frames sent from the switch itself | qos queue sent-from-cpu |
| Generate class map (traffic category conditions) | class-map |
| Associate class map | class |
| Set traffic classification conditions (access-group) | match access-list |
| Set traffic classification conditions (CoS) | match cos |
| Set traffic classification conditions (TOS precedence) | match ip-precedence |
| Set traffic classification conditions (DSCP) | match ip-dscp |
| Set traffic classification conditions (Ethernet Type) | match ethertype |
| Set traffic classification conditions (VLAN ID) | match vlan |
| Set traffic classification conditions (VLAN ID range) | match vlan-range |
| Show class map information | show class-map |
| Set pre-marking (CoS) | set cos |
| Set pre-marking (TOS precedence) | set ip-precedence |
| Set pre-marking (DSCP) | set ip-dscp |
| Set individual policer / aggregate policer (single rate) | police signle-rate |
| Set individual policer / aggregate policer (twin rate) | police twin-rate |
| Set remarking for individual policer / aggregate policer | remark-map |
| Create aggregate policer | aggregate-police |
| Show aggregate policer | show aggregate-police |
| Apply aggregate policer | police-aggregate |
| Show metering counter | show qos metering-counters |
| Clear metering counter | clear qos metering-counters |
| Set egress queue (CoS-Queue) | set cos-queue |
| Set egress queue (DSCP-Queue) | set ip-dscp-queue |
| Set egress queue scheduling | qos wrr-weight |
| Set traffic shaping (individual port) | traffic-shape rate |
| Set traffic shaping (individual queue) | traffic-shape queue rate |
5 Examples of Command Execution
5.1 Priority control (SP) using DSCP values
This example allocates the transmission queue based on the DSCP value of the frame, for priority control (SP).
When the DSCP = 56, 46, 8, 0 frame is received, large frames for DSCP values from LAN port #3 will be processed with priority.
DSCP priority control (SP) setting example

- Prioritizing the input frame is done as follows.
- DSCP = 56 frame is set at priority level 7
- DSCP = 46 frame is set at priority level 5
- DSCP = 8 frame is set at priority level 1
- DSCP = 0 frame is set at priority level 0
- This sets the trust mode for the reception ports (LAN ports #1 and #2) on which QoS is enabled.
Yamaha(config)#qos enable … (enable QoS) Yamaha(config)#interface port1.1 … (setting for LAN port #1) Yamaha(config-if)#qos trust dscp … (change trust mode to DSCP) Yamaha(config-if)#exit Yamaha(config)#interface port1.2 … (setting for LAN port #2) Yamaha(config-if)#qos trust dscp … (change trust mode to DSCP) Yamaha(config-if)#exit
- This sets the DSCP - transmission queue ID conversion table.
As the transmission queue ID corresponding to DSCP value = 46, 56 is the default, there is no need to make this setting, but it is listed for purposes of clarity.
Yamaha(config)#qos dscp-queue 56 7 … (place frames of DSCP = 56 in transmission queue #7) Yamaha(config)#qos dscp-queue 46 5 … (place frames of DSCP = 46 in transmission queue #5) Yamaha(config)#qos dscp-queue 8 1 … (place frames of DSCP = 8 in transmission queue #1) Yamaha(config)#qos dscp-queue 0 0 … (place frames of DSCP = 0 in transmission queue #0)
- This sets the scheduling method per transmission queue.
As this is the default, there is no need to make this setting, but it is listed for purposes of clarity.
Yamaha(config)# no qos wrr-weight 7 … (Queue:7 SP method) Yamaha(config)# no qos wrr-weight 5 … (Queue:5 SP method) Yamaha(config)# no qos wrr-weight 1 … (Queue:1 SP method) Yamaha(config)# no qos wrr-weight 0 … (Queue:0 SP method)
5.2 Priority control (SP+WRR) using an access list
This example classifies traffic by using the source IP address, and sets the priority control (WRR).
Priority control (SP+WRR) setting example
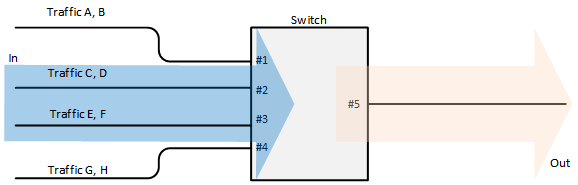
- Classification conditions and priority setting for input frames
- The packet from 192.168.10.2 is classified as traffic A, and is set with a priority level of 7 during packet transmission
- The packet from 192.168.20.2 is classified as traffic B, and is set with a priority level of 6 during packet transmission
- The packet from 192.168.30.2 is classified as traffic C, and is set with a priority level of 5 during packet transmission
- The packet from 192.168.40.2 is classified as traffic D, and is set with a priority level of 4 during packet transmission
- The packet from 192.168.50.2 is classified as traffic E, and is set with a priority level of 3 during packet transmission
- The packet from 192.168.60.2 is classified as traffic F, and is set with a priority level of 2 during packet transmission
- The packet from 192.168.70.2 is classified as traffic G, and is set with a priority level of 1 during packet transmission
- The packet from 192.168.80.2 is classified as traffic H, and is set with a priority level of 0 during packet transmission
Scheduling method
These are the integrated SP and WRR settings to make.
| Queue ID | Method | Weight (%) |
|---|---|---|
| 7 | SP | - |
| 6 | SP | - |
| 5 | SP | - |
| 4 | WRR | 8 (40.0%) |
| 3 | WRR | 6 (30.0%) |
| 2 | WRR | 3 (15.0%) |
| 1 | WRR | 2 (10.0%) |
| 0 | WRR | 1 (5.0%) |
- This enables QoS, defines the access lists for traffic A–H, and defines the traffic classes that will be set in the LAN ports.
Yamaha(config)#qos enable … (enable QoS) Yamaha(config)#access-list 1 permit any 192.168.10.2 0.0.0.0 any … (traffic A) Yamaha(config)#class-map cmap-A Yamaha(config-cmap)#match access-list 1 Yamaha(config-cmap)#exit Yamaha(config)#access-list 2 permit any 192.168.20.2 0.0.0.0 any … (traffic B) Yamaha(config)#class-map cmap-B Yamaha(config-cmap)#match access-list 2 Yamaha(config-cmap)#exit Yamaha(config)#access-list 3 permit any 192.168.30.2 0.0.0.0 any … (traffic C) Yamaha(config)#class-map cmap-C Yamaha(config-cmap)#match access-list 3 Yamaha(config-cmap)#exit Yamaha(config)#access-list 4 permit any 192.168.40.2 0.0.0.0 any … (traffic D) Yamaha(config)#class-map cmap-D Yamaha(config-cmap)#match access-list 4 Yamaha(config-cmap)#exit Yamaha(config)#access-list 5 permit any 192.168.50.2 0.0.0.0 any … (traffic E) Yamaha(config)#class-map cmap-E Yamaha(config-cmap)#match access-list 5 Yamaha(config-cmap)#exit Yamaha(config)#access-list 6 permit any 192.168.60.2 0.0.0.0 any … (traffic F) Yamaha(config)#class-map cmap-F Yamaha(config-cmap)#match access-list 6 Yamaha(config-cmap)#exit Yamaha(config)#access-list 7 permit any 192.168.70.2 0.0.0.0 any … (traffic G) Yamaha(config)#class-map cmap-G Yamaha(config-cmap)#match access-list 7 Yamaha(config-cmap)#exit Yamaha(config)#access-list 8 permit any 192.168.80.2 0.0.0.0 any … (traffic H) Yamaha(config)#class-map cmap-H Yamaha(config-cmap)#match access-list 8 Yamaha(config-cmap)#exit
- This reverts the CoS - transmission queue ID conversion table to the default setting.
Yamaha(config)#no qos cos-queue 0 Yamaha(config)#no qos cos-queue 1 Yamaha(config)#no qos cos-queue 2 Yamaha(config)#no qos cos-queue 3 Yamaha(config)#no qos cos-queue 4 Yamaha(config)#no qos cos-queue 5 Yamaha(config)#no qos cos-queue 6 Yamaha(config)#no qos cos-queue 7
- This generates and applies the policy to LAN port #1 (port1.1).
This sets a transmission queue with CoS value 7 to traffic-A, and a transmission queue with CoS value 6 to traffic-B.
Yamaha(config)#policy-map pmap1 Yamaha(config-pmap)#class cmap-A Yamaha(config-pmap-c)#set cos-queue 7 … (Traffic-A is local priority order 7) Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#class cmap-B Yamaha(config-pmap-c)#set cos-queue 6 … (Traffic-B is local priority order 6) Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#exit Yamaha(config)#interface port1.1 … (LAN port #1) Yamaha(config-if)#service-policy input pmap1 … (apply policy to reception frames) Yamaha(config-if)# exit
- This generates and applies the policy to LAN port #2 (port1.2).
This sets a transmission queue with CoS value 5 to traffic-C, and a transmission queue with CoS value 4 to traffic-D.
Yamaha(config)#policy-map pmap2 Yamaha(config-pmap)#class cmap-C Yamaha(config-pmap-c)#set cos-queue 5 … (Traffic-C is local priority order 5) Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#class cmap-D Yamaha(config-pmap-c)#set cos-queue 4 … (Traffic-D is local priority order 4) Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#exit Yamaha(config)#interface port1.2 … (LAN port #2) Yamaha(config-if)#service-policy input pmap2 … (apply policy to reception frames) Yamaha(config-if)# exit
- This generates and applies the policy to LAN port #3 (port1.3).
This sets a transmission queue with CoS value 3 to traffic-E, and a transmission queue with CoS value 0 to traffic-F.
Yamaha(config)#policy-map pmap3 Yamaha(config-pmap)#class cmap-E Yamaha(config-pmap-c)#set cos-queue 3 … (Traffic-E is local priority order 3) Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#class cmap-F Yamaha(config-pmap-c)#set cos-queue 0 … (Traffic-F is local priority order 2) Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#exit Yamaha(config)#interface port1.3 … (LAN port #3) Yamaha(config-if)#service-policy input pmap3 … (apply policy to reception frames) Yamaha(config-if)# exit
- This generates and applies the policy to LAN port #4 (port1.4).
This sets a transmission queue with CoS value 2 to traffic-G, and a transmission queue with CoS value 1 to traffic-H.
Yamaha(config)#policy-map pmap4 Yamaha(config-pmap)#class cmap-G Yamaha(config-pmap-c)#set cos-queue 2 … (Traffic-G is local priority order 1) Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#class cmap-H Yamaha(config-pmap-c)#set cos-queue 1 … (Traffic-H is local priority order 0) Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#exit Yamaha(config)#interface port1.4 … (LAN port #4) Yamaha(config-if)#service-policy input pmap4 … (apply policy to reception frames) Yamaha(config-if)#exit
- This sets the scheduling method for the transmission queue.
As this queue IDs 5, 6, and 7 are the defaults, there is no need to make this setting, but it is listed for purposes of clarity.
Yamaha(config)#qos wrr-weight 0 1 … (transmission queue 0: WRR method, weighting 1) Yamaha(config)#qos wrr-weight 1 2 … (transmission queue 1: WRR method, weighting 2) Yamaha(config)#qos wrr-weight 2 3 … (transmission queue 2: WRR method, weighting 3) Yamaha(config)#qos wrr-weight 3 6 … (transmission queue 3: WRR method, weighting 6) Yamaha(config)#qos wrr-weight 4 8 … (transmission queue 4: WRR method, weighting 8) Yamaha(config)#no qos wrr-weight 5 … (transmission queue 5: SP method) Yamaha(config)#no qos wrr-weight 6 … (transmission queue 6: SP method) Yamaha(config)#no qos wrr-weight 7 … (transmission queue 7: SP method)
5.3 Priority control using port priority trust mode
The transmission queue is determined according to the port priority order that is specified for each reception port.
Priority control using port priority; setting example

- Set priority for each reception port
- Set LAN port#1 (port1.1) to priority order 6.
- Set LAN port#2 (port1.2) to priority order 4.
- Set LAN port#3 (port1.3) to priority order 2.
- Enable QoS and set the trust mode for the reception ports (LAN ports #1, #2, and #3).
Yamaha(config)#qos enable … (enable QoS) Yamaha(config)#interface port1.1 … (settings for LAN port #1) Yamaha(config-if)#qos trust port-priority … (change trust mode to “port priority”) Yamaha(config-if)#qos port-priority-queue 6 … (set port priority to 6) Yamaha(config-if)#exit Yamaha(config)#interface port1.2 … (settings for LAN port #2) Yamaha(config-if)#qos trust port-priority … (change trust mode to “port priority”) Yamaha(config-if)#qos port-priority-queue 4 … (set port priority to 4) Yamaha(config-if)#exit Yamaha(config)#interface port1.3 … (settings for LAN port #3) Yamaha(config-if)#qos trust port-priority … (change trust mode to “port priority”) Yamaha(config-if)#qos port-priority-queue 2 … (set port priority to 2) Yamaha(config-if)#exit
5.4 Bandwidth control using access list (twin rate / individual policer)
This example set bandwidth control by using the source IP address. A twin rate policer and an individual policer are used for metering.
Bandwidth control setting example

- Classification conditions and bandwidth limits for input frames
- Packets from 192.168.10.2 are classified as traffic A, and a reception rate (CIR) of 25 Mbps is guaranteed.
- Packets from 192.168.20.2 are classified as traffic B, and a reception rate (CIR) of 15 Mbps is guaranteed.
- Packets from 192.168.30.2 are classified as traffic C, and a reception rate (CIR) of 10 Mbps is guaranteed.
- Enable QoS, define the access lists for traffic A–C, and define the traffic classes that will be set for the LAN ports.
Yamaha(config)#qos enable … (enable QoS) Yamaha(config)#access-list 1 permit any 192.168.10.2 0.0.0.0 any … (traffic A) Yamaha(config)#class-map cmap-A Yamaha(config-cmap)#match access-list 1 Yamaha(config-cmap)#exit Yamaha(config)#access-list 2 permit any 192.168.20.2 0.0.0.0 any … (traffic B) Yamaha(config)#class-map cmap-B Yamaha(config-cmap)#match access-list 2 Yamaha(config-cmap)#exit Yamaha(config)#access-list 3 permit any 192.168.30.2 0.0.0.0 any … (traffic C) Yamaha(config)#class-map cmap-C Yamaha(config-cmap)#match access-list 3 Yamaha(config-cmap)#exit
- Generate and apply the policy to LAN port #1 (port1.1).
Individually specify metering for traffic A through traffic C.
In the twin rate policer, bandwidth for green can be allocated (guaranteed) by discarding yellow and red.
Yamaha(config)#policy-map pmap1 Yamaha(config-pmap)#class cmap-A … (Traffic-A metering settings) Yamaha(config-pmap-c)#police twin-rate 25000 25000 156 11 yellow-action drop red-action drop Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#class cmap-B … (Traffic-B metering settings) Yamaha(config-pmap-c)#police twin-rate 15000 15000 93 11 yellow-action drop red-action drop Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#class cmap-C … (Traffic-C metering settings) Yamaha(config-pmap-c)#police twin-rate 10000 10000 62 11 yellow-action drop red-action drop Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#exit Yamaha(config)#interface port1.1… (LAN port 1) Yamaha(config-if)#service-policy input pmap1 … (apply policy to reception frames) Yamaha(config-if)#exit
- The metering setting values are shown below.
- Metering type: Twin rate policer
- Traffic-A: CIR, PIR (25,000 kbps), CBS (156 kbyte), PBS (11 kbyte)
- Traffic-B: CIR, PIR (15,000 kbps), CBS (93 kbyte), PBS (11 kbyte)
- Traffic-C: CIR, PIR (10,000 kbps), CBS (62 kbyte), PBS (11 kbyte)
The following calculation is used to find the CBS, with a round-trip time of 0.05 sec.
CBS = CIR (bps) ÷ 8 (bit) × 0.05 (second)
- The metering setting values are shown below.
5.5 Bandwidth control using access list (single rate / aggregate policer)
This example set bandwidth control by using the source IP address. A single rate policer and an aggregate policer are used for metering.
Bandwidth control setting example

- Classification conditions and bandwidth limits for input frames
- Packets from 192.168.10.2 are classified as traffic A.
- Packets from 192.168.20.2 are classified as traffic B.
- Packets from 192.168.30.2 are classified as traffic C.
- The reception rate is limited to 25 Mbps for traffic A, B, and C collectively.
- Bandwidth class C “yellow” is remarked as DSCP=0, and sent with low priority.
- Enable QoS, define the access lists for traffic A–C, and define the traffic classes that will be set for the LAN ports.
Yamaha(config)#qos enable … (enable QoS) Yamaha(config)#access-list 1 permit any 192.168.10.2 0.0.0.0 any … (traffic A) Yamaha(config)#class-map cmap-A Yamaha(config-cmap)#match access-list 1 Yamaha(config-cmap)#exit Yamaha(config)#access-list 2 permit any 192.168.20.2 0.0.0.0 any … (traffic B) Yamaha(config)#class-map cmap-B Yamaha(config-cmap)#match access-list 2 Yamaha(config-cmap)#exit Yamaha(config)#access-list 3 permit any 192.168.30.2 0.0.0.0 any … (traffic C) Yamaha(config)#class-map cmap-C Yamaha(config-cmap)#match access-list 3 Yamaha(config-cmap)#exit
- Set the DSCP–transmission queue ID conversion table.
Assign the lowest-priority transmission queue to the DSCP value (0) used for remarking “yellow.”
Yamaha(config)#qos dscp-queue 0 0
- Create an aggregate policer.
Yamaha(config)#aggregate-police agp1 … (create aggregate policer) Yamaha(config-agg-policer)#police single-rate 25000 156 11 yellow-action remark red-action drop Yamaha(config-agg-policer)#remark-map yellow ip-dscp 0 Yamaha(config-agg-policer)#exit
- The aggregate policer’s metering setting values are as follows.
- Metering type: Single rate policer
- Remark “yellow” to DSCP value = 0
- CIR (25,000 kbps), CBS (156 kbyte), EBS (11 kbyte)
The following calculation is used to find the CBS, with a round-trip time of 0.05 sec.
CBS = CIR (bps) ÷ 8 (bit) × 0.05 (second)
- The aggregate policer’s metering setting values are as follows.
- Generate and apply the policy to LAN port #1 (port1.1).
Specify metering (aggregate policer) for the aggregated traffic of A through C.
Yamaha(config)#policy-map pmap1 Yamaha(config-pmap)#class cmap-A … (Traffic-A metering settings) Yamaha(config-pmap-c)#police-aggregate agp1 Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#class cmap-B … (Traffic-B metering settings) Yamaha(config-pmap-c)#police-aggregate agp1 Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#class cmap-C … (Traffic-C metering settings) Yamaha(config-pmap-c)#police-aggregate agp1 Yamaha(config-pmap-c)#exit Yamaha(config-pmap)#exit Yamaha(config)#interface port1.1… (LAN port 1) Yamaha(config-if)#service-policy input pmap1 … (apply policy to reception frames) Yamaha(config-if)#exit
6 Points of Caution
- LAN/SFP ports that use settings different from those shown below cannot be aggregated as a logical interface. Also, as for the settings shown below for a LAN/SFP port that belongs to a logical interface in startup config, the settings for the most recent port number will be applied to the logical interface.
- Trust mode
- Default CoS
- Port priority
- LAN/SFP ports on which policy maps have been applied cannot belong to a logical interface.
- Policy maps cannot be applied to a LAN/SFP port that belongs to a logical interface. However, if a LAN/SFP port that belongs to a logical interface in startup config has a policy map, the settings for the most recent port number will be applied to the logical interface.
- Conditions might not be determined correctly for fragment packets. Specifically, if layer 4 information (source port number, destination port number, and various TCP flags) is included in the conditions, correct information cannot be determined because the information is not included in the second and subsequent fragment packets. If there is a possibility of processing fragment packets, do not include layer 4 information in the conditions.
7 Related Documentation
None
Flow control
1 Function Overview
A switch initially stores received frames in memory and then performs relay processing.
When many frames are sent at the same time and relay processing cannot keep up (a congested state), exceeding the available memory capacity for storage, the frames to be relayed are discarded.
This product includes the following two functions to help mitigate such congestion.
- When ports are operating at full duplex: IEEE 802.3x flow control can be enabled.
- When ports are operating at half duplex: the back pressure function will always be enabled.
2 Definition of Terms Used
- Bit time
On a 10BASE network, the speed is 10Mbps, so 1 bit time = 100 nsec.
In the same way, the bit time on 100BASE is 10 nsec, and on 1000BASE is 1 nsec.
- Jam signals
In half-duplex communications, where data cannot be transmitted and received at the same time, there is a possibility of data collision.
The transmitting device monitors the possibility of data collision during transmission. When possible data collision is detected, the device stops transmitting and sends a jam signal. After the jam signal is sent, the device waits for a random interval before resuming transmission.
Although undefined in IEEE, jam signals that use a 32-digit alternating “1” and “0” bit sequence (such as “10101010101010101010101010101010”) are often used.
3 Function Details
3.1 IEEE 802.3x flow control
For full duplex communication, the MAC control protocol with IEEE802.3x option can be used.
The MAC control frame in the diagram below is used for flow control.
MAC control frame
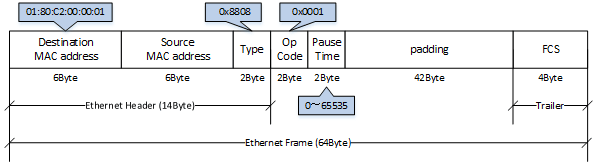
The following flow control operations are performed, based on the restriction start threshold and the restriction cancel threshold.
Flow control: processing flow
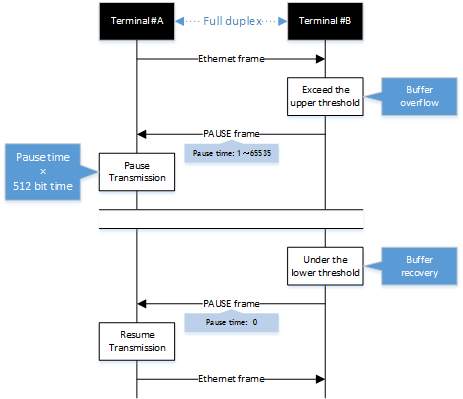
This product can be used for either transmitting or receiving MAC control frames. The operations for each are shown below.
- MAC control frame transmission processing
- Frames are stored in the receive buffer. When the number of frames exceeds the restriction start threshold, a PAUSE frame with a pause time of 65535 is sent.
- When the overflow in the receive buffer is resolved, and the number of frames falls below the restriction cancel threshold, a PAUSE frame with a pause time of 0 is sent.
- MAC control frame reception processing
- When a PAUSE frame with a pause time of 1–65535 is received, the transmission processing will be stopped if the corresponding bit time has elapsed, or if the a PAUSE frame with a pause time of 0 has been received.
Use the flowcontrol command to enable or disable the flow control (when transmitting/receiving MAC control frames).
This setting can be made for the system and for each transmitting/receiving LAN/SFP+ port, and is set to “disable” by factory default.
In order to enable flow control for an individual port, flow control must be enabled for the system.
When flow control is enabled for the system, the tail drop function is disabled.
If the Qos function is enabled, flow control cannot be enabled.
3.2 Back pressure
This product sends a jam signal whenever the receiving buffer of a LAN port is about to overflow.
With this, the sender waits for a random amount of time as per the CSMA/CD, and then sends the frames.
When the LAN port is operating at half duplex, the back pressure function will always be enabled.
Back pressure processing flow
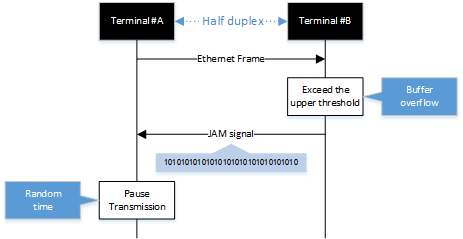
4 Related Commands
The related commands are shown below.
For details, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Set (system) flow control (IEEE 802.3x PAUSE send/receive) | flowcontrol |
| Set (interface) flow control (IEEE 802.3x PAUSE send/receive) | flowcontrol |
| Show flow control operating status | show flowcontrol |
5 Examples of Command Execution
- Enable flow control on LAN port #1.
After the function is enabled, check the flow control operating status.
Yamaha(config)#flowcontrol enable Yamaha(config)#interface port1.1 Yamaha(config-if)#flowcontrol both Yamaha(config-if)#end Yamaha#show flowcontrol port1.1 Port FlowControl RxPause TxPause --------- ----------- ------- ------- port1.1 Both 0 64
6 Points of Caution
None
7 Related Documentation
None
Storm control
1 Function Overview
This product provides a storm control function as a countermeasure against L2 loops and DoS attacks.
Broadcasts, multicasts, and unicast (dlf) frames that are addressed to an unknown host are monitored for each LAN/SFP+ port, and frames that exceed a preset threshold value are discarded.
This prevents such frames from taking up bandwidth on the LAN/SFP+ port.
Using this along with the proprietary loop detection and storm control functions enhances the precision of loop detection (avoiding such frames in the first place).
2 Definition of Terms Used
- Broadcast storm/multicast storm
This means a situation where frames addressed for broadcast or multicast are continuously forwarded.
In this situation, the switch floods all ports except for the reception port with the broadcast or multicast.
When this is received by another switch, all ports except for the reception port are flooded in the same way.
When this continues, it can lead to the following symptoms.
- Bandwidth is taken up by the broadcast storm/multicast storm
- The switch’s CPU load increases, making normal operations difficult
- Devices connected to the switch become unable to communicate
Unicast streamThis means a situation where frames addressed to an unknown unicast destination (dlf: Destination Lookup Failure) are continuously forwarded.
When the MAC address of the receiving device has not been registered in the ARP table, all ports on the switch except for the reception port are flooded.
This leads to the same symptoms occurring as with a broadcast storm or multicast storm.
3 Function Details
The operating specifications for storm control are shown below.
- The storm control function can be enabled for LAN/SFP+ ports.
The setting is disabled for all ports by default.
- Storm control on this product can be specified as a tolerance percentage for the bandwidth of the LAN/SFP+ ports that receive broadcast frames, multicast frames, and frames addressed to an unknown unicast destination.
(Control can be made in two decimal points. Specifying 100% is the same as disabling the storm function.)
The bandwidth tolerance is common for all frames, and the user can select the applicable frames.
The settings are made using the storm-control command.
- The following SYSLOG will be outputted at the time that storm control is enabled or disabled.
- When enabled: [ STORM]:inf: storm-control ENABLE (port:port1.1, type:B M U, level:50. 0%)
- When disabled: [ STORM]:inf: storm-control DISABLE (port:port1.1)
- When frames are received that exceeds the permitted bandwidth, the excessive frames are discarded.
- Use the show storm-control command to check the storm control information set for the LAN/SFP+ port.
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| Set storm control | storm-control |
| Show storm control reception upper limit | show storm-control |
5 Examples of Command Execution
In this example, the receivable L2 broadcast packets for LAN port 1 are restricted to a port bandwidth of 30%.
Storm control command setting: example
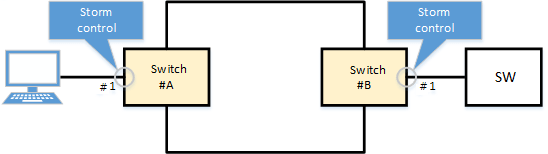
Yamaha(config)#interface port1.1 Yamaha(config-if)#storm-control broadcast level 30 … (Limit broadcast to 30% of the bandwidth) Yamaha(config-if)#end Yamaha# Yamaha#show storm-control Port BcastLevel McastLevel UcastLevel port1.1 30.00% 100.00% 100.00% port1.2 100.00% 100.00% 100.00% port1.3 100.00% 100.00% 100.00% port1.4 100.00% 100.00% 100.00% port1.5 100.00% 100.00% 100.00% port1.6 100.00% 100.00% 100.00% port1.7 100.00% 100.00% 100.00% port1.8 100.00% 100.00% 100.00%
6 Points of Caution
None
7 Related Documentation
- SWP2 Series Technical Data (Basic Functions)
- AP layer function
RADIUS Server
1 Function Overview
The RADIUS server function manages user information and certificates, and performs authentication based on information notified from the client.
By combining with MAC authentication, 802.1X authentication, and Web authentication of this device, the authentication function can be realized with this device alone.
Also, when authenticating with a device other than this device, this device can be operated as an authentication server.
When this device is running in Dante mode, the RADIUS server function cannot be used.
The basic performance of the RADIUS server function and the corresponding authentication method are as follows.
Basic performance
| Item | Performance |
|---|---|
| Number of RADIUS clients that can be registered | 100 |
| Number of users that can be registered | 2000 |
| Key strength | 2048 bit |
| Signature algorithm | SHA256 |
| Certificate Authority name (default value) | YAMAHA_SWITCH |
Supported authentication methods
| Authentication method | Application |
|---|---|
| PAP | MAC authentication |
| EAP-MD5 | IEEE802.1X authentication, MAC authentication, WEB authentication |
| EAP-TLS | IEEE802.1X authentication |
| EAP-TTLS | IEEE802.1X authentication |
| PEAP | IEEE802.1X authentication |
2 Definition of Terms Used
- PKI (Public Key Infrastructure)
Public key infrastructure. Includes digital certificates and certificate authorities (CAs) using public key cryptography.
- Certificate Authority (CA)
An organization that guarantees reliability. It is divided into a root Certificate Authority and an intermediate Certificate Authority.
It has a tree structure with the root Certificate Authority at the top and an intermediate Certificate Authority under it.- Intermediate Certificate Authority
Among Certificate Authorities (CAs), indicates a Certificate Authority whose reliability is guaranteed by a higher-level Certificate Authority (CA).
- Root Certificate Authority
Among Certificate Authorities (CA), indicates a Certificate Authority whose reliability is guaranteed by itself.
- Root Certificate Authority certificate
A public key certificate that has the same issuer and subject and has signed its own public key with its own private key. It is the root of a tree-structured certificate.
- Digital certificate
Data that certifies that the public key issued by the Certificate Authority is the genuine issuer’s public key.
When the issuer makes a certificate request to the Certificate Authority (CA) together with the public key, the Certificate Authority (CA) issues a digital certificate after scrutinizing and confirming it.- EAP-MD5 authentication method (Message digest algorithm 5)
This is an authentication method that uses a user name and password. Authenticates by exchanging an MD5 hash value instead of a plain text password.
- EAP-TLS authentication method (Transport Layer Security)
An authentication method used in IEEE 802.1X, a type of EAP implementation that authenticates by exchanging digital certificates after encrypting the transport layer between the user and the RADIUS server, instead of authenticating with a user ID and password. This is defined in RFC2716 and RFC5216.
- EAP-TTLS authentication method (Tunneled TLS)
An authentication method used in IEEE 802.1X, a type of EAP implementation that establishes a TLS communication channel using the server’s digital certificate and authenticates the user with a password within the encrypted channel. This is defined in RFC5281.
- PEAP authentication method (Protected EAP)
The operating principle is the same as EAP-TTLS (there is only a difference in the protocol in the encrypted tunnel). A TLS communication channel is established using the server’s digital certificate, and the user is authenticated with a password in the encrypted communication channel.
- It is trusted
A certificate indicating that the public key belongs to the issuer has been issued by a trusted third party.
- RADIUS server
The host device that provides the RADIUS server function, in this case, this device.
Authenticates connected users via a RADIUS server and manages authentication/authorization information such as user IDs, passwords, MAC addresses, and associated VLANs.- Server certificate
A certificate to state that the Certificate Authority (CA) has proved that the RADIUS server is trusted.
- RADIUS client
Also called a NAS or an authenticator, it relays between the user connected to the LAN/SFP port and the authentication server, and controls access to the LAN based on the success or failure of authentication.
- User
A device that connects to a RADIUS client and requests authentication, or a supplicant that is software.
It is the minimum unit for identifying the person to be authenticated. There are data required for authentication and authorization, such as a unique user ID and password.- Client certificate (user certificate)
This certificate proves that the user described above is trusted by the Certificate Authority (CA).
3 Function Details
3-1 Root Certificate Authority
To use the RADIUS server function, you must first create a root Certificate Authority.
The root Certificate Authority is used for issuing and managing digital certificates. It can be created with the crypto pki generate ca command.
The Certificate Authority name can be specified in the crypto pki generate ca command argument, if omitted it becomes YAMAHA_SWITCH.
The following certificates are issued and managed based on the root Certificate Authority.
All certificates have a key strength of 2048 bits and a signature algorithm of SHA256.
| Root Certificate Authority certificate | Proves that this device is a trusted root Certificate Authority. Issued at the same time that the root Certificate Authority is created. |
| Server certificate | Proves that this device is a trusted server. Issued at the same time that the root Certificate Authority is created. |
| Client (user) certificate | Proves that the user is trusted. |
| Client revocation certificate | Proves that the client certificate has been revoked. |
The root Certificate Authority is deleted or overwritten by the following operations.
- It is deleted when the cold start command is executed.
- It is deleted when the no crypto pki generate ca command is executed.
- It is deleted when the stack enable command is executed.
- It is deleted when the stack disable command is executed.
- It is deleted when the erase startup-config command is executed.
- It is overwritten when the crypto pki generate ca command is executed again.
- It is overwritten when the restore system command is executed.
It is necessary to keep the root Certificate Authority installed first consistent, so be careful not to delete it carelessly.
Also, please take measures to back up the file in advance, in case it is deleted.
Once the root CA is deleted, even if the same CA name is set, it will be a different CA from before.
If you delete the root Certificate Authority before backup, you cannot add or revoke the certificate after that. You will have to reissue all the certificates from the beginning.
When the root certificate authority is created by the crypto pki generate ca command, it is automatically saved in the internal area, so there is no need to execute the write command.
3-2 RADIUS client settings
Use the nas command to specify the RADIUS clients that are allowed to access the RADIUS server.
You can specify an individual IP address or network address, and up to 100 addresses can be set.
The settings of the RADIUS client set by the nas command are not displayed in the config by show running-config.
There is no need to execute the write command because it is automatically saved in a different area from the configuration, but it is necessary to execute the radius-server local refresh command to reflect it in the actual operation.
Use the show radius-server local nas command to confirm the settings.
3-3 User registration
User information for authentication is registered with the user command.
Up to 2000 user information can be registered.
Items that can be set with the user command are as follows.
| Type | Item | Summary/Remarks |
|---|---|---|
| Mandatory | User ID | ID for uniquely identifying user information |
| Password | Password used in combination with user ID If the client certificate is compressed, use this password for decompression. | |
| Option | User name | Any character string can be set for user identification. |
| MAC address | Compared when the RADIUS client notifies the Calling-Station-Id, and if it does not match, it is not authenticated. | |
| SSID | Compared when the RADIUS client notifies the Called-Station-Id, and if it does not match, it is not authenticated. | |
| Mail address | This is the address for sending the certificate by email. | |
| Authentication method | The default is EAP-TLS, so you must specify it if you want to use another authentication method. | |
| Period of certificate validity | This is valid only when the authentication method is EAP-TLS. If omitted, it will be 23:59:59 on December 31, 2037. | |
| Dynamic VLAN-ID | Specify when using the dynamic VLAN function. |
The user settings set by the user command are not displayed in the config by show running-config etc.
There is no need to execute the write command because it is automatically saved in a different area from the configuration, but it is necessary to execute the radius-server local refresh command to reflect it in the actual operation.
Use the show radius-server local user command to confirm the settings.
3-4 Restricting the authentication method
The authentication method can be restricted by the authentication command.
The authentication method is not restricted by default, but you can use it when you want to temporarily disable a specific authentication method.
3-5 Enabling the RADIUS server function
To enable the RADIUS server function, use the radius-server local enable command.
Set the RADIUS client and user information, and enable the RADIUS server function after the necessary preparations are completed.
3-6 Reflecting settings in operation
If you add/change/delete the settings related to the RADIUS server, execute the radius-server local refresh command to reflect them in actual operation.
The commands reflected in the actual operation by the radius-server local refresh command are as follows.
- authentication command
- nas command
- reauth interval command
- user command
When you add/change/delete settings related to the RADIUS server in Web GUI, processing equivalent to the radius-server local refresh command is automatically performed.
3-7 Issuing a client certificate
Use the certificate user command to issue a client certificate to a user who performs authentication using a certificate (a user whose authentication method is EAP-TLS with the user command).
Each user can hold up to two client certificates, and issuing a third client certificate will cause the older client certificate to expire.
If you specify an individual user ID with the certificate user command, a client certificate for the specified user is issued.
If you do not specify individual user IDs in the certificate user command, client certificates are issued for all users that meet any of the following conditions.
Conditions for batch issuance of client certificates
- Client certificate has never been issued
- The password or expiration date has changed since the client certificate was issued
It takes about 15 seconds to issue a client certificate. Although the certificate user command issues client certificates in the background, be aware that batch issuing client certificates for multiple users can be time consuming.
To cancel the issuance of a client certificate partway through, use the certificate abort command.
The method to export an issued client certificate is as follows.
Specify the mail option in the certificate user command
The client certificate can be sent to the specified email address at the same time that the client certificate is issued.
The client certificate is ZIP compressed and can be decompressed with the password of the user command.
For details on sending a client certificate by email, refer to 3-9 Sending a certificate by email.
certificate export mail command
The client certificate of any user or all users can be sent to the email address set by the user command.
The client certificate is ZIP compressed and can be decompressed with the password of the user command.
Access the device with Web GUI
The client certificate can be downloaded for any or all users.
Although it is ZIP compressed, no password is required for decompression.
3-8 Revoking a client certificate
To prevent authentication for the user who issued the client certificate, you must issue a revocation certificate.
When a revocation certificate is issued to any user, the revocation certificate is referenced in the authentication process and reflected in the authentication result.
Revocation certificates are issued by the following process.
Execute the certificate revoke id command
A revocation certificate is issued for the client certificate with the specified certificate ID.
Execute the certificate revoke user command
A revocation certificate is issued for all client certificates of the specified user.
Change the authentication method from EAP-TLS to other (PAP, PEAP, EAP-MD5, EAP-TTLS) with the user command
Revocation certificates are issued for all client certificates of the target user.
If you change the authentication method of the target user to EAP-TLS again, it will be subject to the batch issue of client certificates in 3-7.
Deletion of user command
Revocation certificates are issued for all client certificates of the target user.
If you register a user again with the same user ID as the target user, it will be subject to the batch issue of client certificates in 3-7.
Issue a third client certificate with the certificate user command
A revocation certificate is issued for the target user’s older client certificate.
Importing with 3-12 Import and export of user information
If a user is deleted due to an import, a revocation certificate is issued for all client certificates of the deleted user.
3-9 Sending a certificate by email
To use the client certificate email transmission described in 3-7 Issuing a client certificate, the following preparations are required in advance.
The settings described here are the minimum settings. Make the necessary settings according to the usage.
Set SMTP server
- 1-1 Specify the SMTP server with the mail server smtp host command.
Specify the mail template.
- 2-1 Specify the template ID with the mail template command and switch to the template setting mode.
- 2-2 Specify the mail server ID of the SMTP server set by the mail server smtp host command with the send server command.
- 2-3 Specify the sender email address with the send from command.
Specify the email template to use for sending certificate emails
- 3-1 Specify the ID of the mail template created above with the mail send certificate command.
The subject and body of the email are as follows. The format cannot be changed.
| Subject | Certification Publishment |
| Body | Certification is published. Name : [*NAME parameter of the user command] Account : [*USERID parameter of the user command] MAC address : XX:XX:XX:XX:XX:XX Expire : YYYY/MM/DD |
3-10 Checking settings and certificates
Checking the RADIUS client settings
Use the show radius-server local nas command.
Yamaha# show radius-server local nas 192.168.100.0/24 host key -------------------------------------------------------------------------------------------------------- 192.168.100.0/24 abcde
Checking the user settings
Use the show radius-server local user command.
Yamaha# show radius-server local user Total 1 userid name vlan mode -------------------------------------------------------------------------------- 00a0de000000 Yamaha 1 eap-md5
Yamaha# show radius-server local user detail 00a0de000000 Total 1 userid : 00a0de000000 password : secretpassword mode : eap-md5 name : Yamaha vlan : 1
Checking the status of client certificate issuance processing
Use the show radius-server local certificate status command.
Yamaha# show radius-server local certificate status certificate process: xxxx/ zzzz processing...
Check the list of client certificates
Use the show radius-server local certificate list command.
Yamaha# show radius-server local certificate list detail Taro userid certificate number enddate --------------------------------------------------------------------------------------------- Yamaha Yamaha-DF598EE9B44D22CC 2018/12/31 Yamaha-DF598EE9B44D22CD 2019/12/31Checking the revocation certificate
Use the show radius-server local certificate revoke command.
Yamaha# show radius-server local certificate revoke userid certificate number reason --------------------------------------------------------------------------------------------- Yamaha Yamaha-DF598EE9B44D22CC expired Yamaha Yamaha-DF598EE9B44D22CD revoked
3-11 Email notification of expiration of client certificate
An email notification can be sent before the client certificate expires.
The following preparations are required in advance to use advance email notification.
The settings described here are the minimum settings. Make the necessary settings according to the usage.
Set SMTP server
- 1-1 Specify the SMTP server with the mail server smtp host command.
Specify the mail template.
- 2-1 Specify the template ID with the mail template command and switch to the template setting mode.
- 2-2 Specify the mail server ID of the SMTP server set by the mail server smtp host command with the send server command.
- 2-3 Specify the sender email address with the send from command.
Specify the email template to use for the certificate expiration advance email notification
- 3-1 Specify the ID of the mail template created above with the mail send certificate-notify command.
Specifying when to send a certificate expiration advance email notification
- 4-1 Specify the number of days before the expiration date to send the email notification with the mail certificate expire-notify command.
Confirmation of the certificates that are subject to the client certificate expiration advance email notification is performed every day at 23:59:59.
The subject and body of the email are as follows. The format cannot be changed.
| Subject | Certification expiration |
| Body | Your certificate will expire in [Remaining days] days. Name : [*NAME parameter of the user command] Account : [*USERID parameter of the user command] MAC address : XX:XX:XX:XX:XX:XX Expire : YYYY/MM/DD |
3-12 Import and export of user information
- Export
User information can be exported as a CSV file from the Web GUI.
Users can be registered collectively by appending them to the exported CSV format file.
- Import
User information can be imported from the Web GUI.
When importing user information, client certificates can be batch issued to the users for whom the client certificate was issued as a result of the import.
When importing user information that includes a large number of users, it may take some time before it is reflected in actual operations.
3-13 Backing up and restoring all RADIUS server related information
This device can back up and restore all RADIUS server related information including the root Certificate Authority from Web GUI.
We recommend that you back up RADIUS server related information in case of device failure.
The backup file contains the setting information of the following three commands, but does not include the setting information related to the other RADIUS server functions. We recommend that you back up the configuration file along with the backup file.
- crypto pki generate ca command
- user command
- nas command
3-14 SYSLOG output information
The following information is output to the SYSLOG as a RADIUS server function.
The prefix is [RADIUSD].
| Type | Message | Description |
|---|---|---|
| INFO | RADIUS server started. | The RADIUS server function process has started. |
| INFO | RADIUS server stopped. | The RADIUS server function process has stopped. |
| INFO | Authentication succeeded.: [{ User ID }/<via Auth-Type = { Authentication method }>] (from client port { port number } cli { MAC address }) | User authentication succeeded. |
| INFO | Authentication failed.: [{ User ID }/<via Auth-Type = { Authentication method }>] (from client port { port number } cli { MAC address }) | User authentication failed. |
| INFO | MAC address is not allowed.User-ID: { User ID } MAC: { MAC address } | User authentication failed because the MAC address is incorrect. |
| INFO | Connected NAS is not allowed.IP: { IP address } | An authentication request was received from an unauthorized RADIUS client. |
4 Related Commands
The related commands are shown below.
For details on the commands, refer to the Command Reference.
List of related commands
| Operations | Operating commands |
|---|---|
| radius-server local enable | Setting of local RADIUS server function |
| radius-server local interface | Access interface settings |
| crypto pki generate ca | Generate root Certificate Authority |
| radius-server local-profile | RADIUS configuration mode |
| authentication | Authentication method setting |
| nas | RADIUS client (NAS) settings |
| user | Authentication user settings |
| reauth interval | Set reauthentication interval |
| radius-server local refresh | Set data reflected on local RADIUS server |
| certificate user | Issue client certificate |
| certificate abort | Suspend client certificate issuance |
| certificate revoke id | Revoke client certificate with the specified certificate ID |
| certificate revoke user | Revoke client certificate for specified user |
| certificate export mail | Export client certificate (send email) |
| show radius-server local nas | Show RADIUS client (NAS) |
| show radius-server local user | Show authentication user information |
| show radius-server local certificate status | Show issuance status of client certificate |
| show radius-server local certificate list | Show list of client certificates |
| show radius-server local certificate revoke | Show revocation list of client certificates |
5 Setting Examples
5-1 When using RADIUS server function and port authentication function simultaneously
Use a local RADIUS server to configure supplicants A, B, and C to authenticate with MAC, IEEE802.1X, and Web authentication, respectively.
- Enable the local RADIUS server with the switch and register the user.
Yamaha# configure terminal Yamaha(config)# crypto pki generate ca Generate CA? (y/n): y Finished Yamaha(config)# radius-server local-profile Yamaha(config-radius)# user 00a0de000001 00a0de000001 auth peap Yamaha(config-radius)# user 8021xuser 8021xpass auth peap Yamaha(config-radius)# user webuser webpass auth peap Yamaha(config-radius)# exit Yamaha(config)# radius-server local enable Yamaha(config)# exit Yamaha# radius-server local refresh
- Assign an IP address to VLAN #1 for web authentication
Yamaha# configure terminal Yamaha(config)# interface vlan1 Yamaha(config-if)# ip-address 192.168.100.240/24
- Enable MAC authentication, IEEE802.1X authentication, and Web authentication on LAN port #1.
Yamaha# configure terminal Yamaha(config)# aaa authentication auth-mac Yamaha(config)# auth-mac auth-user unformatted lower-case Yamaha(config)# aaa authentication dot1x Yamaha(config)# aaa authentication auth-web Yamaha(config)# interface port1.1 Yamaha(config-if)# auth host-mode multi-supplicant Yamaha(config-if)# auth-mac enable Yamaha(config-if)# dot1x port-control auto Yamaha(config-if)# auth-web enable
- Set the RADIUS server used for the authentication function.
Yamaha# configure terminal Yamaha(config)# radius-server host 127.0.0.1 key secret_local
6 Points of Caution
- When this device is running in Dante mode, the RADIUS server function cannot be used.
- In the RADIUS server function, the time of the internal clock of this device is used for processing such as authentication processing and certificate issuance.
Therefore, it is necessary to always keep the internal clock of this device at the correct time. Time synchronization with NTP server is recommended.
- It is necessary to keep the root Certificate Authority consistent from its creation, so be careful not to delete it carelessly.
If it is deleted, the issued client certificates cannot be used, and client certificates must be reissued for all users.
Also, almost all settings related to the RADIUS server function will be deleted.
- Even if you create a root Certificate Authority with the same name on a Yamaha switch of the same model number, that root Certificate Authority will be a different one.
Client certificates can only be used with Yamaha switch authentication that has the root Certificate Authority used at the time of generation.
To maintain the same root Certificate Authority in multiple devices, see 3-13 Backing up and restoring all RADIUS server related information.
- A certificate cannot be issued for an IPv6 link local address even if the connection is from a RADIUS client.
- There are restrictions on the characters that can be used in the RADIUS server function settings.
Item Restrictions Root Certificate Authority name (CA-NAME option of crypto pki generate ca command)
The following characters cannot be used among single-byte alphanumeric characters and single-byte symbols. ’\’ (backslash)
’/’
’[’
’]’
’?’
’ ’(space)
’"’(double quote)RADIUS client shared password (SECRET parameter of the nas command)
The following characters cannot be used among single-byte alphanumeric characters and single-byte symbols. ‘\’ (backslash)
’[’
’]’
’?’
’ ’(space)
’"’(double quote)%User ID of user information (USERID parameter of the user command)
When the authentication method is EAP-TLSThe following characters cannot be used among single-byte alphanumeric characters and single-byte symbols. ’\’ (backslash)
’/’
’[’
’]’
’:’
’’*’
’>’
’|’
’?’
’ ’ (space)
’"’ (double quote)User ID of user information (USERID parameter of the user command)
When the authentication method is PAP or PEAPThe following characters cannot be used among single-byte alphanumeric characters and single-byte symbols. ’\’ (backslash)
’[’
’]’
’?’
’ ’ (space)
’"’ (double quote)User information password (PASSWORD parameter of the user command)
The following characters cannot be used among single-byte alphanumeric characters and single-byte symbols. ’\’ (backslash)
’[’
’]’
’?’
’ ’ (space)
’"’ (double quote)User information name (NAME option of the user command)
The following characters cannot be used among single-byte alphanumeric characters and single-byte symbols. ’?’
’ ’ (space)
’"’ (double quote)
7 Related Documentation
- Interface control functions: Port authentication functions
- SWP2 Series Technical Data (Basic Functions)
- Other information
- SWP2 Series Technical Data (Basic Functions)
- Other information
- SNMP MIB Reference
SNMP MIB Reference
1 SNMP MIB List
The SNMP MIBs that are supported by this product are shown below.
1.1 MIB tree
The MIB tree for MIB groups that are supported by this product are shown below.
iso(1)
|
+--std(0)
| |
| +--iso8802(8802)
| |
| +--ieee802dot1(1)
| |
| +--ieee802dot1mibs(1)
| |
| +--ieee8021paeMIB(1) (port authentication information)
| |
| +--lldpMIB(2)
| |
| +--lldpObjects(1) (LLDP information)
|
+--member-body(2)
| |
| +--us(840)
| |
| +--802dot3(10006)
| |
| +--snmpmibs(300)
| |
| +--lagMIB(43) (LACP link aggregation information)
|
+--org(3)
|
+--dod(6)
| |
| +--internet(1)
| |
| +--mgmt(2)
| | |
| | +--mib-2(1)
| | |
| | +--system(1) (system information)
| | |
| | +--interfaces(2) (interface information)
| | |
| | +--at(3) (mapping information for network addresses and physical addresses)
| | |
| | +--rmon(16) (RMON information)
| | |
| | +--dot1dBridge(17) (dot1dBridge information)
| | |
| | +--ifMIB(31) (additional information for interface)
| | |
| | +--entityMIB(47) (entity information)
| |
| +--private(4)
| |
| +--enterprises(1)
| |
| +--yamaha(1182)
| |
| +--yamahaSW(3) (private MIB Yamaha switch information)
| |
| +--yamahaSWHardware(1) (hardware information)
| |
| +--yamahaSWFirmware(2) (firmware information)
| |
| +--yamahaSWL2ms(5) (L2MS information)
| |
| +--yamahaSWErrDisable(6) (error detection function information)
| |
| +--yamahaSWRmon(7) (RMON information)
| |
| +--yamahaSWTermMon(8) (terminal monitoring information)
| |
| +--yamahaSWBridge(9) (dot1dBridge information)
| |
| +--yamahaSWLoopDetect(11)(Loop detection information)
|
+--ieee(111)
|
+--standards-association-numbers-series-standards(2)
|
+--lan-man-stds(802)
|
+--ieee802dot1(1)
|
+--ieee802dot1mibs(1)
|
+--lldpV2MIB(13) (LLDP information)
1.2 Standard MIB list
The standard MIB that are supported are shown below.
MIB groups and overview
| MIB group | Summary |
|---|---|
| ieee8021paeMIB group | Port authentication information |
| lldpMIB group | LLDP information |
| lagMIB group | LACP link aggregation information |
| system group | System information |
| interface group | Interface information |
| at group | Mapping information for physical addresses and network addresses |
| rmon group | RMON information |
| dot1dBridge group | dot1dBridge information |
| ifMIB group | Additional information for interface |
| entityMIB group | entity information |
1.3 Private MIB list
Private MIBs that are supported are shown below.
All of this information is related to Yamaha switches.
MIB groups and overview
| MIB group | Summary |
|---|---|
| yamahaSWHardware group | Hardware information |
| yamahaSWFirmware group | Firmware information |
| yamahaSWL2ms group | L2MS information |
| yamahaSWErrDisable group | Error detection function information |
| yamahaSWRmon group | RMON information |
| yamahaSWTermMon group | Terminal monitoring information |
| yamahaSWBridge group | dot1dBridge information |
| yamahaSWLoopDetect group | Loop detection information |
1.4 Standard MIB trap list
The standard MIB traps that are supported are shown below.
Traps and overview
| Trap | Summary |
|---|---|
| coldStart | Power OFF/ON notification |
| warmStart | Reload notification |
| linkDown | Linkdown notification |
| linkUp | Linkup notification |
| authenticationFailure | Notification of failed authentication |
| risingAlarm | Notification that RMON upper threshold value has been exceeded |
| fallingAlarm | Notification that RMON lower threshold value has been exceeded |
| newRoot | Notification that new root for bridge has been detected |
| topologyChange | Notification when a change in topology has been detected |
1.5 Private MIB trap list
Private MIBs traps that are supported are shown below.
Traps and overview
| Trap | Summary |
|---|---|
| ysedTrap | Notification of detect/cancel for error detection function |
| ystmIfTermTrap | Notification of terminal monitoring (port) detection |
| ystmIpTermTrap | Notification of terminal monitoring (IP address) detection |
| ysldPortDetectLoopTrap | Loop detection notification |
| ysldPortResolveLoopTrap | Loop detection cancellation notification |
2 Definition of Terms Used
- MIB access classification
The MIB access used in subsequent explanations is described below.
MIB access classification
Access name Description R/O Access to the MIB is read-only R/W Access to the MIB is read-write R/NW Although the access to the MIB is read-write as per the standards, it is read-only on this product R/C Access to the MIB is read-create R/NC Although the access to the MIB is read-create as per the standards, it is read-only on this product N/A The MIB cannot be retrieved
Note: May be used as additional information for traps (variable-bindings)
3 Obtaining a private MIB
Private MIB files may be acquired from here.
4 Standard MIBs
Standard MIBs that are supported by this product are shown below.
4.1 ieee8021paeMIB group
This MIB is related to port authentication information.
The syntax defined in the ieee8021paeMIB group is shown below.
Syntax defined in the ieee8021paeMIB group
| Syntax | Definition |
|---|---|
| PaeControlledDirections | INTEGER ・both(0) ・in(1) |
| PaeControlledPortStatus | INTEGER ・authorized(1) ・unauthorized(2) |
| PaeControlledPortControl | INTEGER ・forceUnauthorized(1) ・auto(2) ・forceAuthorized(3) |
The ieee8021paeMIB group is divided into subgroups such as those shown below.
ieee8021paeMIB(1)
|
+--paeMIBObjects(1)
|
+--dot1xPaeSystem(1)
|
+--dot1xPaeAuthenticator(2)
dot1xPaeSystem group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot1xPaeSystemAuthControl | 1.0.8802.1.1.1.1.1.1 | R/NW | INTEGER ・enabled(1) ・disabled(2) | Setting value for authentication function at the system level | ||
| dot1xPaePortTable | 1.0.8802.1.1.1.1.1.2 | N/A | System-level information table | |||
| dot1xPaePortEntry | 1.0.8802.1.1.1.1.1.2.1 | N/A | INDEX ・dot1xPaePortNumber | |||
| dot1xPaePortNumber | 1.0.8802.1.1.1.1.1.2.1.1 | N/A | InterfaceIndex | Port numbers for which the authentication function is enabled | ||
| dot1xPaePortProtocolVersion | 1.0.8802.1.1.1.1.1.2.1.2 | R/O | Unsigned32 | Protocol version (2, fixed) | ||
| dot1xPaePortCapabilities | 1.0.8802.1.1.1.1.1.2.1.3 | R/O | BITS | PAE functions supported by the port (0, fixed) | ||
| dot1xPaePortInitialize | 1.0.8802.1.1.1.1.1.2.1.4 | R/NW | TruthValue | Initialization control for ports (2, fixed) | ||
| dot1xPaePortReauthenticate | 1.0.8802.1.1.1.1.1.2.1.5 | R/NW | TruthValue | Re-authentication control for ports (2, fixed) | ||
dot1xPaeAuthenticator group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot1xAuthConfigTable | 1.0.8802.1.1.1.1.2.1 | N/A | Structural object table for Authenticator PAE for each port | |||
| dot1xAuthConfigEntry | 1.0.8802.1.1.1.1.2.1.1 | N/A | INDEX ・dot1xPaePortNumber | |||
| dot1xAuthAdminControlledDirections | 1.0.8802.1.1.1.1.2.1.1.3 | R/NW | PaeControlledDirections | Packet forwarding operation in an unauthenticated state, controlled by management | ||
| dot1xAuthOperControlledDirections | 1.0.8802.1.1.1.1.2.1.1.4 | R/O | PaeControlledDirections | Packet forwarding operation in an unauthenticated state, controlled by operation | ||
| dot1xAuthAuthControlledPortStatus | 1.0.8802.1.1.1.1.2.1.1.5 | R/O | PaeControlledPortStatus | Port authentication status | ||
| dot1xAuthAuthControlledPortControl | 1.0.8802.1.1.1.1.2.1.1.6 | R/NW | PaeControlledPortControl | Setting value for 802.1X authentication operating mode | ||
| dot1xAuthQuietPeriod | 1.0.8802.1.1.1.1.2.1.1.7 | R/NW | Unsigned32 | Setting value for authentication restriction period | ||
| dot1xAuthSuppTimeout | 1.0.8802.1.1.1.1.2.1.1.9 | R/NW | Unsigned32 | Response wait time setting value for the supplicant | ||
| dot1xAuthServerTimeout | 1.0.8802.1.1.1.1.2.1.1.10 | R/NW | Unsigned32 | Setting value for server response wait time | ||
| dot1xAuthMaxReq | 1.0.8802.1.1.1.1.2.1.1.11 | R/NW | Unsigned32 | Setting value for number of times EAPOL packets are retransmitted | ||
| dot1xAuthReAuthPeriod | 1.0.8802.1.1.1.1.2.1.1.12 | R/NW | Unsigned32 | Setting value for reauthentication interval | ||
| dot1xAuthReAuthEnabled | 1.0.8802.1.1.1.1.2.1.1.13 | R/NW | TruthValue | Setting value for reauthentication function | ||
| dot1xAuthKeyTxEnabled | 1.0.8802.1.1.1.1.2.1.1.14 | R/NW | TruthValue | Constant value (2, fixed) used by Authenticator PAE state machine | ||
| dot1xAuthStatsTable | 1.0.8802.1.1.1.1.2.2 | N/A | Statistical data object table for Authenticator PAE associated with each port | |||
| dot1xAuthStatsEntry | 1.0.8802.1.1.1.1.2.2.1 | N/A | INDEX ・dot1xPaePortNumber | |||
| dot1xAuthEapolFramesRx | 1.0.8802.1.1.1.1.2.2.1.1 | R/O | Counter32 | No. of EAPOL frames that are received, all valid types | ||
| dot1xAuthEapolFramesTx | 1.0.8802.1.1.1.1.2.2.1.2 | R/O | Counter32 | No. of EAPOL frames that are transmitted, all types | ||
| dot1xAuthEapolStartFramesRx | 1.0.8802.1.1.1.1.2.2.1.3 | R/O | Counter32 | No. of EAPOL Start frames received | ||
| dot1xAuthEapolLogoffFramesRx | 1.0.8802.1.1.1.1.2.2.1.4 | R/O | Counter32 | No. of EAPOL Logoff frames received | ||
| dot1xAuthEapolRespIdFramesRx | 1.0.8802.1.1.1.1.2.2.1.5 | R/O | Counter32 | No. of EAP Response/Identity frames received | ||
| dot1xAuthEapolRespFramesRx | 1.0.8802.1.1.1.1.2.2.1.6 | R/O | Counter32 | No. of valid EAP Response frames, excepting EAP Response/Identity frames received | ||
| dot1xAuthEapolReqIdFramesTx | 1.0.8802.1.1.1.1.2.2.1.7 | R/O | Counter32 | No. of EAP Request/Identity frames transmitted | ||
| dot1xAuthEapolReqFramesTx | 1.0.8802.1.1.1.1.2.2.1.8 | R/O | Counter32 | No. of EAP Request frames, excepting EAP Request/Identity frames transmitted | ||
| dot1xAuthInvalidEapolFramesRx | 1.0.8802.1.1.1.1.2.2.1.9 | R/O | Counter32 | No. of frames within received EAPOL frames, for which frame type has not been approved | ||
| dot1xAuthEapLengthErrorFramesRx | 1.0.8802.1.1.1.1.2.2.1.10 | R/O | Counter32 | No. of received EAPOL frames, for which the packet body length is invalid | ||
| dot1xAuthLastEapolFrameVersion | 1.0.8802.1.1.1.1.2.2.1.11 | R/O | Unsigned32 | Protocol version numbers for most recently received EAPOL frames | ||
| dot1xAuthLastEapolFrameSource | 1.0.8802.1.1.1.1.2.2.1.12 | R/O | MacAddress | Source MAC address of EAPOL frames most recently received | ||
4.2 lldpMIB group
MIB related to LLDP information.
This product handles the following two systems of MIB groups as MIBs related to LLDP.
- lldpMIB group (MIB defined in IEEE Std 802.1AB-2005)
- lldpV2MIB group (MIB defined in IEEE Std 802.1AB-2009)
Both are MIBs that handle LLDP in the same way, but both MIBs are supported for compatibility with other models.
Some MIBs refer to the same value.
The syntax defined in the lldpMIB group is shown below.Syntax defined in the lldpMIB group
| Syntax | Definition |
|---|---|
| LldpChassisIdSubtype | INTEGER ・chassisComponent(1) ・interfaceAlias(2) ・portComponent(3) ・macAddress(4) ・networkAddress(5) ・interfaceName(6) ・local(7) |
| LldpChassisId | OCTET STRING (SIZE (1..255)) |
| LldpPortIdSubtype | INTEGER ・interfaceAlias(1) ・portComponent(2) ・macAddress(3) ・networkAddress(4) ・interfaceName(5) ・agentCircuitId(6) ・local(7) |
| LldpPortId | OCTET STRING (SIZE (1..255)) |
| LldpSystemCapabilitiesMap | BITS ・other(0) ・repeater(1) ・bridge(2) ・wlanAccessPoint(3) ・router(4) ・telephone(5) ・docsisCableDevice(6) ・stationOnly(7) |
| LldpPortNumber | INTEGER32 (1..4096) |
| LldpXMedDeviceClass | INTEGER ・notDefined(0) ・endpointClass1(1) ・endpointClass2(2) ・endpointClass3(3) ・networkConnectivity(4) |
| LldpXMedCapabilities | INTEGER ・capabilities(0) ・networkPolicy(1) ・location(2) ・extendedPSE(3) ・extendedPD(4) ・inventory(5) |
| LldpManAddress | OCTET STRING (SIZE (1..31)) |
| LldpManAddrIfSubtype | INTEGER ・unknown(1) ・ifIndex(2) ・systemPortNumber(3) |
The lldpMIB group is divided as follows.
lldpObjects(1)
|
+--lldpConfiguration(1)
|
+--lldpStatistics(2)
|
+--lldpLocalSystemData(3)
|
+--lldpRemoteSystemsData(4)
|
+--lldpExtensions(5)
|
+--lldpXMedMIB(4795)
|
+--lldpXMedObjects(1)
|
+--lldpXMedConfig(1)
|
+--lldpXMedRemoteData(3)lldpConfiguration group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpPortConfigTable | 1.0.8802.1.1.2.1.1.6 | N/A | Table of information for each port | |||
| lldpPortConfigEntry | 1.0.8802.1.1.2.1.1.6.1 | N/A | INDEX • lldpPortConfigPortNum | |||
| lldpPortConfigAdminStatus | 1.0.8802.1.1.2.1.1.6.2 | R/O | INTEGER ・txOnly(1) ・rxOnly(2) ・txAndRx(3) ・disabled(4) | LLDP transmission/reception status | ||
| lldpPortConfigNotificationEnable | 1.0.8802.1.1.2.1.1.6.3 | R/O | TruthVal | LLDP notification status | ||
| lldpPortConfigTLVsTxEnable | 1.0.8802.1.1.2.1.1.6.4 | R/O | BITS ・portDesc(0) ・sysName(1) ・sysDesc(2) ・sysCap(3) | Basic management TLV transmission item | ||
lldpStatistics group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpStatsRemTablesLastChangeTime | 1.0.8802.1.1.2.1.2.1 | R/O | TimeTicks | Time from system initialization to remote data update | ||
| lldpStatsRemTablesInserts | 1.0.8802.1.1.2.1.2.2 | R/O | INTEGER (0..4294967295) | Total number of entries added to remote device management table | ||
| lldpStatsRemTablesDeletes | 1.0.8802.1.1.2.1.2.3 | R/O | INTEGER (0..4294967295) | Total number of entries deleted from remote device management table | ||
| lldpStatsRemTablesDrops | 1.0.8802.1.1.2.1.2.4 | R/O | INTEGER (0..4294967295) | Total number of entries that could not be set to remote device management table | ||
| lldpStatsRemTablesAgeouts | 1.0.8802.1.1.2.1.2.5 | R/O | INTEGER (0..4294967295) | Total number of entries that exceeded TTL time (aged out) and were deleted from remote device management table | ||
| lldpStatsTxPortTable | 1.0.8802.1.1.2.1.2.6 | N/A | Table of information for each port | |||
| lldpStatsTxPortEntry | 1.0.8802.1.1.2.1.2.6.1 | N/A | INDEX • lldpStatsTxPortNum | |||
| lldpStatsTxPortNum | 1.0.8802.1.1.2.1.2.6.1.1 | N/A | LldpPortNumber | |||
| lldpStatsTxPortFramesTotal | 1.0.8802.1.1.2.1.2.6.1.2 | R/O | INTEGER (0..4294967295) | Total number of LLDP transmission frames | ||
| lldpStatsRxPortTable | 1.0.8802.1.1.2.1.2.7 | N/A | Table of information for each port | |||
| lldpStatsRxPortEntry | 1.0.8802.1.1.2.1.2.7.1 | N/A | INDEX ・lldpStatsRxPortNum | |||
| lldpStatsRxPortNum | 1.0.8802.1.1.2.1.2.7.1.1 | N/A | LldpPortNumber | |||
| lldpStatsRxPortFramesDiscardedTotal | 1.0.8802.1.1.2.1.2.7.1.2 | R/O | INTEGER (0..4294967295) | Number of discarded LLDP frames | ||
| lldpStatsRxPortFramesErrors | 1.0.8802.1.1.2.1.2.7.1.3 | R/O | INTEGER (0..4294967295) | Number of error frames received | ||
| lldpStatsRxPortFramesTotal | 1.0.8802.1.1.2.1.2.7.1.4 | R/O | INTEGER (0..4294967295) | Number of LLDP frames received | ||
| lldpStatsRxPortTLVsDiscardedTotal | 1.0.8802.1.1.2.1.2.7.1.5 | R/O | INTEGER (0..4294967295) | Number of TLVs discarded | ||
| lldpStatsRxPortTLVsUnrecognizedTotal | 1.0.8802.1.1.2.1.2.7.1.6 | R/O | INTEGER (0..4294967295) | Number of unrecognized TLVs received | ||
| lldpStatsRxPortAgeoutsTotal | 1.0.8802.1.1.2.1.2.7.1.7 | R/O | INTEGER (0..4294967295) | Number of entries aged out | ||
lldpLocalSystemData group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpLocChassisIdSubtype | 1.0.8802.1.1.2.1.3.1 | R/O | LldpChassisIdSubtype | Subtype of chassis ID | ||
| lldpLocChassisId | 1.0.8802.1.1.2.1.3.2 | R/O | LldpChassisId | Chassis ID | ||
| lldpLocSysName | 1.0.8802.1.1.2.1.3.3 | R/O | SnmpAdminString (SIZE (0..255)) | System name | ||
| lldpLocSysDesc | 1.0.8802.1.1.2.1.3.4 | R/O | SnmpAdminString (SIZE (0..255)) | System description | ||
| lldpLocSysCapSupported | 1.0.8802.1.1.2.1.3.5 | R/O | LldpSystemCapabilitiesMap | Functions supported by the system | ||
| lldpLocSysCapEnabled | 1.0.8802.1.1.2.1.3.6 | R/O | LldpSystemCapabilitiesMap | Functions enabled by the system | ||
| lldpLocPortTable | 1.0.8802.1.1.2.1.3.7 | N/A | Table of information for each port | |||
| lldpLocPortEntry | 1.0.8802.1.1.2.1.3.7.1 | N/A | INDEX • lldpLocPortNum | |||
| lldpLocPortNum | 1.0.8802.1.1.2.1.3.7.1.1 | N/A | LldpPortNumber | |||
| lldpLocPortIdSubtype | 1.0.8802.1.1.2.1.3.7.1.2 | R/O | LldpPortIdSubtype | Port ID subtype | ||
| lldpLocPortId | 1.0.8802.1.1.2.1.3.7.1.3 | R/O | OCTET STRING (SIZE (1..255)) | Port ID | ||
| lldpLocPortDesc | 1.0.8802.1.1.2.1.3.7.1.4 | R/O | SnmpAdminString (SIZE (0..255)) | Port description | ||
| lldpLocManAddrTable | 1.0.8802.1.1.2.1.3.8 | N/A | Table of local system management addresses | |||
| lldpLocManAddrEntry | 1.0.8802.1.1.2.1.3.8.1 | N/A | INDEX ・lldpV2LocManAddrSubtype ・lldpLocManAddr | |||
| lldpLocManAddrSubtype | 1.0.8802.1.1.2.1.3.8.1.1 | N/A | AddressFamilyNumbers | Sub-type for management address | ||
| lldpLocManAddr | 1.0.8802.1.1.2.1.3.8.1.2 | N/A | LldpManAddress | management address | ||
| lldpLocManAddrLen | 1.0.8802.1.1.2.1.3.8.1.3 | R/O | Integer32 | management address length | ||
| lldpLocManAddrIfSubtype | 1.0.8802.1.1.2.1.3.8.1.4 | R/O | LldpManAddrIfSubtype | Interface sub-type | ||
| lldpLocManAddrIfId | 1.0.8802.1.1.2.1.3.8.1.5 | R/O | Integer32 | Interface ID | ||
lldpRemoteSystemsData group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpRemTable | 1.0.8802.1.1.2.1.4.1 | N/A | Table of information for each port | |||
| lldpRemEntry | 1.0.8802.1.1.2.1.4.1.1 | N/A | INDEX ・lldpRemTimeMark ・lldpRemLocalPortNum ・lldpRemIndex | |||
| lldpRemTimeMark | 1.0.8802.1.1.2.1.4.1.1.1 | N/A | TimeFilter | |||
| lldpRemLocalPortNum | 1.0.8802.1.1.2.1.4.1.1.2 | N/A | LldpPortNumber | |||
| lldpRemIndex | 1.0.8802.1.1.2.1.4.1.1.3 | N/A | INTEGER32 (1..2147483647) | |||
| lldpRemChassisIdSubtype | 1.0.8802.1.1.2.1.4.1.1.4 | R/O | LldpChassisIdSubtype | Subtype of the chassis ID of remote device | ||
| lldpRemChassisId | 1.0.8802.1.1.2.1.4.1.1.5 | R/O | SnmpAdminString (SIZE (0..255)) | Chassis ID of remote device | ||
| lldpRemPortIdSubtype | 1.0.8802.1.1.2.1.4.1.1.6 | R/O | LldpPortIdSubtype | Subtype of port ID of the remote device | ||
| lldpRemPortId | 1.0.8802.1.1.2.1.4.1.1.7 | R/O | OCTET STRING (SIZE (1..255)) | Port ID of remote device | ||
| lldpRemPortDesc | 1.0.8802.1.1.2.1.4.1.1.8 | R/O | SnmpAdminString (SIZE (0..255)) | Port description of remote device | ||
| lldpRemSysName | 1.0.8802.1.1.2.1.4.1.1.9 | R/O | SnmpAdminString (SIZE (0..255)) | System name of remote device | ||
| lldpRemSysDesc | 1.0.8802.1.1.2.1.4.1.1.10 | R/O | SnmpAdminString (SIZE (0..255)) | System description of remote device | ||
| lldpRemSysCapSupported | 1.0.8802.1.1.2.1.4.1.1.11 | R/O | LldpSystemCapabilitiesMap | Functions supported by the remote device system | ||
| lldpRemSysCapEnabled | 1.0.8802.1.1.2.1.4.1.1.12 | R/O | LldpSystemCapabilitiesMap | Functions enabled in the remote device system | ||
| lldpRemManAddrTable | 1.0.8802.1.1.2.1.4.2 | N/A | ||||
| lldpRemManAddrEntry | 1.0.8802.1.1.2.1.4.2.1 | N/A | INDEX ・lldpRemTimeMark ・lldpRemLocalPortNum ・lldpRemIndex ・lldpRemManAddrSubtype ・lldpRemManAddr | |||
| lldpRemManAddrSubtype | 1.0.8802.1.1.2.1.4.2.1.1 | N/A | LldpPortNumber | |||
| lldpRemManAddr | 1.0.8802.1.1.2.1.4.2.1.2 | N/A | ||||
| lldpRemManAddrIfSubtype | 1.0.8802.1.1.2.1.4.2.1.3 | R/O | INTEGER ・unknown(1) ・ifIndex(2) ・systemPortNumber(3) | Subtype of the remote device interface | ||
| lldpRemManAddrIfId | 1.0.8802.1.1.2.1.4.2.1.4 | R/O | LldpChassisIdSubtype | Interface ID of the remote device | ||
| lldpRemManAddrOID | 1.0.8802.1.1.2.1.4.2.1.5 | R/O | LldpChassisIdSubtype | OID of the management address of the remote device | ||
| lldpRemUnknownTLVTable | 1.0.8802.1.1.2.1.4.3 | N/A | ||||
| lldpRemUnknownTLVEntry | 1.0.8802.1.1.2.1.4.3.1 | N/A | INDEX ・lldpRemTimeMark ・lldpRemLocalPortNum ・lldpRemIndex ・lldpRemUnknownTLVType | |||
| lldpRemUnknownTLVType | 1.0.8802.1.1.2.1.4.3.1.1 | N/A | LldpPortNumber | |||
| lldpRemUnknownTLVInfo | 1.0.8802.1.1.2.1.4.3.1.2 | R/O | LldpPortNumber | Latest undefined TLV information of the remote device | ||
| lldpRemOrgDefInfoTable | 1.0.8802.1.1.2.1.4.4 | N/A | ||||
| lldpRemOrgDefInfoEntry | 1.0.8802.1.1.2.1.4.4.1 | N/A | INDEX ・lldpRemTimeMark ・lldpRemLocalPortNum ・lldpRemIndex ・lldpRemOrgDefInfoOUI ・lldpRemOrgDefInfoSubtype, lldpRemOrgDefInfoIndex | |||
| lldpRemOrgDefInfoOUI | 1.0.8802.1.1.2.1.4.4.1.1 | N/A | ||||
| lldpRemOrgDefInfoSubtype | 1.0.8802.1.1.2.1.4.3.1.2 | N/A | ||||
| lldpRemOrgDefInfoIndex | 1.0.8802.1.1.2.1.4.3.1.3 | N/A | ||||
| lldpRemOrgDefInfo | 1.0.8802.1.1.2.1.4.3.1.4 | R/O | OCTET STRING (SIZE (0..507)) | Undefined TLV information list of the remote device (IEEE802.1, IEEE802.3 only) | ||
lldpXMedConfig group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpXMedLocDeviceClass | 1.0.8802.1.1.2.1.5.4795.1.1.1 | R/O | LldpXMedDeviceClass | Device class of this unit itself | ||
| lldpXMedPortConfigTable | 1.0.8802.1.1.2.1.5.4795.1.1.2 | N/A | Table of information for each port | |||
| lldpXMedPortConfigEntry | 1.0.8802.1.1.2.1.5.4795.1.1.2.1 | N/A | INDEX • Port number | |||
| lldpXMedPortCapSupported | 1.0.8802.1.1.2.1.5.4795.1.1.2.1.1 | R/O | LldpXMedCapabilities | Sent TLV items supported by LLDP-MED | ||
| lldpXMedPortConfigTLVsTxEnable | 1.0.8802.1.1.2.1.5.4795.1.1.2.1.2 | R/O | LldpXMedCapabilities | TLV items sent as LLDP-MED | ||
| lldpXMedPortConfigNotifEnable | 1.0.8802.1.1.2.1.5.4795.1.1.2.1.3 | R/O | TruthValue | LLDP-MED notification status | ||
| lldpXMedFastStartRepeatCount | 1.0.8802.1.1.2.1.5.4795.1.1.3 | R/O | Unsigned32 (1..10) | LLDP-MED high-speed transmission count Write processing is not supported | ||
lldpXMedRemoteData group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpXMedRemXPoETable | 1.0.8802.1.1.2.1.5.4795.1.3.5 | N/A | Remote device information table | |||
| lldpXMedRemXPoEEntry | 1.0.8802.1.1.2.1.5.4795.1.3.5.1 | N/A | INDEX ・lldpRemTimeMark ・lldpRemLocalPortNum ・lldpRemIndex | |||
| lldpXMedRemXPoEDeviceType | 1.0.8802.1.1.2.1.5.4795.1.3.5.1.1 | R/O | INTEGER ・unknown(1) ・pseDevice(2) ・pdDevice(3) ・none(4) | Whether the remote device is PSE or PD | ||
| lldpXMedRemXPoEPSETable | 1.0.8802.1.1.2.1.5.4795.1.3.6 | N/A | PSE information table of remote device | |||
| lldpXMedRemXPoEPSEEntry | 1.0.8802.1.1.2.1.5.4795.1.3.6.1 | N/A | INDEX ・lldpRemTimeMark ・lldpRemLocalPortNum ・lldpRemIndex | |||
| lldpXMedRemXPoEPSEPowerAv | 1.0.8802.1.1.2.1.5.4795.1.3.6.1.1 | R/O | Integer(0..1023) | Required power of remote device (0.1w unit) | ||
| lldpXMedRemXPoEPSEPowerSource | 1.0.8802.1.1.2.1.5.4795.1.3.6.1.2 | R/O | INTEGER ・unknown(1) ・fromPSE(2) ・local(3) ・localAndPSE(4) | Power supply type of remote device | ||
| lldpXMedRemXPoEPDPowerPriority | 1.0.8802.1.1.2.1.5.4795.1.3.6.1.3 | R/O | INTEGER ・unknown(1) ・critical(2) ・high(3) ・low(4) | Power supply priority of remote device | ||
| lldpXMedRemXPoEPDTable | 1.0.8802.1.1.2.1.5.4795.1.3.7 | N/A | PSE information table of remote device | |||
| lldpXMedRemXPoEPDEntry | 1.0.8802.1.1.2.1.5.4795.1.3.7.1 | N/A | INDEX ・lldpRemTimeMark ・lldpRemLocalPortNum ・lldpRemIndex | |||
| lldpXMedRemXPoEPDPowerReq | 1.0.8802.1.1.2.1.5.4795.1.3.7.1.1 | R/O | Integer(0..1023) | Required power of remote device (0.1w unit) | ||
| lldpXMedRemXPoEPDPowerSource | 1.0.8802.1.1.2.1.5.4795.1.3.7.1.2 | R/O | INTEGER ・unknown(1) ・fromPSE(2) ・local(3) ・localAndPSE(4) | Power supply type of remote device | ||
| lldpXMedRemXPoEPDPowerPriority | 1.0.8802.1.1.2.1.5.4795.1.3.7.1.3 | R/O | INTEGER ・unknown(1) ・critical(2) ・high(3) ・low(4) | Power supply priority of remote device | ||
The lldpV2MIB group is divided as follows.
lldpV2MIB(13)
|
+--lldpV2Objects(1)
|
+--lldpV2Configuration(1)
|
+--lldpV2Statistics(2)
|
+--lldpV2LocalSystemData(3)
|
+--lldpV2RemoteSystemsData(4)lldpV2Configuration group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpV2PortConfigTable | 1.3.111.2.802.1.1.13.1.1.8 | N/A | Table for managing transmission information for each port | |||
| lldpV2PortConfigEntry | 1.3.111.2.802.1.1.13.1.1.8.1 | N/A | INDEX ・lldpV2PortConfigIfIndex ・lldpV2PortConfigDestAddressIndex | |||
| lldpV2PortConfigIfIndex | 1.3.111.2.802.1.1.13.1.1.8.1.1 | N/A | InterfaceIndex | Index by port | ||
| lldpV2PortConfigDestAddressIndex | 1.3.111.2.802.1.1.13.1.1.8.1.2 | N/A | LldpV2DestAddressTableIndex | Index of destination MAC address | ||
| lldpV2PortConfigAdminStatus | 1.3.111.2.802.1.1.13.1.1.8.1.3 | R/O | INTEGER ・txOnly(1) ・rxOnly(2) ・txAndRx(3) ・disabled(4) | LLDP transmission/reception status | ||
| lldpV2PortConfigNotificationEnable | 1.3.111.2.802.1.1.13.1.1.8.1.4 | R/O | TruthValue | LLDP notification status | ||
| lldpV2PortConfigTLVsTxEnable | 1.3.111.2.802.1.1.13.1.1.8.1.5 | R/O | BITS ・portDesc(0) ・sysName(1) ・sysDesc(2) ・sysCap(3) | Basic management TLV transmission item | ||
| lldpV2DestAddressTable | 1.3.111.2.802.1.1.13.1.1.9 | N/A | Table of MAC addresses used in LLDP | |||
| lldpV2DestAddressTableEntry | 1.3.111.2.802.1.1.13.1.1.9.1 | N/A | INDEX ・lldpV2AddressTableIndex | |||
| lldpV2AddressTableIndex | 1.3.111.2.802.1.1.13.1.1.9.1.1 | N/A | LldpV2DestAddressTableIndex | Index of destination MAC address | ||
| lldpV2DestMacAddress | 1.3.111.2.802.1.1.13.1.1.9.1.2 | R/O | MacAddress | MAC address used when sending LLDP | ||
lldpV2Statistics group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpV2StatsRemTablesLastChangeTime | 1.3.111.2.802.1.1.13.1.2.1 | R/O | TimeStamp | Time from system initialization to remote data update | ||
| lldpV2StatsRemTablesInserts | 1.3.111.2.802.1.1.13.1.2.2 | R/O | ZeroBasedCounter32 | Total number of entries added to the device management table | ||
| lldpV2StatsRemTablesDeletes | 1.3.111.2.802.1.1.13.1.2.3 | R/O | ZeroBasedCounter32 | Total number of entries deleted from the device management table | ||
| lldpV2StatsRemTablesDrops | 1.3.111.2.802.1.1.13.1.2.4 | R/O | ZeroBasedCounter32 | Total number of entries that could not be set in the device management table | ||
| lldpV2StatsRemTablesAgeouts | 1.3.111.2.802.1.1.13.1.2.5 | R/O | ZeroBasedCounter32 | Total number of entries that exceeded TTL time (aged out) and were deleted from the device management table | ||
| lldpV2StatsTxPortTable | 1.3.111.2.802.1.1.13.1.2.6 | N/A | LLDP transmission statistics information table | |||
| lldpV2StatsTxPortEntry | 1.3.111.2.802.1.1.13.1.2.6.1 | N/A | INDEX ・lldpV2StatsTxIfInde ・lldpV2StatsTxDestMACAddress | |||
| lldpV2StatsTxIfIndex | 1.3.111.2.802.1.1.13.1.2.6.1.1 | N/A | InterfaceIndex | Port index | ||
| lldpV2StatsTxDestMACAddress | 1.3.111.2.802.1.1.13.1.2.6.1.2 | N/A | LldpV2DestAddressTableIndex | Index of destination MAC address | ||
| lldpV2StatsTxPortFramesTotal | 1.3.111.2.802.1.1.13.1.2.6.1.3 | R/O | Counter32 | Total number of LLDP transmission frames | ||
| lldpV2StatsTxLLDPDULengthErrors | 1.3.111.2.802.1.1.13.1.2.6.1.4 | R/O | Counter32 | Number of LLDP frame length errors | ||
| lldpV2StatsRxPortTable | 1.3.111.2.802.1.1.13.1.2.7 | N/A | LLDP reception statistics information table | |||
| lldpV2StatsRxPortEntry | 1.3.111.2.802.1.1.13.1.2.7.1 | N/A | INDEX ・lldpV2StatsRxDestIfIndex ・lldpV2StatsRxDestMACAddress | |||
| lldpV2StatsRxDestIfIndex | 1.3.111.2.802.1.1.13.1.2.7.1.1 | N/A | InterfaceIndex | Port index | ||
| lldpV2StatsRxDestMACAddress | 1.3.111.2.802.1.1.13.1.2.7.1.2 | N/A | LldpV2DestAddressTableIndex | Index of destination MAC address | ||
| lldpV2StatsRxPortFramesDiscardedTotal | 1.3.111.2.802.1.1.13.1.2.7.1.3 | R/O | Counter32 | Number of discarded LLDP frames | ||
| lldpV2StatsRxPortFramesErrors | 1.3.111.2.802.1.1.13.1.2.7.1.4 | R/O | Counter32 | Number of error frames received | ||
| lldpV2StatsRxPortFramesTotal | 1.3.111.2.802.1.1.13.1.2.7.1.5 | R/O | Counter32 | Number of LLDP frames received | ||
| lldpV2StatsRxPortTLVsDiscardedTotal | 1.3.111.2.802.1.1.13.1.2.7.1.6 | R/O | Counter32 | Number of discarded LLDP frames | ||
| lldpV2StatsRxPortTLVsUnrecognizedTotal | 1.3.111.2.802.1.1.13.1.2.7.1.7 | R/O | Counter32 | Number of unrecognized TLVs received | ||
| lldpV2StatsRxPortAgeoutsTotal | 1.3.111.2.802.1.1.13.1.2.7.1.8 | R/O | ZeroBasedCounter32 | Number of entries aged out | ||
lldpV2LocalSystemData group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpV2LocChassisIdSubtype | 1.3.111.2.802.1.1.13.1.3.1 | R/O | LldpV2ChassisIdSubtype | Subtype of chassis ID | ||
| lldpV2LocChassisId | 1.3.111.2.802.1.1.13.1.3.2 | R/O | LldpV2ChassisId | Chassis ID | ||
| lldpV2LocSysName | 1.3.111.2.802.1.1.13.1.3.3 | R/O | SnmpAdminString (SIZE (0..255)) | System name | ||
| lldpV2LocSysDesc | 1.3.111.2.802.1.1.13.1.3.4 | R/O | SnmpAdminString (SIZE (0..255)) | System description | ||
| lldpV2LocSysCapSupported | 1.3.111.2.802.1.1.13.1.3.5 | R/O | LldpV2SystemCapabilitiesMap | Functions supported by the system | ||
| lldpV2LocSysCapEnabled | 1.3.111.2.802.1.1.13.1.3.6 | R/O | LldpV2SystemCapabilitiesMap | Functions enabled by the system | ||
| lldpV2LocPortTable | 1.3.111.2.802.1.1.13.1.3.7 | N/A | Local port information table | |||
| lldpV2LocPortEntry | 1.3.111.2.802.1.1.13.1.3.7.1 | N/A | INDEX ・lldpV2LocPortIfIndex | |||
| lldpV2LocPortIfIndex | 1.3.111.2.802.1.1.13.1.3.7.1.1 | N/A | InterfaceIndex | Port index | ||
| lldpV2LocPortIdSubtype | 1.3.111.2.802.1.1.13.1.3.7.1.2 | R/O | LldpV2PortIdSubtype | Port ID subtype | ||
| lldpV2LocPortId | 1.3.111.2.802.1.1.13.1.3.7.1.3 | R/O | LldpV2PortId | Port ID | ||
| lldpV2LocPortDesc | 1.3.111.2.802.1.1.13.1.3.7.1.4 | R/O | SnmpAdminString (SIZE (0..255)) | Port description | ||
| lldpV2LocManAddrTable | 1.3.111.2.802.1.1.13.1.3.8 | N/A | Table of local system management addresses | |||
| lldpV2LocManAddrEntry | 1.3.111.2.802.1.1.13.1.3.8.1 | N/A | INDEX ・lldpV2LocManAddrSubtype ・lldpV2LocManAddr | |||
| lldpV2LocManAddrSubtype | 1.3.111.2.802.1.1.13.1.3.8.1.1 | N/A | AddressFamilyNumbers | Sub-type for management address | ||
| lldpV2LocManAddr | 1.3.111.2.802.1.1.13.1.3.8.1.2 | N/A | LldpV2ManAddress | management address | ||
| lldpV2LocManAddrLen | 1.3.111.2.802.1.1.13.1.3.8.1.3 | R/O | Unsigned32 | management address length | ||
| lldpV2LocManAddrIfSubtype | 1.3.111.2.802.1.1.13.1.3.8.1.4 | R/O | LldpV2ManAddrIfSubtype | Interface sub-type | ||
| lldpV2LocManAddrIfId | 1.3.111.2.802.1.1.13.1.3.8.1.5 | R/O | Unsigned32 | Interface ID | ||
lldpV2RemoteSystemsData group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| lldpV2RemTable | 1.3.111.2.802.1.1.13.1.4.1 | N/A | Information table of connected remote devices | |||
| lldpV2RemEntry | 1.3.111.2.802.1.1.13.1.4.1.1 | N/A | INDEX ・lldpV2RemTimeMark ・lldpV2RemLocalIfIndex ・lldpV2RemLocalDestMACAddress ・lldpV2RemIndex | |||
| lldpV2RemTimeMark | 1.3.111.2.802.1.1.13.1.4.1.1.1 | N/A | TimeFilter | Time filter for lldpV2RemEntry | ||
| lldpV2RemLocalIfIndex | 1.3.111.2.802.1.1.13.1.4.1.1.2 | N/A | InterfaceIndex | Port index | ||
| lldpV2RemLocalDestMACAddress | 1.3.111.2.802.1.1.13.1.4.1.1.3 | N/A | LldpV2DestAddressTableIndex | Destination MAC address | ||
| lldpV2RemIndex | 1.3.111.2.802.1.1.13.1.4.1.1.4 | N/A | Unsigned32(1..2147483647) | Remote system index | ||
| lldpV2RemChassisIdSubtype | 1.3.111.2.802.1.1.13.1.4.1.1.5 | R/O | LldpV2ChassisIdSubtype | Subtype of chassis ID | ||
| lldpV2RemChassisId | 1.3.111.2.802.1.1.13.1.4.1.1.6 | R/O | LldpV2ChassisId | Chassis ID | ||
| lldpV2RemPortIdSubtype | 1.3.111.2.802.1.1.13.1.4.1.1.7 | R/O | LldpV2PortIdSubtype | Port ID subtype | ||
| lldpV2RemPortId | 1.3.111.2.802.1.1.13.1.4.1.1.8 | R/O | LldpV2PortId | Port ID | ||
| lldpV2RemPortDesc | 1.3.111.2.802.1.1.13.1.4.1.1.9 | R/O | SnmpAdminString (SIZE (0..255)) | Port description | ||
| lldpV2RemSysName | 1.3.111.2.802.1.1.13.1.4.1.1.10 | R/O | SnmpAdminString (SIZE (0..255)) | System name | ||
| lldpV2RemSysDesc | 1.3.111.2.802.1.1.13.1.4.1.1.11 | R/O | SnmpAdminString (SIZE (0..255)) | System description | ||
| lldpV2RemSysCapSupported | 1.3.111.2.802.1.1.13.1.4.1.1.12 | R/O | LldpV2SystemCapabilitiesMap | Functions supported by the system | ||
| lldpV2RemSysCapEnabled | 1.3.111.2.802.1.1.13.1.4.1.1.13 | R/O | LldpV2SystemCapabilitiesMap | Functions enabled on the system | ||
| lldpV2RemRemoteChanges | 1.3.111.2.802.1.1.13.1.4.1.1.14 | R/O | TruthValue | Flag indicating that the MIB has changed on the remote device | ||
| lldpV2RemTooManyNeighbors | 1.3.111.2.802.1.1.13.1.4.1.1.15 | R/O | TruthValue | Flag indicating that the number of connected remote devices has exceeded the upper limit of the management table | ||
| lldpV2RemManAddrTable | 1.3.111.2.802.1.1.13.1.4.2 | N/A | Remote system management address table | |||
| lldpV2RemManAddrEntry | 1.3.111.2.802.1.1.13.1.4.2.1 | N/A | INDEX ・lldpV2RemTimeMark ・lldpV2RemLocalIfIndex ・lldpV2RemLocalDestMACAddress ・lldpV2RemIndex ・lldpV2RemManAddrSubtype ・lldpV2RemManAddr | |||
| lldpV2RemManAddrSubtype | 1.3.111.2.802.1.1.13.1.4.2.1.1 | N/A | AddressFamilyNumbers | Management address subtype | ||
| lldpV2RemManAddr | 1.3.111.2.802.1.1.13.1.4.2.1.2 | N/A | LldpV2ManAddress | Management address of remote system | ||
| lldpV2RemManAddrIfSubtype | 1.3.111.2.802.1.1.13.1.4.2.1.3 | R/O | LldpV2ManAddrIfSubtype | Interface subtype | ||
| lldpV2RemManAddrIfId | 1.3.111.2.802.1.1.13.1.4.2.1.4 | R/O | Unsigned32 | Interface ID | ||
| lldpV2RemManAddrOID | 1.3.111.2.802.1.1.13.1.4.2.1.5 | R/O | OBJECT IDENTIFIER | OID of management address | ||
| lldpV2RemUnknownTLVTable | 1.3.111.2.802.1.1.13.1.4.3 | N/A | Table of undefined TLV information | |||
| lldpV2RemUnknownTLVEntry | 1.3.111.2.802.1.1.13.1.4.3.1 | N/A | INDEX ・lldpV2RemTimeMark ・lldpV2RemLocalIfIndex ・lldpV2RemLocalDestMACAddress ・lldpV2RemIndex ・lldpV2RemUnknownTLVType | |||
| lldpV2RemUnknownTLVType | 1.3.111.2.802.1.1.13.1.4.3.1.1 | N/A | Unsigned32(9..126) | Undefined TLV types | ||
| lldpV2RemUnknownTLVInfo | 1.3.111.2.802.1.1.13.1.4.3.1.2 | R/O | OCTET STRING (SIZE (0..511)) | Undefined TLV information | ||
| lldpV2RemOrgDefInfoTable | 1.3.111.2.802.1.1.13.1.4.4 | N/A | OUI information table | |||
| lldpV2RemOrgDefInfoEntry | 1.3.111.2.802.1.1.13.1.4.4.1 | N/A | INDEX ・lldpV2RemTimeMark ・lldpV2RemLocalIfIndex ・lldpV2RemLocalDestMACAddress ・lldpV2RemIndex ・lldpV2RemOrgDefInfoOUI ・lldpV2RemOrgDefInfoSubtype ・lldpV2RemOrgDefInfoIndex | |||
| lldpV2RemOrgDefInfoOUI | 1.3.111.2.802.1.1.13.1.4.4.1.1 | N/A | OCTET STRING (SIZE (3)) | OUI information of remote system | ||
| lldpV2RemOrgDefInfoSubtype | 1.3.111.2.802.1.1.13.1.4.4.1.2 | N/A | Unsigned32(1..255) | OUI information subtype of remote system | ||
| lldpV2RemOrgDefInfoIndex | 1.3.111.2.802.1.1.13.1.4.4.1.3 | N/A | Unsigned32(1..2147483647) | Index for OUI information and OUI information subtype | ||
| lldpV2RemOrgDefInfo | 1.3.111.2.802.1.1.13.1.4.4.1.4 | R/O | OCTET STRING (SIZE (0..507)) | Information defined for each organization | ||
4.3 lagMIB group
This MIB is related to LACP link aggregation information.
The syntax defined in the lagMIB group is shown below.
Syntax defined in the lagMIB group
| Syntax | Definition |
|---|---|
| LacpKey | INTEGER (1..127) Note: Although this is INTEGER (0..65535) as per the standards, on this product it is in the range of INTEGER (1..127) |
| LacpState | BITS ・lacpActivity(0) ・lacpTimeout(1) ・aggregation(2) ・synchronization(3) ・collecting(4) ・distributing(5) ・defaulted(6) ・expired(7) |
| ChurnState | INTEGER ・noChurn(1) ・churn(2) ・churnMonitor(3) |
The lagMIB group is divided into subgroups such as those shown below.
lagMIB(43)
|
+--lagMIBObjects(1)
|
+--dot3adAgg(1)
|
+--dot3adAggPort(2)
|
+--dot3adTablesLastChanged(3)
dot3adAgg group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot3adAggTable | 1.2.840.10006.300.43.1.1.1 | N/A | LACP information table for system | |||
| dot3adAggEntry | 1.2.840.10006.300.43.1.1.1.1 | N/A | INDEX ・dot3adAggIndex | |||
| dot3adAggIndex | 1.2.840.10006.300.43.1.1.1.1.1 | N/A | InterfaceIndex | LACP logical interface number | ||
| dot3adAggMACAddress | 1.2.840.10006.300.43.1.1.1.1.2 | R/O | MacAddress | MAC address for LACP logical interface | ||
| dot3adAggActorSystemPriority | 1.2.840.10006.300.43.1.1.1.1.3 | R/NW | INTEGER (1..65535) Note: Although this is INTEGER (0..65535) as per the standards, on this product it is in the range of INTEGER (1..65535) Same applies to other priority-related lagMIB | LACP system priority for this device | ||
| dot3adAggActorSystemID | 1.2.840.10006.300.43.1.1.1.1.4 | R/NW | MacAddress | LACP system ID for the device itself | ||
| dot3adAggAggregateOrIndividual | 1.2.840.10006.300.43.1.1.1.1.5 | R/O | TruthValue | Whether operating as Aggregate (true) or as individual links (alternate waiting ports) (false) | ||
| dot3adAggActorAdminKey | 1.2.840.10006.300.43.1.1.1.1.6 | R/NW | LacpKey | ADMIN Key (identifier ID for the LACP logical interface) used in managing this device “Used in managing” means the setting values for ADMIN properties or the config value. Same applies to other lagMIB | ||
| dot3adAggActorOperKey | 1.2.840.10006.300.43.1.1.1.1.7 | R/O | LacpKey | ADMIN Key (identifier ID for the LACP logical interface) used in operation, for this device “Used in operating” means the current values of the current operation, which are exchanged by the LACP protocol. Same applies to other lagMIB | ||
| dot3adAggPartnerSystemID | 1.2.840.10006.300.43.1.1.1.1.8 | R/O | MacAddress | LACP system ID of the opposing device | ||
| dot3adAggPartnerSystemPriority | 1.2.840.10006.300.43.1.1.1.1.9 | R/O | INTEGER (1..65535) | LACP system priority for the opposing device | ||
| dot3adAggPartnerOperKey | 1.2.840.10006.300.43.1.1.1.1.10 | R/O | LacpKey | ADMIN Key (identifier ID for the LACP logical interface) used in operation, for the opposing device | ||
| dot3adAggCollectorMaxDelay | 1.2.840.10006.300.43.1.1.1.1.11 | R/NW | INTEGER (0..65535) | Delay time from when the LACP packet is received to the time it is reflected in operation | ||
| dot3adAggPortListTable | 1.2.840.10006.300.43.1.1.2 | N/A | LACP port list table for the system | |||
| dot3adAggPortListEntry | 1.2.840.10006.300.43.1.1.2.1 | N/A | INDEX ・dot3adAggIndex | |||
| dot3adAggPortListPorts | 1.2.840.10006.300.43.1.1.2.1.1 | R/O | PortList | List of ports where LACP is used. Bits are assigned in the following order, starting with the most significant bit shown on interface (port) bitmap. Ports 1.1 to 1.51, port 1.52, ports 2.1 to 2.51, and port 2.52 If port 1.4 and port 2.4 are used, for example, then the following values are indicated in hexadecimal. 10 00 00 00 00 00 01 00 00 00 00 00 00 | ||
dot3adAggPort group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot3adAggPortTable | 1.2.840.10006.300.43.1.2.1 | N/A | Table of information for ports used by the LACP | |||
| dot3adAggPortEntry | 1.2.840.10006.300.43.1.2.1.1 | N/A | INDEX ・dot3adAggPortIndex | |||
| dot3adAggPortIndex | 1.2.840.10006.300.43.1.2.1.1.1 | N/A | InterfaceIndex | Port interface number | ||
| dot3adAggPortActorSystemPriority | 1.2.840.10006.300.43.1.2.1.1.2 | R/NW | INTEGER (1..65535) | LACP system priority for this device | ||
| dot3adAggPortActorSystemID | 1.2.840.10006.300.43.1.2.1.1.3 | R/O | MacAddress | LACP system ID for the device itself | ||
| dot3adAggPortActorAdminKey | 1.2.840.10006.300.43.1.2.1.1.4 | R/NW | LacpKey | ADMIN Key (identifier ID for the LACP logical interface) used in managing this device | ||
| dot3adAggPortActorOperKey | 1.2.840.10006.300.43.1.2.1.1.5 | R/NW | LacpKey | ADMIN Key (identifier ID for the LACP logical interface) used in operation, for this device | ||
| dot3adAggPortPartnerAdminSystemPriority | 1.2.840.10006.300.43.1.2.1.1.6 | R/NW | INTEGER (1..65535) | LACP system priority used in management, for the opposing device | ||
| dot3adAggPortPartnerOperSystemPriority | 1.2.840.10006.300.43.1.2.1.1.7 | R/O | INTEGER (1..65535) | LACP system priority used in operation, for the opposing device | ||
| dot3adAggPortPartnerAdminSystemID | 1.2.840.10006.300.43.1.2.1.1.8 | R/NW | MacAddress | LACP system ID used in management, for the opposing device | ||
| dot3adAggPortPartnerOperSystemID | 1.2.840.10006.300.43.1.2.1.1.9 | R/O | MacAddress | LACP system ID used in operation, for the opposing device | ||
| dot3adAggPortPartnerAdminKey | 1.2.840.10006.300.43.1.2.1.1.10 | R/NW | LacpKey | ADMIN Key (identifier ID for the LACP logical interface) used in management, for the opposing device | ||
| dot3adAggPortPartnerOperKey | 1.2.840.10006.300.43.1.2.1.1.11 | R/O | LacpKey | ADMIN Key (identifier ID for the LACP logical interface) used in operation, for the opposing device | ||
| dot3adAggPortSelectedAggID | 1.2.840.10006.300.43.1.2.1.1.12 | R/O | InterfaceIndex | Logical interface number selected by the port | ||
| dot3adAggPortAttachedAggID | 1.2.840.10006.300.43.1.2.1.1.13 | R/O | InterfaceIndex | Logical interface number connected to the port | ||
| dot3adAggPortActorPort | 1.2.840.10006.300.43.1.2.1.1.14 | R/O | INTEGER (0..65535) | Physical interface number of this device | ||
| dot3adAggPortActorPortPriority | 1.2.840.10006.300.43.1.2.1.1.15 | R/NW | INTEGER (0..65535) | Port priority for physical interface of this device | ||
| dot3adAggPortPartnerAdminPort | 1.2.840.10006.300.43.1.2.1.1.16 | R/NW | INTEGER (0..65535) | Physical interface number used in management, for the opposing device | ||
| dot3adAggPortPartnerOperPort | 1.2.840.10006.300.43.1.2.1.1.17 | R/O | INTEGER (0..65535) | Physical interface number used in operation, for the opposing device | ||
| dot3adAggPortPartnerAdminPortPriority | 1.2.840.10006.300.43.1.2.1.1.18 | R/NW | INTEGER (1..65535) | Port priority of physical interface used in management, for the opposing device | ||
| dot3adAggPortPartnerOperPortPriority | 1.2.840.10006.300.43.1.2.1.1.19 | R/O | INTEGER (1..65535) | Port priority for physical interface used in operation, for the opposing device | ||
| dot3adAggPortActorAdminState | 1.2.840.10006.300.43.1.2.1.1.20 | R/NW | LacpState | Actor_State used in management, for this device ActorState is a status variable that shows internal transitions | ||
| dot3adAggPortActorOperState | 1.2.840.10006.300.43.1.2.1.1.21 | R/O | LacpState | Actor_State used in operation, for this device | ||
| dot3adAggPortPartnerAdminState | 1.2.840.10006.300.43.1.2.1.1.22 | R/NW | LacpState | Actor_State used in management, for the opposing device | ||
| dot3adAggPortPartnerOperState | 1.2.840.10006.300.43.1.2.1.1.23 | R/O | LacpState | Actor_State used in operation, for the opposing device | ||
| dot3adAggPortAggregateOrIndividual | 1.2.840.10006.300.43.1.2.1.1.24 | R/O | TruthValue | Whether Aggregate (true), or individual physical interfaces (alternate waiting ports) (false) | ||
| dot3adAggPortStatsTable | 1.2.840.10006.300.43.1.2.2 | N/A | Table of statistical information for ports used by the LACP | |||
| dot3adAggPortStatsEntry | 1.2.840.10006.300.43.1.2.2.1 | N/A | INDEX ・dot3adAggPortIndex | |||
| dot3adAggPortStatsLACPDUsRx | 1.2.840.10006.300.43.1.2.2.1.1 | R/O | Counter32 | No. of correct LACPDU received by the physical interface | ||
| dot3adAggPortStatsMarkerPDUsRx | 1.2.840.10006.300.43.1.2.2.1.2 | R/O | Counter32 | No. of correct marker frames received by the physical interface | ||
| dot3adAggPortStatsMarkerResponsePDUsRx | 1.2.840.10006.300.43.1.2.2.1.3 | R/O | Counter32 | No. of correct marker response frames received by the physical interface | ||
| dot3adAggPortStatsUnknownRx | 1.2.840.10006.300.43.1.2.2.1.4 | R/O | Counter32 | No. of unknown frames received by the physical interface | ||
| dot3adAggPortStatsIllegalRx | 1.2.840.10006.300.43.1.2.2.1.5 | R/O | Counter32 | No. of frames received by the physical interface on which the EtherType was 0x8809 but the PDU was invalid | ||
| dot3adAggPortStatsLACPDUsTx | 1.2.840.10006.300.43.1.2.2.1.6 | R/O | Counter32 | No. of LACPDU transmitted from physical interface | ||
| dot3adAggPortStatsMarkerPDUsTx | 1.2.840.10006.300.43.1.2.2.1.7 | R/O | Counter32 | No. of marker frames transmitted from physical interface | ||
| dot3adAggPortStatsMarkerResponsePDUsTx | 1.2.840.10006.300.43.1.2.2.1.8 | R/O | Counter32 | No. of marker response frames transmitted from physical interface | ||
| dot3adAggPortDebugTable | 1.2.840.10006.300.43.1.2.3 | N/A | Debug information table for ports used by the LACP | |||
| dot3adAggPortDebugEntry | 1.2.840.10006.300.43.1.2.3.1 | N/A | INDEX ・dot3adAggPortIndex | |||
| dot3adAggPortDebugRxState | 1.2.840.10006.300.43.1.2.3.1.1 | R/O | INTEGER ・current(1) ・expired(2) ・defaulted(3) ・initialize(4) ・lacpDisabled(5) ・portDisabled(6) | Status of LACP protocol “Receive machine” transition variable | ||
| dot3adAggPortDebugLastRxTime | 1.2.840.10006.300.43.1.2.3.1.2 | R/O | TimeTicks | Internal time when logical interface last received data | ||
| dot3adAggPortDebugMuxState | 1.2.840.10006.300.43.1.2.3.1.3 | R/O | INTEGER ・detached(1) ・waiting(2) ・attached(3) ・collecting(4) ・distributing(5) ・collecting_distributing(6) | Status of LACP protocol “Mux machine” transition variable | ||
| dot3adAggPortDebugMuxReason | 1.2.840.10006.300.43.1.2.3.1.4 | R/O | DisplayString | Reason why most recent LACP protocol “Mux machine” transition variable was changed | ||
| dot3adAggPortDebugActorChurnState | 1.2.840.10006.300.43.1.2.3.1.5 | R/O | ChurnState | Status of “Churn Detection” transition variable for LACP protocol of this device | ||
| dot3adAggPortDebugPartnerChurnState | 1.2.840.10006.300.43.1.2.3.1.6 | R/O | ChurnState | Status of LACP protocol “Churn Detection” transition variable for the opposing device | ||
| dot3adAggPortDebugActorChurnCount | 1.2.840.10006.300.43.1.2.3.1.7 | R/O | Counter32 | No. of times that the LACP protocol “Churn Detection” status variable changed to ACTOR_CHURN status | ||
| dot3adAggPortDebugPartnerChurnCount | 1.2.840.10006.300.43.1.2.3.1.8 | R/O | Counter32 | No. of times that LACP protocol “Churn Detection” status variable changed to PARTNER_CHURN status | ||
| dot3adAggPortDebugActorSyncTransitionCount | 1.2.840.10006.300.43.1.2.3.1.9 | R/O | Counter32 | No. of times that LACP protocol “Mux machine” status variable of this device changed to IN_SYNC status | ||
| dot3adAggPortDebugPartnerSyncTransitionCount | 1.2.840.10006.300.43.1.2.3.1.10 | R/O | Counter32 | No. of times that the LACP protocol “Mux machine” status variable of the opposing device changed to IN_SYNC status | ||
| dot3adAggPortDebugActorChangeCount | 1.2.840.10006.300.43.1.2.3.1.11 | R/O | Counter32 | No. of times that the LAG ID of this device was changed | ||
| dot3adAggPortDebugPartnerChangeCount | 1.2.840.10006.300.43.1.2.3.1.12 | R/O | Counter32 | No. of times that the LAG ID of the opposing device was changed | ||
dot3adTablesLastChanged group
| MIB name | OID | Access | Syntax | Description |
|---|---|---|---|---|
| dot3adTablesLastChanged | 1.2.840.10006.300.43.1.3 | R/O | TimeTicks | Most recent time in which Dot3adAggTable, dot3adAggPortListTable, and dot3adAggPortTable was changed Note: This is always “0” on this product |
4.4 system group
This MIB is related to system information.
system group
| MIB name | OID | Access | Syntax | Description |
|---|---|---|---|---|
| sysDescr | 1.3.6.1.2.1.1.1 | R/O | DisplayString (SIZE (0..255)) | The description of the device. Device name and firmware revision |
| sysObjectID | 1.3.6.1.2.1.1.2 | R/O | OBJECT IDENTIFIER | Device OID that is defined by Yamaha’s private MIB |
| sysUpTimeInstance | 1.3.6.1.2.1.1.3 | R/O | TimeTicks | Elapsed time from boot |
| sysContact | 1.3.6.1.2.1.1.4 | R/W | DisplayString (SIZE (0..255)) | Administrator contact information Setting value for snmp-server contact command |
| sysName | 1.3.6.1.2.1.1.5 | R/W | DisplayString (SIZE (0..255)) | Administrative name Setting value for hostname command |
| sysLocation | 1.3.6.1.2.1.1.6 | R/W | DisplayString (SIZE (0..255)) | Device location Setting value for snmp-server location command |
| sysServices | 1.3.6.1.2.1.1.7 | R/O | INTEGER (0..127) | Value that indicates services the device supports |
4.5 interface group
This MIB is related to interface information.
interface group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| ifNumber | 1.3.6.1.2.1.2.1 | R/O | Integer32 | No. of interfaces | ||
| ifTable | 1.3.6.1.2.1.2.2 | N/A | Interface information table | |||
| ifEntry | 1.3.6.1.2.1.2.2.1 | N/A | INDEX ・ifIndex | |||
| ifIndex | 1.3.6.1.2.1.2.2.1.1 | R/O | InterfaceIndex | Interface ID number | ||
| ifDescr | 1.3.6.1.2.1.2.2.1.2 | R/O | DisplayString (SIZE (0..255)) | Description of the interface. Interface name | ||
| ifType | 1.3.6.1.2.1.2.2.1.3 | R/O | IANAifType ・ethernetCsmacd(6) ・l3ipvlan(136), others | Types of interfaces | ||
| ifMtu | 1.3.6.1.2.1.2.2.1.4 | R/O | Integer32 | Maximum frame size that can be transmitted/received | ||
| ifSpeed | 1.3.6.1.2.1.2.2.1.5 | R/O | Gauge32 | Interface speed | ||
| ifPhysAddress | 1.3.6.1.2.1.2.2.1.6 | R/O | PhysAddress | MAC address | ||
| ifAdminStatus | 1.3.6.1.2.1.2.2.1.7 | R/W | INTEGER ・up(1) ・down(2) | Desirable interface status | ||
| ifOperStatus | 1.3.6.1.2.1.2.2.1.8 | R/O | INTEGER ・up(1) ・down(2) | Current status of interface | ||
| ifLastChange | 1.3.6.1.2.1.2.2.1.9 | R/O | TimeTicks | Time when the interface changed to the current status (time elapsed time from boot) | ||
| ifInOctets | 1.3.6.1.2.1.2.2.1.10 | R/O | Counter32 | Total no. of octets received | ||
| ifInUcastPkts | 1.3.6.1.2.1.2.2.1.11 | R/O | Counter32 | No. of unicast packets notified to higher protocol | ||
| ifInNUcastPkts | 1.3.6.1.2.1.2.2.1.12 | R/O | Counter32 | Number of non-unicast packets notified to higher protocol | ||
| ifInDiscards | 1.3.6.1.2.1.2.2.1.13 | R/O | Counter32 | No. of packets that were discarded, despite no errors detected | ||
| ifInErrors | 1.3.6.1.2.1.2.2.1.14 | R/O | Counter32 | No. of packets not notified to higher protocol due to errors | ||
| ifInUnknownProtos | 1.3.6.1.2.1.2.2.1.15 | R/O | Counter32 | No. of discarded packets, due to an unsupported protocol | ||
| ifOutOctets | 1.3.6.1.2.1.2.2.1.16 | R/O | Counter32 | Total no. of octets transmitted | ||
| ifOutUcastPkts | 1.3.6.1.2.1.2.2.1.17 | R/O | Counter32 | No. of unicast packets requested for transmission by a higher protocol | ||
| ifOutNUcastPkts | 1.3.6.1.2.1.2.2.1.18 | R/O | Counter32 | No. of non-unicast packets requested for transmission by a higher protocol | ||
| ifOutDiscards | 1.3.6.1.2.1.2.2.1.19 | R/O | Counter32 | No. of packets that were discarded for transmission, despite no errors detected | ||
| ifOutErrors | 1.3.6.1.2.1.2.2.1.20 | R/O | Counter32 | No. of packets not transmitted due to errors | ||
| ifSpecific | 1.3.6.1.2.1.2.2.1.22 | R/O | OBJECT IDENTIFIER | Reference to MIB that defines interface media characteristics If no reference exists, this will be 0.0 | ||
4.6 at group
This MIB is related to mapping information for physical addresses and network addresses.
at group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| atTable | 1.3.6.1.2.1.3.1 | N/A | Table of mapping information for physical addresses and network addresses | |||
| atEntry | 1.3.6.1.2.1.3.1.1 | N/A | INDEX ・atIfIndex ・atNetAddress | |||
| atIfIndex | 1.3.6.1.2.1.3.1.1.1 | R/NW | INTEGER | ifIndex for the corresponding interface | ||
| atPhysAddress | 1.3.6.1.2.1.3.1.1.2 | R/NW | PhysAddress | Physical address | ||
| atNetAddress | 1.3.6.1.2.1.3.1.1.3 | R/NW | NetworkAddress | IP address corresponding to the physical address | ||
4.7 rmon group
This MIB is related to RMON information.
The syntax defined in the rmon group is shown below.
Syntax defined in the rmon group
| Syntax | Definition |
|---|---|
| OwnerString | OCTET STRING (SIZE (0..127)) |
| EntryStatus | INTEGER ・valid(1) ・createRequest(2) ・underCreation(3) ・invalid(4) |
The rmon group is divided into subgroups such as those shown below.
rmon(16)
|
+--statistics(1)
|
+--history(2)
|
+--alarm(3)
|
+--event(9)
statistics group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| etherStatsTable | 1.3.6.1.2.1.16.1.1 | N/A | Table of statistical information for Ethernet | |||
| etherStatsEntry | 1.3.6.1.2.1.16.1.1.1 | N/A | INDEX ・etherStatsIndex | |||
| etherStatsIndex | 1.3.6.1.2.1.16.1.1.1.1 | R/O | Integer32 (1..65535) | Index of entries | ||
| etherStatsDataSource | 1.3.6.1.2.1.16.1.1.1.2 | R/C | OBJECT IDENTIFIER | Interface being monitored | ||
| etherStatsDropEvents | 1.3.6.1.2.1.16.1.1.1.3 | R/O | Counter32 | Number of packets dropped | ||
| etherStatsOctets | 1.3.6.1.2.1.16.1.1.1.4 | R/O | Counter32 | Number of octets received | ||
| etherStatsPkts | 1.3.6.1.2.1.16.1.1.1.5 | R/O | Counter32 | Number of packets received | ||
| etherStatsBroadcastPkts | 1.3.6.1.2.1.16.1.1.1.6 | R/O | Counter32 | Number of broadcast packets received | ||
| etherStatsMulticastPkts | 1.3.6.1.2.1.16.1.1.1.7 | R/O | Counter32 | Number of multicast packets received | ||
| etherStatsCRCAlignErrors | 1.3.6.1.2.1.16.1.1.1.8 | R/O | Counter32 | Number of FCS error packets received | ||
| etherStatsUndersizePkts | 1.3.6.1.2.1.16.1.1.1.9 | R/O | Counter32 | Number of undersize packets received (packets smaller than 64 octets) | ||
| etherStatsOversizePkts | 1.3.6.1.2.1.16.1.1.1.10 | R/O | Counter32 | Number of oversize packets received (packets larger than 1518 octets) | ||
| etherStatsFragments | 1.3.6.1.2.1.16.1.1.1.11 | R/O | Counter32 | Number of fragment packets received (packets smaller than 64 octets with abnormal FCS) | ||
| etherStatsJabbers | 1.3.6.1.2.1.16.1.1.1.12 | R/O | Counter32 | Number of jabber packets received (packets larger than 1518 octets with abnormal FCS) | ||
| etherStatsCollisions | 1.3.6.1.2.1.16.1.1.1.13 | R/O | Counter32 | Number of collisions | ||
| etherStatsOwner | 1.3.6.1.2.1.16.1.1.1.20 | R/C | OwnerString | Name of owner | ||
| etherStatsStatus | 1.3.6.1.2.1.16.1.1.1.21 | R/C | EntryStatus | Status of statistical group | ||
history group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| historyControlTable | 1.3.6.1.2.1.16.2.1 | N/A | Table of control information for the history group | |||
| historyControlEntry | 1.3.6.1.2.1.16.2.1.1 | N/A | INDEX ・historyControlIndex | |||
| historyControlIndex | 1.3.6.1.2.1.16.2.1.1.1 | R/O | Integer32 (1..65535) | Index of entries | ||
| historyControlDataSource | 1.3.6.1.2.1.16.2.1.1.2 | R/C | OBJECT IDENTIFIER | Interface being monitored | ||
| historyControlBucketsRequested | 1.3.6.1.2.1.16.2.1.1.3 | R/C | Integer32 (1..65535) | Number of history group history saves requested | ||
| historyControlBucketsGranted | 1.3.6.1.2.1.16.2.1.1.4 | R/O | Integer32 (1..65535) | Number of history group histories saved | ||
| historyControlInterval | 1.3.6.1.2.1.16.2.1.1.5 | R/C | Integer32 (1..3600) | Interval at which history group histories are saved | ||
| historyControlOwner | 1.3.6.1.2.1.16.2.1.1.6 | R/C | OwnerString | Name of owner | ||
| historyControlStatus | 1.3.6.1.2.1.16.2.1.1.7 | R/C | EntryStatus | History group status | ||
| etherHistoryTable | 1.3.6.1.2.1.16.2.2 | N/A | Table of history information | |||
| etherHistoryEntry | 1.3.6.1.2.1.16.2.2.1 | N/A | INDEX ・etherHistoryIndex ・etherHistorySampleIndex | |||
| etherHistoryIndex | 1.3.6.1.2.1.16.2.2.1.1 | R/O | Integer32 (1..65535) | Same value as the index value of historyControlIndex | ||
| etherHistorySampleIndex | 1.3.6.1.2.1.16.2.2.1.2 | R/O | Integer32 (1..2147483647) | Index of history entries | ||
| etherHistoryIntervalStart | 1.3.6.1.2.1.16.2.2.1.3 | R/O | TimeTicks | Interval at which history group histories are saved | ||
| etherHistoryDropEvents | 1.3.6.1.2.1.16.2.2.1.4 | R/O | Counter32 | Number of packets dropped | ||
| etherHistoryOctets | 1.3.6.1.2.1.16.2.2.1.5 | R/O | Counter32 | Number of octets received | ||
| etherHistoryPkts | 1.3.6.1.2.1.16.2.2.1.6 | R/O | Counter32 | Number of packets received | ||
| etherHistoryBroadcastPkts | 1.3.6.1.2.1.16.2.2.1.7 | R/O | Counter32 | Number of broadcast packets received | ||
| etherHistoryMulticastPkts | 1.3.6.1.2.1.16.2.2.1.8 | R/O | Counter32 | Number of multicast packets received | ||
| etherHistoryCRCAlignErrors | 1.3.6.1.2.1.16.2.2.1.9 | R/O | Counter32 | Number of FCS error packets received | ||
| etherHistoryUndersizePkts | 1.3.6.1.2.1.16.2.2.1.10 | R/O | Counter32 | Number of undersize packets received (packets smaller than 64 octets) | ||
| etherHistoryOversizePkts | 1.3.6.1.2.1.16.2.2.1.11 | R/O | Counter32 | Number of oversize packets received (packets larger than 1518 octets) | ||
| etherHistoryFragments | 1.3.6.1.2.1.16.2.2.1.12 | R/O | Counter32 | Number of fragment packets received (packets smaller than 64 octets with abnormal FCS) | ||
| etherHistoryJabbers | 1.3.6.1.2.1.16.2.2.1.13 | R/O | Counter32 | Number of jabber packets received (packets larger than 1518 octets with abnormal FCS) | ||
| etherHistoryCollisions | 1.3.6.1.2.1.16.2.2.1.14 | R/O | Counter32 | Number of collisions | ||
| etherHistoryUtilization | 1.3.6.1.2.1.16.2.2.1.15 | R/O | Integer32 (0..10000) | Estimated value of network usage ratio | ||
alarm group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| alarmTable | 1.3.6.1.2.1.16.3.1 | N/A | Table of information for the alarm group | |||
| alarmEntry | 1.3.6.1.2.1.16.3.1.1 | N/A | INDEX ・alarmIndex | |||
| alarmIndex | 1.3.6.1.2.1.16.3.1.1.1 | R/O | Integer32 (1..65535) | Index of entries | ||
| alarmInterval | 1.3.6.1.2.1.16.3.1.1.2 | R/C | Integer32 | Sampling interval | ||
| alarmVariable | 1.3.6.1.2.1.16.3.1.1.3 | R/C | OBJECT IDENTIFIER | MIB object to be monitored | ||
| alarmSampleType | 1.3.6.1.2.1.16.3.1.1.4 | R/C | INTEGER ・absoluteValue(1) ・deltaValue(2) | Sampling type | ||
| alarmValue | 1.3.6.1.2.1.16.3.1.1.5 | R/O | Integer32 | Estimated value | ||
| alarmStartupAlarm | 1.3.6.1.2.1.16.3.1.1.6 | R/C | INTEGER ・risingAlarm(1) ・fallingAlarm(2) ・risingOrFallingAlarm(3) | Threshold value used for first alarm determination | ||
| alarmRisingThreshold | 1.3.6.1.2.1.16.3.1.1.7 | R/C | Integer32 | Upper threshold value | ||
| alarmFallingThreshold | 1.3.6.1.2.1.16.3.1.1.8 | R/C | Integer32 | Lower threshold value | ||
| alarmRisingEventIndex | 1.3.6.1.2.1.16.3.1.1.9 | R/C | Integer32 (0..65535) | Event index when crossing upper limit | ||
| alarmFallingEventIndex | 1.3.6.1.2.1.16.3.1.1.10 | R/C | Integer32 (0..65535) | Event index when crossing lower limit | ||
| alarmOwner | 1.3.6.1.2.1.16.3.1.1.11 | R/C | OwnerString | Name of owner | ||
| alarmStatus | 1.3.6.1.2.1.16.3.1.1.12 | R/C | EntryStatus | Alarm group status | ||
event group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| eventTable | 1.3.6.1.2.1.16.9.1 | N/A | Table of information for event group | |||
| eventEntry | 1.3.6.1.2.1.16.9.1.1 | N/A | INDEX ・eventIndex | |||
| eventIndex | 1.3.6.1.2.1.16.9.1.1.1 | R/O | Integer32 (1..65535) | Index of entries | ||
| eventDescription | 1.3.6.1.2.1.16.9.1.1.2 | R/C | DisplayString (SIZE (0..127)) | Event description | ||
| eventType | 1.3.6.1.2.1.16.9.1.1.3 | R/C | INTEGER ・none(1) ・log(2) ・snmptrap(3) ・logandtrap(4) | Event type | ||
| eventCommunity | 1.3.6.1.2.1.16.9.1.1.4 | R/C | OCTET STRING (SIZE (0..127)) | Community name | ||
| eventLastTimeSent | 1.3.6.1.2.1.16.9.1.1.5 | R/O | TimeTicks | Event execution time | ||
| eventOwner | 1.3.6.1.2.1.16.9.1.1.6 | R/C | OwnerString | Name of owner | ||
| eventStatus | 1.3.6.1.2.1.16.9.1.1.7 | R/C | EntryStatus | Event group status | ||
4.8 dot1dBridge group
This MIB is related to dot1dBridge information.
The syntax defined in the dot1dBridge group is shown below.
Syntax defined in the dot1dBridge group
| Syntax | Definition |
|---|---|
| BridgeId | OCTET STRING (SIZE (8)) |
| Timeout | Integer32 |
| PortList | OCTET STRING |
| VlanIndex | Unsigned32 |
| VlanId | Integer32 (1..4094) |
The dot1dBridge group is divided into subgroups such as those shown below.
dot1dBridge(17)
|
+--dot1dBase(1)
|
+--dot1dStp(2)
|
+--dot1dTp(4)
|
+--dot1dStatic(5)
|
+--qBridgeMIB(7)
|
+--qBridgeMIBObjects(1)
|
+--dot1qBase(1)
|
+--dot1qTp(2)
|
+--dot1qVlan(4)
dot1dBase group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot1dBaseBridgeAddress | 1.3.6.1.2.1.17.1.1 | R/O | MacAddress | MAC address of bridge | ||
| dot1dBaseNumPorts | 1.3.6.1.2.1.17.1.2 | R/O | Integer32 | No. of ports for bridge | ||
| dot1dBaseType | 1.3.6.1.2.1.17.1.3 | R/O | INTEGER ・unknown(1) ・transparent-only(2) ・sourceroute-only(3) ・srt(4) | Type of bridging executable by the bridge | ||
| dot1dBasePortTable | 1.3.6.1.2.1.17.1.4 | N/A | Table of port information for bridge | |||
| dot1dBasePortEntry | 1.3.6.1.2.1.17.1.4.1 | N/A | INDEX ・dot1dBasePort | |||
| dot1dBasePort | 1.3.6.1.2.1.17.1.4.1.1 | R/O | Integer32 (1..65535) | Port number | ||
| dot1dBasePortIfIndex | 1.3.6.1.2.1.17.1.4.1.2 | R/O | InterfaceIndex | Instance value for ifIndex, defined by the IF-MIB of the interface corresponding to the port | ||
| dot1dBasePortCircuit | 1.3.6.1.2.1.17.1.4.1.3 | R/O | OBJECT IDENTIFIER | Identifier used when the value of dot1dBasePortIfIndex is the same port in the bridge | ||
| dot1dBasePortDelayExceededDiscards | 1.3.6.1.2.1.17.1.4.1.4 | R/O | Counter32 | No. of frames discarded at the port due to a bridge forwarding delay Note: This is always “0” on this product | ||
| dot1dBasePortMtuExceededDiscards | 1.3.6.1.2.1.17.1.4.1.5 | R/O | Counter32 | No. of frames discarded at the port due to excessive size Note: This is always “0” on this product | ||
dot1dStp group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot1dStpProtocolSpecification | 1.3.6.1.2.1.17.2.1 | R/O | INTEGER ・unknown(1) ・decLb100(2) ・ieee8021d(3) | Spanning tree protocol version | ||
| dot1dStpPriority | 1.3.6.1.2.1.17.2.2 | R/NW | Integer32 (0..65535) | Bridge priority value | ||
| dot1dStpTimeSinceTopologyChange | 1.3.6.1.2.1.17.2.3 | R/O | TimeTicks | Time elapsed since detecting a change in topology | ||
| dot1dStpTopChanges | 1.3.6.1.2.1.17.2.4 | R/O | Counter32 | No. of times a change in topology has been detected | ||
| dot1dStpDesignatedRoot | 1.3.6.1.2.1.17.2.5 | R/O | BridgeId | Root bridge identifier of spanning tree | ||
| dot1dStpRootCost | 1.3.6.1.2.1.17.2.6 | R/O | Integer32 | Path cost to root bridge | ||
| dot1dStpRootPort | 1.3.6.1.2.1.17.2.7 | R/O | Integer32 | Port number with the lowest cost from bridge to root bridge | ||
| dot1dStpMaxAge | 1.3.6.1.2.1.17.2.8 | R/O | Timeout | Maximum time elapsed for spanning tree protocol information (in units of 1/100 sec.) | ||
| dot1dStpHelloTime | 1.3.6.1.2.1.17.2.9 | R/O | Timeout | BPDU transmission interval (in units of 1/100 sec.) | ||
| dot1dStpHoldTime | 1.3.6.1.2.1.17.2.10 | R/O | Integer32 | Minimum transmission interval for Configuration BPDU (in units of 1/100 sec.) | ||
| dot1dStpForwardDelay | 1.3.6.1.2.1.17.2.11 | R/O | Timeout | Forward delay time (in units of 1/100 sec.) | ||
| dot1dStpBridgeMaxAge | 1.3.6.1.2.1.17.2.12 | R/NW | Timeout (600..4000) | Setting value for maximum elapsed time | ||
| dot1dStpBridgeHelloTime | 1.3.6.1.2.1.17.2.13 | R/NW | Timeout (100..1000) | Setting value for BPDU transmission interval | ||
| dot1dStpBridgeForwardDelay | 1.3.6.1.2.1.17.2.14 | R/NW | Timeout (400..3000) | Setting value for forward delay time | ||
| dot1dStpPortTable | 1.3.6.1.2.1.17.2.15 | N/A | Table of port information for spanning tree protocol | |||
| dot1dStpPortEntry | 1.3.6.1.2.1.17.2.15.1 | N/A | INDEX ・dot1dStpPort | |||
| dot1dStpPort | 1.3.6.1.2.1.17.2.15.1.1 | R/O | Integer32 (1..65535) | Port number for spanning tree protocol | ||
| dot1dStpPortPriority | 1.3.6.1.2.1.17.2.15.1.2 | R/NW | Integer32 (0..255) | Port priority value | ||
| dot1dStpPortState | 1.3.6.1.2.1.17.2.15.1.3 | R/O | INTEGER ・disabled(1) ・blocking(2) ・listening(3) ・learning(4) ・forwarding(5) ・broken(6) | Port status | ||
| dot1dStpPortEnable | 1.3.6.1.2.1.17.2.15.1.4 | R/NW | INTEGER ・enabled(1) ・disabled(2) | Port enabled/disabled status | ||
| dot1dStpPortPathCost | 1.3.6.1.2.1.17.2.15.1.5 | R/NW | Integer32 (1..65535) | Set path cost | ||
| dot1dStpPortDesignatedRoot | 1.3.6.1.2.1.17.2.15.1.6 | R/O | BridgeId | Root bridge identifier of configuration BPDU | ||
| dot1dStpPortDesignatedCost | 1.3.6.1.2.1.17.2.15.1.7 | R/O | Integer32 | Path cost value for specified port | ||
| dot1dStpPortDesignatedBridge | 1.3.6.1.2.1.17.2.15.1.8 | R/O | BridgeId | Specified port identifier | ||
| dot1dStpPortDesignatedPort | 1.3.6.1.2.1.17.2.15.1.9 | R/O | OCTET STRING (SIZE (2)) | Port identifier for specified bridge | ||
| dot1dStpPortForwardTransitions | 1.3.6.1.2.1.17.2.15.1.10 | R/O | Counter32 | No. of times that port switched from acquisition status to forwarding status | ||
| dot1dStpPortPathCost32 | 1.3.6.1.2.1.17.2.15.1.11 | R/NW | Integer32 (1..200000000) | Path cost value for ports complying with IEEE 802.1t | ||
| dot1dStpVersion | 1.3.6.1.2.1.17.2.16 | R/NW | INTEGER ・stpCompatible(0) ・rstp(2) | Spanning tree protocol version | ||
| dot1dStpTxHoldCount | 1.3.6.1.2.1.17.2.17 | R/NW | Integer32 (1..10) | Forward hold count value | ||
| dot1dStpExtPortTable | 1.3.6.1.2.1.17.2.19 | N/A | Table of port information for RSTP | |||
| dot1dStpExtPortEntry | 1.3.6.1.2.1.17.2.19.1 | N/A | AUGMENTS ・dot1dStpPortEntry | |||
| dot1dStpPortProtocolMigration | 1.3.6.1.2.1.17.2.19.1.1 | R/NW | TruthValue | Writing “true(1)” to this object will cause the BPDU of the port to be forcibly transmitted Note: This is always “false(2)” when read | ||
| dot1dStpPortAdminEdgePort | 1.3.6.1.2.1.17.2.19.1.2 | R/NW | TruthValue | Setting value for edge port | ||
| dot1dStpPortOperEdgePort | 1.3.6.1.2.1.17.2.19.1.3 | R/O | TruthValue | Current value for edge port | ||
| dot1dStpPortAdminPointToPoint | 1.3.6.1.2.1.17.2.19.1.4 | R/NW | INTEGER ・forceTrue(0) ・forceFalse(1) ・auto(2) | Setting value for point-to-point of the port | ||
| dot1dStpPortOperPointToPoint | 1.3.6.1.2.1.17.2.19.1.5 | R/O | TruthValue | Current value for point-to-point of the port | ||
| dot1dStpPortAdminPathCost | 1.3.6.1.2.1.17.2.19.1.6 | R/NW | Integer32 (0..200000000) | Setting value for path cost of port | ||
dot1dTp group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot1dTpLearnedEntryDiscards | 1.3.6.1.2.1.17.4.1 | R/O | Counter32 | Amount of forwarding information that was discarded due to having exceeded the upper save limit of the forwarding database | ||
| dot1dTpAgingTime | 1.3.6.1.2.1.17.4.2 | R/NW | Integer32 (10..1000000) | Timeout duration for aging out forwarding information that was actively acquired | ||
| dot1dTpFdbTable | 1.3.6.1.2.1.17.4.3 | N/A | Table of unicast entries that have forwarding or filtering information | |||
| dot1dTpFdbEntry | 1.3.6.1.2.1.17.4.3.1 | N/A | INDEX ・dot1dTpFdbAddress | |||
| dot1dTpFdbAddress | 1.3.6.1.2.1.17.4.3.1.1 | R/O | MacAddress | Unicast MAC addresses that have forwarding or filtering information | ||
| dot1dTpFdbPort | 1.3.6.1.2.1.17.4.3.1.2 | R/O | Integer32 | Port number of port that transmitted a frame with a source address that is the same as the instance value, corresponding to the dot1dTpFdbAddress | ||
| dot1dTpFdbStatus | 1.3.6.1.2.1.17.4.3.1.3 | R/O | INTEGE ・other(1) ・invalid(2) ・learned(3) ・self(4) ・mgmt(5) | MAC address table status | ||
| dot1dTpPortTable | 1.3.6.1.2.1.17.4.4 | N/A | Table for all port information that is associated with a transparent bridge | |||
| dot1dTpPortEntry | 1.3.6.1.2.1.17.4.4.1 | N/A | INDEX ・dot1dTpPort | |||
| dot1dTpPort | 1.3.6.1.2.1.17.4.4.1.1 | R/O | Integer32 (1..65535) | Port numbers that include transparent bridge management information | ||
| dot1dTpPortMaxInfo | 1.3.6.1.2.1.17.4.4.1.2 | R/O | Integer32 | Maximum size of information fields transmitted/received by a port | ||
| dot1dTpPortInFrames | 1.3.6.1.2.1.17.4.4.1.3 | R/O | Counter32 | No. of frames received by a port | ||
| dot1dTpPortOutFrames | 1.3.6.1.2.1.17.4.4.1.4 | R/O | Counter32 | No. of frames transmitted by a port | ||
| dot1dTpPortInDiscards | 1.3.6.1.2.1.17.4.4.1.5 | R/O | Counter32 | No. of frames that are valid for reception, which were discarded during forwarding | ||
dot1dStatic group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot1dStaticTable | 1.3.6.1.2.1.17.5.1 | N/A | Table of filtering information that was registered statically | |||
| dot1dStaticEntry | 1.3.6.1.2.1.17.5.1.1 | N/A | INDEX ・dot1dStaticAddress ・dot1dStaticReceivePort | |||
| dot1dStaticAddress | 1.3.6.1.2.1.17.5.1.1.1 | R/NC | MacAddress | Destination MAC address for which filtering information is applied | ||
| dot1dStaticReceivePort | 1.3.6.1.2.1.17.5.1.1.2 | R/NC | Integer32 (0..65535) | Reception port no. on which filtering information is applied | ||
| dot1dStaticAllowedToGoTo | 1.3.6.1.2.1.17.5.1.1.3 | R/NC | OCTET STRING (SIZE (0..512)) | Port no. on which filtering information was applied to a transmitted frame | ||
| dot1dStaticStatus | 1.3.6.1.2.1.17.5.1.1.4 | R/NC | INTEGER ・other(1) ・invalid(2) ・permanent(3) ・deleteOnReset(4) ・deleteOnTimeout(5) | Application status for filtering information | ||
dot1qBase group
| MIB name | OID | Access | Syntax | Description |
|---|---|---|---|---|
| dot1qVlanVersionNumber | 1.3.6.1.2.1.17.7.1.1.1 | R/O | INTEGER ・version1(1) | IEEE 802.1Q version information |
| dot1qMaxVlanId | 1.3.6.1.2.1.17.7.1.1.2 | R/O | VlanId | Maximum no. of IEEE 802.1Q VLAN IDs |
| dot1qMaxSupportedVlans | 1.3.6.1.2.1.17.7.1.1.3 | R/O | Unsigned32 | Maximum no. of IEEE 802.1Q VLANs |
| dot1qNumVlans | 1.3.6.1.2.1.17.7.1.1.4 | R/O | Unsigned32 | No. of IEEE 802.1Q VLANs used |
dot1qTp group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot1qFdbTable | 1.3.6.1.2.1.17.7.1.2.1 | N/A | Filtering table | |||
| dot1qFdbEntry | 1.3.6.1.2.1.17.7.1.2.1.1 | N/A | INDEX ・dot1qFdbId | |||
| dot1qFdbId | 1.3.6.1.2.1.17.7.1.2.1.1.1 | N/A | Unsigned32 | Identifier for filtering database | ||
| dot1qFdbDynamicCount | 1.3.6.1.2.1.17.7.1.2.1.1.2 | R/O | Counter32 | No. of active entries in filtering database | ||
| dot1qTpFdbTable | 1.3.6.1.2.1.17.7.1.2.2 | N/A | Table of information for unicast entries that have transparent bridge forwarding or filtering information | |||
| dot1qTpFdbEntry | 1.3.6.1.2.1.17.7.1.2.2.1 | N/A | INDEX ・dot1qFdbId ・dot1qTpFdbAddress | |||
| dot1qTpFdbAddress | 1.3.6.1.2.1.17.7.1.2.2.1.1 | N/A | MacAddress | Unicast MAC addresses that have transparent bridge forwarding or filtering information | ||
| dot1qTpFdbPort | 1.3.6.1.2.1.17.7.1.2.2.1.2 | R/O | Integer32 (0..65535) | Port number of port that transmitted a frame with a source address that is the same as the instance value, corresponding to the transparent bridge dot1qTpFdbAddress | ||
| dot1qTpFdbStatus | 1.3.6.1.2.1.17.7.1.2.2.1.3 | R/O | INTEGER ・other(1) ・invalid(2) ・learned(3) ・self(4) ・mgmt(5) | Transparent bridge MAC address table status | ||
dot1qVlan group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| dot1qVlanNumDeletes | 1.3.6.1.2.1.17.7.1.4.1 | R/O | Counter32 | No. of VLAN entries that were deleted | ||
| dot1qVlanCurrentTable | 1.3.6.1.2.1.17.7.1.4.2 | N/A | Table of VLAN entry information | |||
| dot1qVlanCurrentEntry | 1.3.6.1.2.1.17.7.1.4.2.1 | N/A | INDEX ・dot1qVlanTimeMark ・dot1qVlanIndex | |||
| dot1qVlanTimeMark | 1.3.6.1.2.1.17.7.1.4.2.1.1 | N/A | TimeFilter | Time filter for VLAN entries | ||
| dot1qVlanIndex | 1.3.6.1.2.1.17.7.1.4.2.1.2 | N/A | VlanIndex | VLAN ID | ||
| dot1qVlanFdbId | 1.3.6.1.2.1.17.7.1.4.2.1.3 | R/O | Unsigned32 | Filtering database used by VLAN | ||
| dot1qVlanCurrentEgressPorts | 1.3.6.1.2.1.17.7.1.4.2.1.4 | R/O | PortList | Set of ports that output VLAN traffic as untagged or tagged frames | ||
| dot1qVlanCurrentUntaggedPorts | 1.3.6.1.2.1.17.7.1.4.2.1.5 | R/O | PortList | Set of ports that transmit VLAN traffic as untagged frames | ||
| dot1qVlanStatus | 1.3.6.1.2.1.17.7.1.4.2.1.6 | R/O | INTEGER ・other(1) ・permanent(2) ・dynamicGvrp(3) | VLAN status | ||
| dot1qVlanCreationTime | 1.3.6.1.2.1.17.7.1.4.2.1.7 | R/O | TimeTicks | sysUpTime value when creating VLAN | ||
| dot1qVlanStaticTable | 1.3.6.1.2.1.17.7.1.4.3 | N/A | Table of VLAN static setting information | |||
| dot1qVlanStaticEntry | 1.3.6.1.2.1.17.7.1.4.3.1 | N/A | INDEX ・dot1qVlanIndex | |||
| dot1qVlanStaticName | 1.3.6.1.2.1.17.7.1.4.3.1.1 | R/NC | SnmpAdminString (SIZE (0..32)) | Name assigned to VLAN | ||
| dot1qVlanStaticEgressPorts | 1.3.6.1.2.1.17.7.1.4.3.1.2 | R/NC | PortList | Set of ports assigned to VLAN output list | ||
| dot1qVlanForbiddenEgressPorts | 1.3.6.1.2.1.17.7.1.4.3.1.3 | R/NC | PortList | Set of ports prohibited from being included in the VLAN output list | ||
| dot1qVlanStaticUntaggedPorts | 1.3.6.1.2.1.17.7.1.4.3.1.4 | R/NC | PortList | Set of ports that transmit VLAN output traffic as untagged frames | ||
| dot1qVlanStaticRowStatus | 1.3.6.1.2.1.17.7.1.4.3.1.5 | R/NC | RowStatus | VLAN entry status | ||
| dot1qNextFreeLocalVlanIndex | 1.3.6.1.2.1.17.7.1.4.4 | R/O | Integer32 (0|4096..2147483647) | Next VLAN ID that can be used | ||
| dot1qPortVlanTable | 1.3.6.1.2.1.17.7.1.4.5 | N/A | Table of VLAN setting information for each port | |||
| dot1qPortVlanEntry | 1.3.6.1.2.1.17.7.1.4.5.1 | N/A | AUGMENTS ・dot1dBasePortEntry | |||
| dot1qPvid | 1.3.6.1.2.1.17.7.1.4.5.1.1 | R/NW | VlanIndex | VLAN IDs assigned to untagged or priority tag frames | ||
| dot1qPortAcceptableFrameTypes | 1.3.6.1.2.1.17.7.1.4.5.1.2 | R/NW | INTEGER ・admitAll(1) ・admitOnlyVlanTagged(2) | Frame types permitted for reception on the port | ||
| dot1qPortIngressFiltering | 1.3.6.1.2.1.17.7.1.4.5.1.3 | R/NW | TruthValue | Filtering of received frames on a port | ||
4.9 ifMIB group
This MIB is related to additional information for the interface.
The ifMIB group is divided into subgroups such as those shown below.
ifMIB(31)
|
+--ifMIBObjects(1)
ifMIBObjects group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| ifXTable | 1.3.6.1.2.1.31.1.1 | N/A | Table of additional information for interface | |||
| ifXEntry | 1.3.6.1.2.1.31.1.1.1 | N/A | AUGMENTS ・ifEntry | |||
| ifName | 1.3.6.1.2.1.31.1.1.1.1 | R/O | DisplayString | Interface name | ||
| ifInMulticastPkts | 1.3.6.1.2.1.31.1.1.1.2 | R/O | Counter32 | Number of multicast packets notified to the upper level protocol | ||
| ifInBroadcastPkts | 1.3.6.1.2.1.31.1.1.1.3 | R/O | Counter32 | Number of broadcast packets notified to the upper level protocol | ||
| ifOutMulticastPkts | 1.3.6.1.2.1.31.1.1.1.4 | R/O | Counter32 | Number of multicast packets requested to be sent by the upper level protocol | ||
| ifOutBroadcastPkts | 1.3.6.1.2.1.31.1.1.1.5 | R/O | Counter32 | Number of broadcast packets requested to be sent by the upper level protocol | ||
| ifHCInOctets | 1.3.6.1.2.1.31.1.1.1.6 | R/O | Counter64 | Total number of octets received 64-bit version of ifInOctets | ||
| ifHCOutOctets | 1.3.6.1.2.1.31.1.1.1.10 | R/O | Counter64 | Total number of octets sent 64-bit version of ifOutOctets | ||
| ifHighSpeed | 1.3.6.1.2.1.31.1.1.1.15 | R/O | Gauge32 | Interface speed Mbps | ||
| ifAlias | 1.3.6.1.2.1.31.1.1.1.18 | R/NW | DisplayString (SIZE (0..64)) | Alias name of the interface If the description command is set for the interface, that value will be used. If the description command is not set, that will be an empty character string. If a character string exceeding 64 characters is set in the description command, only the first 64 characters are returned. | ||
4.10 entityMIB Groups
This MIB is related to entity information
Syntax defined in the entityMIB group is indicated below.
Syntax Defined in the entityMIB Group
| Syntax | Definition |
|---|---|
| PhysicalIndex | Integer32 (1..2147483647) |
The entityMIB group is divided into subgroups, as follows.
entityMIB(47)
|
+--entityMIBObjects(1)
|
+--entityPhysical(1)entityPhysical group
| MIB Name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| entPhysicalTable | 1.3.6.1.2.1.47.1.1.1 | N/A | Table of entity information | |||
| entPhysicalEntry | 1.3.6.1.2.1.47.1.1.1.1 | N/A | INDEX ・ entPhysicalIndex | |||
| entPhysicalIndex | 1.3.6.1.2.1.47.1.1.1.1.1 | N/A | PhysicalIndex | Index of entities Stack ID | ||
| entPhysicalSerialNum | 1.3.6.1.2.1.47.1.1.1.1.11 | R/NW | SnmpAdminString (SIZE (0..32)) | Device serial no. | ||
5 Private MIB
The private MIBs that are supported by this product are shown below.
5.1 yamahaSWHardware group
This MIB is related to hardware information for Yamaha switches.
yamahaSWHardware group
| MIB name | OID | Access | Syntax | Description |
|---|---|---|---|---|
| yshMemorySize | 1.3.6.1.4.1.1182.3.1.2 | R/O | INTEGER | Memory size |
| yshFlashROMSize | 1.3.6.1.4.1.1182.3.1.3 | R/O | INTEGER | FlashROM size |
| yshMemoryUtil | 1.3.6.1.4.1.1182.3.1.4 | R/O | Gauge (0..100) | Memory usage ratio |
| yshCpuUtil5sec | 1.3.6.1.4.1.1182.3.1.5 | R/O | Gauge (0..100) | CPU usage ratio (5-second average) |
| yshCpuUtil1min | 1.3.6.1.4.1.1182.3.1.6 | R/O | Gauge (0..100) | CPU usage ratio (1-minute average) |
| yshCpuUtil5min | 1.3.6.1.4.1.1182.3.1.7 | R/O | Gauge (0..100) | CPU usage ratio (5-minute average) |
5.2 yamahaSWFirmware group
This MIB is related to firmware information for Yamaha switches.
yamahaSWFirmware group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| ysfConfigFile | 1.3.6.1.4.1.1182.3.2.2 | R/O | DisplayString (SIZE (0..255)) | Startup config | ||
| ysfRevision | 1.3.6.1.4.1.1182.3.2.3 | R/O | DisplayString (SIZE (0..255)) | Firmware version | ||
| ysfUpTime | 1.3.6.1.4.1.1182.3.2.4 | R/O | TimeTicks | Elapsed time from boot | ||
| ysfRestart | 1.3.6.1.4.1.1182.3.2.11 | R/W | INTEGER ・nothing(1) ・restart(2) | The system will reboot when the “restart” value is written | ||
5.3 yamahaSWL2ms group
This MIB is related to L2MS information for Yamaha switches.
yamahaSWL2ms group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| ysl2msNumber | 1.3.6.1.4.1.1182.3.5.1 | N/A | INTEGER | Number of switches that can be recognized Note: Used only with trap notifications | ||
| ysl2msEnableTrap | 1.3.6.1.4.1.1182.3.5.2 | R/W | INTEGER ・enabled(1) ・disabled(2) | Setting value for determining whether SNMP traps due to L2MS information are notified | ||
| ysl2msTable | 1.3.6.1.4.1.1182.3.5.3 | N/A | Table of information for devices connected via L2MS | |||
| ysl2msEntry | 1.3.6.1.4.1.1182.3.5.3.1 | N/A | INDEX ・ysl2msIndex | |||
| ysl2msIndex | 1.3.6.1.4.1.1182.3.5.3.1.1 | N/A | DisplayString (SIZE (0..6)) | MAC address of device Note: Used only with trap notifications | ||
| ysl2msProduct | 1.3.6.1.4.1.1182.3.5.3.1.2 | N/A | INTEGER ・generic(1) ・swx2200-8g(2) ・swx2200-24g(3) ・swx2200-8poe(4) | Model of device Note: Used only with trap notifications | ||
| ysl2msPhysAddress | 1.3.6.1.4.1.1182.3.5.3.1.5 | N/A | DisplayString (SIZE (0..6)) | MAC address of device Note: Used only with trap notifications | ||
| ysl2msRoute | 1.3.6.1.4.1.1182.3.5.3.1.11 | N/A | DisplayString (SIZE (0..64)) | Route information to device Note: Used only with trap notifications | ||
5.4 yamahaSWErrDisable group
This MIB is related to error detection function information for Yamaha switches.
yamahaSWErrDisable group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| ysedConfigTable | 1.3.6.1.4.1.1182.3.6.1 | N/A | Table of setting information for the error detection function | |||
| ysedConfigEntry | 1.3.6.1.4.1.1182.3.6.1.1 | N/A | INDEX ・ysedConfigIndex | |||
| ysedConfigIndex | 1.3.6.1.4.1.1182.3.6.1.1.1 | N/A | INTEGER (1..2147483647) | Table index Corresponds to the ysedConfigFunction value | ||
| ysedConfigFunction | 1.3.6.1.4.1.1182.3.6.1.1.2 | R/O | INTEGER ・bpduguard(1) ・loopdetect(2) | Functions that are enabled for error detection | ||
| ysedConfigAutoRecovery | 1.3.6.1.4.1.1182.3.6.1.1.3 | R/W | INTEGER ・enabled(1) ・disabled(2) | Setting for automatic recovery from Error Disable state | ||
| ysedConfigRecoveryInterval | 1.3.6.1.4.1.1182.3.6.1.1.4 | R/W | INTEGER (10..1000000) | Frequency (seconds) at which to attempt automatic recovery from Error Disable state | ||
| ysedEnableTrap | 1.3.6.1.4.1.1182.3.6.2 | R/W | INTEGER ・enabled(1) ・disabled(2) | Setting value for determining whether SNMP traps due to error detection functions are notified | ||
| ysedIfTable | 1.3.6.1.4.1.1182.3.6.3 | N/A | Table of information for the error detection function | |||
| ysedIfEntry | 1.3.6.1.4.1.1182.3.6.3.1 | N/A | INDEX ・ysedIfIndex | |||
| ysedIfIndex | 1.3.6.1.4.1.1182.3.6.3.1.1 | N/A | INTEGER (1..2147483647) | Interface index | ||
| ysedIfStatus | 1.3.6.1.4.1.1182.3.6.3.1.2 | R/O | INTEGER ・normal(1) ・bpduguard(2) ・loopdetect(3) ・portsecurity(4) | Error Disable state of port | ||
5.5 yamahaSWRmon group
This MIB is related to RMON information for Yamaha switches.
yamahaSWRmon group
| MIB name | OID | Access | Syntax | Description |
|---|---|---|---|---|
| ysrmonSetting | 1.3.6.1.4.1.1182.3.7.1 | R/W | INTEGER ・enabled(1) ・disabled(2) | Enabled/disabled setting of RMON function |
| ysrmonEnableTrap | 1.3.6.1.4.1.1182.3.7.2 | R/W | INTEGER ・enabled(1) ・disabled(2) | Setting value for determining whether SNMP traps due to RMON functions are notified |
5.6 yamahaSWTermMon group
This MIB is related to terminal monitoring information for Yamaha switches.
yamahaSWTermMon group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| ystmEnableTrap | 1.3.6.1.4.1.1182.3.8.1 | R/W | INTEGER ・enabled(1) ・disabled(2) | Setting value for determining whether SNMP traps due to terminal monitoring functions are notified | ||
| ystmIfTermTable | 1.3.6.1.4.1.1182.3.8.3 | N/A | Table of terminal monitoring functions targeted at ports | |||
| ystmIfTermEntry | 1.3.6.1.4.1.1182.3.8.3.1 | N/A | INDEX ・ystmIfTermIndex | |||
| ystmIfTermIndex | 1.3.6.1.4.1.1182.3.8.3.1.1 | N/A | INTEGER (1..2147483647) | ifIndex Note: Used only with trap notifications | ||
| ystmIfTermDescr | 1.3.6.1.4.1.1182.3.8.3.1.2 | N/A | DisplayString (SIZE (0..255)) | Terminal monitoring description Note: Used only with trap notifications | ||
| ystmIfTermStatus | 1.3.6.1.4.1.1182.3.8.3.1.3 | N/A | INTEGER ・up(1) ・down(2) ・idle(3) | Terminal monitoring status Note: Used only with trap notifications | ||
| ystmIpTermTable | 1.3.6.1.4.1.1182.3.8.4 | N/A | Table of terminal monitoring functions targeted at IP addresses | |||
| ystmIpTermEntry | 1.3.6.1.4.1.1182.3.8.4.1 | N/A | INDEX ystmIpTermIndex | |||
| ystmIpTermIndex | 1.3.6.1.4.1.1182.3.8.4.1.1 | N/A | IpAddress | IP address of monitored target Note: Used only with trap notifications | ||
| ystmIpTermDescr | 1.3.6.1.4.1.1182.3.8.4.1.2 | N/A | DisplayString (SIZE (0..255)) | Terminal monitoring description Note: Used only with trap notifications | ||
| ystmIpTermStatus | 1.3.6.1.4.1.1182.3.8.4.1.3 | N/A | INTEGER ・up(1) ・down(2) ・idle(3) | Terminal monitoring status Note: Used only with trap notifications | ||
5.7 yamahaSWBridge group
This MIB is related to dot1dBridge information for Yamaha switches.
yamahaSWBridge group
| MIB name | OID | Access | Syntax | Description |
|---|---|---|---|---|
| ysbridgeEnableTrap | 1.3.6.1.4.1.1182.3.9.1 | R/W | INTEGER ・enabled(1) ・disabled(2) | Setting value for determining whether SNMP traps due to dot1dBridge information are notified |
5.8 yamahaSWLoopDetect group
This MIB is related to loop detection information for Yamaha switches.
yamahaSWLoopDetect group
| MIB name | OID | Access | Syntax | Description | ||
|---|---|---|---|---|---|---|
| ysldEnableTrap | 1.3.6.1.4.1.1182.3.11.1 | R/W | INTEGER ・enabled(1) ・disabled(2) | Whether or not trap sends notification | ||
| ysldSystemAdmin | 1.3.6.1.4.1.1182.3.11.2 | R/W | INTEGER ・enabled(1) ・disabled(2) | Enables/disables loop detection for the entire system | ||
| ysldSystemBlockingRecoveryInterval | 1.3.6.1.4.1.1182.3.11.6 | R/W | INTEGER (0|10..3600) | Time (seconds) for a blocked port to be automatically restored after resolving a loop | ||
| ysldSystemStatusReset | 1.3.6.1.4.1.1182.3.11.7 | R/W | INTEGER ・nothing(1) ・reset(2) | Reset loop detection status | ||
| ysldPortTable | 1.3.6.1.4.1.1182.3.11.8 | N/A | Table of loop detection information for each port | |||
| ysldPortEntry | 1.3.6.1.4.1.1182.3.11.8.1 | N/A | INDEX ・ysldPortStackId ・ysldPortIndex | |||
| ysldPortStackId | 1.3.6.1.4.1.1182.3.11.8.1.1 | N/A | INTEGER (1..2147483647) | Stack ID This can be obtained with stack ID 1 if stack was not configured. | ||
| ysldPortIndex | 1.3.6.1.4.1.1182.3.11.8.1.2 | N/A | INTEGER (1..2147483647) | Port number | ||
| ysldPortAdmin | 1.3.6.1.4.1.1182.3.11.8.1.3 | R/W | INTEGER ・enable(1) ・disable(2) | Enables/disables loop detection at ports | ||
| ysldPortStatus | 1.3.6.1.4.1.1182.3.11.8.1.4 | R/O | INTEGER ・disabled(1) ・normal(2) ・detected(3) ・blocked(4) ・shutdown(5) | Loop detected disabled(1) : Loop detection disabled normal(2) : Loop not detected detected(3) : Loop detected blocked(4) : Loop is detected and port is blocked shutdown(5) : Loop is detected and port is shut down | ||
| ysldPortBlocking | 1.3.6.1.4.1.1182.3.11.8.1.5 | R/W | INTEGER ・enable(1) ・disable(2) | Sets whether or not to block port if a loop occurs | ||
6 Standard MIB traps
Standard MIB traps that are supported by this product are shown below.
6.1 Traps defined by RFC1157
These are traps defined by RFC1157.
List of traps defined by RFC1157
| Trap name | OID | Additional information for trap (variable-bindings) | Description |
|---|---|---|---|
| coldStart | 1.3.6.1.6.3.1.1.5.1 | None | Notification on power OFF/ON and during firmware updates |
| warmStart | 1.3.6.1.6.3.1.1.5.2 | None | Notification while the reload command is being executed |
| linkDown | 1.3.6.1.6.3.1.1.5.3 | ifIndex ifAdminStatus ifOperStatus | Notification during linkdown |
| linkUp | 1.3.6.1.6.3.1.1.5.4 | ifIndex ifAdminStatus ifOperStatus | Notification during linkup |
| authenticationFailure | 1.3.6.1.6.3.1.1.5.5 | None | Notification when receiving an SNMP message that has an incorrect community name |
6.2 rmon group trap
This trap is related to RMON information.
rmon group trap list
| Trap name | OID | Additional information for trap (variable-bindings) | Description |
|---|---|---|---|
| risingAlarm | 1.3.6.1.2.1.16.0.1 | alarmIndex alarmVariable alarmSampleType alarmValue alarmRisingThreshold | Notification that upper threshold value has been exceeded |
| fallingAlarm | 1.3.6.1.2.1.16.0.2 | alarmIndex alarmVariable alarmSampleType alarmValue alarmFallingThreshold | Notification that lower threshold value has been exceeded |
6.3 dot1dBridge group trap
This trap is related to dot1dBridge information.
dot1dBridge group trap list
| Trap name | OID | Additional information for trap (variable-bindings) | Description |
|---|---|---|---|
| newRoot | 1.3.6.1.2.1.17.0.1 | None | Notification that a new root for bridge has been detected |
| topologyChange | 1.3.6.1.2.1.17.0.2 | None | Notification that a change in topology has been detected |
7 Private MIB traps
The private MIB traps that are supported by this product are shown below.
7.1 yamahaSWErrDisable group trap
This trap is related to error detection function information for Yamaha switches.
yamahaSWErrDisable group trap list
| Trap name | OID | Additional information for trap (variable-bindings) | Description |
|---|---|---|---|
| ysedTrap | 1.3.6.1.4.1.1182.3.6.0.1 | ysedIfStatus | Notification when ErrorDisable is detected/cancelled |
7.2 yamahaSWTermMon group trap
This trap is related to terminal monitoring information for Yamaha switches.
yamahaSWTermMon group trap list
| Trap name | OID | Additional information for trap (variable-bindings) | Description |
|---|---|---|---|
| ystmIfTermTrap | 1.3.6.1.4.1.1182.3.8.0.1 | ystmIfTermDescr ystmIfTermStatus | Notification when terminal monitoring is detected |
| ystmIpTermTrap | 1.3.6.1.4.1.1182.3.8.0.2 | ystmIpTermDescr ystmIpTermStatus | Notification when IP address terminal monitoring is detected |
7.3 yamahaSWLoopDetect group trap
This trap is related to loop detection information for Yamaha switches.
List of yamahaSWLoopDetect group traps
| Trap name | OID | Additional information for trap (variable-bindings) | Description |
|---|---|---|---|
| ysldPortDetectLoopTrap | 1.3.6.1.4.1.1182.3.11.0.1 | ysldPortStackId ysldPortIndex ysldPortStatus | Sends notification when loop is detected |
| ysldPortResolveLoopTrap | 1.3.6.1.4.1.1182.3.11.0.2 | ysldPortStackId ysldPortIndex ysldPortStatus | Sends notification when loop is resolved |
8 Points of Caution
- The 64-bit counter MIB can be read and written by SNMPv2c and SNMPv3 requests.
- SNMPv1 requests cannot be read or written.
- SWP2 Series Technical Data (Basic Functions)
- Other information
- Command reference
- SWP2 Series Technical Data (Basic Functions)
- Other information
- About the licenses
About the licenses
Open-source software used in this product
- For information about the license provisions, visit the Yamaha Pro Audio website.
- SWP2 Series Technical Data (Basic Functions)
- Other information
- About Google Analytics
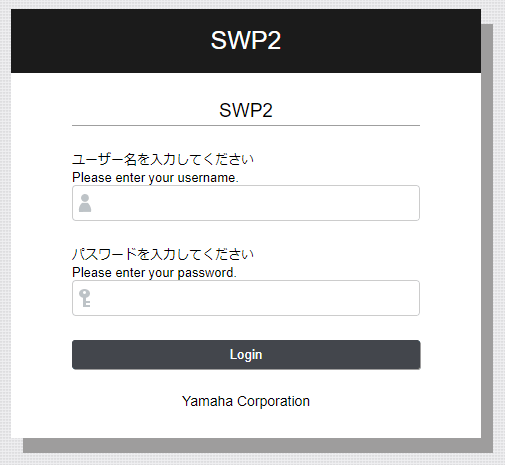
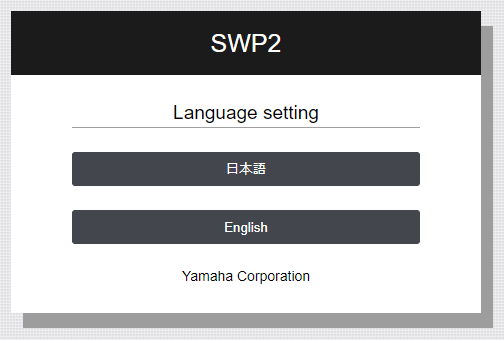
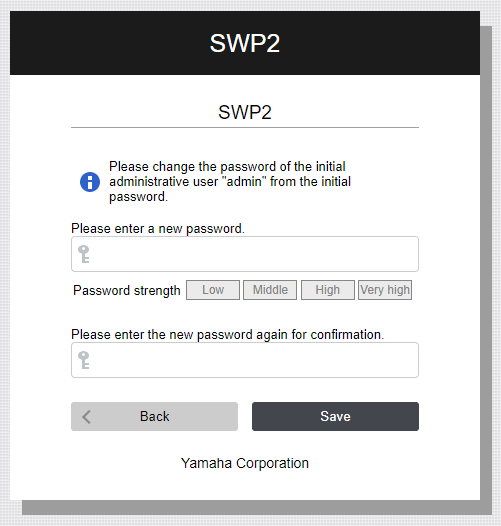

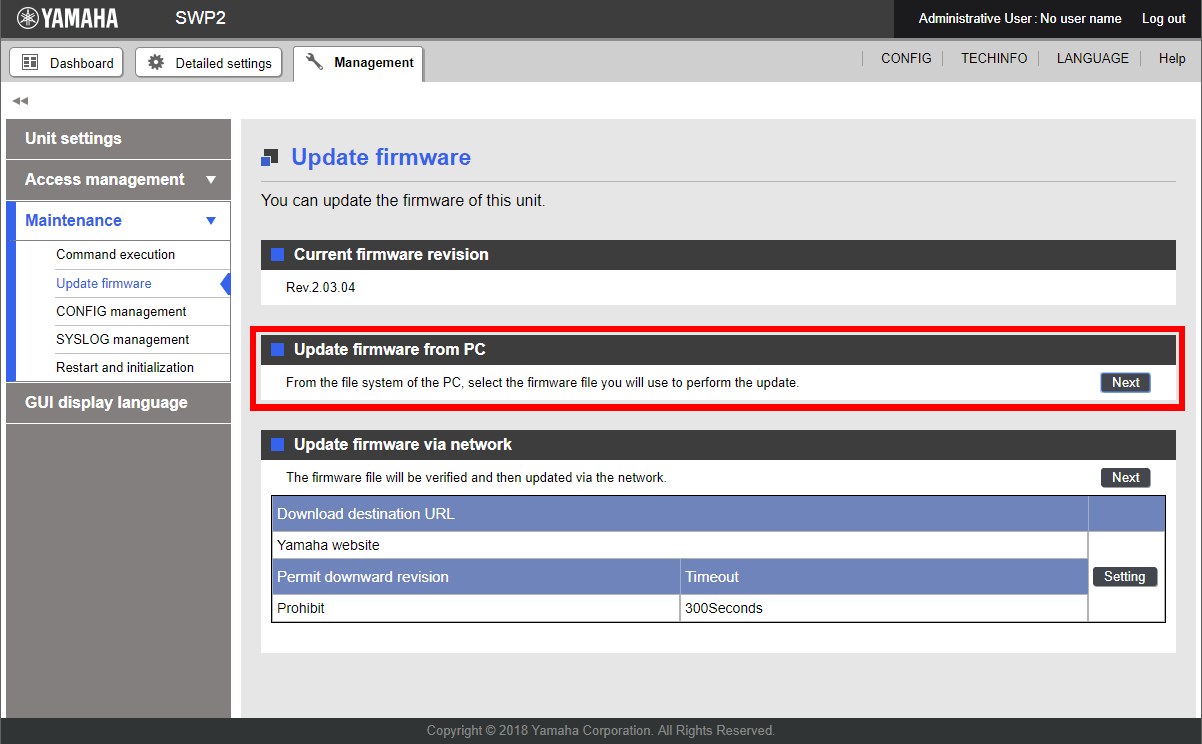
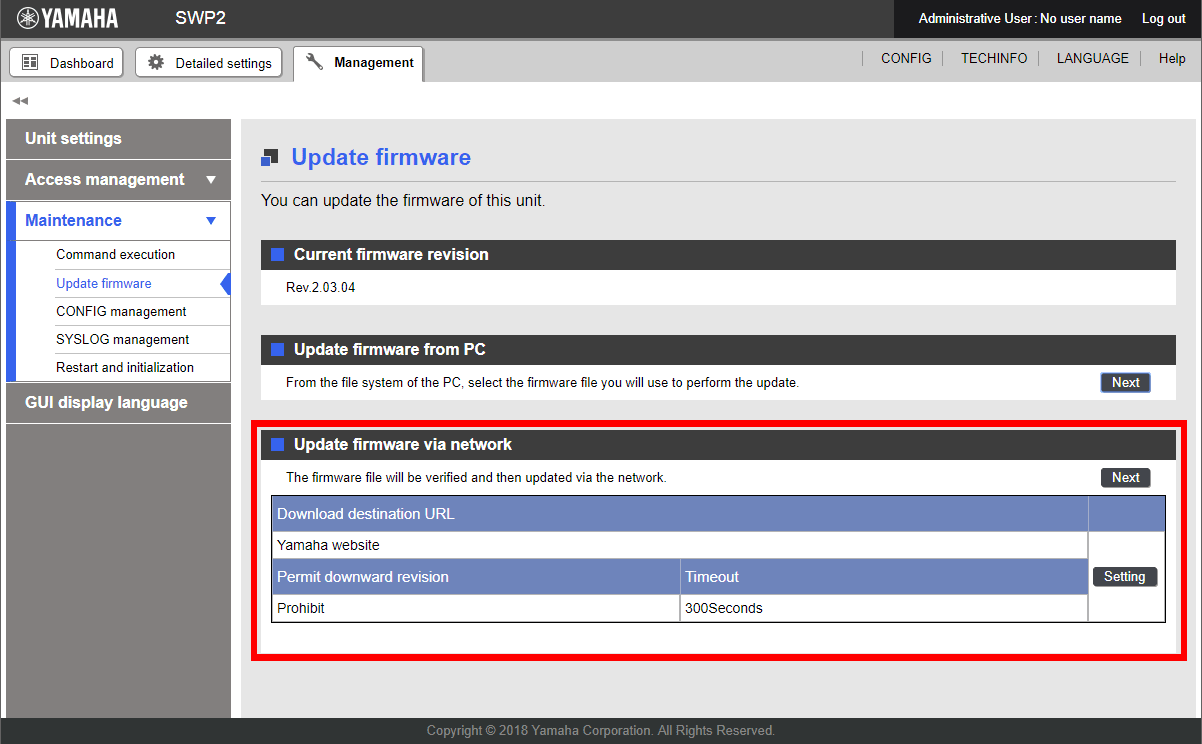

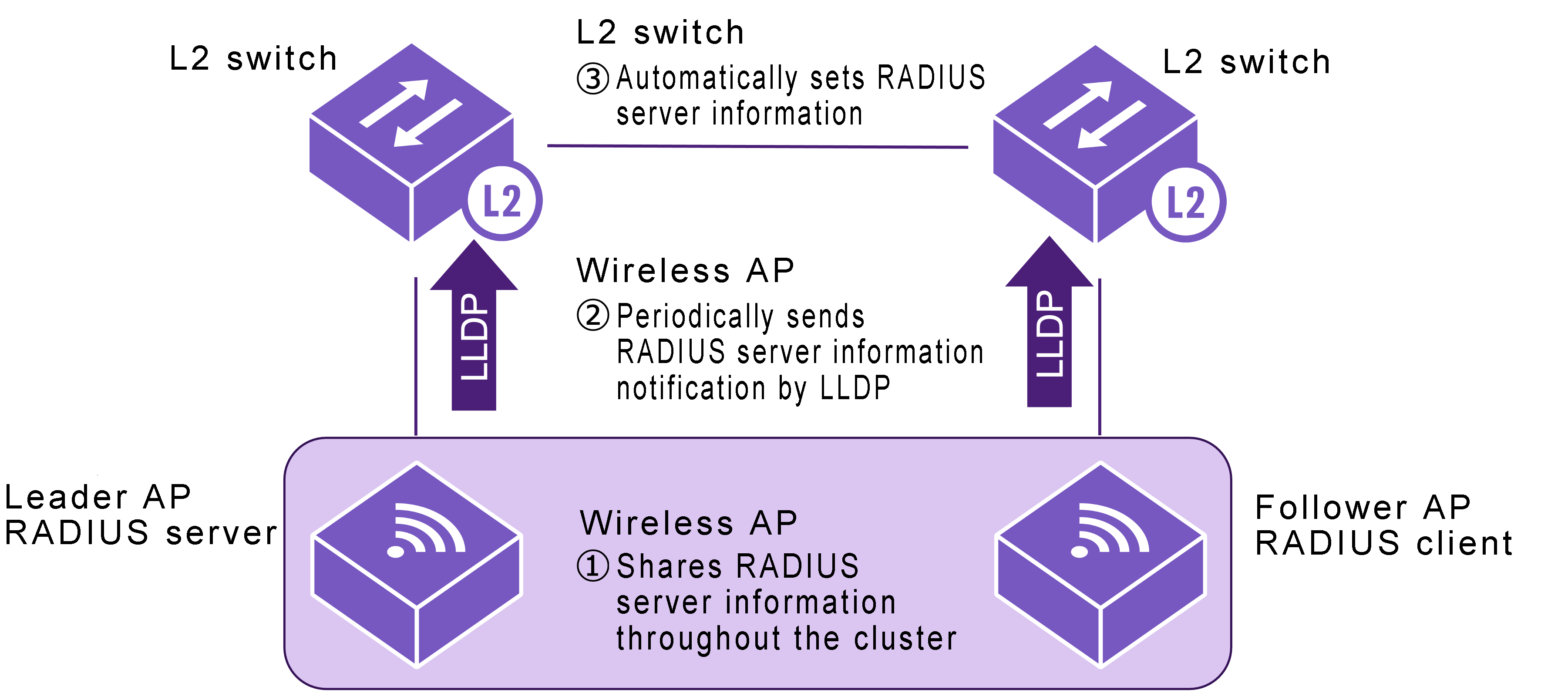
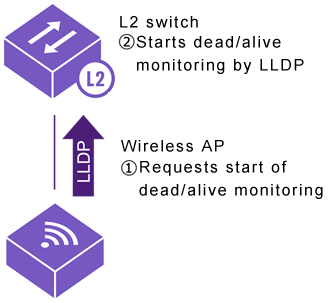
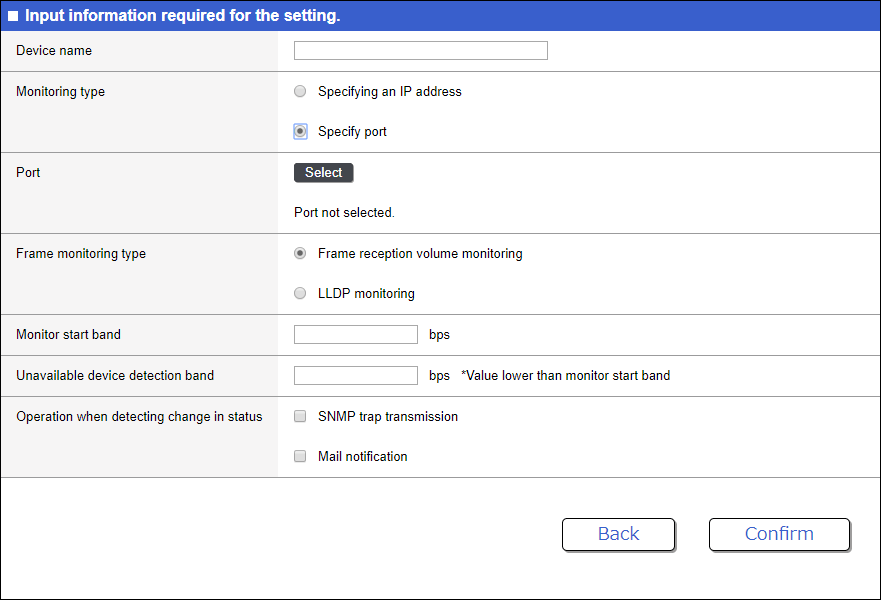
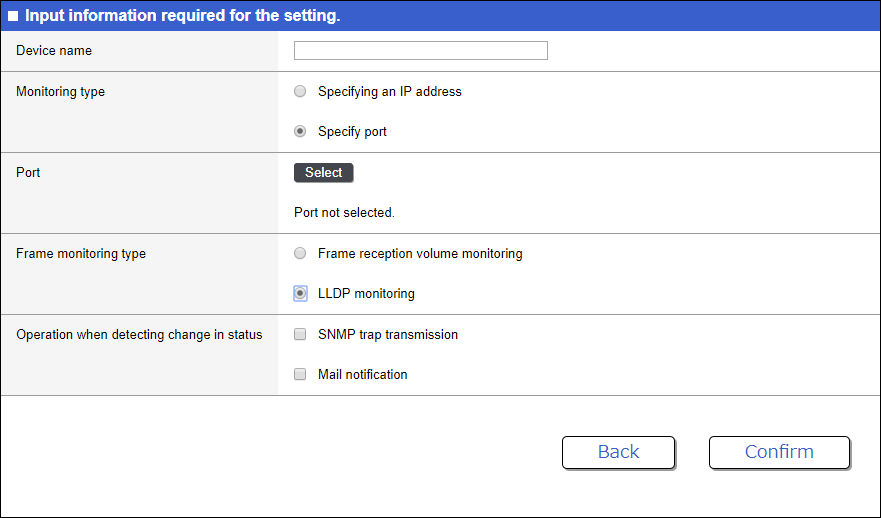
 ), and then make a selection in the following screen.
), and then make a selection in the following screen.